#privesc search results
Dell patched a Critical (CVSS 9.1) flaw (CVE-2025-46608) in Dell Data Lakehouse that allows a high-privileged remote attacker to escalate privileges and gain unauthorized administrative control. #Dell #DataLakehouse #PrivEsc #Cybersecurity securityonline.info/critical-dell-…
A High-severity flaw (CVSS 8.0) in Splunk Enterprise/Universal Forwarder for Windows allows low-privileged users to access/tamper with sensitive installation directories due to incorrect permissions. #Splunk #PrivEsc #Cybersecurity #PatchNow securityonline.info/high-severity-…
Elastic patched a Critical EoP flaw (CVE-2025-37736) in ECE (v3.8.3/4.0.3) where the readonly user can create admin users and inject new API keys by bypassing authorization checks. #ElasticSearch #ECE #PrivEsc #Cybersecurity securityonline.info/elastic-patche…
securityonline.info
Elastic Patches High-Severity Privilege Escalation Flaw in Elastic Cloud Enterprise (CVE-2025-37736)
Elastic patched a Critical EoP flaw (CVE-2025-37736) in ECE (v3.8.3/4.0.3) where the readonly user can create admin users and inject new API keys by bypassing authorization checks.
NVIDIA patched a High-severity EoP flaw (CVE-2025-23358) in the NVIDIA App installer for Windows. A local attacker could exploit a search path issue to achieve code execution with elevated privileges. #NVIDIA #PrivEsc #Cybersecurity #WindowsUpdate securityonline.info/high-severity-…
Dell patched seven flaws in CloudLink, including two Critical bugs that allow an authenticated user to escape the restricted shell and execute arbitrary commands for system takeover. Update to v8.2. #DellCloudLink #PrivEsc #Cybersecurity #PatchNow securityonline.info/critical-dell-…
Elastic patched a High-severity flaw (CVE-2025-37735) in Elastic Defend for Windows. A local attacker can delete arbitrary files via the SYSTEM service, risking privilege escalation. Update to v8.19.6+. #ElasticDefend #PrivEsc #Cybersecurity #PatchNow securityonline.info/high-severity-…
A Critical DLL Hijacking flaw (CVE-2025-13051) in ASUSTOR Backup Plan/EZSync allows local attackers to gain SYSTEM privileges by planting a malicious DLL in a user-writable path. Update immediately. #ASUSTOR #DLLHijacking #PrivEsc #Cybersecurity securityonline.info/critical-asust…
MinIO patched a privilege escalation flaw (CVE-2025-62506) where restricted service accounts could bypass session policies during account creation to gain full parent privileges. #MinIO #PrivEsc #CloudSecurity #ObjectStorage securityonline.info/privilege-esca…
Cisco patched a High-severity EoP flaw (CVE-2025-20341) in Catalyst Center Virtual Appliance. A low-privileged Observer user can remotely elevate privileges to Administrator via a crafted HTTP request. #CiscoCatalyst #PrivEsc #Cybersecurity #PatchNow securityonline.info/cisco-warns-of…
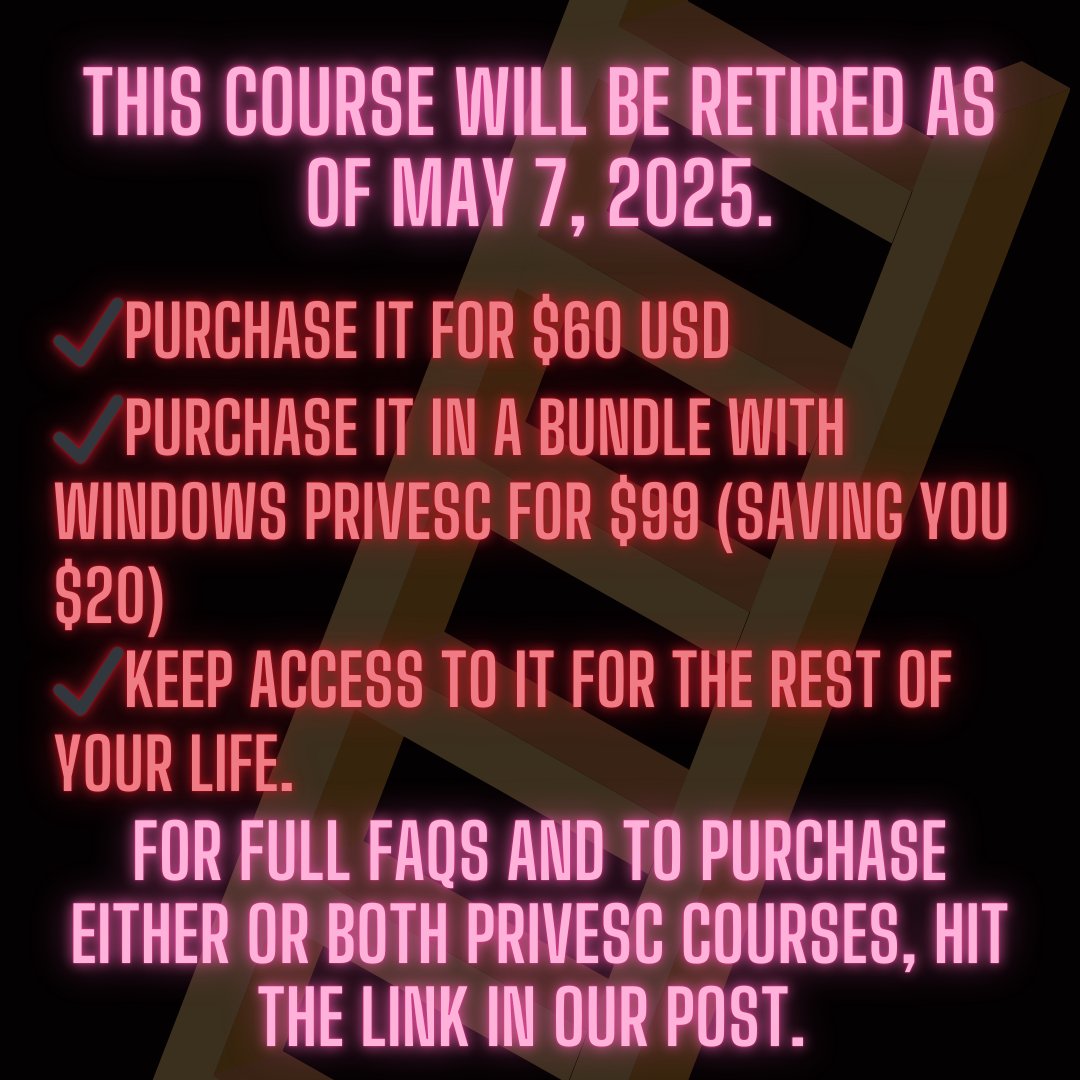
Our Linux and Windows Privilege Escalation courses will be officially retired for good on May 7th, 2025. Once retired, these courses will no longer be available, and we do not plan to remake them. You can still purchase the #PrivEsc courses until May 7th to secure lifetime

