#networksecurity search results
Traffic Redirection Techniques in Network Security 🔐 #cybersecurity #networksecurity #infosec #pentesting #security
🚨 “Locked” Wi-Fi Isn’t Always Safe… 😳 Many people think: “If it’s locked, I’m secure.” That’s not always true. 🔓 Weak points like WPS can expose networks even when they look protected. Share and Comment "SECURE" 🔥👇 #cybersecurity #wifi #networksecurity #infosec
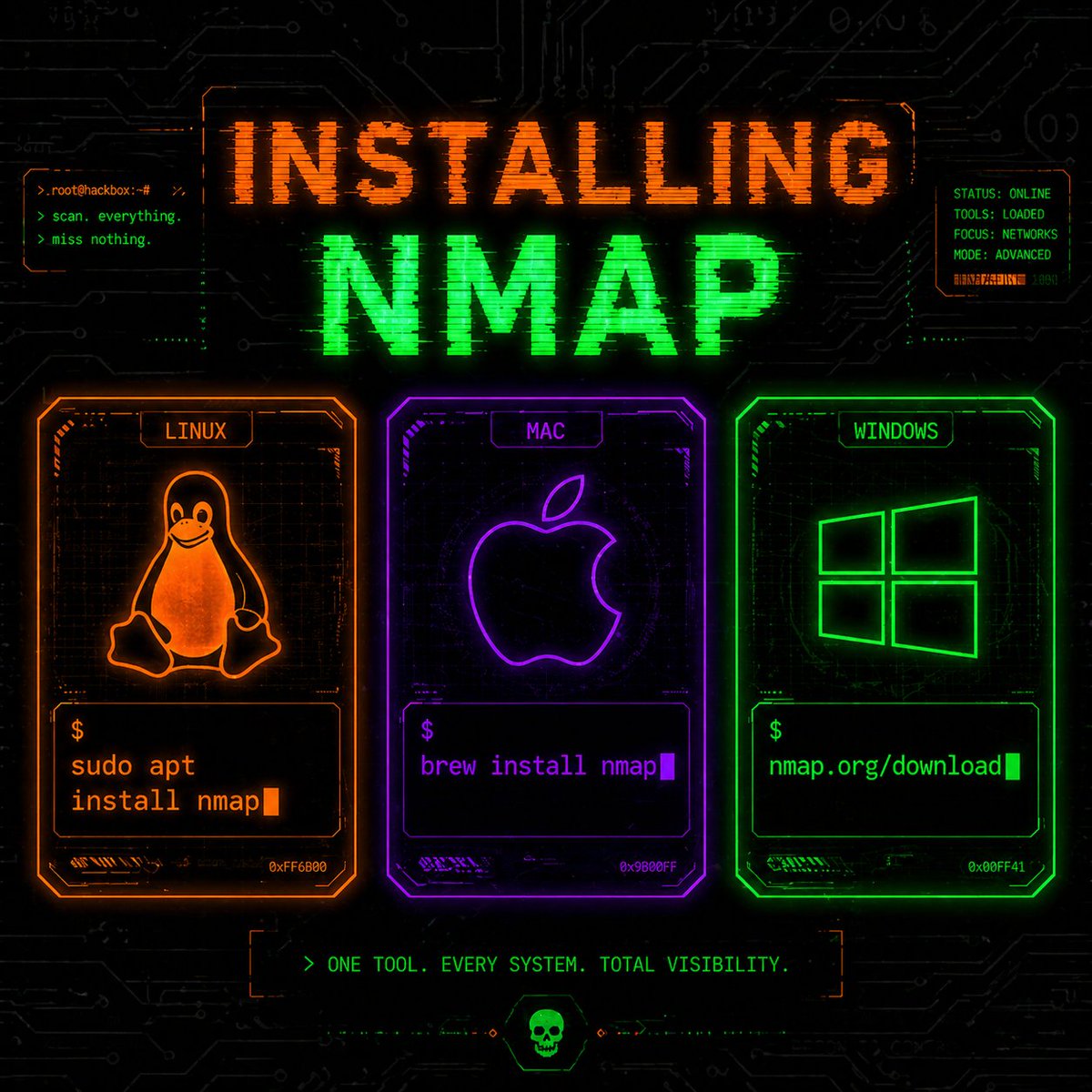
Nmap: Network Discovery and Scanning Tool 📡 Nmap is a widely used tool for network discovery and security auditing, helping identify active hosts, open ports, and running services. #nmap #networksecurity #cybersecurity #infosec #security
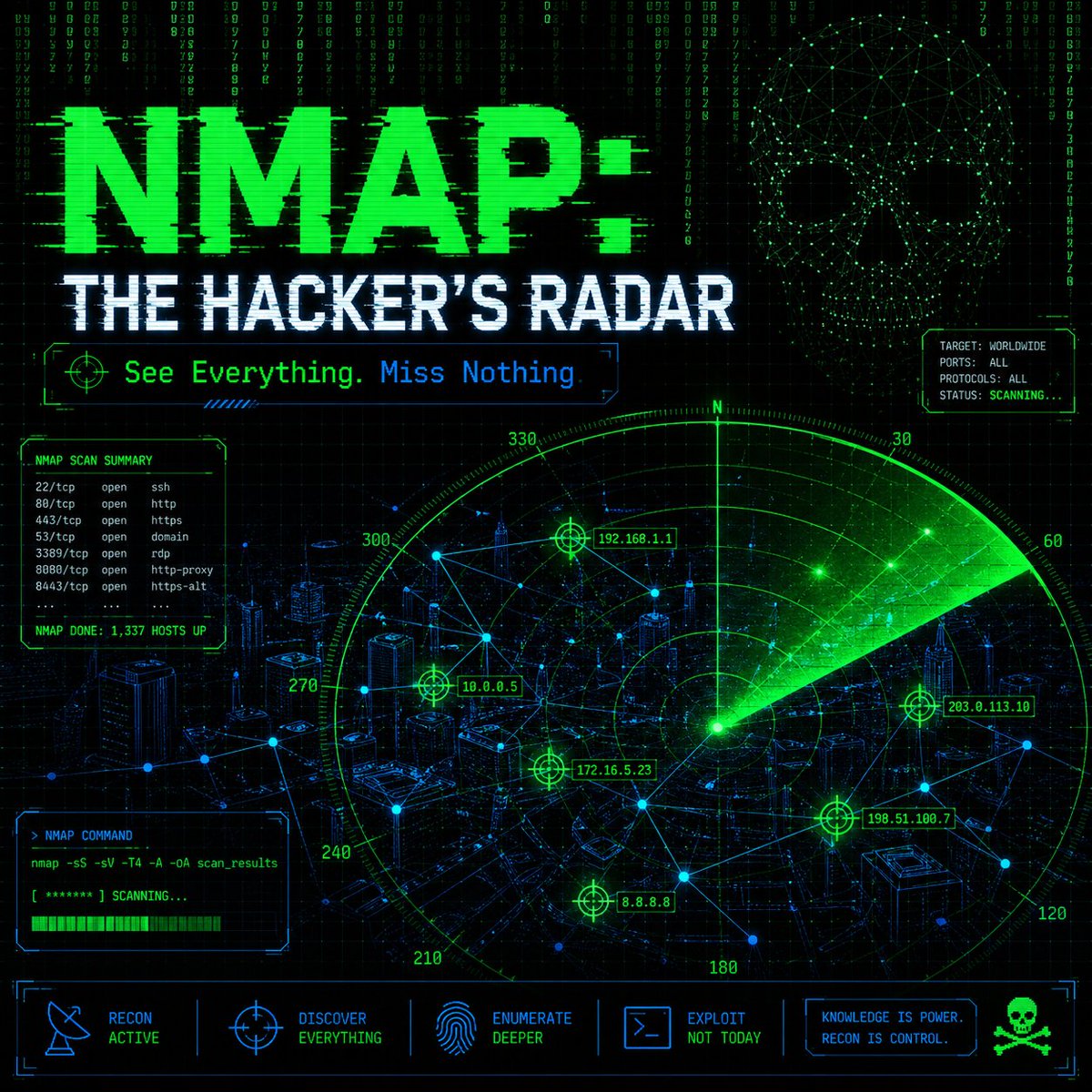


