#flarevm risultati di ricerca
Exploring Suricata in Flare VM! Learn to analyze pcap files, generate alerts, and tackle potential errors while processing offline. Enhance your malware analysis toolkit! 🔍🛡️ #Suricata #FlareVM #PCAPAnalysis #Youtube link: ift.tt/94LSDEP
It is an easy, albeit manual, pivot for people triaging malware and doing research and all quickly doable within @FireEye's own #FlareVM github.com/fireeye/flare-…. Hope that was instructive (or at least a good reminder) for life in .NET.
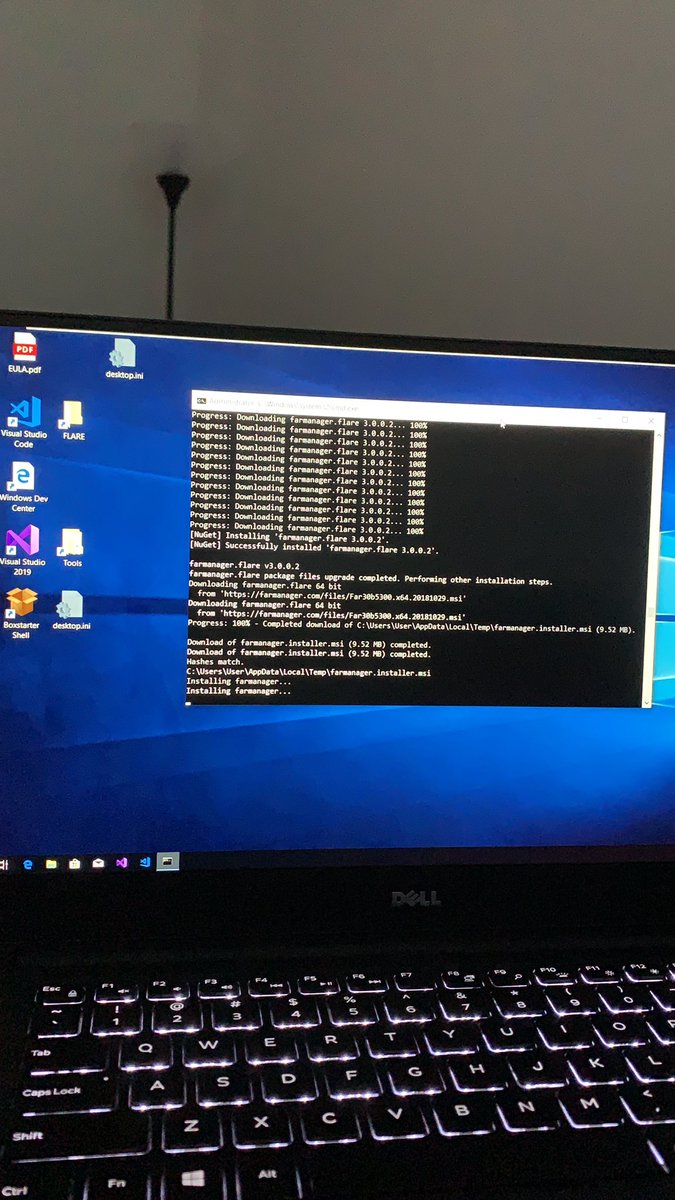
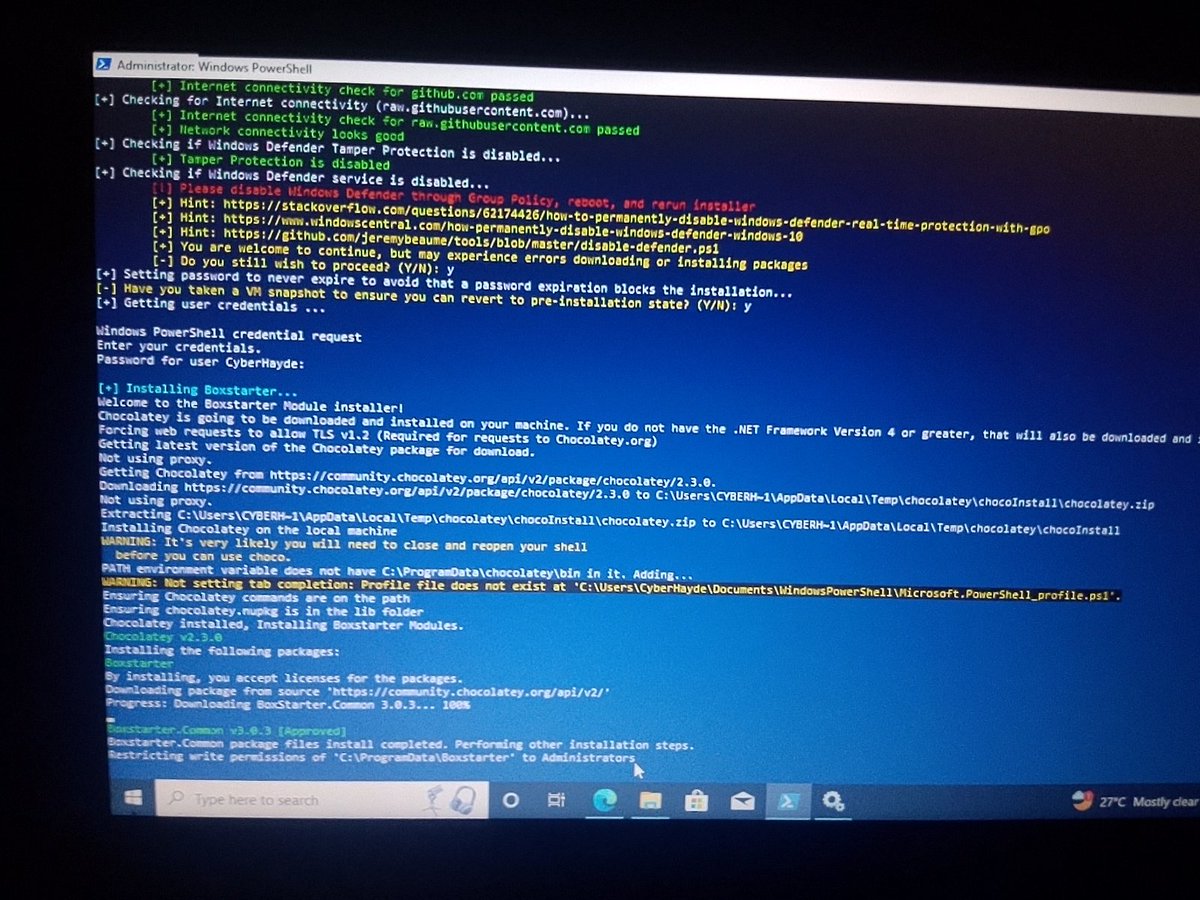
🔴 We are live! Sort of embarrassing… I was going to do some debugging but my free Windows VM expired so instead we will just be chilling and installing #FLAREVM 😇 Join if you just want to hang out and chat 😸😸 twitch.tv/oalabslive
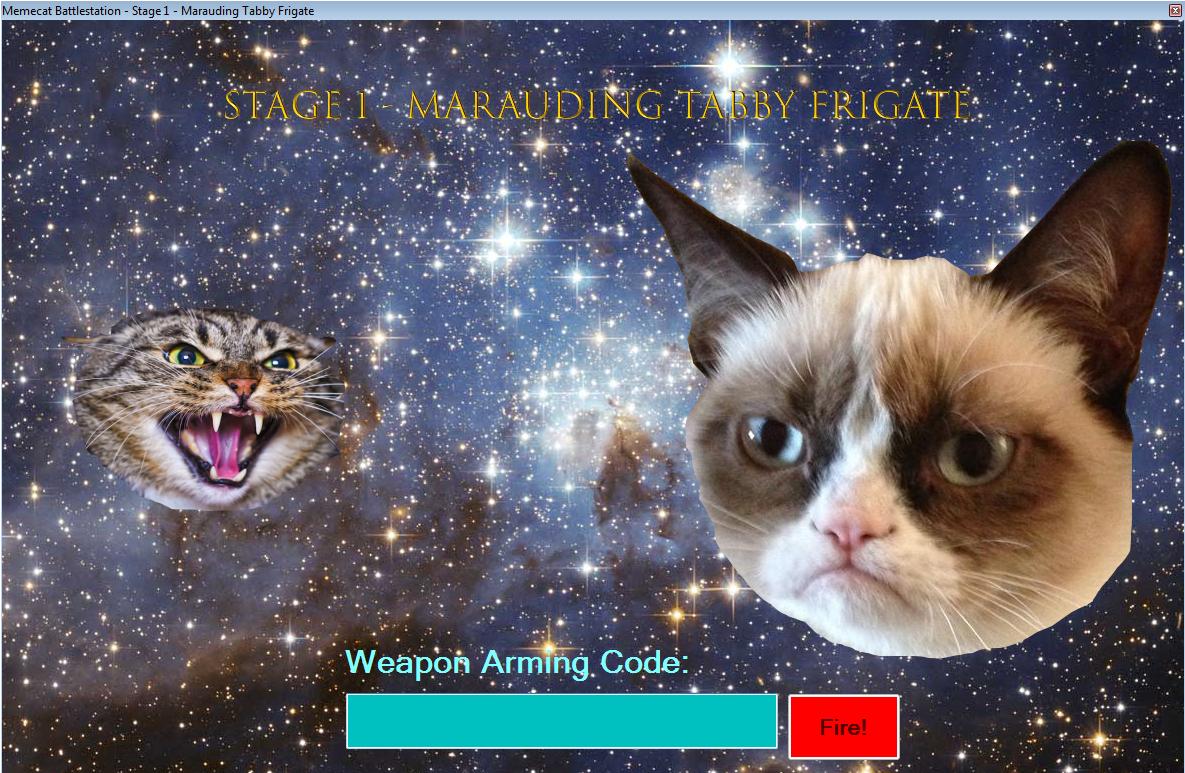
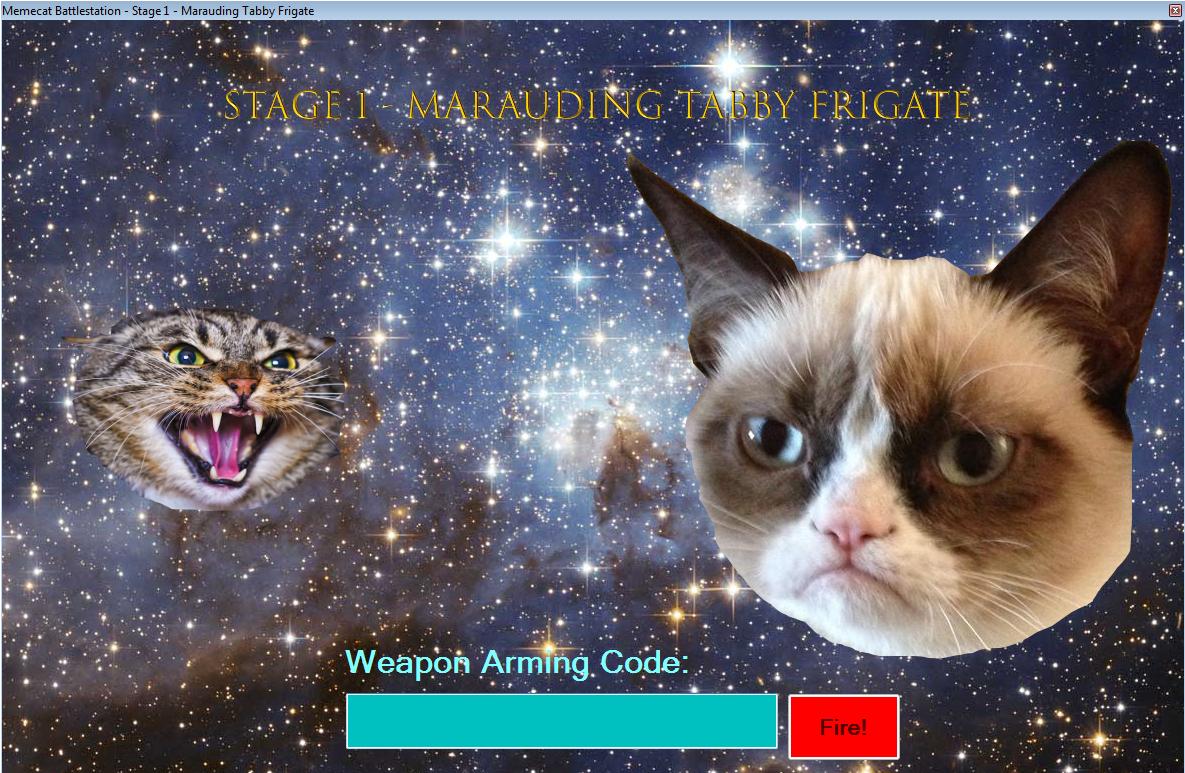
Booted up #FLAREvm and MemeCatBattlestation.exe is glorious. >> Stage 1 - Marauding Tabby Frigate! #FLAREon6 bonus level from #BHUSA2019
#FLAREVM updated with many new malware analysis tools and a powershell installer. Check it out flarevm.info
@_odino_ grazie della segnalazione, purtroppo #flarevm non offre gli stessi servizi di gandi.net: raid60, cloud, aumento potenza, etc...
#Flarevm sembra essere down, così come i miei vps. Qualcuno sa di che cosa si tratta?
this is a great light-weight alternative to #FlareVM by @LabsSentinel github.com/SentineLabs/Se…
Going to take #flarevm for a spin! To have the tools to be able to reverse engineer malware, will be very interesting and am looking forward to trying! #ofsec #cybersecurity #malwareanalysis #malware #virus #bug #reverseengineering #pefilesystem #nt #exe #dll #vm #virtualmachine
🚨 Video 1 in a 5 part series discussing how to install #suricata into the #FLAREVM to use with PCAPs to generate network alerts 👇 youtu.be/MSg4GbDTF1k
youtube.com
YouTube
01 - Installing Suricata into the FLARE-VM
In case someone else wants to set up the #FlareVM from @FireEye with only "one click", I shared a script for it on gist: gist.github.com/botlabsDev/d2c…
TIL you can create Windows Forms UIs in Powershell 🤯 Found in the installer of #FlareVM for #ReverseEngineering. Check it out for other reasons, too :) github.com/mandiant/flare…
Friday night and what's a girl to do? Firing up my #flarevm for some malware analysis. I've been away from my debugger for far too long. #FridayFeeling #Malware