Upgrade your privilege escalation game 🚀 with the Linux PrivEsc course from the TCM Security Academy. But you need to act fast - the course (alongside Windows #PrivEsc) will be retired May 7th. Grab it before May 7th and get lifetime access, either on its own or bundled with



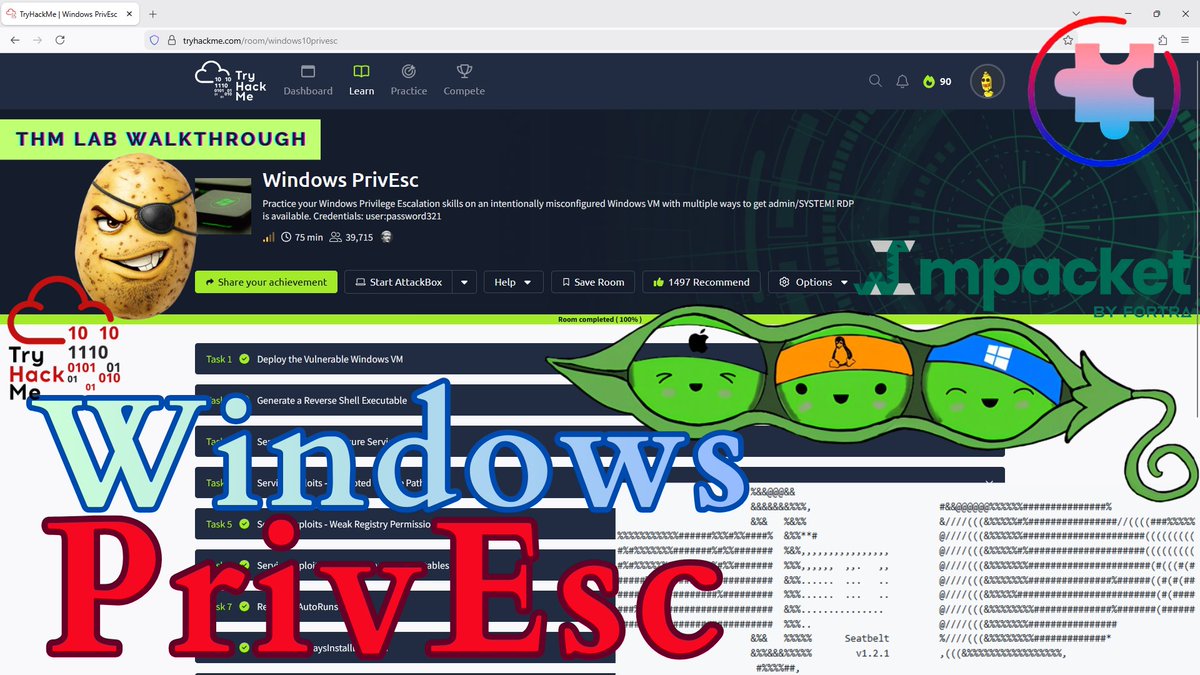
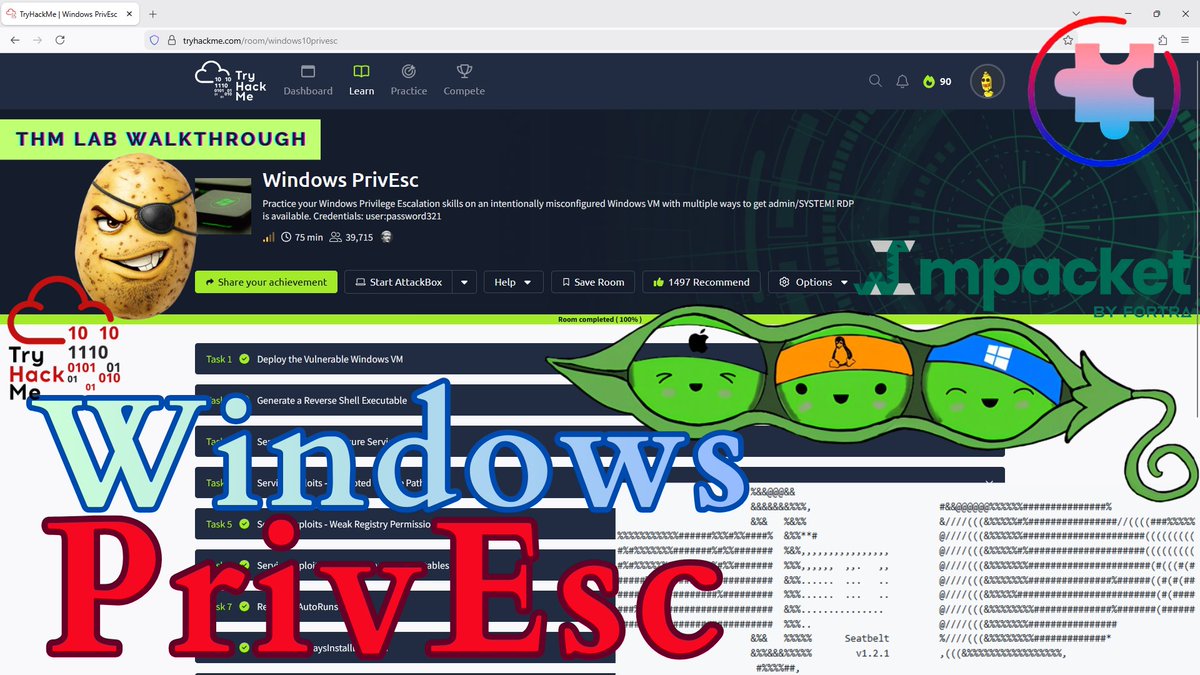
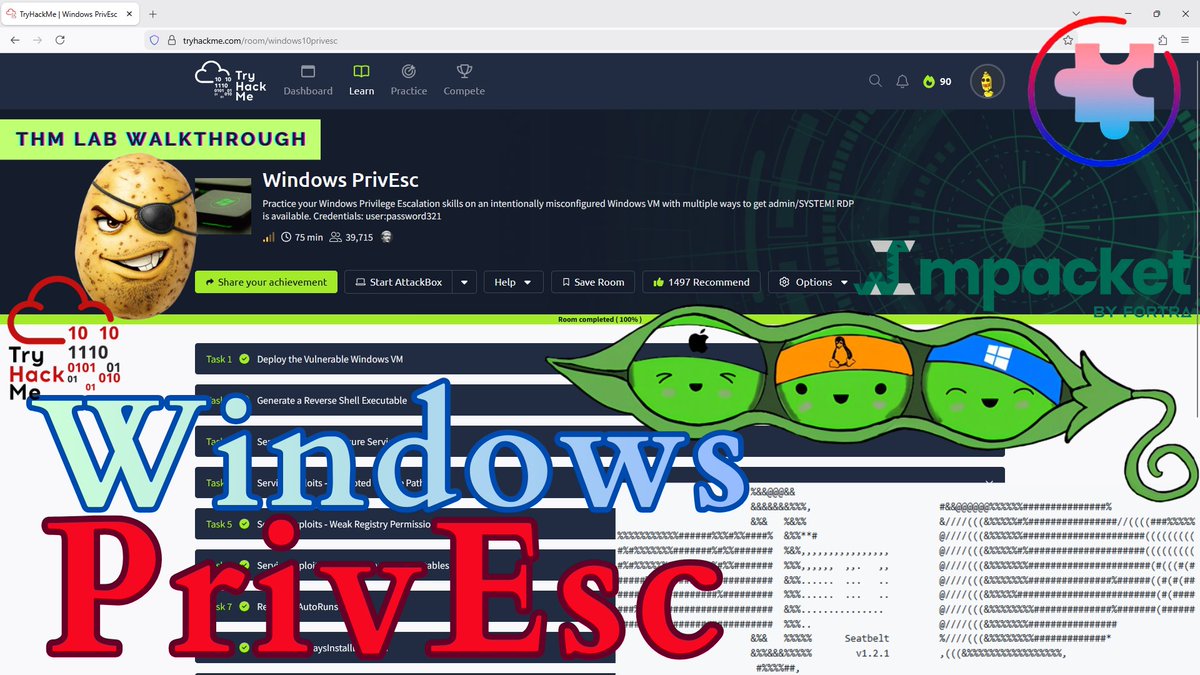
New video on my YouTube channel "Windows PrivEsc (@tryhackme walkthrough)"! youtu.be/tx-jYhqm6Jk #tryhackme #privesc #winpeas #impacket #cybersecuritytraining
Vulnversity - I have just completed this room! Check it out: tryhackme.com/room/vulnversi… #tryhackme #recon #privesc #webappsec #video #vulnversity via @tryhackme
tryhackme.com
Vulnversity
Learn about active recon, web app attacks and privilege escalation.
Introducing our latest course and our first course 100% made up of Hands-On Labs: 🧪 IAM Privilege Escalation (PrivEsc) Labs 🎉🍾 📣 This week and starting today, we’re releasing one new #AWS IAM #PrivEsc lab per day! Get started: cybr.com/courses/iam-pr…

