#edrevasion search results
A new technique, "EDR-Freeze," uses a built-in Windows feature to suspend antivirus and EDR processes, giving attackers a critical window to operate undetected. #Cybersecurity #EDREvasion #WindowsDefender #Malware #Hacking securityonline.info/edr-freeze-how…
securityonline.info
EDR-Freeze: How a Researcher Turned Windows Error Reporting Into a Weapon Against Antivirus
A new technique, "EDR-Freeze," uses a built-in Windows feature to suspend antivirus and EDR processes, giving attackers a critical window to operate undetected.
If you're still using `whoami` to check context during post-ex, try `whoami /priv` instead. Sometimes the keys are in the privileges, not the name. SeDebugPrivilege? Time to play in LSASS. #RedTeam #PostEx #EDREvasion #WindowsInternals
Process injection via Atom Tables is an underrated stealth tactic. Store shellcode in an atom, retrieve it in a remote process, and execute via callback. Avoids common memory scanning detections. #RedTeam #EDREvasion #Infosec #CyberSecurity
Blog post up on #HellsGate #EdrEvasion written in #Rust, using direct syscalls to prevent usermode hooking & static scanning. fluxsec.red/rust-edr-evasi… #redteam #hacking #rustlang #pentesting #cyber #cybersecurity #infosec #MalwareDevelopment #BlueTeam #SecurityResearch #Malware
I wrote a full deep-dive on the core logic, stub pool generation, and bypassing static/dynamic analysis on the blog. Blog: arth.imbeddex.com/malware/develo… Repo: github.com/Oorth/YetAnoth… #MalwareDev #RedTeaming #EDREvasion #ReverseEngineering
In 2025, ransomware isn’t just malware—it’s identity abuse. 🧑💻 Valid creds = lateral movement 🔐 AD misconfigs = escalation ⚠️ No malware = EDR blindspots Focus on least privilege, AD attack paths, and identity monitoring. #Ransomware #EDREvasion 🔗 delasecurity.com

If you're pivoting via WMI and still using `wmic` instead of `Invoke-WmiMethod` with obfuscated PowerShell, you might as well email the SOC your payload. #RedTeam #EDREvasion #PowerShell #Infosec
That “harmless” DLL sideload you missed during triage? It’s been the attacker’s silent RDP gateway for 3 weeks. No beacon, no creds, just your own trust and lazy detections. #EDRevasion #redteam
Pro tip: Most companies whitelist Zoom. Drop a malicious payload as `ZoomInstallerFull.exe`, sign it with a cheap EV cert, and watch EDR snooze like it’s Sunday. #RedTeam #EDRevasion #MalwareDev #CyberSecurity
I am very proud to share that I gave my first talk on Security BSides Athens 2024 on June 29. About EDR Evasion, in this talk we utilized C/C++ to bypass modern EDRs #BSidesAth #EDREvasion #RedTeam #MalwareDevelopment




BestEdrOfTheMarket is an open-source lab for training and learning EDR evasion techniques, utilizing Windows NT's telemetric capabilities. github.com/Xacone/BestEdr… #EDREvasion
Ransomware gangs are using the Shanya.exe packer to hide EDR-killers — making defenses blind before the attack even begins. Obfuscation is their new edge. 🧩💀 #Ransomware #EDREvasion buff.ly/ZdCdbiO
Malicious DLL sideloading via trusted AV vendors is still gold. Drop a rogue DLL named identically to a legit one, but in a writable path the signed binary loads first. AVs often whitelist their own paths. Test with LOLBins like MpCmdRun.exe. #redteam #EDRevasion #pentest
Most companies block *.exe attachments but still allow .iso, .img, or .lnk files. Pack your payload in a virtual disk, drop a shortcut, and watch AV stare at it like it’s a modern art piece. #RedTeam #EDRevasion #Phishing #CyberSecurity
Ransomware attackers are now using ESXi systems as stealthy tunnels to C2 servers, blending into legit traffic. Also, Andariel group's RID hijacking & new EDR evasion techniques are on the rise. Stay vigilant! #Cybersecurity #Ransomware #EDREvasion #ESXi #ThreatIntel
Ransomware brokers are abusing EDR tools to execute malware stealthily — turning defenses into delivery systems. Even security layers can be weaponized. 🛡️💀 #EDREvasion #Ransomware buff.ly/9aWA57Q
Company: “We disabled PowerShell to stop attackers.” Me with signed LNK + mshta + COM object persistence: *laughs in LOLBAS* #RedTeam #EDREvasion #PostExploitation #LOLBAS #CyberSecurity
Non mi sono distratto. Volevo vedere se pubblicando meno articoli li leggete. Capite la gravità della situazione ed i messaggi che vi danno? #edrevasion #ransomware lnkd.in/ddSbRi5c
We ran the engagement clean. No alerts, no detection, full dwell time. That's the goal. Bharath's course at @BlackHatEvents teaches you how to actually get there. blackhat.com/us-26/training… #BHUSA #RedTeam #EDREvasion