🔥 #SCLauncher is now a part of the #flarevm! ✅ github.com/jstrosch/sclau… This makes it easier than ever to debug and even produce #PE files from #shellcode. Thanks to @anamma_06 for all the help with the integration and everything you do for the flare-vm project!

📣 part 4 of installing #Suricata in the #FLAREVM is now live! In this video, we'll explore how to use #fakenet to generate network traffic with network emulation and then generate alert data from #suri 👇 youtu.be/sc-sDgKpzeM

youtube.com
YouTube
04 - Using Fakenet-NG for Network Emulation and PCAP Generation
🚨 The last video in working with #Suricata in the #FLAREVM is now live! This video introduces a basic rule writing workflow 👇 youtu.be/mWGdJ3YYUQ8 Full playlist (5 videos) -> youtube.com/playlist?list=…
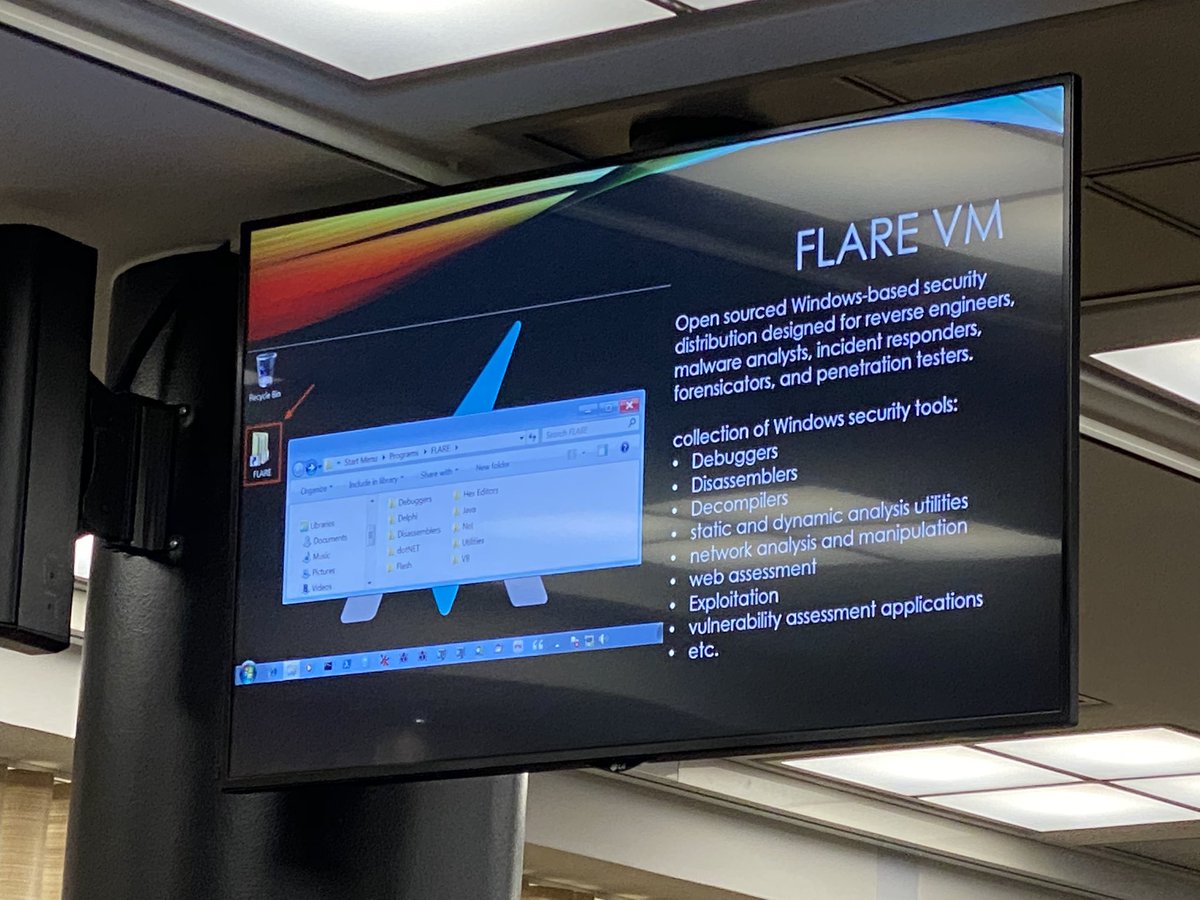
Malware Analysis Distribution #FLAREVM fireeye.com/blog/threat-re…
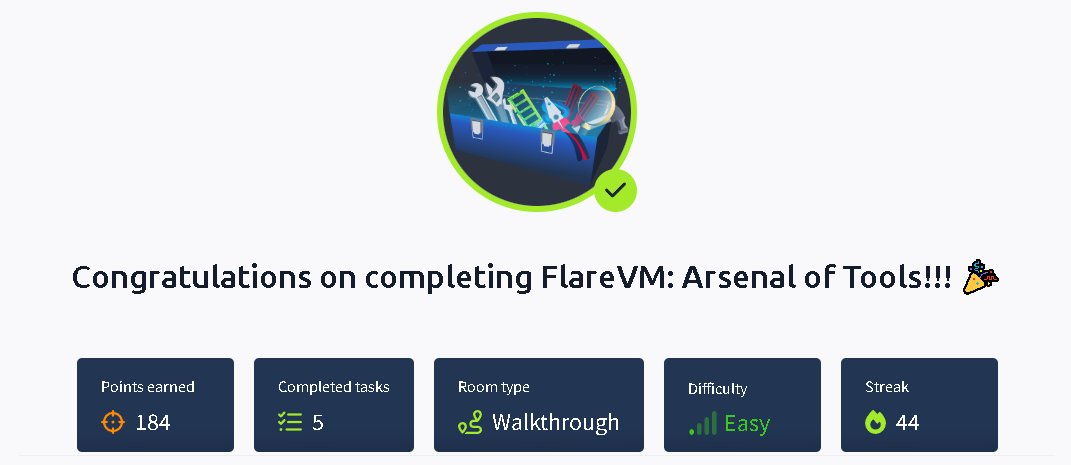
Just wrapped up the FlareVM: Arsenal of Tools room on @tryhackme 🚀🔥 🎯 Check it out: tryhackme.com/room/flarevmar… #TryHackMe #FlareVM #CyberSecurity #MalwareAnalysis
Read “Malware Analysis: Snake Keylogger/Snake Stealer“. This sample uses various techniques to evade detection, such as Reflective Code Loading, steganography, Process Hollowing and Control Flow Obfuscation. #pestudio #flarevm #malware #yara medium.com/@0x747863/malw…
medium.com
Malware Analysis: Snake Keylogger/Snake Stealer
Hi all.
Just earned my Shield Apprentice badge for conquering the FlareVM: Arsenal of Tools room on @tryhackme! 🛡️💥 🏅 Badge: tryhackme.com/milindagraj23/… #TryHackMe #FlareVM #CyberSecurity #MalwareAnalysis #BadgeUnlocked
Just wrapped up the FlareVM: Arsenal of Tools room on @tryhackme 🚀🔥 🎯 Check it out: tryhackme.com/room/flarevmar… #TryHackMe #FlareVM #CyberSecurity #MalwareAnalysis
🧰 Just completed the FlareVM: Arsenal of Tools room on @TryHackMe! #TryHackMe #CyberSecurity #FlareVM #MalwareAnalysis #ReverseEngineering #DFIR #Infosec #SecurityEngineer #LearningInPublic tryhackme.com/room/flarevmar… #tryhackme via @tryhackme
Hey Cyber Family 🥰 Reinstalled FLARE VM after a crash (13 hrs later 😩). Had a connection but no internet. Troubleshot it, DNS was the issue. Fixed it with a friend. Boom, back online. 💻✨ Keep digging. You'll find it. #CyberSec #FlareVM #Tech

