#fullsecure search results
📢 Only 2 days ⏱️ left to benefit from a 25% discount on the #Fullsecure store. #couponcode 🎟️CYBER CADEAU 2019🎟️ 🛍️ fullsecure.link/boutique/ Protect your sensitive #data from € 33 youtube.com/watch?v=rZYweV… Thank to RT 😉
#Fullsecure expose au #CBC #CyberBusinessConvention le 14/11 #Toulouse ! C'est une opportunité de vous présenter nos #innovation2019 en #cybersecurite #hardware #NFC des #DonnéeSensible #horsligne ↓ Plus d'Infos ↓ cbc-convention.com #b2b #business

🆕#Fullsecure will be present at #CBC #CyberBusinessConvention #Toulouse #France! Come to see our #innovation2019 en #cybersecurity #hardware #NFC #coldwallet #cryptocurrency #SensitiveData #Offline ↓ More Infos ↓ cbc-convention.com #b2b #business

🏆#DataShielder HSM nou ecosistema andorrà patentat de #Fullsecure que assegura sense servidor, sense base de dades els seus secrets, ha guanyat #Fortress #CyberSecurity #Award 2023 @BigAwards Millor solució de #xifratge🔐 cc @XavierEspot @freemindtronic freemindtronic.com/datashielder-h…
Get the best quality in Doors!! #BajajDoor is always double strong & double secure!! 📱 You can contact us on : 9503013936 📍 Office: Plot no. D5/1, M.I.D.C. Hingna Industrial Estate, Nagpur-16 #fullsecure #smartdoores #bajajdoors #BajajBsecureDoors #doormanufacturer

🚩Rappel à nos clients & avis à nos futurs clients! Les produits #fullsecure👉#evitoken #evipro #eviplus #evivault #evione #evilite #evitag #evicard👈n’utilisent pas la carte SIM des smartphones. Les données sont isolées dans les dispositifs #NFC cc @NiuAndorra @AndorraTelecom
#CyberSecurity: New #SIM Card Flaw Lets Hackers #Hijack Any #Phone Just By Sending #SMS thehackernews.com/2019/09/simjac…
thehackernews.com
New SIM Card Flaw Lets Hackers Hijack Any Phone Just By Sending SMS
