#datasecurity search results
Aman itu bukan feeling. Tapi dibuktikan.🔐 Tanpa Pentest, kamu nggak pernah benar-benar tahu: ❌ Di mana celah sistem kamu ❌ Kapan serangan datang ❌ Seberapa besar risiko kerugian 📩 Konsultasi & FREE Pentest sekarang +62 815-8825-003 #CyberSecurity #Pentest #DataSecurity


🔐 Fully Automated BitLocker. Zero Headaches. Self-healing encryption, auto key backup, tamper detection & weekly reporting—your data stays protected without manual effort. 🔗 techpio.com/plugins/produc… #BitLocker #DataSecurity #CyberSecurity #MSP #BackupManagement #TechPIO

VECT 2.0 ransomware has a flaw that destroys large files instead of encrypting them, permanently losing data, what's the real motive behind this malfunction, an honest error or intentional sabotage #ransomware #datasecurity #malware
When the breach happens, what will you tell your board? That you didn't know what employees were uploading? That you kept pushing it off? Free 5-min risk assessment: tinyurl.com/msu9eexu Find out if you're vulnerable. #AIRisk #DataSecurity #leadership

♻️ What happens after your e-waste is picked up? Sorting, secure data handling, refurbishment, and material recovery — all handled through R2V3 & ISO-certified processes. 👉 Read more: #EWaste #DataSecurity #EvergreenITSolutions wix.to/4oLd1IU
Where is your compliance data stored? Many tools quietly move it to their cloud. With Verify, you stay in control and choose where it runs. AWS, Azure, Google Cloud, or your own servers. 👉 Learn More: fizentech.com/verify-complia… #Compliance #DataSecurity #FinTech #Verify #Fizen