Ghosting the Endpoint: EDR Evasion 101 EDR systems are the digital sentinels, watching every move on the endpoint. #RedTeam #EDREvasion #Cybersecurity #OffensiveSecurity #Hacking #Stealth #ThreatEmulation #PurpleTeam #AdversarySimulation #Infosec #TTPs #PostExploitation


I wrote a full deep-dive on the core logic, stub pool generation, and bypassing static/dynamic analysis on the blog. Blog: arth.imbeddex.com/malware/develo… Repo: github.com/Oorth/YetAnoth… #MalwareDev #RedTeaming #EDREvasion #ReverseEngineering
We ran the engagement clean. No alerts, no detection, full dwell time. That's the goal. Bharath's course at @BlackHatEvents teaches you how to actually get there. blackhat.com/us-26/training… #BHUSA #RedTeam #EDREvasion

One byte (0xC3) written to EtwEventWrite = ALL ETW telemetry dead. EDR can't see PowerShell, .NET assembly loads, or anything. #redteam #CRTO #EDRevasion #cybersecurity
New BlackSanta EDR-killer malware is targeting HR departments — attackers are aiming where data and trust intersect. Even people teams are now frontline targets. 🎯💀 #EDREvasion #SocialEngineering bleepingcomputer.com/news/security/…
Crypto24 ransomware targets top firms in finance, manufacturing, entertainment, and tech using custom EDR evasion tools, privilege escalation, and security disabling tactics for data exfiltration and encryption. #Crypto24 #EDREvasion #DataTheft ift.tt/yBQl76L
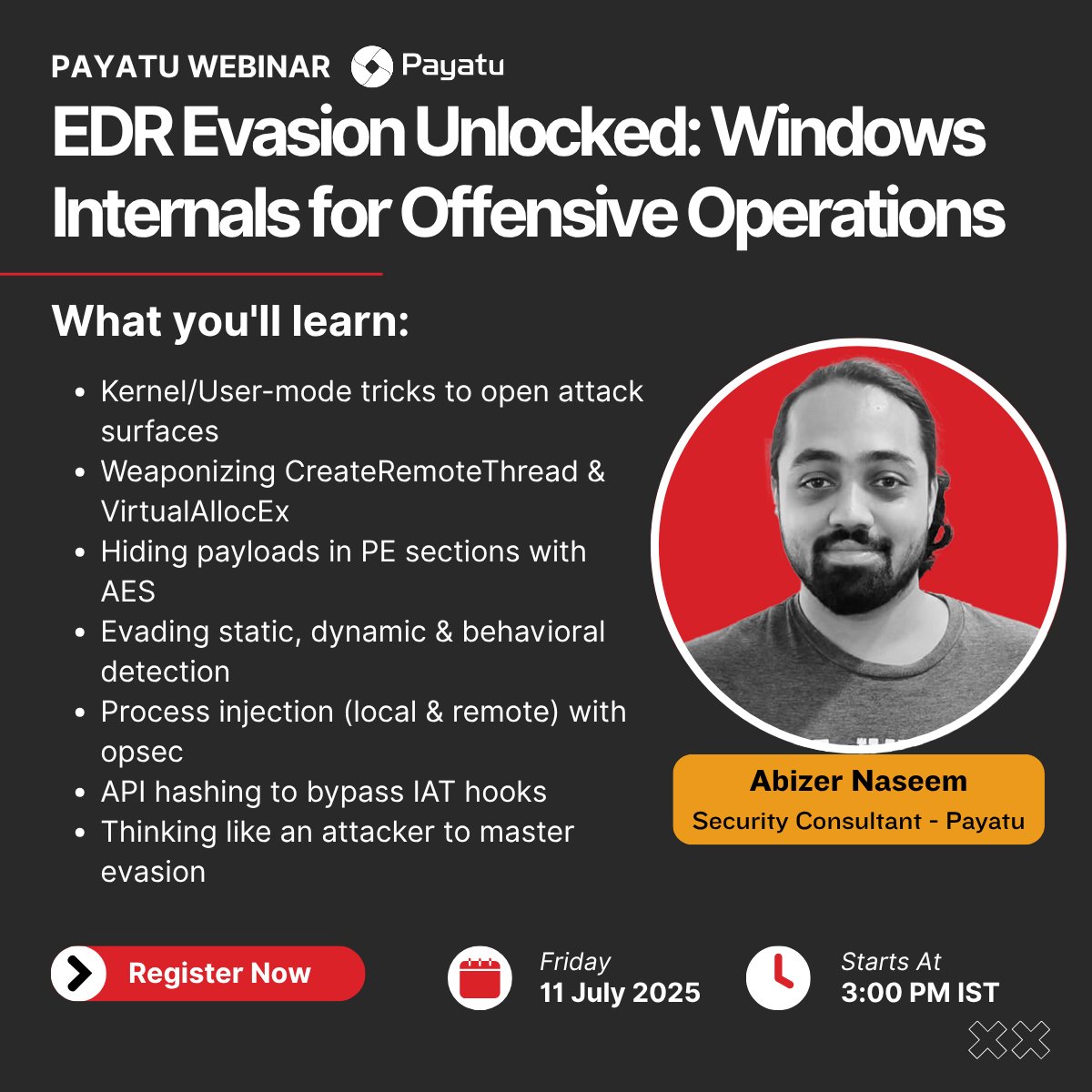
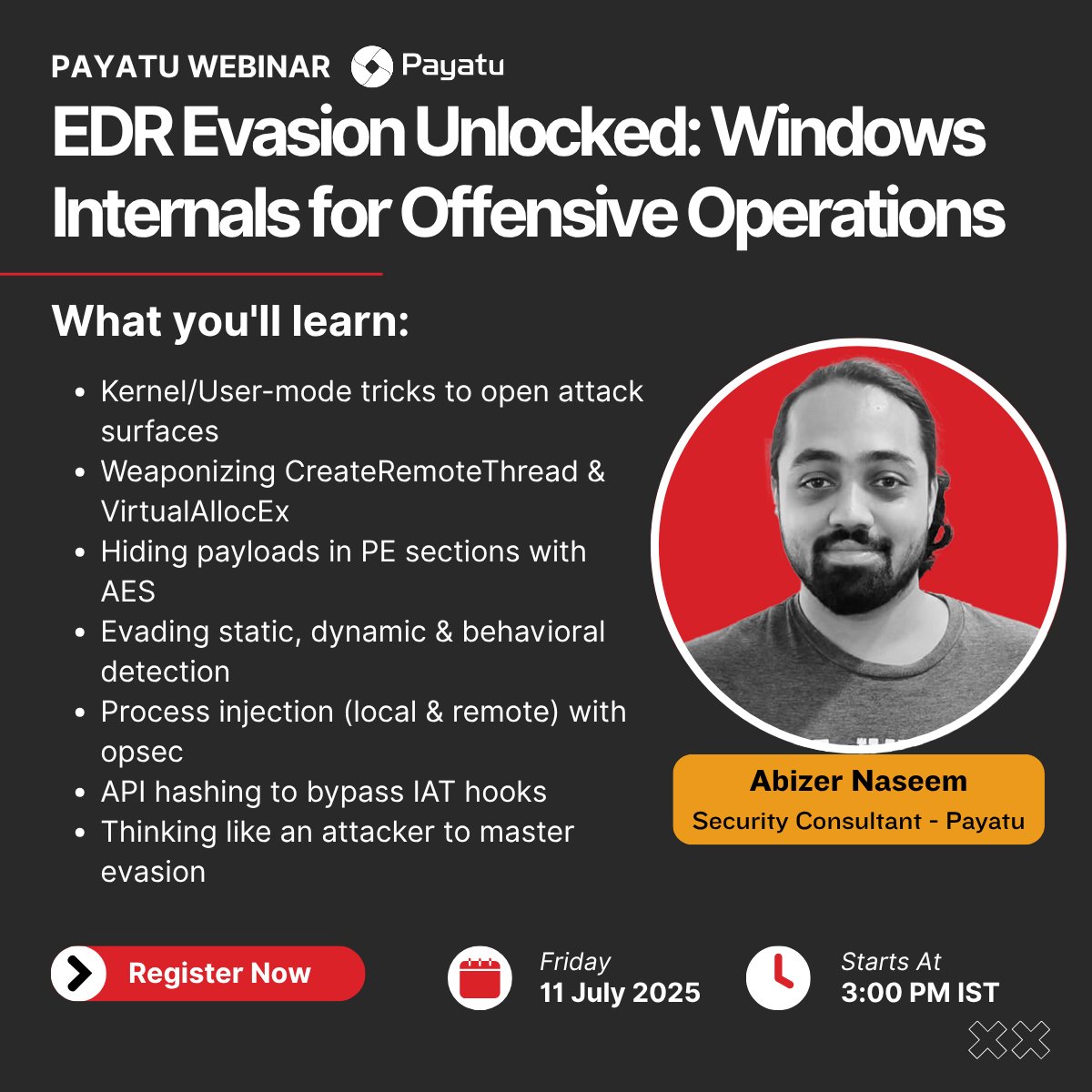
EDR Evasion, Unlocked! From Windows internals to shellcode loaders, Abizer Naseem breaks down how attackers bypass EDRs and what defenders must know. 🎥 Watch now: youtu.be/CY1DHmQoxtM?si… #EDREvasion #RedTeam #CyberSecurity #Payatu
Ghosting the Endpoint: EDR Evasion 101 EDR systems are the digital sentinels, watching every move on the endpoint. #RedTeam #EDREvasion #Cybersecurity #OffensiveSecurity #Hacking #Stealth #ThreatEmulation #PurpleTeam #AdversarySimulation #Infosec #TTPs #PostExploitation