Completed FLARE VM Arsenal of Tools on @tryhackme! Used tools like PEStudio, CFF Explorer, and Process Monitor to see how FLARE VM ties it all together for real-world malware and forensic analysis. Thanks to @allenharper for the support! #InfoSec #FLAREVM #DFIR
🎉 Excited to share that I've earned the Shield Apprentice badge on TryHackMe! 🛡️ #CyberSecurity #TryHackMe #FlareVM #MalwareAnalysis #ReverseEngineering #ContinuousLearninghttps://tryhackme.com/Skar037/badges/shieldapprentice #tryhackme via @tryhackme
🎉 I’ve just completed the FLARE VM: Ninja, Volatility, and FTK Imager. 🛠️💻 • 🧩 Exploring tools for static & dynamic analysis #Tkeaways:ryHackMe #FlareVM #MalwareAnalysis #ReverseEngineering #DigitalForensics #AlwaysLearning tryhackme.com/r/room/flarevm…
Flare VM how many times have i called you? Please allow me to install you in Peace my love. #val #flarevm #cybersecurity
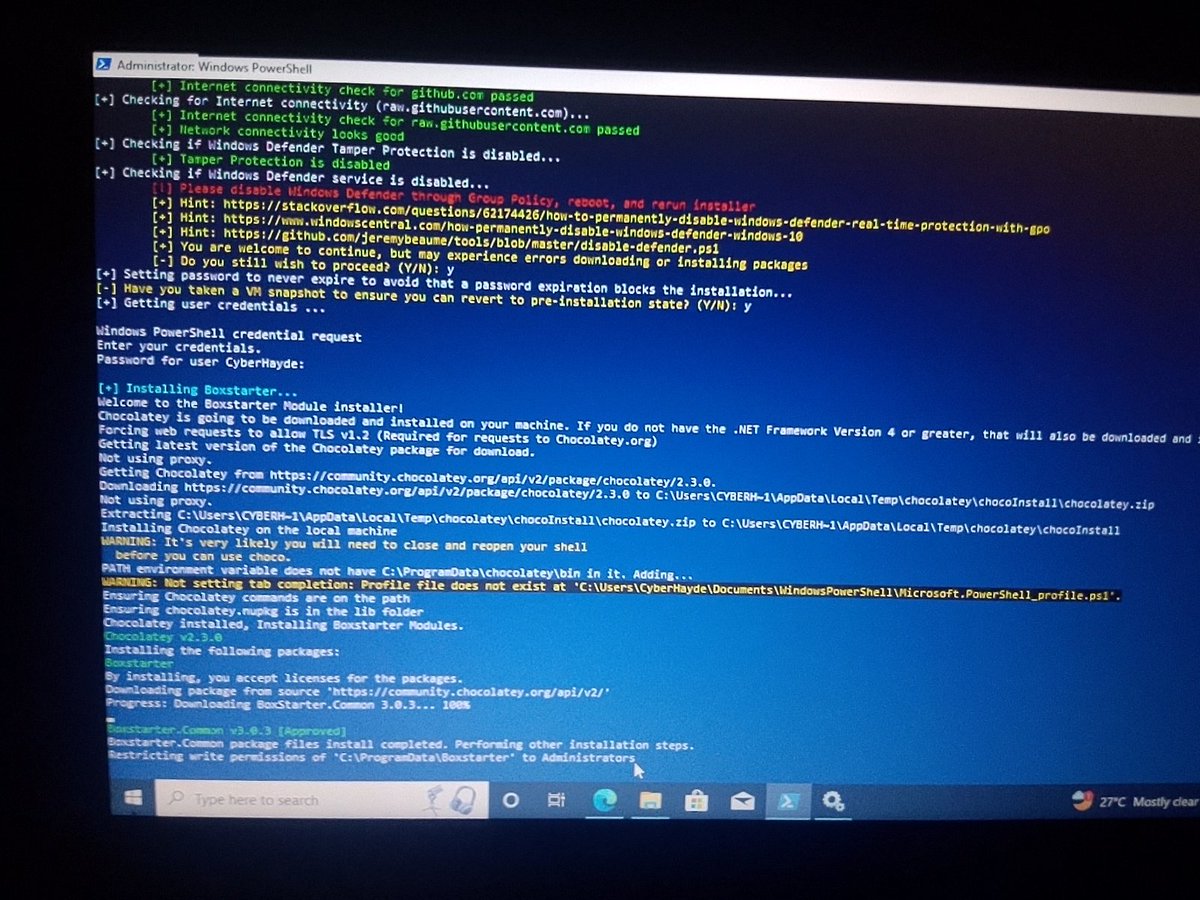
#flarevm: Windows-based security for malware analysis, IR, & pen testing. Automated tool deployment via PowerShell & Chocolatey. Key tools include HashCalc, PEiD for static, Wireshark for dynamic analysis, & debuggers like x64dbg. Installation can take hours based on your setup.
🚨 The last video in working with #Suricata in the #FLAREVM is now live! This video introduces a basic rule writing workflow 👇 youtu.be/mWGdJ3YYUQ8 Full playlist (5 videos) -> youtube.com/playlist?list=…
📣 part 4 of installing #Suricata in the #FLAREVM is now live! In this video, we'll explore how to use #fakenet to generate network traffic with network emulation and then generate alert data from #suri 👇 youtu.be/sc-sDgKpzeM