Cybersecurity researchers today revealed the existence of Simjacker, a SIM Card vulnerability that could allow remote hackers to spy on devices just by sending SMS
Mantap. Dipaksa logout. Verifikasinya ada 4. 1. Masukkan no. Hp 2. Masukkan password 3. Masukkan PIN 4. Masukkan OTP yang dikirim ke no. 1. #fullsecure #flipid
Bonjour, existe également les gestionnaires physiques et Off-Line #Evitag-NFC et #Evicard-NFC by #Fullsecure. Solutions les + secure, c'est pas moi qui le dit, car vos données sont dans votre poche, activées par #NFC, et pas sur les bases de données d'internet Cc @freemindtronic
@CBerthelemy @taziden non le contrôle à la sortie de chez soi du citoyen. Et à son entrée quelque part #FullSecure
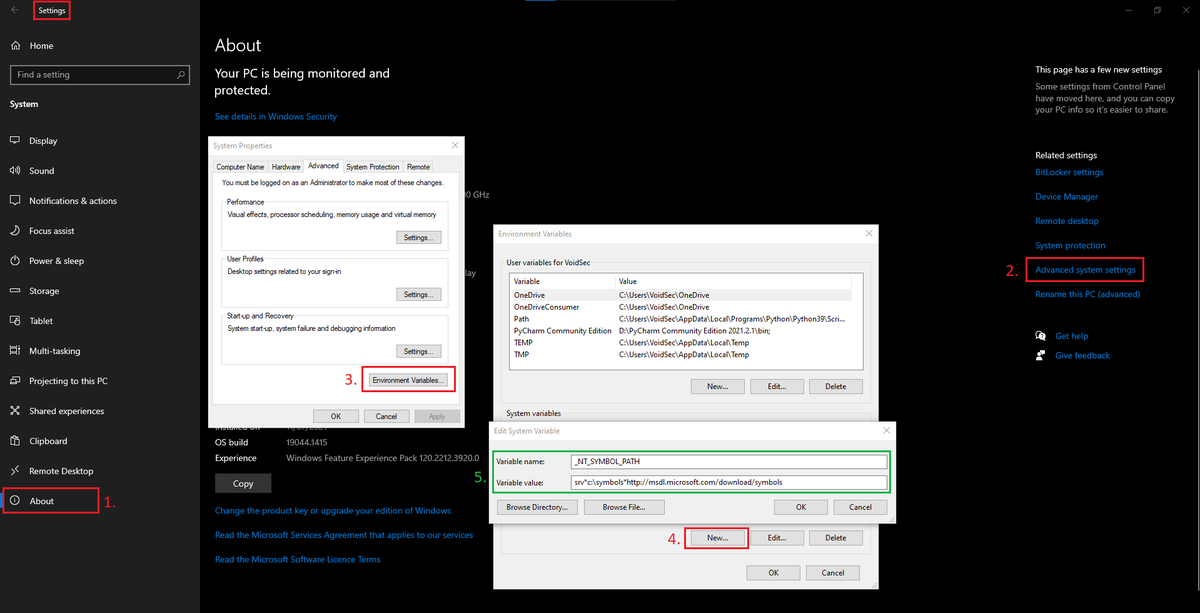
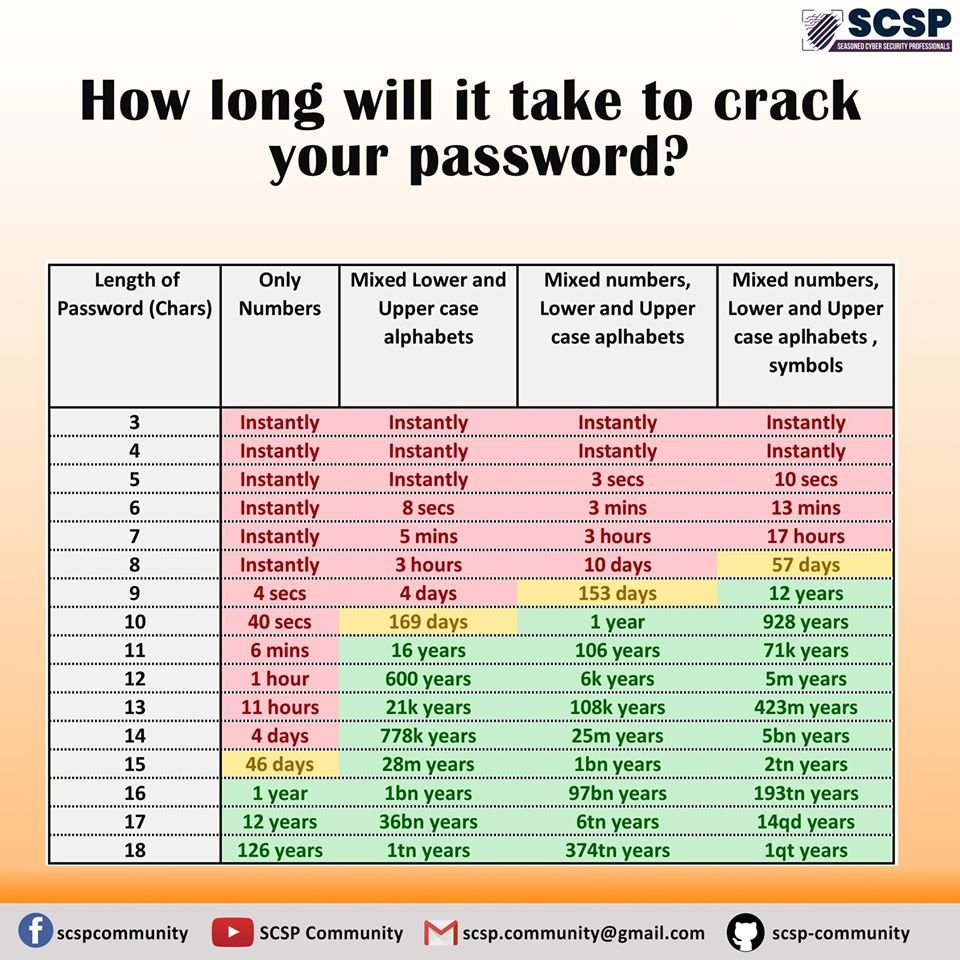
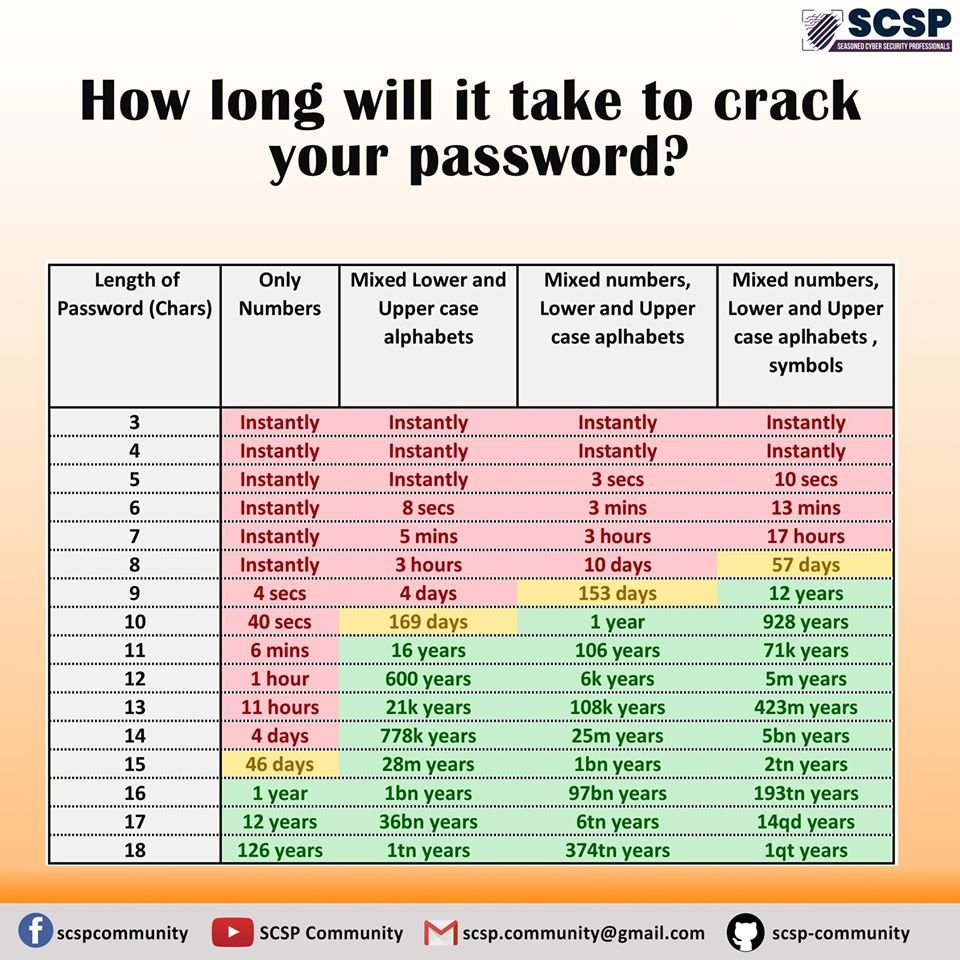
Utilisez un générateur de #motdepasse tel que #EviToken jusqu'à 48 caractères ASCII aléatoires. Le temps dépend aussi de la puissance de calcul. Il y a un lien dans l'article #fullsecure d'un simulateur temps d'attaque force brute réalisé par Bob Beeman fullsecure.link/766-trillions-…
Combien de temps faut-il pour déchiffrer un mot de passe? 👉Plus c'est long, mieux c'est... #cybersecurité #motdepasse #hackers bit.ly/2tSuGvy
Le @GovernAndorra travaille sur un protocole de reprise d'activité des entreprises et professions libérales en #Andorre. Dans l'attente l'entreprise #Fullsecure demeure fermée. L'activité #rechercheetdéveloppement #freemindtronic est maintenue en #teletravail. #RestezChezVous
#Fullsecure expose au #CBC #CyberBusinessConvention le 14/11 #Toulouse ! C'est une opportunité de vous présenter nos #innovation2019 en #cybersecurite #hardware #NFC des #DonnéeSensible #horsligne ↓ Plus d'Infos ↓ cbc-convention.com #b2b #business