2025 threat actors are chaining LLMs with living-off-the-land binaries (LOLBins) to evade EDR and simulate human behavior in post-exploitation. Full TTP breakdown in VerSprite’s report: 🔗 versprite.com/blog/2025-envi… #EDREvasion #LOLBins #PostExploitation #CyberThreatIntel
versprite.com
2025 ENVISIONS Geopolitical Critical Threat Report
Geopolitical Critical Intelligence for Tomorrow's Security Landscape The ENVISIONS Geopolitical Critical Threat Report 2025 delivers forward-looking
WEBINAR ALERT: EDR Evasion Unlocked: Windows Internals for Offensive Operations | Payatu 🗓️ 11th July, 3 PM IST 🔗 Register here: lnkd.in/dwDXQjcS #EDREvasion #RedTeam #CyberSecurityWebinar #MalwareAnalysis #WindowsSecurity #Payatu #InfoSecWebinar
In 2025, ransomware isn’t just malware—it’s identity abuse. 🧑💻 Valid creds = lateral movement 🔐 AD misconfigs = escalation ⚠️ No malware = EDR blindspots Focus on least privilege, AD attack paths, and identity monitoring. #Ransomware #EDREvasion 🔗 delasecurity.com

EDRs aren’t telling you the full story. Register today for our live session to discover how Lumu Technologies exposes what EDR can't see. >> zurl.co/278XI 🗓️ June 10 🕑 2:00pm ET #Live #EDR #EDREvasion #Cybersecurity #Training #Webinar
🚨 AV/EDR evasion — no alerts, no flags. 🎯 Our custom implant evaded: ✔️ Microsoft Defender (real-time on) ✔️ Sandboxes & analysis tools Encryption + Obfuscation + Stealth Injection. Watch the demo 👇 youtube.com/watch?v=25KTeg… #MalDev #AVEvasion #EDREvasion #RedTeam #Shellcode
youtube.com
YouTube
Evading AV/EDR — and What Comes Next
Most EDRs trust anything signed by Microsoft. So do sysadmins. So does your SOC. Spoof trust, live in memory, and watch the blue team chase their own tail. #EDRevasion #RedTeam #Infosec #WindowsInternals
That “harmless” DLL sideload you missed during triage? It’s been the attacker’s silent RDP gateway for 3 weeks. No beacon, no creds, just your own trust and lazy detections. #EDRevasion #redteam
If you're pivoting via WMI and still using `wmic` instead of `Invoke-WmiMethod` with obfuscated PowerShell, you might as well email the SOC your payload. #RedTeam #EDREvasion #PowerShell #Infosec
Company: “We disabled PowerShell to stop attackers.” Me with signed LNK + mshta + COM object persistence: *laughs in LOLBAS* #RedTeam #EDREvasion #PostExploitation #LOLBAS #CyberSecurity
If you're still using `whoami` to check context during post-ex, try `whoami /priv` instead. Sometimes the keys are in the privileges, not the name. SeDebugPrivilege? Time to play in LSASS. #RedTeam #PostEx #EDREvasion #WindowsInternals
Most companies block *.exe attachments but still allow .iso, .img, or .lnk files. Pack your payload in a virtual disk, drop a shortcut, and watch AV stare at it like it’s a modern art piece. #RedTeam #EDRevasion #Phishing #CyberSecurity
Pro tip: Most companies whitelist Zoom. Drop a malicious payload as `ZoomInstallerFull.exe`, sign it with a cheap EV cert, and watch EDR snooze like it’s Sunday. #RedTeam #EDRevasion #MalwareDev #CyberSecurity
Malicious DLL sideloading via trusted AV vendors is still gold. Drop a rogue DLL named identically to a legit one, but in a writable path the signed binary loads first. AVs often whitelist their own paths. Test with LOLBins like MpCmdRun.exe. #redteam #EDRevasion #pentest
I am very proud to share that I gave my first talk on Security BSides Athens 2024 on June 29. About EDR Evasion, in this talk we utilized C/C++ to bypass modern EDRs #BSidesAth #EDREvasion #RedTeam #MalwareDevelopment