Data Governance Lead East Midlands | £60–80k + Bonus Experience working with large datasets & supporting business insight highly desirable. #DataGovernance #CyberRisk #DataSecurity #BI paiger.link/260000034
The companies that collect your data have more restrictions than random strangers online. If your LinkedIn info isn't protected, it's a scary world. Online data can be used for AI, inferences, and more without consent. #Privacy #DataSecurity
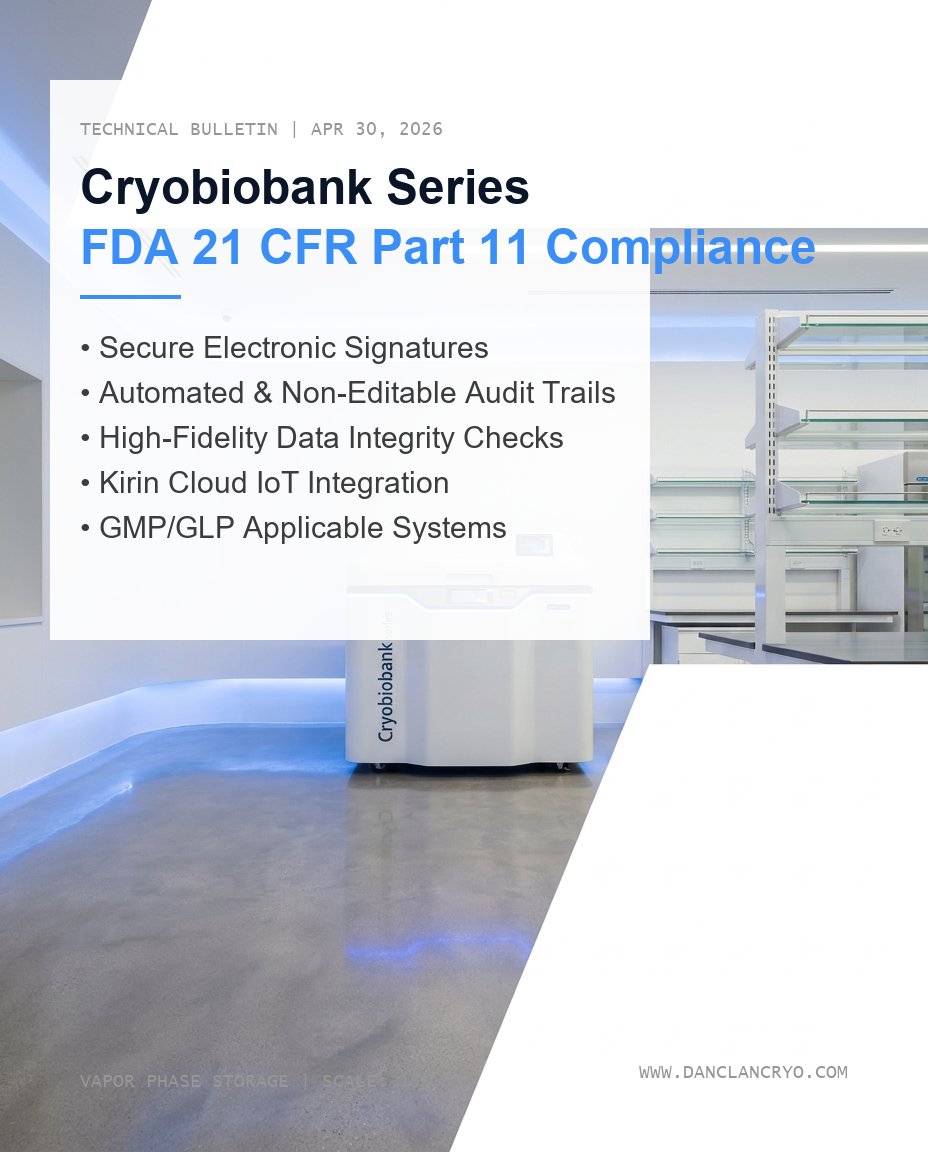
Scientific Fact: Data is as perishable as samples. 🧬🛡️ Without a secure, time-stamped audit trail, your research value drops. Danclan’s Kirin Cloud IoT delivers FDA 21 CFR Part 11 integrity on autopilot. Trust the process. Secure the truth. ❄️📈 #FDA #DataSecurity #Danclan
Ransomware isn’t just encryption anymore—it’s extortion. 🔐 Learn how modern attacks work and how to protect your business. 👉 Read now: csm-int.com/blog/f/ransomw… #Ransomware #Cybersecurity #DataSecurity #ITSecurity
Speed increases data collection. More data collected means more exposure. Brian Degon – 23 years as a data analyst – walks through how AI amplifies a risk already a burden to businesses … [5 min. read] bryl.us/rc7j #DataSecurity #AI
![BryleySystems's tweet image. Speed increases data collection. More data collected means more exposure. Brian Degon – 23 years as a data analyst – walks through how AI amplifies a risk already a burden to businesses … [5 min. read] bryl.us/rc7j #DataSecurity #AI](https://pbs.twimg.com/media/HHJ3uRSXwAADZ1x.jpg)
If payment systems go down, everything stops. Gas. Groceries. Daily life. That’s what @BankannaRb is protecting. With Cohesity, they’re keeping critical systems running and ready when it matters most 👉cohesity.co/4ce1xOs #CyberResilience #DataSecurity #BackupAndRecovery
A security flaw in @RobinhoodApp was exploited to send phishing emails that appeared legitimate, bypassing authentication checks & tricking users into fake alerts. 𝐑𝐞𝐚𝐝 𝐭𝐡𝐞 𝐟𝐮𝐥𝐥 𝐧𝐞𝐰𝐬: tinyurl.com/5xa4skf3 #CyberSecurity #Phishing #DataSecurity #CyberThreats

🔐📊 Company safety is crucial when it comes to data. Learn more about our services: 🌐 aegstrategicdata.it #DataSecurity #CompanySafety #CyberSecurity
Understanding the different types of cyber attacks can help individuals and businesses strengthen their digital defense and reduce risks online. #CyberSecurity #CyberAttack #DataSecurity #InformationSecurity #Ransomware #Phishing #Malware #Hacking #NetworkSecurity