Sujet analogue 😉 #Fullsecure a développé pour la première fois des produits furtifs professionnels #evitoken en #Andorra pour sécuriser physiquement #offline les données confidentielles ainsi renforcer les outils de #cybersecurite et de souveraineté individuelle cc @
Les États-Unis ont déployé pour la première fois des avions furtifs F-22 « Raptor » au Qatar, a annoncé, vendredi 28 juin, le Pentagone, augmentant ainsi encore un peu plus la présence militaire américaine dans le Golfe, en pleine tension avec l'Iran. rfi.fr/moyen-orient/2…
J-7⏳13-15 november 📅@SmartCityexpo 🇪🇸@IniciativaActua🇦🇩@freemindtronic #fullsecure Discover 21st century #Innovations an individual nomad solution that secures🔐sensitive data #Offline ⏱#Realtime demonstration physical and digital #cybersecurity offline at booth 425 #barcelone

Go to that person and just say in his ear the message you want to told with him by whatsapp.😂 #fullsecure #costly @theamitsharma1
Et parmi les solutions, il faut désormais citer les dispositifs #Evitag-NFC et #Evicard-NFC de #Fullsecure qui permettent à leurs utilisateurs de devenir totalement anonymes des systèmes informatiques et de toutes bases de données, cc @freemindtronic @GascuelJ
#webconference #cybermatinee #fullsecure sécurité électronique #airgap d'un poste de travail via #NFC démo #ssd #autologon #VPN #chiffrement @MondeInformatiq



