#exploitdev 搜尋結果
New article alert : ek0msUSB medium.com/@ekoms1/ek0msu… #hacker #greyhat #exploitdev #commandandcontrol #payloads




I’m happy to announce that I passed OSED from @offsectraining 😍😍 I just got the email and man IT FELT SO GOOD #CyberSecurity #exploitdev

Happy New Year 2025! #infosec #CyberSec #ExploitDev #Hacker #Bug #bugbountyhunter #vulnerabilityResearcher #ReverseEngineering #Binex

If you're exploiting a driver offering R/W access to physical memory on Win11 24H2, you can leverage this simple trick to circumvent kernel address leak restrictions and retrieve the kernel base address :p xacone.github.io/kaslr_leak_24h… #exploitdev #driverexploitation
Mastering buffer overflows in Vulnserver is essential for exploit development. WinDBG aids in debugging vulnerabilities by controlling EIP and generating shellcode. A must-learn for secure environments! 🔍⚙️ #ExploitDev #BufferOverflow link: ift.tt/fFk6AGK

This should be the final set of labs published publicly. That's all folks for now... #RE #Offsec #ExploitDev #SoftwareExploitation exploitation.ashemery.com



Interested in Software Exploitation? This course is for you and will take you from knowing nothing, to understanding how exploits work and how to write them... I hope it will be useful to someone out there! #Offsec #Cybersecurity #ExploitDev #Debugging youtube.com/watch?v=5GGyFb…

⚠️ Afraid of public classes? 🔒 Corelan Academy = private, intense, small-group exploit dev training 2–8 ppl • one-on-one access • flexible timing • competitive pricing • Stack & Heap DM or reply interested #corelan #exploitdev #training #heap #stack #corelanacademy
Bypassing PIE with partial overwrite? 🔥 Instead of guessing full addresses, just overwrite specific bytes to align with predictable offsets. Precision > brute force. A reminder that security evolves, and so must we. 🛡️ #CyberSecurity #ExploitDev #ReverseEngineering


Pwning LLaMA.cpp RPC Server #LLAMACpp #RPCServer #ExploitDev #CTF pwner.gg/2024/10/03/lla…
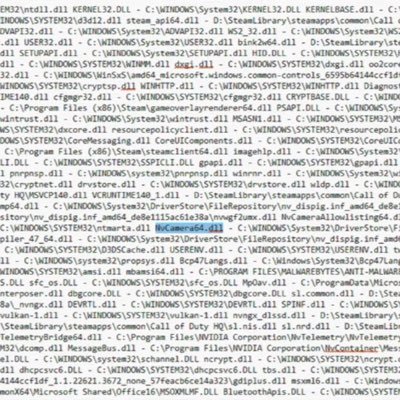
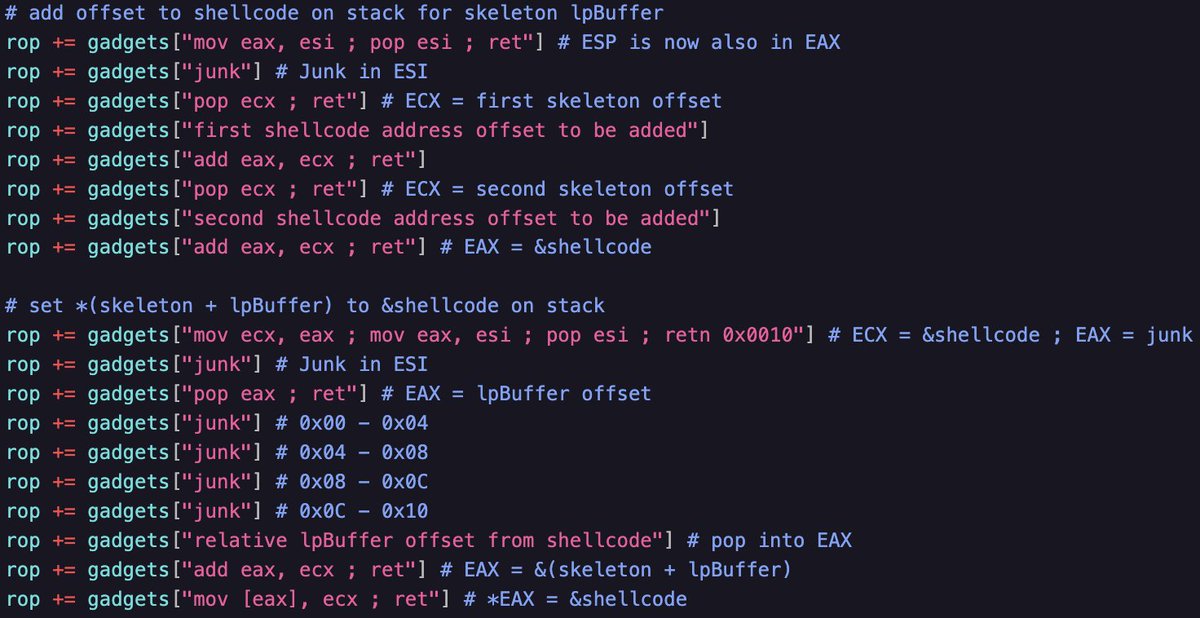
Hand-crafted ROP chain 🛠️! Had limited gadgets, so I used an IAT entry for HeapAlloc and calculated the VirtualAllocStub RVA offset. Got creative without ASLR and possibly should've used a read primitive. Details in the gist! #ROP #ExploitDev #osed gist.githubusercontent.com/snowcra5h/a7c1…