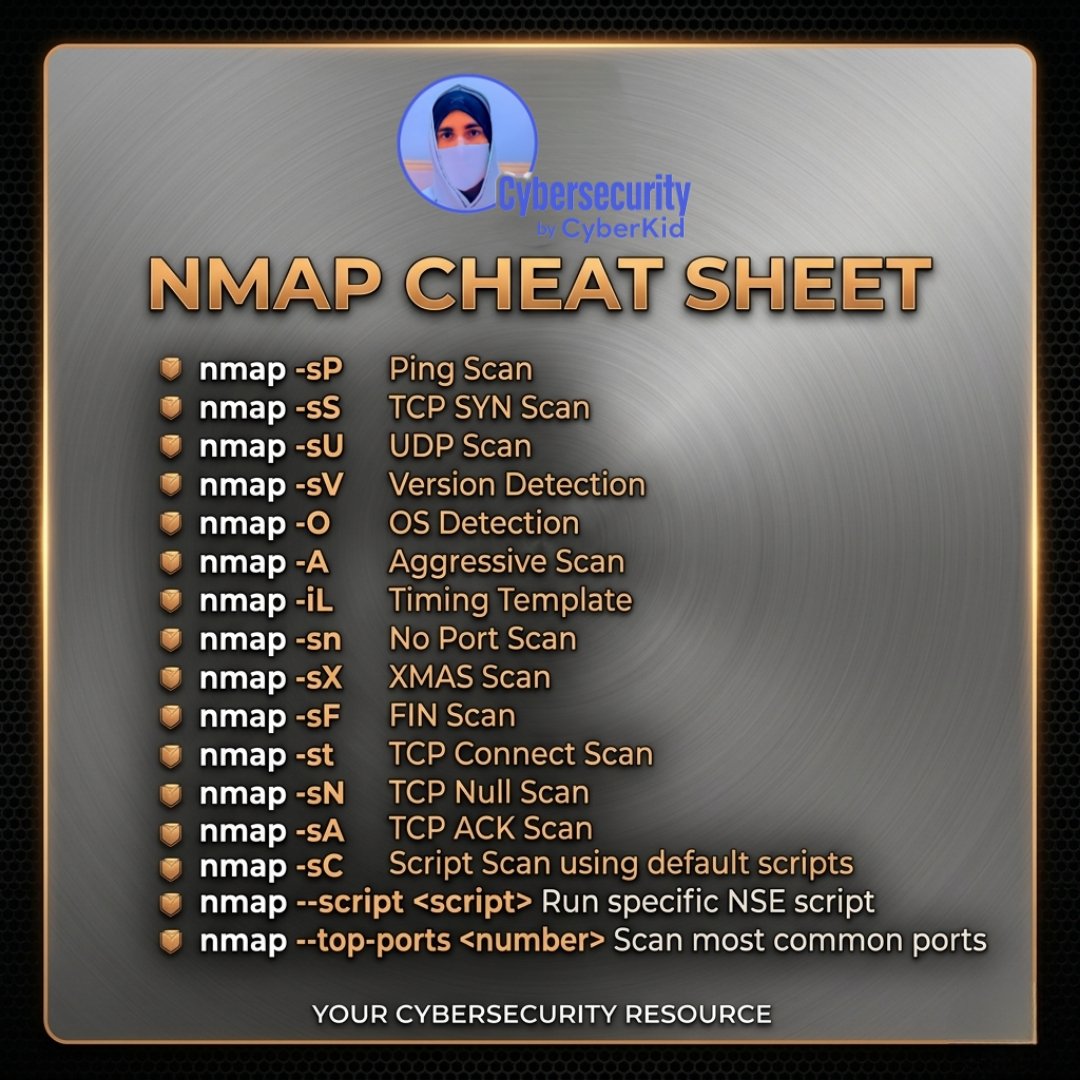
Nmap Cheat Sheet: Essential Scanning Commands 📡 A practical reference for common Nmap commands used in network discovery and security assessment. #Nmap #CyberSecurity #NetworkSecurity #Pentesting #InfoSec
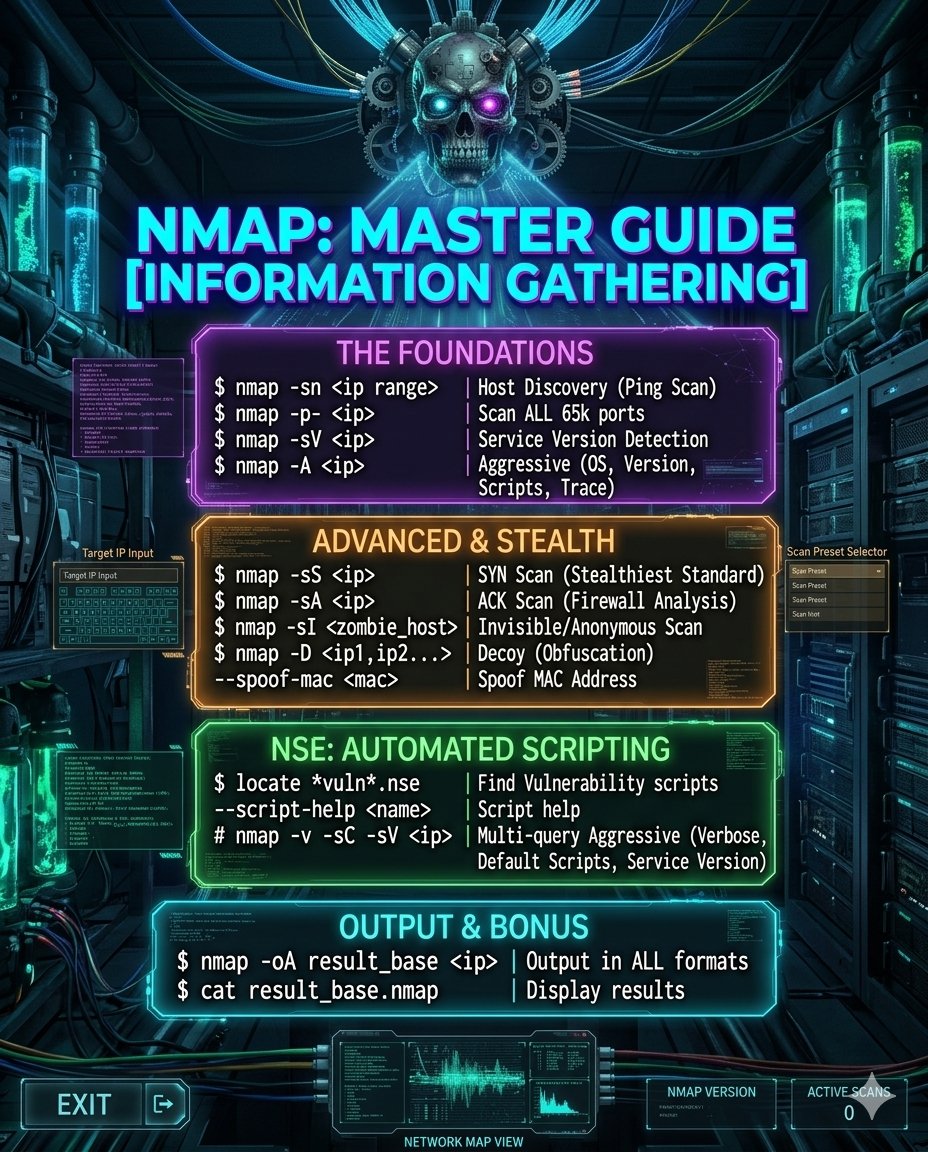
Nmap Master Guide: Information Gathering Nmap remains one of the most essential tools for network discovery, service enumeration, and security assessment in authorised environments. Comment NMAP 📡🔍👇 #nmap #cybersecurity #networksecurity #infosec #pentesting
Most firewall training teaches features. Few prepare you for real world security. 🛡️ This Fortinet path covers FortiGate, NGFW, labs, management tools, and cert prep from FCF to FCX. Explore it: bit.ly/4e3tWYR #Fortinet #NetworkSecurity #Cybersecurity
Most firewall training teaches features. Few prepare you for real world security. 🛡️ This Fortinet path covers FortiGate, NGFW, labs, management tools, and cert prep from FCF to FCX. Explore it: bit.ly/4ucHgiu #Fortinet #NetworkSecurity #Cybersecurity