Merci pour ce partage sur les dispositifs de sécurité des usages numériques #Fullsecure : à l'heure de l'appel national à la "contamination" sur la sécurité numérique, il faut promouvoir ces solutions Off-Line alternatives au monde du "tout connecté" et 100% compatibles RGPD.
#Fullsecure selected as one of the 100 best cyber security companies in Spain Andorra (2021) by @Threat_Tech cc @freemindtronic @XavierEspot @mubachfont @GovernAndorra @IniciativaActua @cesarmarquina @CEA_And @JGallardoAND threat.technology/these-are-the-… #Andorra #CyberSecurity #Spain
🏆#DataShielder HSM nou ecosistema andorrà patentat de #Fullsecure que assegura sense servidor, sense base de dades els seus secrets, ha guanyat #Fortress #CyberSecurity #Award 2023 @BigAwards Millor solució de #xifratge🔐 cc @XavierEspot @freemindtronic freemindtronic.com/datashielder-h…
Mantap. Dipaksa logout. Verifikasinya ada 4. 1. Masukkan no. Hp 2. Masukkan password 3. Masukkan PIN 4. Masukkan OTP yang dikirim ke no. 1. #fullsecure #flipid
जो यहाँ देश विरोधी आके कमेंट में भाषड़ दे रहे हैं न, उनसे सिर्फ यही कहना हैं.... अपनी अम्मी के घोसला में घुस जाओ #staysafe and #fullsecure अपने बाप की पोस्ट पर सोचकर कमेंट किया करो वे, दुनिया शस्त्रों का उपयोग करती हैं पेलने में, विश्वास भाई शब्दों का प्रयोग करके ही ले लेंगे😀🙏
#Fullsecure selected as one of the 100 best cyber security companies in Spain Andorra (2021) by @Threat_Tech cc @freemindtronic @XavierEspot @mubachfont @GovernAndorra @IniciativaActua @cesarmarquina @CEA_And @JGallardoAND threat.technology/these-are-the-… #Andorra #CyberSecurity #Spain
See this young man holding the sign? He was my student @PinerHighSchool and now he begins his teaching career with me at SRHS @SRCSchools @athletics_srhs #fullsecure #homegrownsrcs #prospectortopanther ❤️❤️❤️❤️

Eurekas Home Made Food Network 🍔🍟🍕🌮🍲🍿🍚🍛🍜🍝🍩🍪🍮😄😆😉😊😋🤗😙😚🙄😏😛😝😜 #Foods #HomemadeFOOD #fullsecure #quality #services #readyto #eat #Hunger #Biryani #learningfromhome #Cooking #cookingathome #temptation

#Fullsecure a fait une Démo #chiffrement des #données via dispositifs #NFC sur ordinateur et smartphone solution nomade qui fonctionne #horsligne idéal #teletravail aujourd'hui sur LMI TV @MondeInformatiq #cybermatinee #Occitanie 2020 voir Replay cybermatinees.fr/replay-occitan…
Le chiffrement des données devient une priorité - itsocial.fr/enjeux-it/enje…
Visionnez en replay #cybermatinée #Occitanie sur LMI TV du @MondeInformatiq la démo #fullsecure commence à 2:21:00 cc @FabriceCrasnier @GroupeSyselec @BleujourInfo @GovernAndorra @AndorraDPA @CEA_And @cambracomerc @forum_ad @mubachfont @PVynckier cybermatinees.fr/replay-occitan…
22 avril #webconference protection des #données, mobilité, #teletravail #confinement démo #autologin #autologon #chiffrement #SansContact avec #Token #NFC cc @IniciativaActua @MondeInformatiq @BleujourInfo @Sysecure1 @La_Melee #quedatacasa #restezalamaison #cybersecurite

#webconference #cybermatinee #fullsecure sécurité électronique #airgap d'un poste de travail via #NFC démo #ssd #autologon #VPN #chiffrement @MondeInformatiq



Le @GovernAndorra travaille sur un protocole de reprise d'activité des entreprises et professions libérales en #Andorre. Dans l'attente l'entreprise #Fullsecure demeure fermée. L'activité #rechercheetdéveloppement #freemindtronic est maintenue en #teletravail. #RestezChezVous
Utilisez un générateur de #motdepasse tel que #EviToken jusqu'à 48 caractères ASCII aléatoires. Le temps dépend aussi de la puissance de calcul. Il y a un lien dans l'article #fullsecure d'un simulateur temps d'attaque force brute réalisé par Bob Beeman fullsecure.link/766-trillions-…
Combien de temps faut-il pour déchiffrer un mot de passe? 👉Plus c'est long, mieux c'est... #cybersecurité #motdepasse #hackers bit.ly/2tSuGvy
📢 Only 2 days ⏱️ left to benefit from a 25% discount on the #Fullsecure store. #couponcode 🎟️CYBER CADEAU 2019🎟️ 🛍️ fullsecure.link/boutique/ Protect your sensitive #data from € 33 youtube.com/watch?v=rZYweV… Thank to RT 😉
#Fullsecure expose au #CBC #CyberBusinessConvention le 14/11 #Toulouse ! C'est une opportunité de vous présenter nos #innovation2019 en #cybersecurite #hardware #NFC des #DonnéeSensible #horsligne ↓ Plus d'Infos ↓ cbc-convention.com #b2b #business

🆕#Fullsecure will be present at #CBC #CyberBusinessConvention #Toulouse #France! Come to see our #innovation2019 en #cybersecurity #hardware #NFC #coldwallet #cryptocurrency #SensitiveData #Offline ↓ More Infos ↓ cbc-convention.com #b2b #business

#Fullsecure expose au #CBC #CyberBusinessConvention le 14/11 #Toulouse ! C'est une opportunité de vous présenter nos #innovation2019 en #cybersecurite #hardware #NFC des #DonnéeSensible #horsligne ↓ Plus d'Infos ↓ cbc-convention.com #b2b #business