🇧🇪 Belgian Roots. Global Impact. 🌍 Corelan delivers world-class exploit dev training for Windows: 🔹 Stack Smashing 🔹 Heap Masterclass Built in Europe. Respected worldwide. Sign up 👉 bit.ly/corelan-traini… #CyberSecurity #ExploitDev #MadeInBelgium
Important note to those new to this account. The course below is completely FREE. I know someone (maybe more) has ripped the videos & probably now the labs & is selling them on @udemy. Please do not pay for this course, it is FREE! #ExploitDev #Offsec exploitation.ashemery.com
And we did it ! 🙌🏽 We brought the great @corelanc0d3r to teach a master class of exploit development for the first time in Brazil and Latin America. 😎 Many thx Peter for this amazing experience. #exploitdev #redteam #gohacking #corelan #cyber


This week was the last public class of 2023, we’re already filling up the agenda for 2024. However, we still have some timeslots for private classes. (either at your company or in Belgium, for small groups). Interested? DM for info! #corelan #exploitdev #windows11 #stack #heap

I was driving back home and never thought this last #offsec #ExploitDev #SoftwareExploitation share for 2022 will go this viral. THANKS to all those who Retweeted/Liked/Commented/etc... Wishing you all a great 2023 ...

Uploaded all my Offensive Security & Reverse Engineering (OSRE) course labs (docx) to my repo found below. Most of them have very detailed instructions and should be great to get you started in Software Exploitation. 1/n #Offsec #SoftwareExploitation #RE exploitation.ashemery.com

🚨 Released a full SEH exploit chain for DeepFreeze 8! With custom shellcode and ROP chain. Software was fully reversed, and an SEH vuln discovered studying for the #OSED 💪Blog write-up coming soon.🔍github.com/snowcra5h/Faro… #CyberSecurity #ExploitDev
⚠️ Afraid of public classes? 🔒 Corelan Academy = private, intense, small-group exploit dev training 2–8 ppl • one-on-one access • flexible timing • competitive pricing • Stack & Heap DM or reply interested #corelan #exploitdev #training #heap #stack #corelanacademy
⚠️ Afraid of public classes? 🔒 Corelan Academy = private, intense, small-group exploit dev training 2–8 ppl • one-on-one access • flexible timing • competitive pricing • Stack & Heap DM or reply interested #corelan #exploitdev #training #heap #stack #corelanacademy
New article alert : ek0msUSB medium.com/@ekoms1/ek0msu… #hacker #greyhat #exploitdev #commandandcontrol #payloads