youtube.com
YouTube
04 - Using Fakenet-NG for Network Emulation and PCAP Generation
Exploring Suricata in Flare VM! Learn to analyze pcap files, generate alerts, and tackle potential errors while processing offline. Enhance your malware analysis toolkit! 🔍🛡️ #Suricata #FlareVM #PCAPAnalysis #Youtube link: ift.tt/94LSDEP
🚨 Part 3 is now live - learn how to process PCAPs with Suricata in the #FLAREVM to generate alerts and other network data 👇 youtu.be/2Xt40wuMH1o

youtube.com
YouTube
03 - Processing PCAPs in Offline Mode
🚨 Part 02 is live - in this video we'll talk about manually updating Suricata's ruleset in the #FLAREVM, which means we're running #suricata in Windows 🙀 youtu.be/CeD58UZuJBo
youtube.com
YouTube
02 - Manually Updating the Ruleset with Emerging Threats Open
🚨 Video 1 in a 5 part series discussing how to install #suricata into the #FLAREVM to use with PCAPs to generate network alerts 👇 youtu.be/MSg4GbDTF1k
youtube.com
YouTube
01 - Installing Suricata into the FLARE-VM
When the malware author forgets to obfuscate the compiler path lolol #FlareVm #RE #DFIR #MalDev #BenDev(?) :3
YouTube video walk through for TryHackMe room Learn the arsenal of investigative tools in FlareVM. Learn the arsenal of investigative tools in FlareVM. Part of the new path: Cyber Security 101 youtu.be/1Q0CuI9_474 #THMCyberSecurity101 #CyberSecurity101 #FlareVM
youtube.com
YouTube
TryHackMe FlareVM Arsenal of Tools forensics incident response...
🚨 Ready to build a malware & reverse engineering VM? This video covers installing #flarevm: youtu.be/i8dCyy8WMKY If you haven't used FLARE-VMin a while, it's worth another look! And if you haven't used it before, it's like #REMnux for #Windows. Lot's of great improvements!