🚩Rappel à nos clients & avis à nos futurs clients! Les produits #fullsecure👉#evitoken #evipro #eviplus #evivault #evione #evilite #evitag #evicard👈n’utilisent pas la carte SIM des smartphones. Les données sont isolées dans les dispositifs #NFC cc @NiuAndorra @AndorraTelecom
#CyberSecurity: New #SIM Card Flaw Lets Hackers #Hijack Any #Phone Just By Sending #SMS thehackernews.com/2019/09/simjac…
thehackernews.com
New SIM Card Flaw Lets Hackers Hijack Any Phone Just By Sending SMS
Cybersecurity researchers today revealed the existence of Simjacker, a SIM Card vulnerability that could allow remote hackers to spy on devices just by sending SMS
🇦🇩 Avis aux #Andorran ! L'entreprise #fullsecure à #EscaldesEngordany fabrique en #Andorre des produits personnels #evitag #evicard & entreprise #evitoken de #cybersecurite #ciberseguretat pour se protéger youtu.be/uQeqv1VyhOY cc @NiuAndorra @IniciativaActua @AndorraTelecom
La @Gendarmerie du #IRCGN fait parler les ordinateurs, les smartphones,.. 20minutes.fr/faits_divers/2…. Les #coffrefortelectronique de #fullsecure #USBKey ou #ssddisk risquent de complexifier leurs investigations. protection #bruteforce INFO : fullsecure.link/evikey-plus-nfc
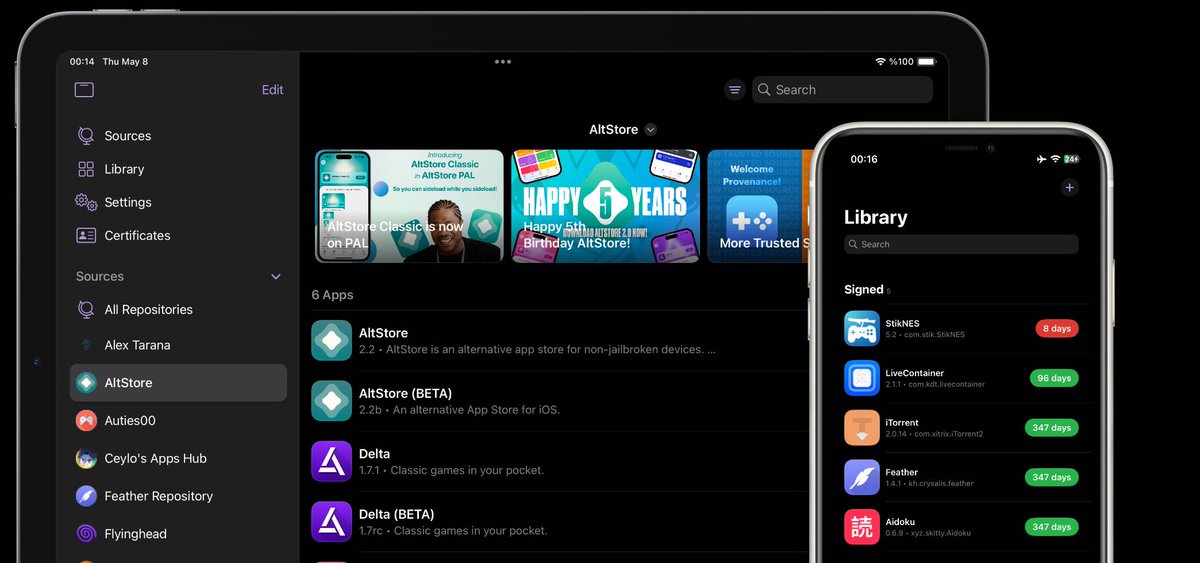
LARA IPA OUT! Full root access (no jailbreak) 👇 • iOS 18 – 18.7.1 • iOS 26.0 – 26.0.1 ⚡ Powered by DarkSword 📥IPA & Guide: senumy.com/#new-updated

Feather v_2.7.0 is out Open-source IPA installer for iOS 15 → 26+ No 3rd-party services — full control with your own cert 🔐 New: • Remote pairing (iOS 17.4+) • More sources • Extension injection 🔗 senumy.com/ipa-library/fe…
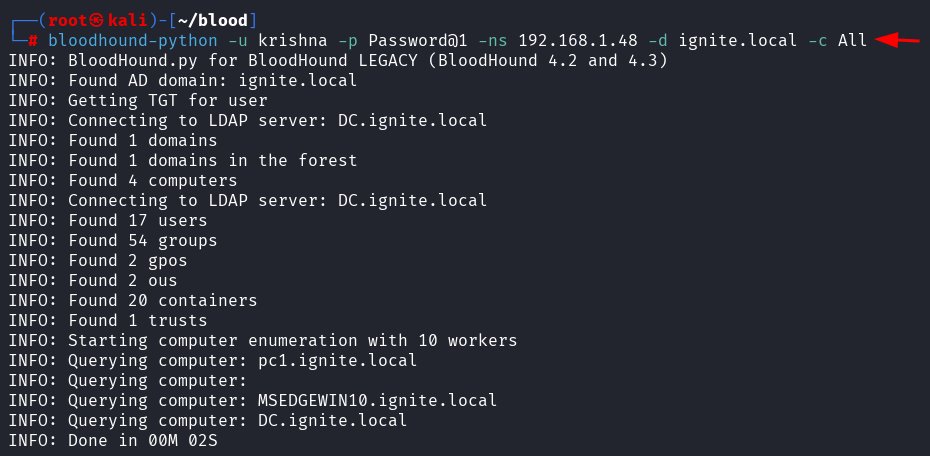
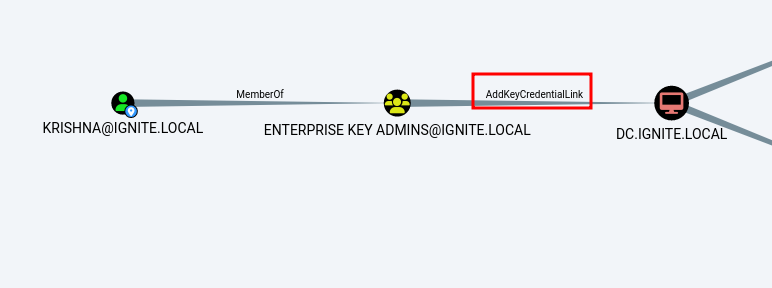
Shadow Credentials Attack 🔥 Telegram: t.me/hackinarticles ✴ Twitter: x.com/hackinarticles Shadow Credentials attack abuses Active Directory Certificate Services (AD CS) by injecting rogue public keys into the msDS-KeyCredentialLink attribute, allowing attackers to


