#securityautomation wyniki wyszukiwania
Human Security automated 40+ workflows in two weeks, eliminated 100+ hours of manual work, and cut security tool costs before the PO was even signed with BlinkOps. Now that's security automation done right 💯 #AgenticSecurity #SecurityAgents #SecurityAutomation
Accelerate disposal. Save countless team hours at data end-of-life. Watch the video: sbee.link/fkvymqu36n #BlankIsScalable #SecurityAutomation #DataProtection #DataSecurity #BlankIs
The demand for security automation has never been higher. Here are some best practices to consider when implementing security automation in your business. Learn more here hubs.la/Q02TNKp_0 #SecurityAutomation #AutomationTools #DataProtection
380 Gigs of LLM Downloaded, slowly, overnight... and then this 😂😂🖕 @CtgIntelligence #DeepSeek #Ollama #SecurityAutomation

Implementing security automation comes with several significant benefits. Security automation is a complex topic, with many different types and use cases. Learn more in our detailed guide hubs.la/Q02VPjWS0 #SecurityAutomation #AutomationTools #DataProtection
🚨 "We integrated security scanning into our pipeline... and our release cycles BLEW OUT!" Sound familiar? #AppSec #DevSecOps #SecurityAutomation #SaaS #WebSecurity #SaaSGrowth #SoftwareDevelopment #SoftwareEngineering #DevOps
Turbine Tips & Tricks: Simplify Data Transforms 💥 Too many tools, too many data schemas? In this 60-second video, Bryon Page, Swimlane Field CTO, shows how Turbine Canvas makes no-code data transformation effortless. #SecurityAutomation #NoCode #SOC
🌟 The reliability of VMRay’s analyses enables analysis of unknown #malware and #phishing threats and helps streamline #SecurityAutomation, according to the Head of Computer Security & Incident Response of a prominent European public organization. bit.ly/3P0Xkl4

Discover how AI and automation are transforming the security industry, empowering guards to predict threats and focus on strategy, not just surveillance. Ready to elevate your security game? 👉 Read more here: bit.ly/3BPfClC #SecurityAutomation #FutureOfWork

How AI and automation are reshaping security leadership - helpnetsecurity.com/2025/03/18/sec… - @tines_hq @IDC - #SOC #ArtificialIntelligence #SecurityAutomation #CyberSecurity #netsec #security #InfoSecurity #CISO #ITsecurity #CyberSecurityNews #SecurityNews
Manual Processes vs. Automation: Is Regulation Holding You Back? 🤔 At #HashiConf2024, we asked AJ Oller (AVP of Engineering @TheHartford ). Does automation actually help with security regulations? #CloudSecurity #SecurityAutomation
Our latest webinar with Tenable explores how teams are shifting from reactive patching to adaptive, autonomous solutions—without adding to their workload. Watch the full webinar on-demand: hubs.li/Q039_7C20 #AEM #SecurityAutomation #PatchManagement
Final Reminder: Our webinar is tomorrow! zoom.us/webinar/regist… Don't miss out on our webinar where we will explore how to achieve seamless #SecurityAutomation within your #SOC. Learn how VMRay integrates with #SentinelOne #EDR / #XDR for enhanced threat detection and…

Preparing for HashiCorp Consul Associate? Check out this must-see video guide → youtu.be/vOlg7SM4gzI #HashiCorp #ConsulAssociate #SecurityAutomation #HashiCorpAutomation #Consul #HashiCorpCertification
youtube.com
YouTube
Consul Associate Certification: Exam Overview, Tips & Study Plan
Manual rule writing? Out. Our Seamless IOC Ingestion feature auto-imports all threat intel indicators. No manual config. Deployment time: Hours ➡️ Minutes. Read more: hubs.la/Q03SgCH50 #ThreatIntelligence #IOCs #SecurityAutomation #SOCEfficiency #RuleWriting #Cybersecurity
🔒 The future of cybersecurity is smarter and faster. Automating defenses helps cut response times, reduce risks, and stay ahead of attackers. Embrace proactive protection today! 🔗 Download here:ow.ly/8PGa50Xm2m0 . . . #CyberSecurity #SafeAeon #SecurityAutomation
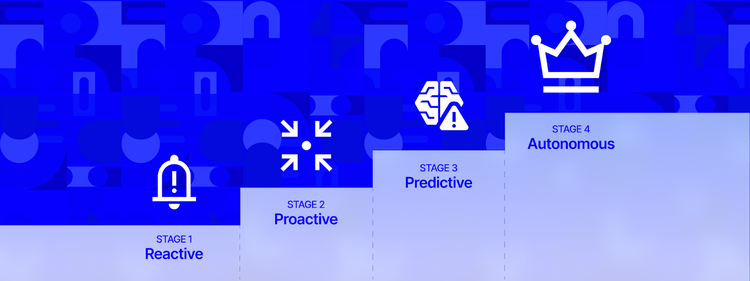
Organizations face info overload from security feeds, limiting action on threats. Recorded Future’s Threat Intelligence Maturity Model moves from Reactive to Autonomous to improve outcomes. #ThreatIntelligence #SecurityAutomation #RecordedFuture ift.tt/vq65P4U
Privileged identity failures are among the biggest threats to enterprise security today. Discover how Hire2Retire can solve this problem for you. bit.ly/49nf1q9 #Hire2Retire #IdentityManagement #SecurityAutomation #AccessControl #IAM #DataSecurity #EmployeeLifecycle
'Our Secure DevOps Services offers continuous security, compliance automation, and vulnerability scanning for faster, safer development. #DevSecOps #SecurityAutomation #FreeVulnerabilityAssessment. Book now at maksec.com'
We trust smart tech to protect our homes. Why do we rely on slow, manual systems for billions of dollars in DeFi? @Drosera_xyz is the Smart Home Security System for Web3. It doesn't just alert you to a hack, it stops it—instantly. No waiting f #SecurityAutomation #Drosera #DeFi
Human Security automated 40+ workflows in two weeks, eliminated 100+ hours of manual work, and cut security tool costs before the PO was even signed with BlinkOps. Now that's security automation done right 💯 #AgenticSecurity #SecurityAgents #SecurityAutomation
🔐 Automate security with Crossvale's Ansible solutions ✔️ Develop custom playbooks for compliance, patching, and monitoring integration ✔️ Reduce downtime and ensure consistent security posture ➡️ Learn more: hubs.ly/Q03QkTsg0 #SecurityAutomation #Ansible #Crossvale
🔐 Automate security with Crossvale's Ansible solutions ✔️ Develop custom playbooks for compliance, patching, and monitoring integration ✔️ Reduce downtime and ensure consistent security posture ➡️ Learn more: hubs.ly/Q03QkTkW0 #SecurityAutomation #Ansible #Crossvale
The new release of VMRay Platform is out! 🚀 bit.ly/3odBLDb Here are the highlights from our latest release. #securityautomation #incidentresponse #threatintelligence #cybersecurity #malware #phishing