youtube.com
YouTube
Building a VM for Reverse Engineering and Malware Analysis! Install...
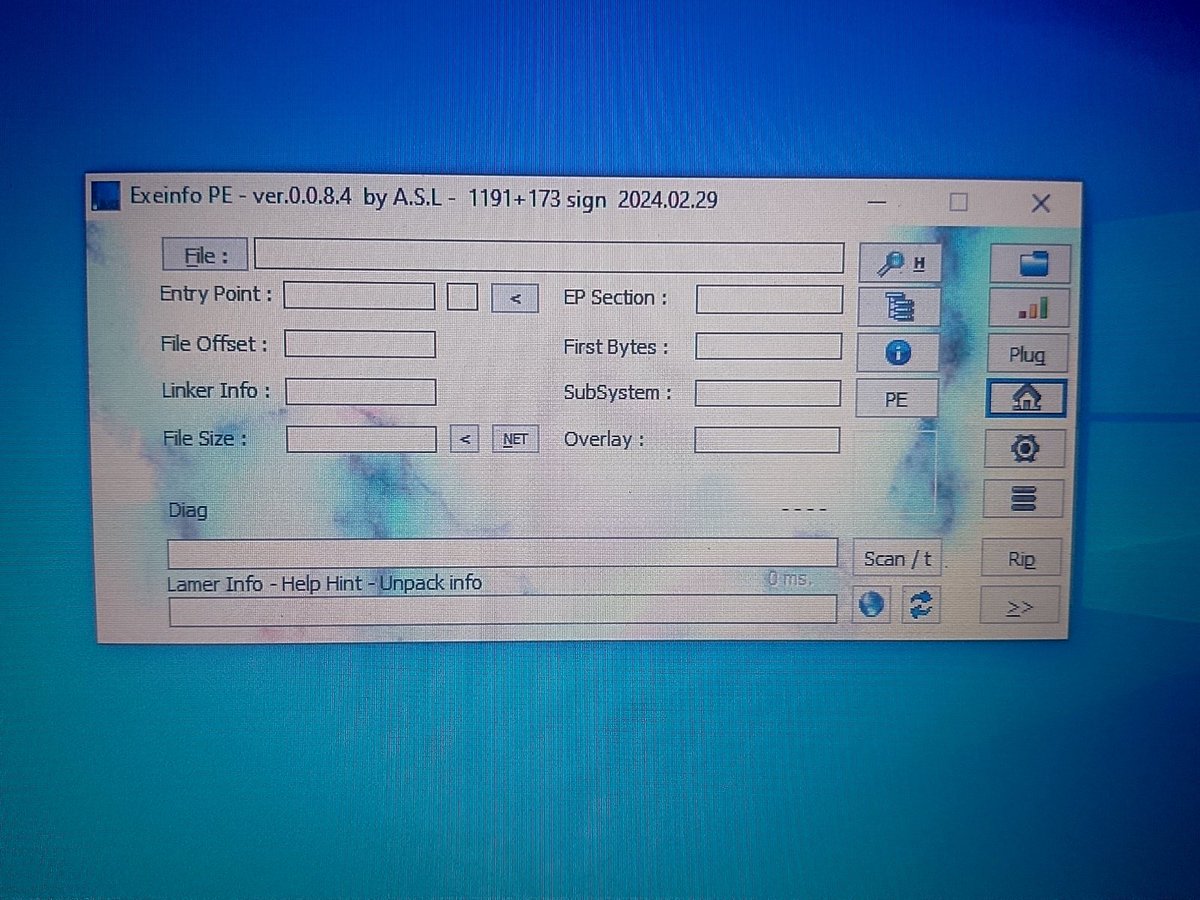
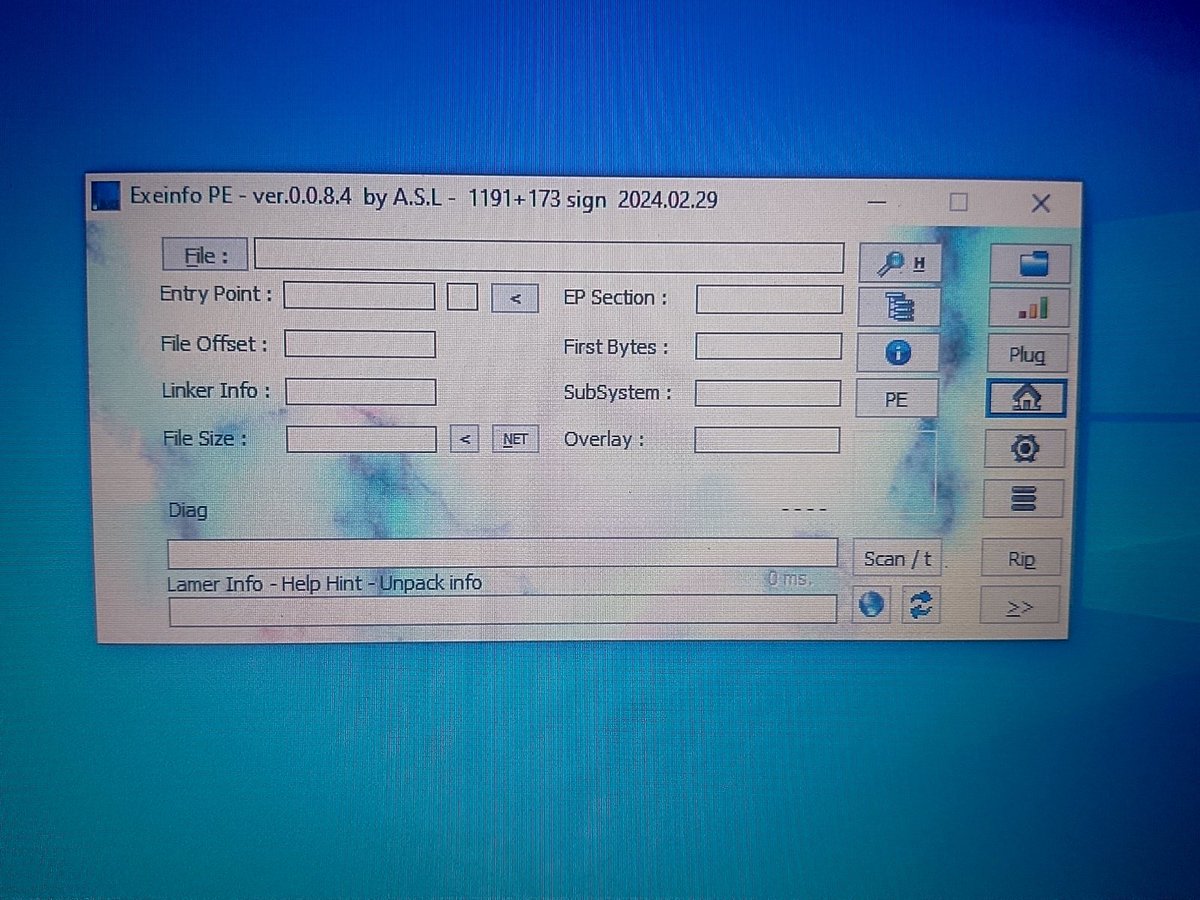
🚨 Day 17 of my #CybersecurityLearningStreak Today was all about Malware Analysis! Set up a sandbox with #FLAREVM, worked with tools like PEStudio, CFF Explorer, Exeinfo PE, HxD, and more, to successfully identify Portable Executable (PE) Malware. Onwards and upwards! 🔥

Booted up #FLAREvm and MemeCatBattlestation.exe is glorious. >> Stage 1 - Marauding Tabby Frigate! #FLAREon6 bonus level from #BHUSA2019
🚨 Day 17 of my #CybersecurityLearningStreak Today was all about Malware Analysis! Set up a sandbox with #FLAREVM, worked with tools like PEStudio, CFF Explorer, Exeinfo PE, HxD, and more, to successfully identify Portable Executable (PE) Malware. Onwards and upwards! 🔥

🔥 #SCLauncher is now a part of the #flarevm! ✅ github.com/jstrosch/sclau… This makes it easier than ever to debug and even produce #PE files from #shellcode. Thanks to @anamma_06 for all the help with the integration and everything you do for the flare-vm project!