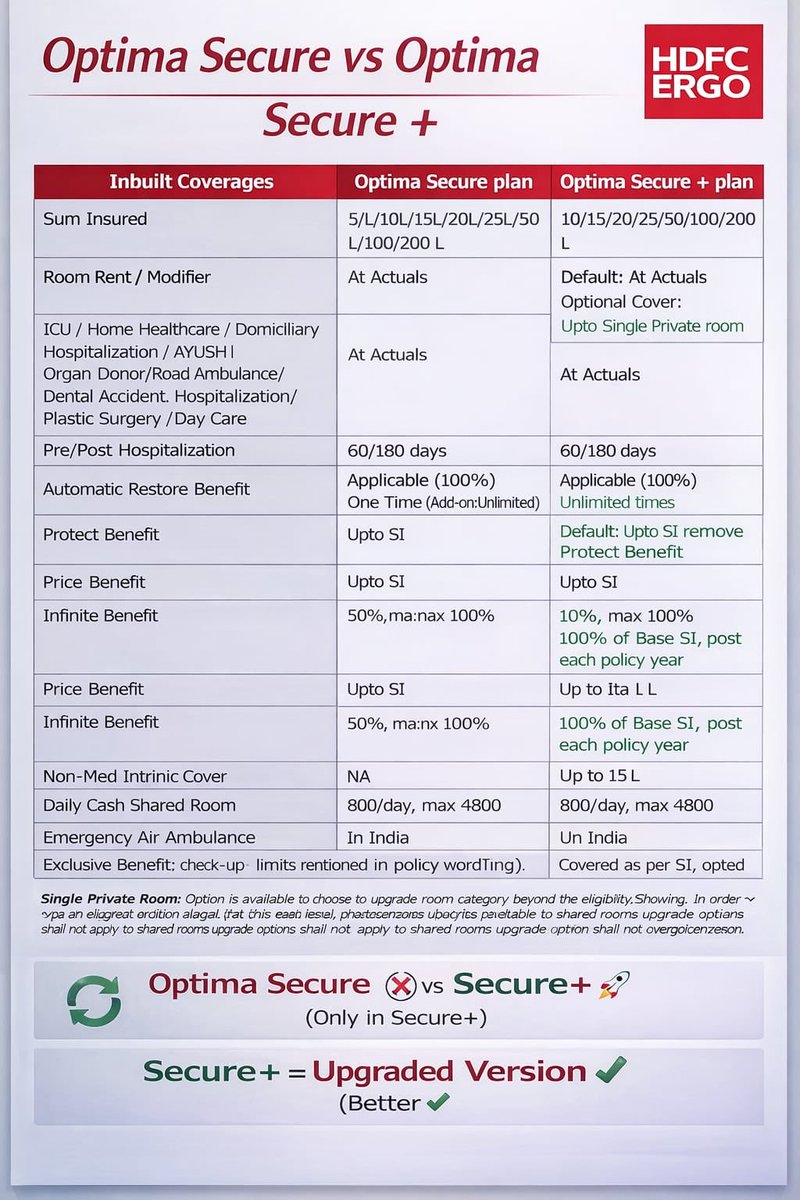
Many people having trouble in understanding diffrence between … Hdfc ergo optima secure vs hdfc ergo optima secure+ Check the table below you will see major feature diffrent from optima secure to secure+
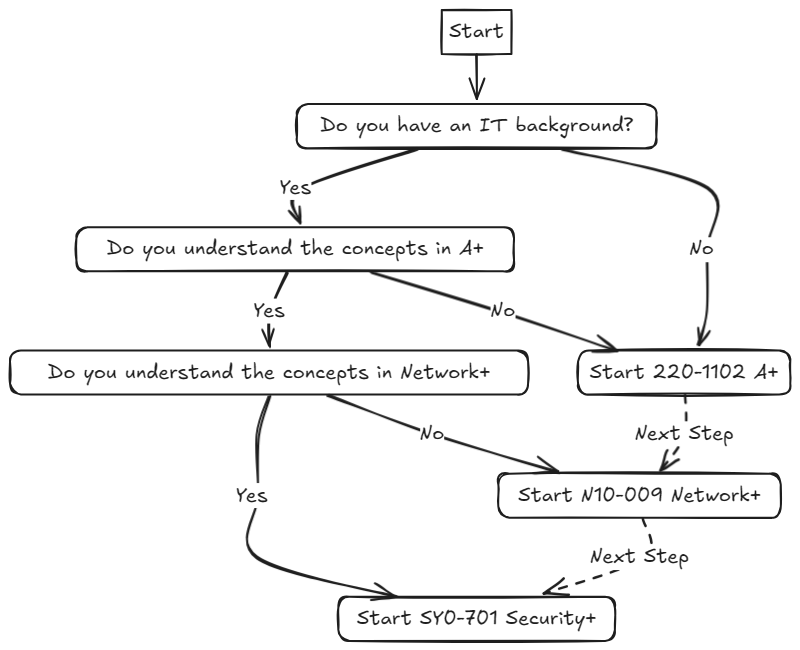
📚 A Complete Beginners Guide on breaking into Cyber Security. Blog: jhalon.github.io/breaking-into-… Author: @jack_halon #infosec

🔥 Phantom — Autonomous AI Red Team Agent ⚔️ LLM-Powered Offensive Security Automation Framework 👉 github.com/kmdn-ch/phanto…

Pic of the Day #infosec #cybersecurity #cybersecuritytips #pentesting #cybersecurityawareness #informationsecurity
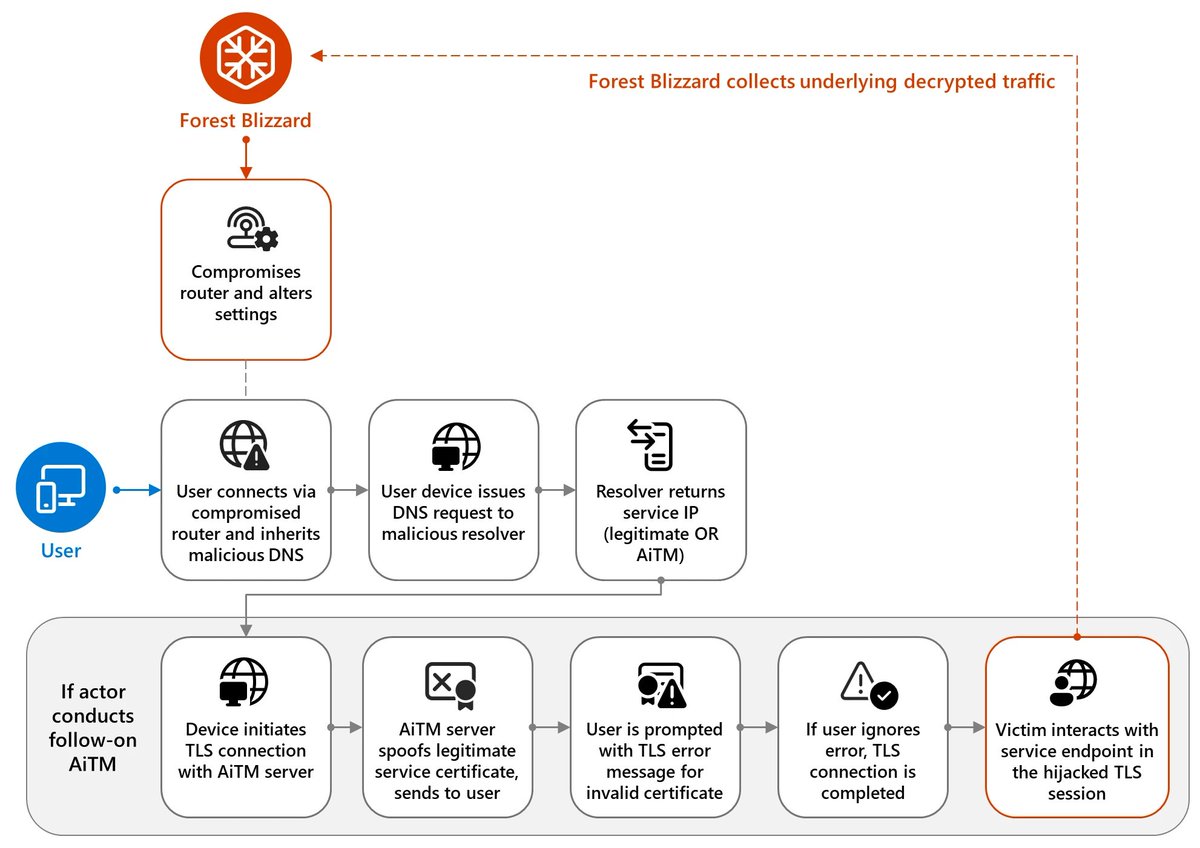
Microsoft exposes Forest Blizzard’s hijacking of 5,000+ SOHO routers for DNS spying and AiTM attacks on Microsoft 365 and governments. Patch your router now! #ForestBlizzard #DNSHijacking #CyberSecurity #InfoSec #RouterSecurity #GRU #ThreatIntel securityonline.info/forest-blizzar…
🚨Cyber Alert ‼️ 🇪🇬Egypt - 𝗘𝗹 𝗪𝗮𝘀𝘁𝗮𝗻𝗶 𝗣𝗲𝘁𝗿𝗼𝗹𝗲𝘂𝗺 𝗖𝗼𝗺𝗽𝗮𝗻𝘆 (𝗪𝗔𝗦𝗖𝗢) Payload hacking group claims to have breached El Wastani Petroleum Company (WASCO). Threat actor: Payload Sector: Energy / Utilities Data exposure (claimed): 50 GB Data type: Not