Windows Privilege Escalation for Beginners will be retired as of May 7th! 😱 But don't panic yet - we are offering lifetime access for $60 USD or you can bundle it with Linux #PrivEsc for $99 USD. This 7-hour course, led by Heath Adams, covers everything you need to get started


MontréHack c'est demain! En présentiel dans les bureaux de Google Montréal ou en ligne! Join us tomorrow for MontreHack in Google Montreal's offices or online! #cybersecurity #privesc #rce #cybersecurite
Prochain MontréHack mercredi 15 novembre dans les bureaux de Google Montréal! Infos: montrehack.ca/2023/11/15/uni… Next MontreHack Wed. Nov. 15 in Google Montreal's offices! Details: montrehack.ca/2023/11/15/uni… #privesc #rce

Escalate Service Account To LocalSystem via Kerberos. github.com/wh0amitz/S4UTo… #privesc #ad #redteam #pentest
Windows Privilege Escalation - I have just completed this room! Check it out: tryhackme.com/room/windowspr… #tryhackme #windows #privesc #penetrationtesting #redteam #windowsprivesc20 via @tryhackme
Enumy: Enumeración y Escalada de Privilegios Post-Explotación en Linux | #Enumeracion #PostExplotación #PrivEsc #SeguridadOfensiva #Seguridad esgeeks.com/enumy-enumerac…
esgeeks.com
▷ Enumy: Enumeración y Escalada de Privilegios en Linux » EsGeeks
|➨ Enumy es una herramienta de enumeración, escalada de privilegios posteriores a la explotación de un sistema Linux. ✔
⚠️ CVE-2026-26143: Micr... PowerShell's input validation bypass hits 7.8 CVSS with local RCE potential - perfect for persistence once you're already in #PowerShell #PrivEsc. zerodaysignal.com/vulnerability/… #netsec #vulnerability #CVE #sysadmin #zeroday
zerodaysignal.com
CVE-2026-26143 - Security Alert
Improper input validation in Microsoft PowerShell allows an unauthorized attacker to bypass a security feature locally....
🚨 CVE-2012-10041: WAN E... Unauthenticated RCE chained with SUID privesc to root via shell_exec() and dosu binary - classic network appliance nightmare. #RCE #privesc #SUID. zerodaysignal.com/vulnerability/… #netsec #vulnerability #CVE #sysadmin #zeroday
zerodaysignal.com
CVE-2012-10041 - Security Alert
WAN Emulator v2.3 contains two unauthenticated command execution vulnerabilities. The result.php script calls shell_exec() with unsanitized input from...
🚨 CVE-2026-1114: Improper... Weak JWT secrets = admin access via offline bruteforce - LOLLMS basically handed attackers the keys to forge admin tokens at scale #JWT #PrivEsc. zerodaysignal.com/vulnerability/… #netsec #vulnerability #CVE #sysadmin #zeroday
zerodaysignal.com
CVE-2026-1114 - Security Alert
In parisneo/lollms version 2.1.0, the application's session management is vulnerable to improper access control due to the use of a weak secret key fo...
🚨 CVE-2026-34989: CI4... Profile name injection bypasses all RBAC controls in CI4MS - one XSS payload grants admin access across the entire CMS skeleton #StoredXSS #PrivEsc. zerodaysignal.com/vulnerability/… #netsec #vulnerability #CVE #sysadmin #zeroday
zerodaysignal.com
CVE-2026-34989 - Security Alert
CI4MS is a CodeIgniter 4-based CMS skeleton that delivers a production-ready, modular architecture with RBAC authorization and theme support. Prior to...
🚨 CVE-2026-33950: sig... Unauthenticated admin takeover on marine navigation systems - one HTTP request turns you into captain of someone else's boat. #MaritimeSec #PrivEsc. zerodaysignal.com/vulnerability/… #netsec #vulnerability #CVE #sysadmin #zeroday
zerodaysignal.com
CVE-2026-33950 - Security Alert
Signal K Server is a server application that runs on a central hub in a boat. Prior to version 2.24.0-beta.4, there is a privilege escalation vulnerab...
FortiClient for Linux affected with local privilege escalation vulnerability tracked as CVE-2026-24018. #cve #privesc #vulnerability
🚨 CVE-2026-4606: GeoVi... GeoVision ERM's file dialogs run as SYSTEM - trivial local privesc via Import Data function spawns SYSTEM-privileged explorer.exe #PrivEsc #Windows. zerodaysignal.com/vulnerability/… #netsec #vulnerability #CVE #sysadmin #zeroday
zerodaysignal.com
CVE-2026-4606 - Security Alert
GV Edge Recording Manager (ERM) v2.3.1 improperly runs application components with SYSTEM-level privileges, allowing any local user to gain full contr...
🚨 CVE-2026-4038: Aimo... Unauthenticated function call to `update_option` = instant admin takeover on 9.8 CVSS WordPress sites running this AI plugin. #WordPressSec #PrivEsc. zerodaysignal.com/vulnerability/… #netsec #vulnerability #CVE #sysadmin #zeroday
zerodaysignal.com
CVE-2026-4038 - Security Alert
The Aimogen Pro plugin for WordPress is vulnerable to Arbitrary Function Call that can lead to privilege escalation due to a missing capability check ...
New video on my YouTube channel "Windows PrivEsc (@tryhackme walkthrough)"! youtu.be/tx-jYhqm6Jk #tryhackme #privesc #winpeas #impacket #cybersecuritytraining
🔥 Microsoft Critical: SQL Server PrivEsc CVE-2026-21262 allows low priv to sysadmin in SQL 2016-2025. Patch KB5039217+ across envs, audit failed logins/escalations, block via WAF/EDR rules. #MSFTSecurity #SQLServer #PrivEsc #ThreatIntel