🔗 Por qué las redes planas de Kubernetes fallan a gran escala Replantea la seguridad de red para plataformas cloud-native. thenewstack.io/kubernetes-net… #KubernetesNetworking #Microservices #NetworkSecurity #RoxsRoss
thenewstack.io
Why flat Kubernetes networks fail at scale
Learn how implementing security hierarchies and policy simulation to Kubernetes networks improves connectivity, security, and compliance.
That invisible device on your network? It’s not invisible to attackers. Here’s what most teams miss: zurl.co/oeKAV #CyberSecurity #AttackSurfaceManagement #NetworkSecurity #ManageEngine

Most firewall training teaches features. Few prepare you for real world security. 🛡️ This Fortinet path covers FortiGate, NGFW, labs, management tools, and cert prep from FCF to FCX. Explore it: bit.ly/4sY5gVs #Fortinet #NetworkSecurity #Cybersecurity

What does growth look like for a modern managed security provider? For Altermedios MSS, it meant moving beyond fragmented tools and building a scalable security business with an integrated platform. See how they did it: wgrd.tech/4bv2Jws #MSP #NetworkSecurity #WatchGuard

Still relying on email or manual file transfers? Access Server simplifies secure access and eliminates delays. 👉 openv.pn/4833kn3 #NetworkSecurity #AccessServer

What is identity segmentation? A modern approach to network segmentation based on user identity instead of IP or location. Why it matters for Zero Trust: openv.pn/4tXYQHj #ZeroTrust #NetworkSecurity
Juniper Networks issued patches for nearly 36 vulnerabilities in Junos OS, vLWC, and more. Top flaw CVE-2026-33784 exposes a default high-privilege password in Support Insights vLWC. #JuniperFix #NetworkSecurity #USA ift.tt/uaHFJsw
Wi-Fi roaming security practices for access network providers and identity providers - helpnetsecurity.com/2026/04/16/wba… - @WBAlliance #WiFiSecurity #CyberSecurity #NetworkSecurity #OpenRoaming #Passpoint
Complex networking ≠ better security. Access Server delivers simple, secure access to critical systems. openv.pn/4cq5uja #NetworkSecurity #AccessServer

On International Labour Day, we honor the dedication behind every secure network. Reliable firewall and network security are essential for daily business operations. Contact Sky IT Network to strengthen your Windows Server 2025 security. #InternationalLabourDay #NetworkSecurity

Remote work across multiple countries? Carbon relies on Access Server to protect client data and ensure compliance. Learn more: openv.pn/4ebx7NX #NetworkSecurity #RemoteWork #Fintech #OpenVPN

Network security matters for every organization. Use firewalls, segmentation, monitoring, and secure remote access to protect your data and reduce risk. Secure your network → AIP US #NetworkSecurity #CyberSecurity #AIPUS

🚨 New Blog Alert! Explored network traffic analysis to detect malware patterns, uncover anomalies and strengthen cybersecurity defenses 🔖GitHub Repository: github.com/mitra9917/Malw… 🔖Read here: …malware-analysis-shubham.blogspot.com/2026/04/networ… #CyberSecurity #MalwareAnalysis #NetworkSecurity #InfoSec




Responder in Network Security Assessments 🌐 Responder is a well-known tool used in authorized penetration testing to simulate network-based attacks such as LLMNR and NBT-NS poisoning. #NetworkSecurity #CyberSecurity #Pentesting #InfoSec #RedTeam
Firmware Updates Can Break Things. Here's What Every IT Team Should Know Before Hitting Update. 👉 upserra.com #FirmwareUpdate #NetworkSecurity #Firewall #CyberSecurity #Cisco #Dell #HPE #Fortinet #PaloAlto #Juniper #Huawei #Aruba #CheckPoint #SonicWall #Upserra
📷 Call: 0432 704 947 📷 Email: [email protected] 📷 Visit: cyberedgesolutions.com.au #CyberSecurity #NetworkSecurity #SecureDesign #ITInfrastructure #CyberDefense #InfoSec #DigitalPerformance #ScalableSecurity #TechArchitecture #SecureNetworks
Secure remote access helps nonprofits support people in need — safely. Learn how Access Server strengthens connectivity for a national youth support organization. 👉openv.pn/3QzMbvn #NetworkSecurity #VPNsolutions