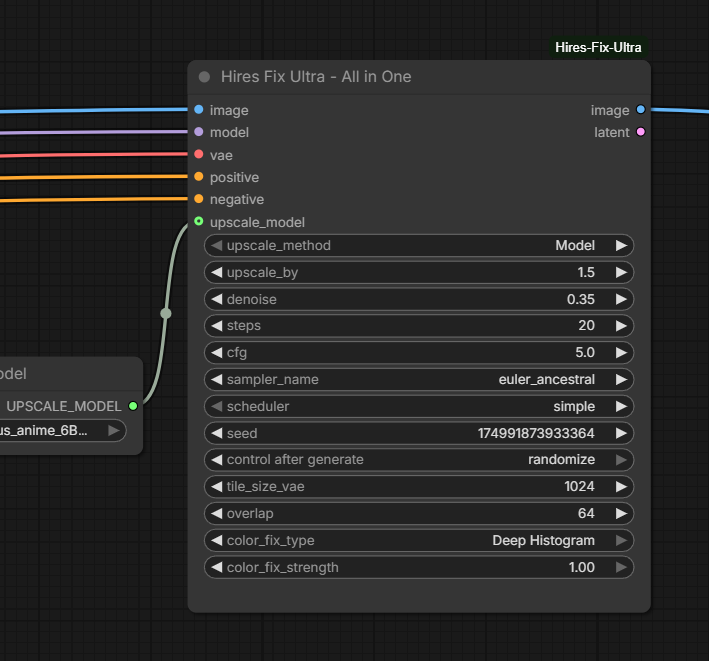
In the endless stream of papers, models and nodes coming out, I generally try to avoid posting everything under the sun, only stuff that I want to use. This nodemight replace a half-dozen nodes in my SDXL workflows. Might give it a try later tonight. github.com/ThetaCursed/Co…
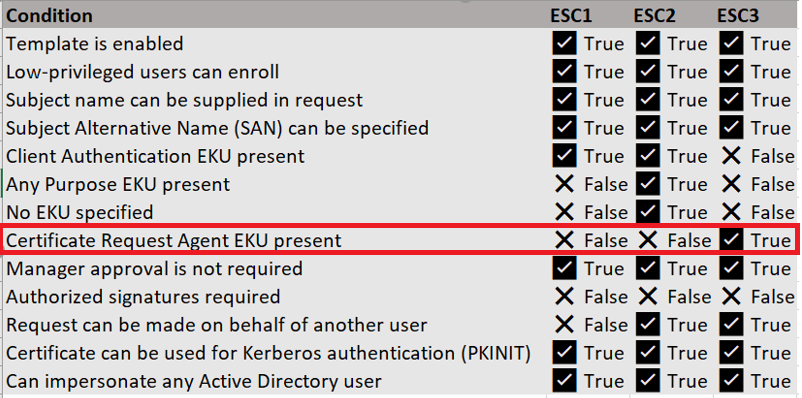
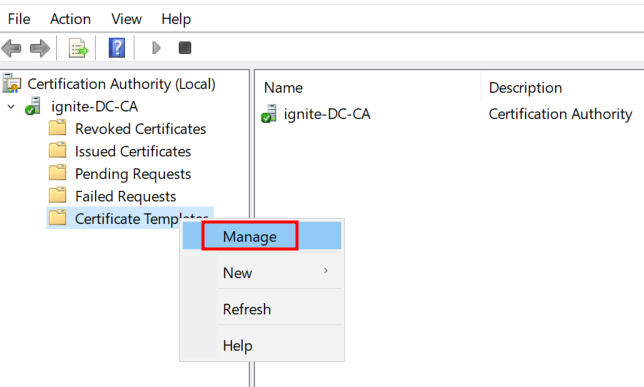
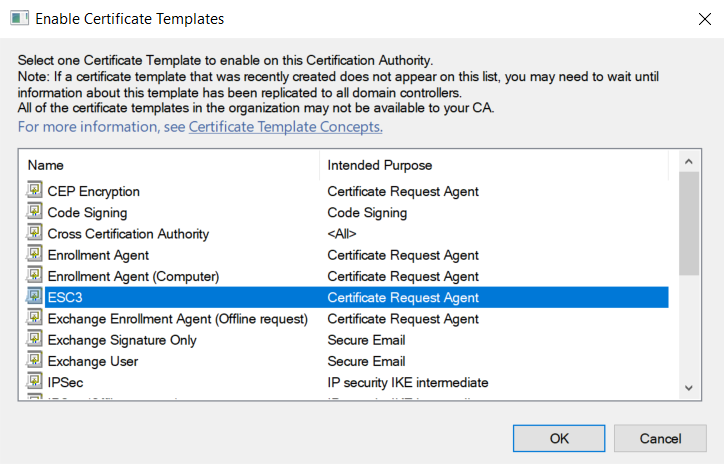
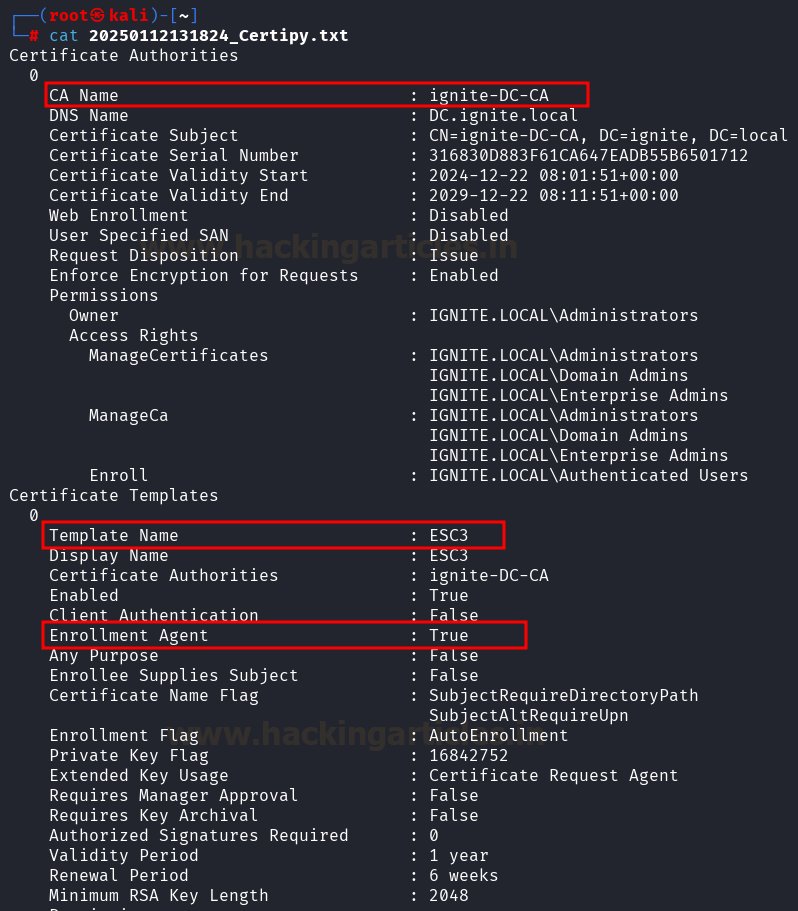
ADCS ESC3: Enrollment Agent Template 🔥 Telegram: t.me/hackinarticles ✴ Twitter: x.com/hackinarticles Active Directory Certificate Services (ADCS) is commonly targeted in ESC3 certificate attacks, which exploit misconfigurations in certificate templates to enable
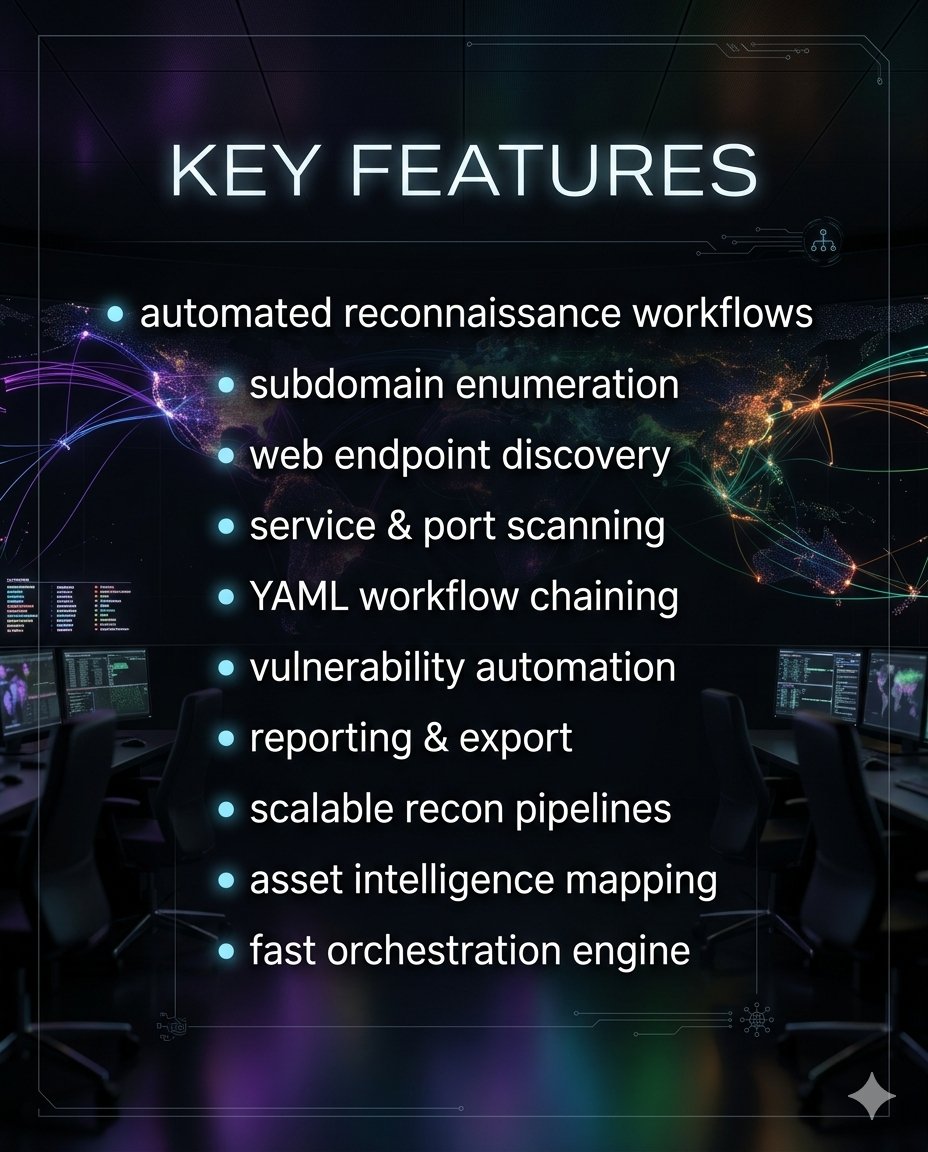
Automation and workflow efficiency are key in modern cybersecurity research. Osmedeus helps streamline reconnaissance, asset discovery, and security assessment workflows in a structured and scalable way. From visibility to automation, having the right workflow engine can save