🚨 CVE-2026-32267: Craft... Token-based impersonation bypass in Craft CMS lets any low-priv user instantly become admin - shared URLs become admin shells. #CraftCMS #PrivEsc. zerodaysignal.com/vulnerability/… #netsec #vulnerability #CVE #sysadmin #zeroday
zerodaysignal.com
CVE-2026-32267 - Security Alert
Craft CMS is a content management system (CMS). From version 4.0.0-RC1 to before version 4.17.6 and from version 5.0.0-RC1 to before version 5.9.12, a...
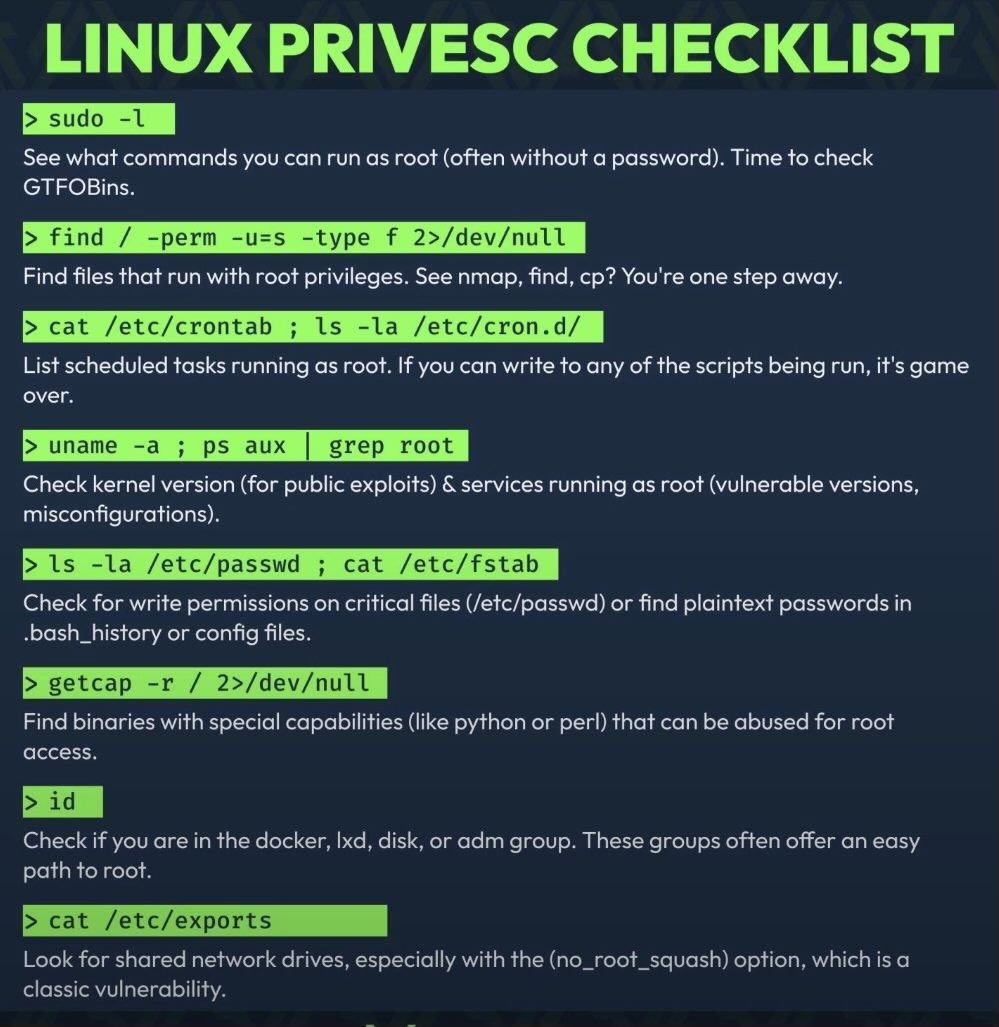
4 questions to ask every time in Linux privesc -What runs as root? (sudo -l) -What SUID binaries exist? (find / -perm -4000) -Any cron jobs running as root? -What writable directories does the system trust? 90% of escalations come from these four. #Linux #PrivEsc #EthicalHacking
grok wrote node code, now my admin panel grants everyone access. postman just uninstalled itself out of sheer embarrassment. asking for a friend (it's me). #AI #NodeJS #PrivEsc
🚨 CVE-2025-5947: Serv... Cookie validation oversight in service_finder_switch_back() leads to trivial admin account takeover with zero auth required. #CookieMonster #PrivEsc. zerodaysignal.com/vulnerability/… #netsec #vulnerability #CVE #sysadmin #zeroday
zerodaysignal.com
CVE-2025-5947 - Security Alert
The Service Finder Bookings plugin for WordPress is vulnerable to privilege escalation via authentication bypass in all versions up to, and including,...
🚨 Priv Esc Alert! Windows Defender Firewall got some nasty vulns ripe for privilege escalation. 🕵️♂️ Attackers could climb the ladder to SYSTEM. Patch up & lock it down! Deets: cybersecuritynews.com/windows-defend… #PrivEsc #CyberSec #Windows
Getting close to wrapping up the Jr Penetration Tester path! Linux Privilege Escalation on @tryhackme was honestly mind-blowing. Learning the many ways to escalate from basic user to root access was wild! 🚀 #PrivEsc #JrPenTester #InfoSec