Would you store your tools in an unsecured van? Then why store your records on an uncertified platform? CE Plus and IASME certified. Your digital records deserve the same protection as your kit. #DataSecurity #CyberEssentials #TradeTools #ToolTheft #mysafedocs
We’ve got the experience, skills, and knowledge to handle any #networking problem. We can help design, implement, scale, and maintain a #securenetwork throughout your organization. Contact us today! #datasecurity #networksecurity

@bigidsecure Expands DSPM to Secure Markdown Files in AI Workflows Read more: cybertechnologyinsights.com/data-security/… #DataSecurity #CyberSecurity #AI #DSPM #DataProtection

Rushing to adopt AI without a safety net? Don’t let your chatbot leak trade secrets or private data. AI Governance is the "seatbelt" your tech needs: 🎯 Control 🔒 Security ✅ Compliance Keep your data yours. Learn how: 🔎 optimum-web.com/ai-shield/ai-g… #aigovernance #datasecurity

♻️ What happens after your e-waste is picked up? Sorting, secure data handling, refurbishment, and material recovery — all handled through R2V3 & ISO-certified processes. 👉 Read more: #EWaste #DataSecurity #EvergreenITSolutions wix.to/4oLd1IU
Is your enterprise AI secure? 🔒 Master AI Data Security & Compliance to protect your business assets. Learn how: encorp.ai/blog/ai-data-s… #AI #DataSecurity #Tech
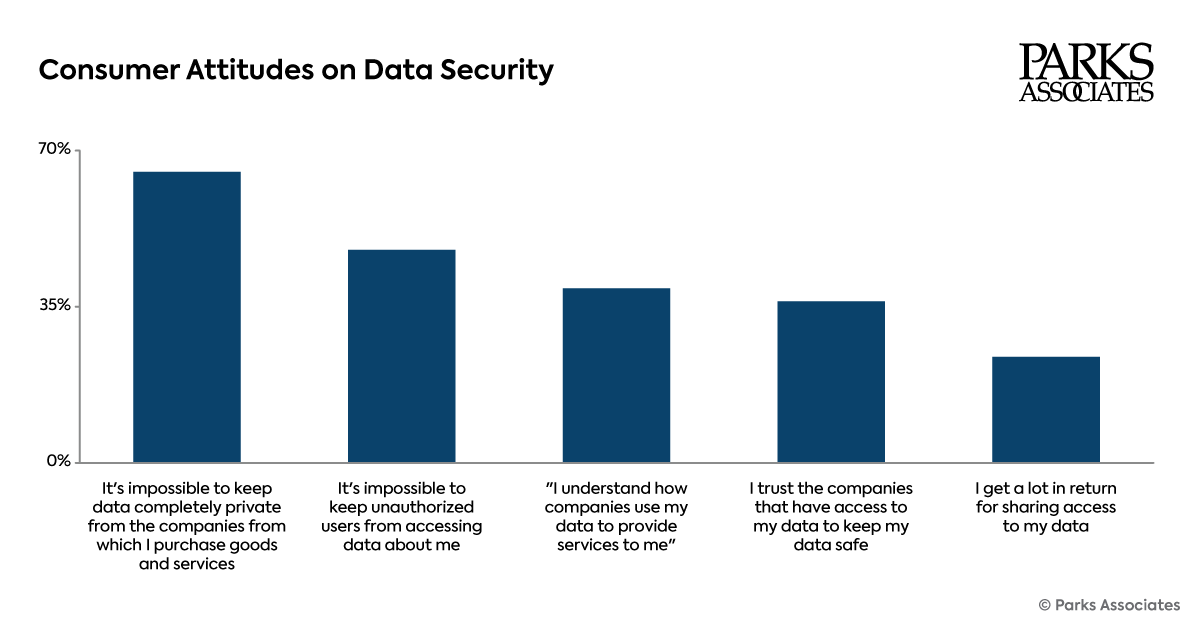
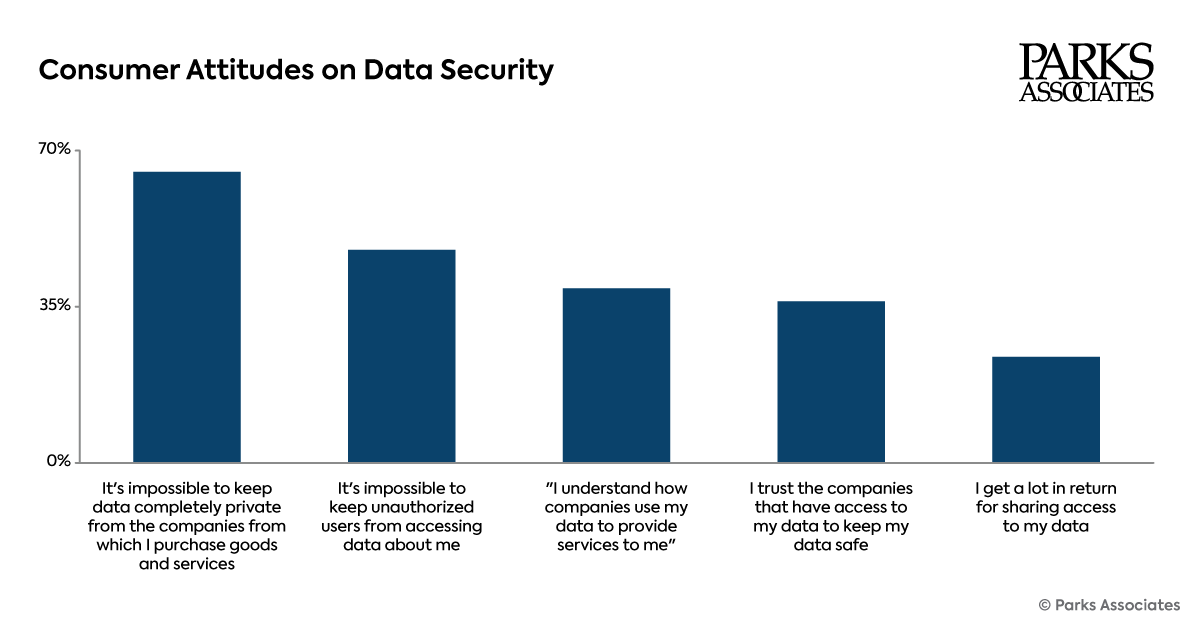
The flagship study tracks sentiment, behaviors, & expectations related to privacy & #datasecurity across #smarthome, #streaming, health, & #AIservices: tinyurl.com/y6uasjn5 Join us at #CONNUS26 to hear from top executives & innovators #pressrelease: tinyurl.com/8cxnfpfk
Where is your compliance data stored? Many tools quietly move it to their cloud. With Verify, you stay in control and choose where it runs. AWS, Azure, Google Cloud, or your own servers. 👉 Learn More: fizentech.com/verify-complia… #Compliance #DataSecurity #FinTech #Verify #Fizen