New whitepaper: Polymorphic shellcode bypasses on modern architectures—evasion techniques, detection gaps, and practical defenses. Read: github.com/MottaSec/White… #SecurityResearch #ExploitDev #BlueTeam
CVE-2025-52915 assigned - my first vulnerability!🥳 A classic BYOVD case: kernel driver with unrestricted process termination. Vendor coordination turned out more challenging than the exploit itself. Technical write-up: blacksnufkin.github.io/posts/BYOVD-CV… #ExploitDev #CVE #BYOVD #RedTeam
Privilege escalation isn't always about the shell. Kernel memory leaks can offer direct paths to root access. Details: versprite.com/blog/the-shell… #PrivilegeEscalation #LinuxSecurity #ExploitDev
versprite.com
The Shell Was Restricted, but the Kernel Memory Was Wide Open - VerSprite
Introduction In embedded device security research, some of the most interesting vulnerabilities emerge from administrative features that were never
NEW: Digital Demonology Grimoire - A dark exploration into buffer overflow exploitation & shellcode analysis Perfect reading for👹 github.com/h3xorc1sm/digi… #DEFCON #ExploitDev #Shellcode #BufferOverflow #InfoSec #HackTheGibson
"Those who gaze into the assembler, take care that the assembler does not gaze also into them." The silicon souls whisper their secrets... github.com/h3xorc1sm/digi… #DEFCON #ExploitDev #DigitalDemonology
We dissect a DFG compiler bug we discovered in Safari/WebKit. This post covers root cause, impact, and technical analysis: blog.exodusintel.com/2025/08/04/oop… #WebKit #VulnerabilityResearch #ExploitDev #Safari #CyberSecurity #ExodusIntel
🔔 Reminder: Zürich, Corelan Stack is coming Oct 7–10, 2025 ✅ No nonsense, No BS ✅ Just real-world exploit dev skills 🎟️ eventcreate.com/e/sigs-corelan… 💛 RT appreciated! #corelan #win11 #exploitdev
🔔 Reminder: Zürich, Corelan Stack is coming Oct 7–10, 2025 ✅ No nonsense, No BS ✅ Just real-world exploit dev skills 🎟️ eventcreate.com/e/sigs-corelan… 💛 RT appreciated! #corelan #win11 #exploitdev
Happy New Year 2025! #infosec #CyberSec #ExploitDev #Hacker #Bug #bugbountyhunter #vulnerabilityResearcher #ReverseEngineering #Binex

I’m happy to announce that I passed OSED from @offsectraining 😍😍 I just got the email and man IT FELT SO GOOD #CyberSecurity #exploitdev

It's truly beautiful.🥹Avoiding bad characters, compensating for limited gadgets. It's like crafting a piece of art🎨. Challenges like this make the #OSED so rewarding!💪Got any tricks up your sleeve? Share them with me. Friday is exam day. #ExploitDev #ArtInCode #infosecurity
Mastering buffer overflows in Vulnserver is essential for exploit development. WinDBG aids in debugging vulnerabilities by controlling EIP and generating shellcode. A must-learn for secure environments! 🔍⚙️ #ExploitDev #BufferOverflow link: ift.tt/fFk6AGK

New article alert : ek0msUSB medium.com/@ekoms1/ek0msu… #hacker #greyhat #exploitdev #commandandcontrol #payloads




Bypassing PIE with partial overwrite? 🔥 Instead of guessing full addresses, just overwrite specific bytes to align with predictable offsets. Precision > brute force. A reminder that security evolves, and so must we. 🛡️ #CyberSecurity #ExploitDev #ReverseEngineering


This should be the final set of labs published publicly. That's all folks for now... #RE #Offsec #ExploitDev #SoftwareExploitation exploitation.ashemery.com



Education is power! corelan-training.com/index.php/trai… #nevergiveup #exploitdev #windows11 #stack #heap @corelanc0d3r

All the Assembly and #RE labs have now been shared. I just need to find the reference to the Crackme(s) I used and then it should be 100% complete. #Offsec #ExploitDev #SoftwareExploitation exploitation.ashemery.com