Wrapped up the Anonymous room on @tryhackme. Anonymous FTP → cron-executed writable script → foothold. Found lxd group membership → privileged container → root. Shoutout to @thecybermentor & @TCMSecurity for the solid #PrivEsc course!
Wh04m1001/CVE-2025-48799 LPE - Windows Update service #redteam #privesc #pentest github.com/Wh04m1001/CVE-…
@Hac10101 Wanna exploit this giveaway together? 🔓I’ll escalate your privileges, you escalate mine - mutual authentication for that AzRTA payload! Social engineering at its finest 😏 Root access to success? Y/N 💀 #PrivEsc #SocialHack
Windows PrivEsc - I have just completed this room! Check it out: tryhackme.com/room/windows10… #tryhackme #privesc #privilege escalation #windows #windows privilege escalation #tib3rius #windows10privesc via @tryhackme

Privilege Escalation: The Dirty Pipe Linux Local Privilege Escalation Exploit #cybersecurity #privesc #cyberwarrior #Linux hackers-arise.com/post/privilege…

Modern Linux privesc flow: Capability Exploitation. Found a target running /usr/bin/python with cap_setuid+eip. One line of Python, abused the capability, instantly flipped the UID to root. Low-priv shell ➡️ root# with one command. #RedTeam #Linux #PrivEsc #Cybersecurity

Privilege Escalation: The Dirty Pipe Exploit #privesc #privilegeescaltion #dirtypipe #cybersecurity #cyberwarrior hackers-arise.com/post/privilege…

Upgrade your privilege escalation game 🚀 with the Linux PrivEsc course from the TCM Security Academy. But you need to act fast - the course (alongside Windows #PrivEsc) will be retired May 7th. Grab it before May 7th and get lifetime access, either on its own or bundled with