Where is your compliance data stored? Many tools quietly move it to their cloud. With Verify, you stay in control and choose where it runs. AWS, Azure, Google Cloud, or your own servers. 👉 Learn More: xduce.com/verify/ #Compliance #DataSecurity #FinTech #Verify #XDuce


China blocked Meta’s $2B bid for Manus, signaling a hard red line on data security and foreign tech cross-border deals. Expect tighter scrutiny on AI assets and data transfer rules shaping global investments. #ChinaTech #AIForeignInvestment #DataSecurity… ift.tt/LalSneJ
khabarasia.com
China Blocks Meta’s $2B AI Startup Bid, Drawing a ‘Red Line’ on Data Security - Khabar Asia
China has halted Meta's $2 billion acquisition of AI startup Manus, citing data security concerns. This marks a first in blocking foreign investment in the AI sector, drawing a clear regulatory line.
Don't get caught in a phishing scam! Delete and block those phishy emails and keep your business safe. Train your staff to spot and properly respond to ransomware threats. 📱 888-891-4201 💻 KTConnections.com #Phishing #Scams #DataSecurity #KTConnections

Agentic AI is no longer experimental. It’s acting, deciding, and accessing data. Is your data security ready for that shift? Can’t make it live? Register anyway and we’ll send you the recording. Save your spot: offer.comforte.com/agentic-ai-is-… #ai #datasecurity #agenticai #cybersecurity