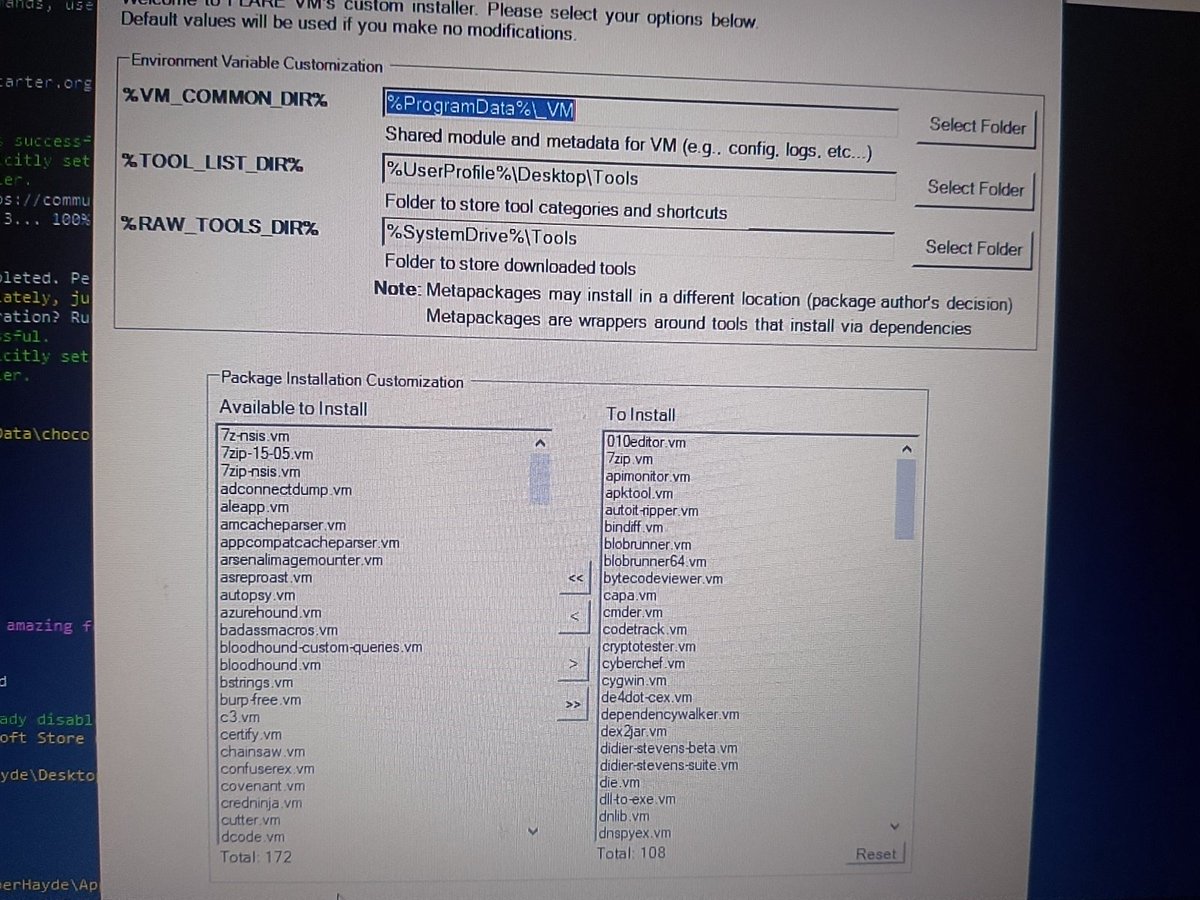
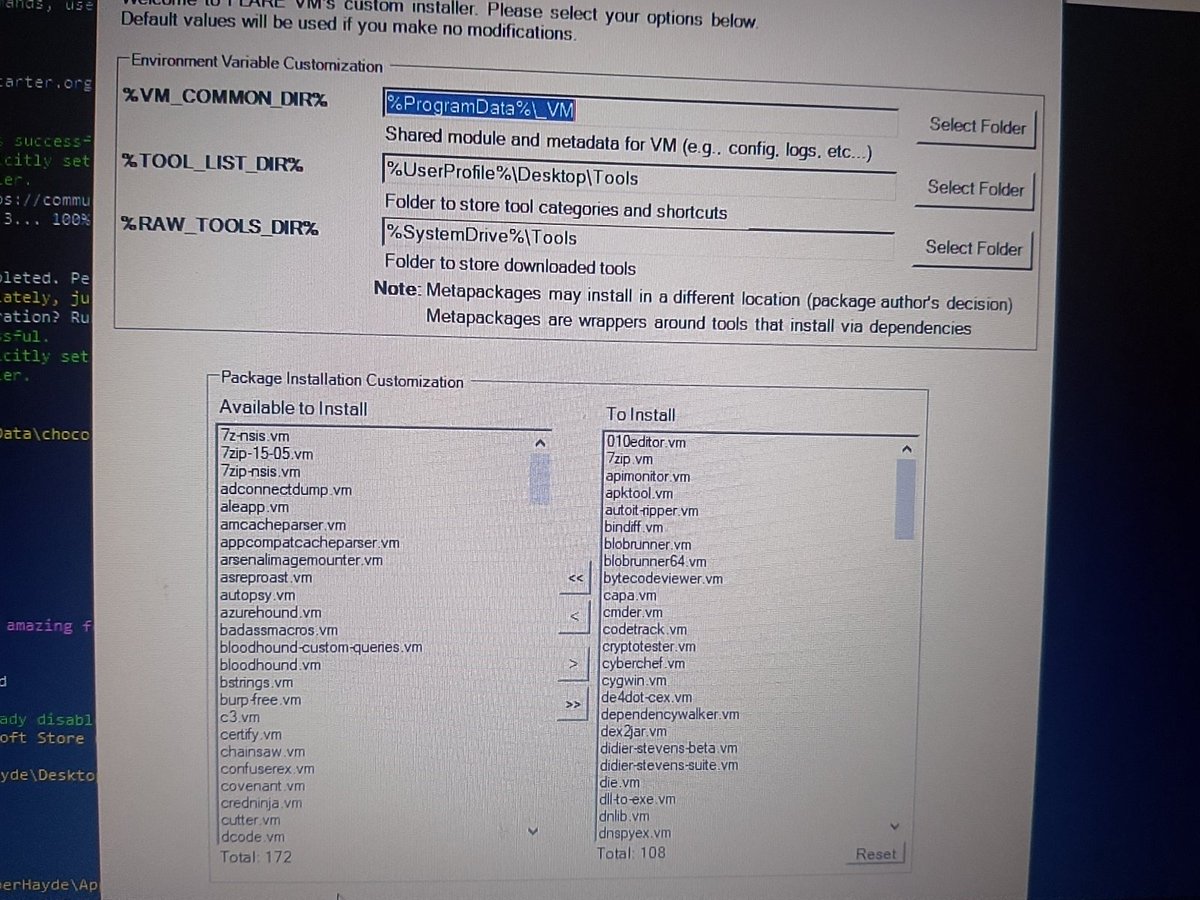
1/2 - Did you know you can automate and customize what tools the #flarevm installs? I've been building "profiles" to help speed installation up by removing packages that aren't needed. This helps me create more purpose-built VMs - what do you think? github.com/jstrosch/FLARE…
If you analyze #Malware on Windows and you’re not using the new #FLAREVM, you’re missing out 😉 The new version just dropped and it’s packed with upgrades for reverse engineers & #DFIR pros. 👇#Reversing