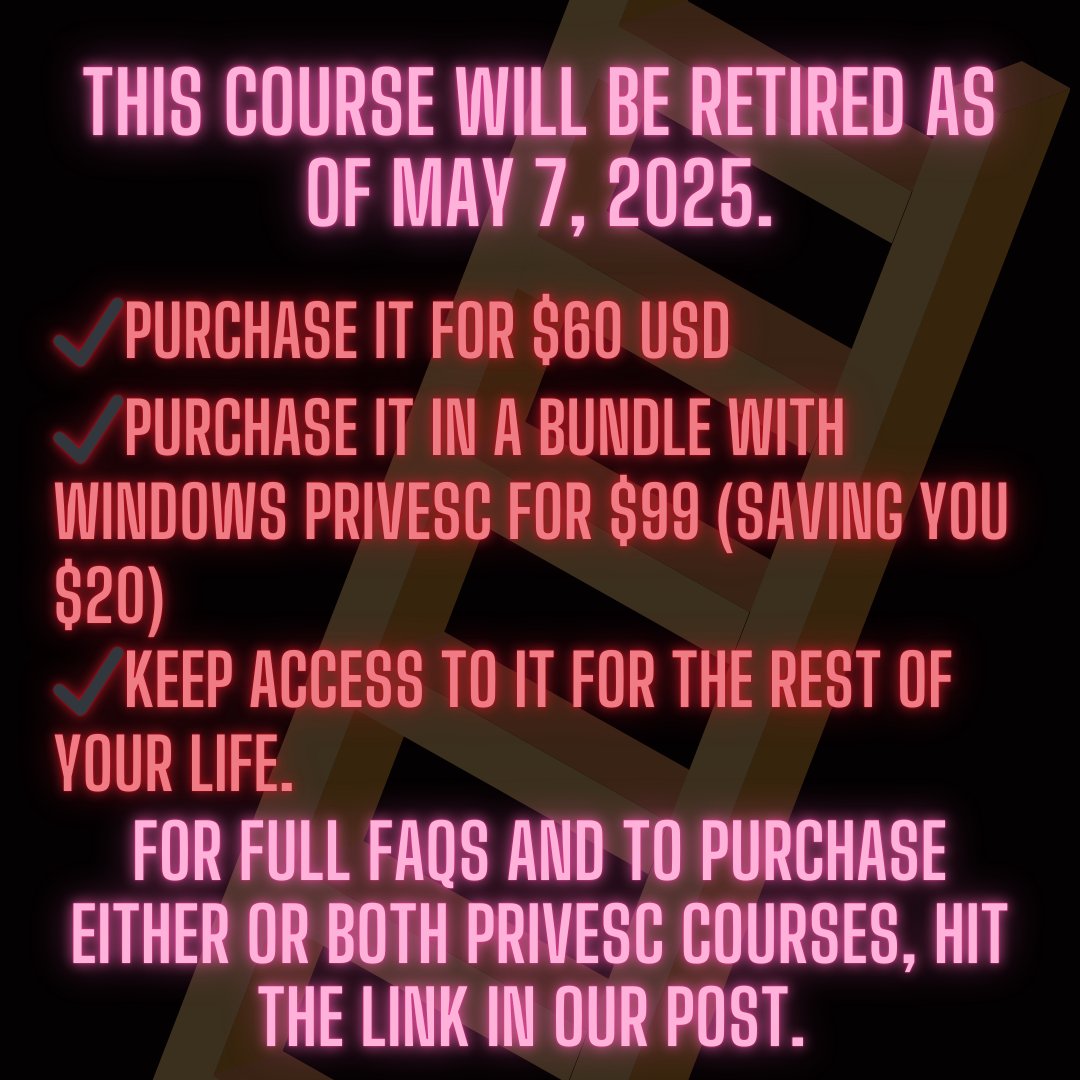
Our Linux and Windows Privilege Escalation courses will be officially retired for good on May 7th, 2025. Once retired, these courses will no longer be available, and we do not plan to remake them. You can still purchase the #PrivEsc courses until May 7th to secure lifetime

New video on my YouTube channel "Windows PrivEsc (@tryhackme walkthrough)"! youtu.be/tx-jYhqm6Jk #tryhackme #privesc #winpeas #impacket #cybersecuritytraining
When a badly coded SUID binary relies on $PATH, it's not a bug, it's a feature. Rooted. Never trust a relative path call in a privileged script. Just leveraged a PATH hijack for full system access. Easy pickings. #RedTeam #PrivEsc

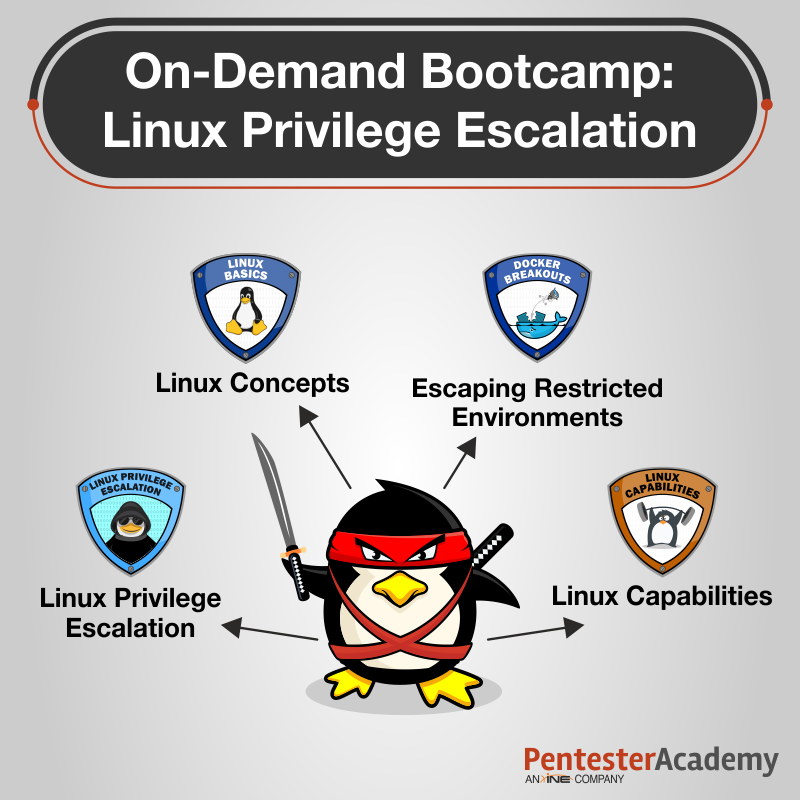
As Linux offers multi-user tenancy, the common perception is that it is impossibly hard to escalate privileges to root. Included with annual plans, our on-demand Privilege Escalation bootcamp shows you why this isn’t the case: bit.ly/3iIvASx #linux #privesc
Level up your hacking skills! Master privilege escalation techniques in our comprehensive course. From kernel exploits to SUID abuse, learn to identify and exploit vulnerabilities like a master hacker. #LinuxSecurity #PrivEsc #CyberSkills @three_cube hackers-arise.net/privilege-esca…