Hand-crafted ROP chain 🛠️! Had limited gadgets, so I used an IAT entry for HeapAlloc and calculated the VirtualAllocStub RVA offset. Got creative without ASLR and possibly should've used a read primitive. Details in the gist! #ROP #ExploitDev #osed gist.githubusercontent.com/snowcra5h/a7c1…

The whole course, labs, videos, etc can be found below. #Cybersecurity #Offsec #ExploitDev #Debugging #Reversing exploitation.ashemery.com

I really enjoy teaching private classes! Even if you're just a small group (min. 4), willing to travel to Belgium, we can make it happen! I still have some timeslots in November & December. DM if interested @corelanconsult #windows #exploitdev #corelan #nevergiveup

Built my own 64-bit ELF packer — something I always wanted to try. XOR encrypts the .text section with a dynamic key and injects a custom stub in new PT_LOAD segment github.com/0x3xploit/entr… #Linux #ELF #Exploitdev #ReverseEngineering #RedTeam #BinaryAnalysis #infosec



And we did it ! 🙌🏽 We brought the great @corelanc0d3r to teach a master class of exploit development for the first time in Brazil and Latin America. 😎 Many thx Peter for this amazing experience. #exploitdev #redteam #gohacking #corelan #cyber


Interested in Software Exploitation? This course is for you and will take you from knowing nothing, to understanding how exploits work and how to write them... I hope it will be useful to someone out there! #Offsec #Cybersecurity #ExploitDev #Debugging youtube.com/watch?v=5GGyFb…

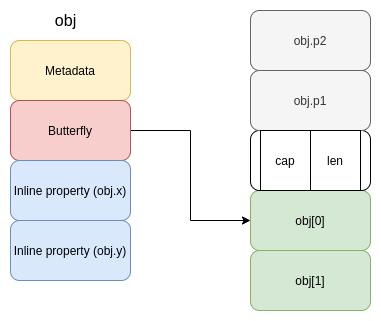
🧠 Heap exploits today = brains > brute force. Leaks, UAFs, type confusion—APT-level tactics. Is your defense still stuck in 2015? 👇 What’s your go-to heap hardening move? #CyberSecurity #ExploitDev 👉️ sec.co/blog/modern-he…

ONE more chance this year to take our popular Bootcamp. High-quality materials, real class, real instructor (AND the perfect prep for our heap exploitation class). Seats are selling fast! What are you waiting for? deep-conference.com/predeep-bootca… #corelan#windows11 #exploitdev

Officially #OSED certified! I've conquered the Windows User Mode Exploit Development exam and earned the Offensive Security Exploit Developer (OSED) certification. Huge thanks to @offsectraining! #ExploitDev #ReverseEngineering #TryHarder

YES! 🔥 The legendary Corelan (@corelanc0d3r) exploit development training is happening in ROME! 🇮🇹 Absolutely stoked about this opportunity right here in Italy. Time to level up those #ExploitDev skills! 💪 #Corelan #CyberSecurity #InfoSec #Reversing #Rome #Hacking #Cyber

Something went wrong.
Something went wrong.
United States Trends
- 1. Giannis 55.5K posts
- 2. Tosin 62.7K posts
- 3. Spotify 1.53M posts
- 4. Leeds 95.6K posts
- 5. Bucks 35.9K posts
- 6. Maresca 48.4K posts
- 7. Milwaukee 16.8K posts
- 8. Danny Phantom 6,210 posts
- 9. #WhyIChime 1,953 posts
- 10. Mark Andrews 1,651 posts
- 11. Wirtz 34.8K posts
- 12. Isaiah Likely N/A
- 13. Sunderland 45K posts
- 14. Delap 17K posts
- 15. Purple 53.1K posts
- 16. Poison Ivy 1,680 posts
- 17. Steve Cropper N/A
- 18. Chiesa 12.3K posts
- 19. Jack Smith 38.2K posts
- 20. Cedric Mullins N/A