FLARE-VM just got a serious upgrade — new GUI, automated builds, and 288+ tools (with better IDA + Go support). The latest update brings: 🧰 Revamped installer ⚙️ New Python script for full VM automation 📚 (cont) bit.ly/48VetqY

Managed to install Ubuntu ARM with KDE plasma desktop and now installing #flarevm on my M1 MacBook, wish me luck 😎.

Friday night and what's a girl to do? Firing up my #flarevm for some malware analysis. I've been away from my debugger for far too long. #FridayFeeling #Malware

@FireEye's #FLAREVM: #Windows #MalwareAnalysis Distribution fireeye.com/blog/threat-re… #kaliLinux #REMnux #infosec #cybersecurity #malware

يوم جميل مليء بالسايبر 🔐💻 خلصت من course Malware Analysis 🛡️📂 حملت Flare VM 💾 ورحت على HTB 👨💻🏴☠️ والحين جالسة أتطلع على آخر ال updates في السايبر 📰🔍 #MalwareAnalysis #FlareVM #HackTheBox


The one...the only🥁 @lennyzeltser throwing down some bad a$$ malware tips-n-tricks #RSAC #FLAREVM #REMnux #GREM @s1r3nn @BanhammersWrath #VirtualAlloc #PeStudio


Now entering hour 5 of #FlareVM installation! I have no idea how much longer it's got but I did manage to get some offline reading done..haha 😅

Want to setup a Windows #malware reverse engineering environment asap ? Try #FlareVM github.com/fireeye/flare-…


FlareVM Tips and Tricks [& Quick Installation] poncho.bearblog.dev/flarevm-tips/ A simple blog on using FlareVM 😎 ⭐️Bonus Blog Post⭐️ How to Create a Flat White Coffee poncho.bearblog.dev/flatwhite-coff… Easy way to make a flat white that'll keep you going ☕️🐸 #infosec #FlareVM #CyberSecurity
![PonchoSec's tweet image. FlareVM Tips and Tricks [& Quick Installation]
poncho.bearblog.dev/flarevm-tips/
A simple blog on using FlareVM 😎
⭐️Bonus Blog Post⭐️
How to Create a Flat White Coffee
poncho.bearblog.dev/flatwhite-coff…
Easy way to make a flat white that'll keep you going ☕️🐸
#infosec #FlareVM #CyberSecurity](https://pbs.twimg.com/media/FTcn7oxWAAAw6o9.jpg)
![PonchoSec's tweet image. FlareVM Tips and Tricks [& Quick Installation]
poncho.bearblog.dev/flarevm-tips/
A simple blog on using FlareVM 😎
⭐️Bonus Blog Post⭐️
How to Create a Flat White Coffee
poncho.bearblog.dev/flatwhite-coff…
Easy way to make a flat white that'll keep you going ☕️🐸
#infosec #FlareVM #CyberSecurity](https://pbs.twimg.com/media/FTcn8ApWAAAhccf.jpg)
Vídeo cortito de como montar Windows 10+FlareVM. Tremendo para el análisis de malware y la ingeniería inversa en general.💯 youtu.be/i5bsNqVsgf4 #flarevm #ciberseguridad #ingenieriainversa #malware
Today I learned from @flaviaKos of a new RE tool VM #FlareVM #HelSec Besides, forensicator needs to be a word.
Hey Cyber Family 🥰 Reinstalled FLARE VM after a crash (13 hrs later 😩). Had a connection but no internet. Troubleshot it, DNS was the issue. Fixed it with a friend. Boom, back online. 💻✨ Keep digging. You'll find it. #CyberSec #FlareVM #Tech

FlareOn es una de mis CTFs preferidas, me hace salir de mi zona de confort. Resumen de varias horas para los retos 1-4 en el nuevo vídeo: youtu.be/i5bsNqVsgf4 #flarevm #ciberseguridad #ingenieriainversa #malware

Completed FLARE VM Arsenal of Tools on @tryhackme! Used tools like PEStudio, CFF Explorer, and Process Monitor to see how FLARE VM ties it all together for real-world malware and forensic analysis. Thanks to @allenharper for the support! #InfoSec #FLAREVM #DFIR
Something went wrong.
Something went wrong.
United States Trends
- 1. Bloodborne N/A
- 2. Aang N/A
- 3. #WWERaw N/A
- 4. #PlanetaAlofoke N/A
- 5. Korra N/A
- 6. Vitaly N/A
- 7. Rich Starry N/A
- 8. Jacksepticeye N/A
- 9. Raven N/A
- 10. #BELIFT_Boycott_Continues N/A
- 11. #OurFutureIsPerfectWITH7 N/A
- 12. #HarryandMeghaninAustralia N/A
- 13. Sade N/A
- 14. Incorrectly N/A
- 15. Cameron Diaz N/A
- 16. Mike Trout N/A
- 17. ATLA N/A
- 18. Wrobleski N/A
- 19. Beyond the Spider-Verse N/A
- 20. Flyers N/A