🚨 CVE-2026-23898 & CVE-2026-23899: Critical File Deletion and Webservice Flaws Exposed in Joomla. 👇Dorks HUNTER : product.name="Joomla"

Bluehammer Privilege escalation via Microsoft Defender. No patch yet github.com/Nightmare-Ecli… #0day #lpe
🚨Cyber Alert ‼️ 🇳🇱Netherlands - 𝗖𝗵𝗶𝗽𝗦𝗼𝗳𝘁 Ransomware attack on ChipSoft, a Dutch healthcare software provider used by ~70% of hospitals, involving possible unauthorized access; patient data may have been accessed or exfiltrated, potentially impacting multiple hospitals

Domain Sold! 💰Detention .com Sold for $17,244 🛒Sold via GoDaddy 🗓️April 5, 2026 This domain name is suitable for platforms related to judicial security, campus management, disciplinary education, compliance risk control, and security supervision. It has a professional and

Attackers are impersonating Linux leaders on Slack to drop malware via fake Google Workspace links. Protect your dev environment—verify before acting! #SocialEngineering #SlackAttack #DevSec #CyberSecurity #InfoSec #LinuxFoundation securityonline.info/social-enginee…

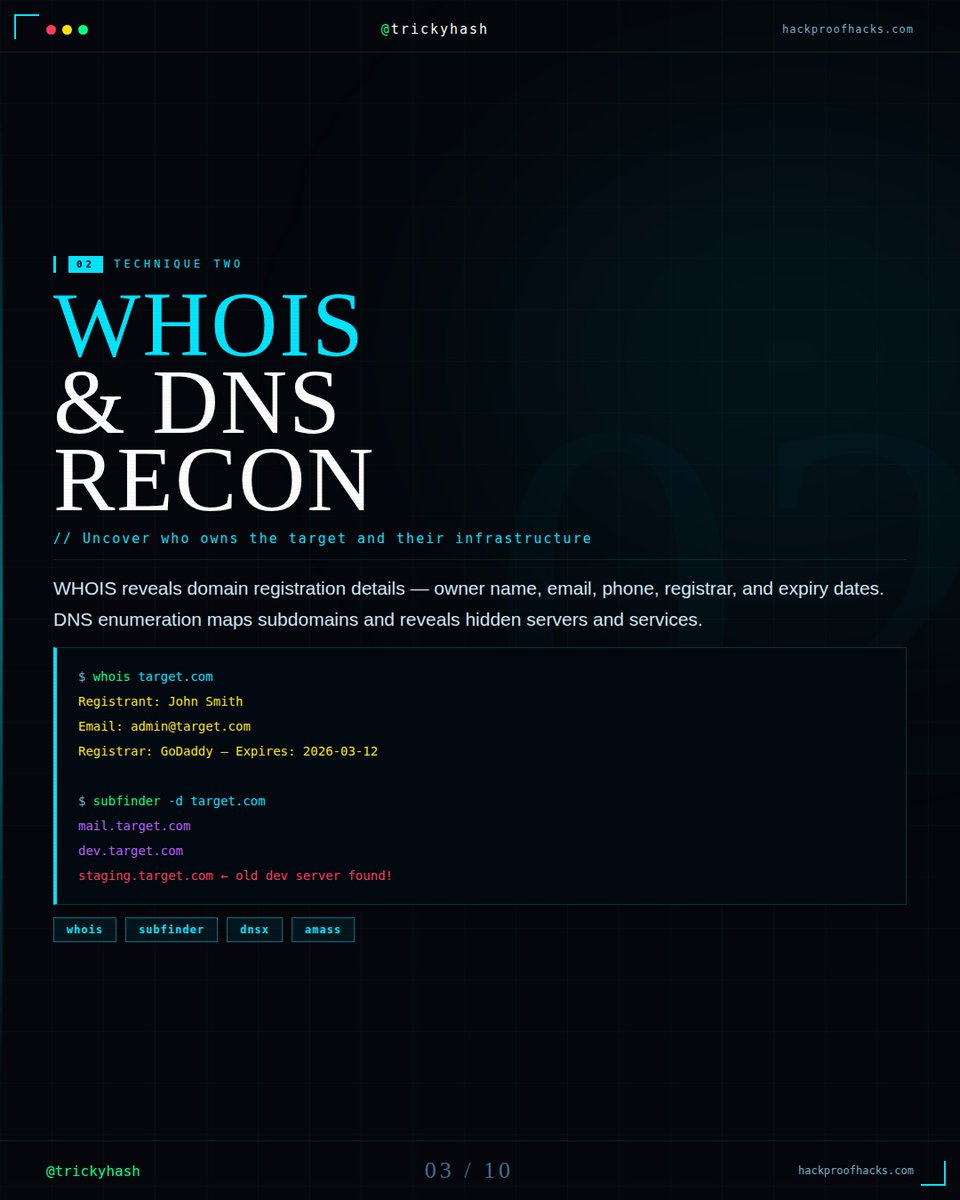
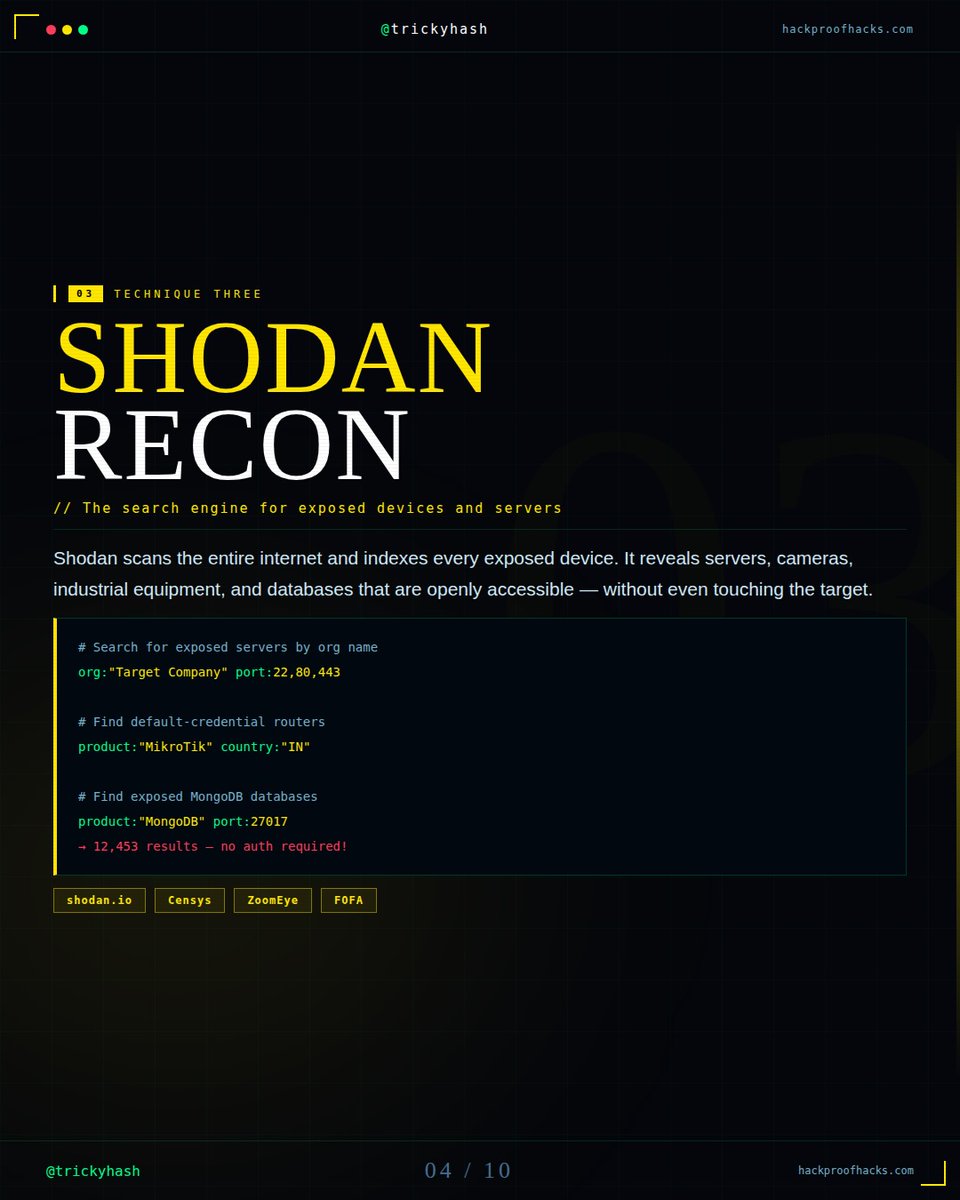
Before any security assessment begins, the most important step is reconnaissance. The more you understand a target’s public digital footprint, the better you understand its exposure. This is where OSINT becomes essential. From search engine operators and WHOIS lookups to


Something went wrong.
Something went wrong.
United States Trends
- 1. COME OVER N/A
- 2. I NEED U N/A
- 3. Good Thursday N/A
- 4. NOT TODAY N/A
- 5. Happy Friday Eve N/A
- 6. FAKE LOVE N/A
- 7. #BTS_WORLDTOUR_ARIRANG_GOYANG N/A
- 8. Selective Service N/A
- 9. #TheMasters N/A
- 10. #thursdayvibes N/A
- 11. I NEED YOU N/A
- 12. Hezbollah N/A
- 13. Whale - Buy N/A
- 14. MERRY GO ROUND N/A
- 15. Thirsty Thursday N/A
- 16. MIC DROP N/A
- 17. RUN BTS N/A
- 18. SIREN JIN ON STAGE N/A
- 19. Idol N/A
- 20. QUICK TRADE N/A