Discover how AI and automation are transforming the security industry, empowering guards to predict threats and focus on strategy, not just surveillance. Ready to elevate your security game? 👉 Read more here: bit.ly/3BPfClC #SecurityAutomation #FutureOfWork

Looking for the best practice of Cisco password types? Check out @TimGlen2's #FAQ article to learn more: cs.co/60143C3dQ. Catch him in person at #CiscoLive Las Vegas (June 4-8) as he will be speaking on #SecurityAutomation! 😉 #NetDevOps #CiscoCommunity

To overcome the growing obstacles #OTsecurity teams face, the critical infrastructure sector should turn to #automatedsecurity solutions. bit.ly/3Zvsx2O .@swimlane #securityautomation #supplychainmanagement #security #assetmanagement #vulnerabilitymanagement

Removing the Barriers to #Security #Automation Implementation - buff.ly/3PglFCw #securityautomation #cybersecurity #ITsecurity

🌟 The reliability of VMRay’s analyses enables analysis of unknown #malware and #phishing threats and helps streamline #SecurityAutomation, according to the Head of Computer Security & Incident Response of a prominent European public organization. bit.ly/3P0Xkl4

RidgeBot® by @Ridge Security Technology Inc. identifies attack surfaces and vulnerabilities to exploit using hacker tactics, techniques, and procedures but avoids the need for additional staff or tools. See how it works: bit.ly/3H6cSj3 #SecurityAutomation #RidgeBot

How AI and automation are reshaping security leadership - helpnetsecurity.com/2025/03/18/sec… - @tines_hq @IDC - #SOC #ArtificialIntelligence #SecurityAutomation #CyberSecurity #netsec #security #InfoSecurity #CISO #ITsecurity #CyberSecurityNews #SecurityNews
Final Reminder: Our webinar is tomorrow! zoom.us/webinar/regist… Don't miss out on our webinar where we will explore how to achieve seamless #SecurityAutomation within your #SOC. Learn how VMRay integrates with #SentinelOne #EDR / #XDR for enhanced threat detection and…

VerSprite’s FORK platform revolutionizes cybersecurity with automated threat models, unifying code, runtime, and business contexts for efficient risk management and streamlined security responses. versprite.com/blog/unified-a… #Cybersecurity #ThreatModeling #SecurityAutomation

Want to peek under the hood? Join us on April 4 to learn how CloudGuard's suite of integrated tools solves the developer's challenge of securing code while protecting CI/CD pipeline at the maximum velocity. Sign up here: bit.ly/3K3hQ1k #CSPM #SecurityAutomation

Your SOC team deserves backup. On June 18, learn how #DropzoneAI reduces alert fatigue & supercharges analyst workflows. Register here → sans.org/u/1Bfe #SecurityAutomation #CyberDefense

Something went wrong.
Something went wrong.
United States Trends
- 1. Florida 97.4K posts
- 2. Texas 167K posts
- 3. Ohio State 23.3K posts
- 4. #SmallBusinessSaturday 1,435 posts
- 5. Good Saturday 30.3K posts
- 6. Kentucky 13.3K posts
- 7. #스키즈_MAMA_AOTY_축하해 6,842 posts
- 8. #StrayKidsAtMAMA2025 6,328 posts
- 9. Go Blue 6,055 posts
- 10. Go Bucks 1,816 posts
- 11. SKZ KARMA OF THE YEAR 6,519 posts
- 12. Buckeyes 3,720 posts
- 13. #MeAndTheeSeriesEP3 844K posts
- 14. #SaturdayVibes 3,188 posts
- 15. The Game 661K posts
- 16. TV Guide N/A
- 17. UTEP N/A
- 18. Successful 81.5K posts
- 19. Caturday 5,663 posts
- 20. Georgia 51.4K posts