Ready to level up your cloud security skills? Learn IAM privilege escalation techniques! From policy manipulation to exploiting wide-ranging permissions. #CloudSecurity #IAM #PrivEsc @three_cube hackers-arise.com/post/hacking-t…

Getting close to wrapping up the Jr Penetration Tester path! Linux Privilege Escalation on @tryhackme was honestly mind-blowing. Learning the many ways to escalate from basic user to root access was wild! 🚀 #PrivEsc #JrPenTester #InfoSec

Available with annual plans, our on-demand Linux Privilege Escalation bootcamp teaches how to identify and leverage misconfigurations to perform horizontal/vertical escalation on Linux machines. See what you'll learn at bit.ly/3iIvASx #linux #privesc
[Infayer] Otro enfoque práctico para aprovechar la vulnerabilidad CVE-2022-33679 en Kerberos infayer.com/archivos/1661 #Kerberos #PrivEsc #Windows #Infayer
![UnD3sc0n0c1d0's tweet image. [Infayer] Otro enfoque práctico para aprovechar la vulnerabilidad CVE-2022-33679 en Kerberos
infayer.com/archivos/1661
#Kerberos #PrivEsc #Windows #Infayer](https://pbs.twimg.com/media/Fqp66nCWAAIGzII.jpg)
Vulnversity - Hacked by me🛡️ I have just completed this room! My tryhackme profile: tryhackme.com/p/rabiussany20… Check it out: tryhackme.com/room/vulnversi… #tryhackme #recon #privesc #webappsec #video #vulnversity via #realtryhackme
Vulnversity - I have just completed this room! Check it out: tryhackme.com/room/vulnversi… #tryhackme #recon #privesc #webappsec #video #vulnversity via @tryhackme
[Infayer] Breve revisión de la vulnerabilidad CVE-2023-21746 a.k.a. LocalPotato infayer.com/archivos/1642 #LocalPotato #PrivEsc #Windows #Infayer
![UnD3sc0n0c1d0's tweet image. [Infayer] Breve revisión de la vulnerabilidad CVE-2023-21746 a.k.a. LocalPotato
infayer.com/archivos/1642
#LocalPotato #PrivEsc #Windows #Infayer](https://pbs.twimg.com/media/Fo4WFW2WAAAlflj.png)
During a recent engagement @Mindlaess_ hacked his way through @vtigercrm which led to discover a privilege escalation and a SQL injection. Learn more in the dedicated advisories: - CVE-2024-42994 #sqli shielder.com/advisories/vti… - CVE-2024-42995 #privesc shielder.com/advisories/vti…

Something went wrong.
Something went wrong.
United States Trends
- 1. Draft Day N/A
- 2. #CantonBitgetLaunchpool N/A
- 3. Good Thursday N/A
- 4. Happy Friday Eve N/A
- 5. AIIocation N/A
- 6. Counseling N/A
- 7. #OPPOFindX9UltraTHxJoongDunk N/A
- 8. JOONGDUNK X OPPO FINDX9 N/A
- 9. And the Lord N/A
- 10. Prince Louis N/A
- 11. #ThursdayVibes N/A
- 12. #ThursdayMotivation N/A
- 13. Atreus N/A
- 14. REBECCA X OPPO FIND X9S N/A
- 15. #23Abr N/A
- 16. Thirsty Thursday N/A
- 17. St. George N/A
- 18. Sign Up Now N/A
- 19. Caruso N/A
- 20. Canton Network N/A



























































![sblmn1337's tweet image. #windows #privesc #potato #lpe #BugBounty
[ GodPotato ]
github.com/BeichenDream/G…](https://pbs.twimg.com/media/Ftjyxx8X0AM0vUR.jpg)





![IT_news_for_all's tweet image. #windows #privesc #potato
[ GodPotato ]
github.com/BeichenDream/G…... t.me/s/it_news_for_…](https://pbs.twimg.com/media/Ftaq-nwXwAIPLKe.jpg)