Every click, every connection—your network sees it all. Make sure it’s protected 24/7. #NetworkSecurity #SecureNetwork #CyberAwareness #InfoSec #TechSecurity

If you're setting this up yourself: start with UniFi. Their network app walks you through VLAN tagging on each port and WiFi SSID. Separate SSIDs per VLAN, tag your switch ports, done. Your smart home gets smarter without becoming a liability. #VLAN #NetworkSecurity
The detail most people miss: inter-VLAN routing rules. Blocking the IoT VLAN isn't enough if your firewall allows return traffic back. Set explicit DENY rules from IoT → Main at the router level. I use pfSense or UniFi — both let you do this in under 10 minutes. #NetworkSecurity
Network security matters for every organization. Use firewalls, segmentation, monitoring, and secure remote access to protect your data and reduce risk. Secure your network → AIP US #NetworkSecurity #CyberSecurity #AIPUS

New episode from @myweirdprompts: DNS Blocking Showdown: Pi-hole vs AdGuard Home myweirdprompts.com/episode/pi-hol… #MyWeirdPrompts #podcast #networksecurity #privacy
April from FastNetMon in one post: → LiveView launched → 3 new Advanced releases → Pentanet case study published → RIPE SEE 14 in Belgrade → Bluesky, Mastodon DDoS attacks + Operation PowerOFF Full roundup: fastnetmon.com/2026/04/30/net… #networksecurity
On International Labour Day, we honor the dedication behind every secure network. Reliable firewall and network security are essential for daily business operations. Contact Sky IT Network to strengthen your Windows Server 2025 security. #InternationalLabourDay #NetworkSecurity

@TechCrushHQ @_favour_Ay @UzoukwuEriciyke @TechCrunch @InfosecurityMag @MsftSecIntel @PowerShellMag @tecmint @CiscoSecure @CiscoNetworking @Cisco @CiscoNetAcad @CISAgov @CISACyber @IamTheCyberChef @StaySafeOnline @NISTcyber @cyber @NSACyber #BuildInPublic #NetworkSecurity #Cisco
They refused to take shortcuts. Our founders, Kumar Mehta and Apurva Mehta built networking and security on the same foundation from day one, and Concerto 13.1.1 is the latest proof that bet was right. Learn more: bit.ly/428ryJ5 #NetworkSecurity #ZeroTrust #SASE


No scanning. No exploits. No brute force. Just Responder on an unsegmented network. 47 credentials captured in 20 minutes. #hacking #networksecurity
Your business runs on your network. Downtime and vulnerabilities aren’t an option. Discover practical ways to build a resilient, secure network in our latest blog post. na2.hubs.ly/H04-X3m0 #XceptionalSecurty #NetworkSecurity
One device for network, security & comms. The @GrandstreamNet GCC6010 series combines VPN, firewall, IP PBX & Wi-Fi. Simple, powerful, built for SMBs. Learn more: hubs.li/Q04d_qBJ0 #UnifiedCommunications #NetworkSecurity #SMB #NetworkInfrastructure

Microsegmentation without identity context is just network isolation. Real control comes from who is allowed to communicate and why. #ZeroTrust #NetworkSecurity
🔐 Protect your business before hackers strike. Cyber threats are growing every day🚀 #CyberSecurity #NetworkSecurity #CloudSecurity #DataProtection #ITSecurity #BusinessSecurity #DigitalSafety #CyberThreats #InformationSecurity #SecureNetwork #EnterpriseSecurity #CyberDefense

Something went wrong.
Something went wrong.
United States Trends
- 1. Embiid N/A
- 2. Embiid N/A
- 3. Celtics N/A
- 4. Jaylen Brown N/A
- 5. Golden Tempo N/A
- 6. Sixers N/A
- 7. Derrick White N/A
- 8. #AEWCollision N/A
- 9. Tatum N/A
- 10. Kentucky Derby N/A
- 11. Paul George N/A
- 12. Queta N/A
- 13. Great White N/A
- 14. Logan Stankoven N/A
- 15. Cherie DeVaux N/A
- 16. Mazzulla N/A
- 17. Live by the 3 N/A
- 18. Reggie Miller N/A
- 19. #Svengoolie N/A
- 20. Nick Nurse N/A