🔐 Fully Automated BitLocker. Zero Headaches. Self-healing encryption, auto key backup, tamper detection & weekly reporting—your data stays protected without manual effort. 🔗 techpio.com/plugins/produc… #BitLocker #DataSecurity #CyberSecurity #MSP #BackupManagement #TechPIO

DataShield’s Records Management solutions help businesses securely store, organize, and access important documents without the burden of on-site clutter. datashieldcorp.com/records-manage… #RecordsManagement #BusinessOperations #DataSecurity #Compliance #OfficeEfficiency @shredvault

Data Governance Lead East Midlands | £60–80k + Bonus Experience working with large datasets & supporting business insight highly desirable. #DataGovernance #CyberRisk #DataSecurity #BI paiger.link/260000034
Ransomware isn’t just encryption anymore—it’s extortion. 🔐 Learn how modern attacks work and how to protect your business. 👉 Read now: csm-int.com/blog/f/ransomw… #Ransomware #Cybersecurity #DataSecurity #ITSecurity
Granting AI agents access to your data comes with severe risks. You should ONLY connect these automated systems to your live data if you have strict security boundaries. Here are just a few of the permission controls you MUST implement: #AI2026 #datasecurity #business




We’ve got the experience, skills, and knowledge to handle any #networking problem. We can help design, implement, scale, and maintain a #securenetwork throughout your organization. Contact us today! #datasecurity #networksecurity

Speed increases data collection. More data collected means more exposure. Brian Degon – 23 years as a data analyst – walks through how AI amplifies a risk already a burden to businesses … [5 min. read] bryl.us/rc7j #DataSecurity #AI
![BryleySystems's tweet image. Speed increases data collection. More data collected means more exposure. Brian Degon – 23 years as a data analyst – walks through how AI amplifies a risk already a burden to businesses … [5 min. read] bryl.us/rc7j #DataSecurity #AI](https://pbs.twimg.com/media/HHJ3uRSXwAADZ1x.jpg)
Varonis is pushing customers to SaaS. Lepide lets you choose your deployment. See how Lepide compares and why some teams are switching. lepide.com/blog/lepide-da… #DataSecurity #SaaS #Lepide #Varonis
At Dictalogic, compliance isn't an afterthought; it's our foundation. HIPAA compliant, ISO/IEC 27001 certified, and UKAS accredited, so your data is always secure. #HIPAACompliant #ISO27001 #DataSecurity #Dictalogic #SecureDictation

Understanding the different types of cyber attacks can help individuals and businesses strengthen their digital defense and reduce risks online. #CyberSecurity #CyberAttack #DataSecurity #InformationSecurity #Ransomware #Phishing #Malware #Hacking #NetworkSecurity

Jazz Highlights Need for IP Safeguards as AI Data Leaks Increase Read more: bit.ly/4u1ceKN #AI #DataSecurity #IPProtection #CyberSecurity #DataPrivacy

@bigidsecure Expands DSPM to Secure Markdown Files in AI Workflows Read more: cybertechnologyinsights.com/data-security/… #DataSecurity #CyberSecurity #AI #DSPM #DataProtection

‘नो लोकल स्टोरेज’ मॉडल से होगी गणना, डेटा सीधे सर्वर पर अपलोड होगा... हर स्टेप पर ऑटो-डिलीट, 6 लेयर सुरक्षा में रहेगा हर परिवार का ब्योरा #Census2026 #DataSecurity #DigitalIndia #Chhattisgarh अधिक खबरें और ई-पेपर पढ़ने के लिए दैनिक भास्कर एप इंस्टॉल करें -

💎 La información confidencial es el tesoro de tu empresa. ¡Ponle el mejor candado! 🔒 Domingos 3, 10, 17, y 24 de Mayo 2026. De 9:00 am a 12:00 pm (UTC -05:00). 📲 WhatsApp: wa.me/51949304030 🌎 Info: reydes.com/archivos/curso… #datasecurity #zerotrust #vulnerability

🎖️ El Curso de Ciberseguridad está permanente disponible en el aula virtual para acceso inmediato. 📲 WhatsApp: wa.me/51949304030 🌐 reydes.com/e/Curso_de_Cib… #datasecurity #zerotrust #vulnerability #cyberattack #threatintel #databreach #cybersecurity

The flagship study tracks sentiment, behaviors, & expectations related to privacy & #datasecurity across #smarthome, #streaming, health, & #AIservices: tinyurl.com/y6uasjn5 Join us at #CONNUS26 to hear from top executives & innovators #pressrelease: tinyurl.com/8cxnfpfk
Which is safer storage? (A) Local device (B) Cloud encrypted (C) External drive Pick 👇 #DataSecurity

Gmail Address Change Feature Fails to Address Core Security Risks, Report Warns cysecurity.news/2026/04/gmail-… #CyberSecurity #Cybersecurity #datasecurity

Why the InfoSec team cannot save your feature, and how to stop treating security like a compliance checklist. #security #datasecurity...Show more

India Bans Chinese Cameras at Highway Tolls Over Data Security Fears cysecurity.news/2026/04/india-… #ChineseCameras #CyberSecurity #datasecurity

It’s critical to keep your company safe and sound from internal cyber attacks. How? Watch the video by @LindaGrass0 > bit.ly/30kI4J6 #CyberAttacks #DataSecurity #CyberSecurity

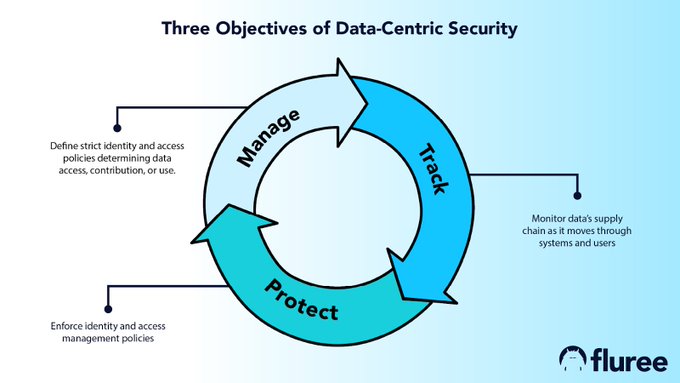
The Data-Centric philosophy involves moving data management responsibilities from the application tier to the data tier — and security is no exception. @FlureePBC bit.ly/3xSa43k Rt: @antgrasso #DataSecurity #DataGovernance #IAM
We're heading to Chicago next week for @Nutanix .NEXT! We'll have live demos, cyber resilience experts, a raffle worth staying for. Come find us 👉 cohesity.co/3NKfRVw #NEXTconf #CyberResilience #DataSecurity #AI




China Mobile strengthens cyber and public opinion security, delivering AI-driven monitoring and real-time threat defense to safeguard enterprises in the digital era. #AI #FinTech #DataSecurity #RiskManagement #CyberSecurity

Technology analyst firm @GigaOm evaluated 19 #datasecurity vendors for its Radar for Data Security Platforms (DSP) v3 report. Only 3️⃣ achieved the Outperformer rating—Proofpoint was one of them. 🏆 Read why our unified #datasecurity solution stands out. proofpoint.com/us/resources/a…

Something went wrong.
Something went wrong.
United States Trends
- 1. Resident Evil N/A
- 2. Ryan Walker N/A
- 3. Toy Story N/A
- 4. JP Morgan N/A
- 5. Term N/A
- 6. Platner N/A
- 7. FLY ME OUT N/A
- 8. Casey Means N/A
- 9. Payamps N/A
- 10. Surgeon General N/A
- 11. Justin Crawford N/A
- 12. Maine N/A
- 13. Jeremiah Jackson N/A
- 14. Collins N/A
- 15. James Wood N/A
- 16. MJ Melendez N/A
- 17. Paul Skenes N/A
- 18. Austin Riley N/A
- 19. Jose Suarez N/A
- 20. Brandon Woodruff N/A