WEBINAR ALERT: EDR Evasion Unlocked: Windows Internals for Offensive Operations | Payatu 🗓️ 11th July, 3 PM IST 🔗 Register here: lnkd.in/dwDXQjcS #EDREvasion #RedTeam #CyberSecurityWebinar #MalwareAnalysis #WindowsSecurity #Payatu #InfoSecWebinar
In 2025, ransomware isn’t just malware—it’s identity abuse. 🧑💻 Valid creds = lateral movement 🔐 AD misconfigs = escalation ⚠️ No malware = EDR blindspots Focus on least privilege, AD attack paths, and identity monitoring. #Ransomware #EDREvasion 🔗 delasecurity.com

Ghosting the Endpoint: EDR Evasion 101 EDR systems are the digital sentinels, watching every move on the endpoint. #RedTeam #EDREvasion #Cybersecurity #OffensiveSecurity #Hacking #Stealth #ThreatEmulation #PurpleTeam #AdversarySimulation #Infosec #TTPs #PostExploitation


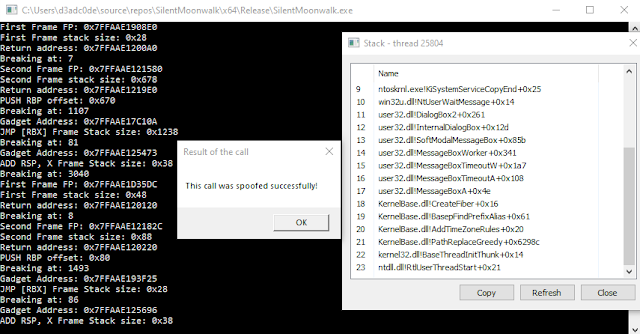
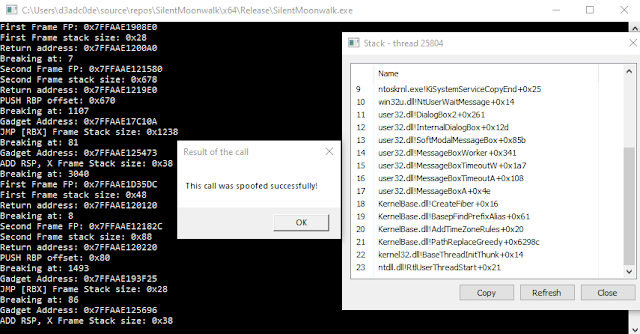
SilentMoonwalk - PoC Implementation Of A Fully Dynamic Call Stack Spoofer #AvEvasion #EdrEvasion #SilentMoonwalk #StackSpoofing dlvr.it/SnkmFf
The ODPC teaches you to build custom malware and C2 tooling to maintain persistence. Take advantage of our Winter Sale thru 1/10: 40% off all training, 2 courses for $600, 3 for $900, or all 6 for $1800! Enroll at whiteknightlabs.com/?utm_campaign=… #EDREvasion #OffensiveSecurity #WinterSale

Play hard ,play smart. #Cybersecurity #EDREvasion #SecurityLeadership #SOC #CISO #ThreatIntelligence #Resilience #ZeroTrust #SecurityArchitect #RedTeam #BlueTeam #DefendersGuide #PlayHardPlaySmart
⚠️ New exploit alert: EDR-Redir uses Windows’ Bind & Cloud Filter drivers to hijack EDR folders - no kernel access needed. ➡️ Attacker can isolate Elastic, Sophos, even disable Defender with a single API trick. A new level of #EDREvasion? 💭 Drop your thoughts + follow @TechNadu

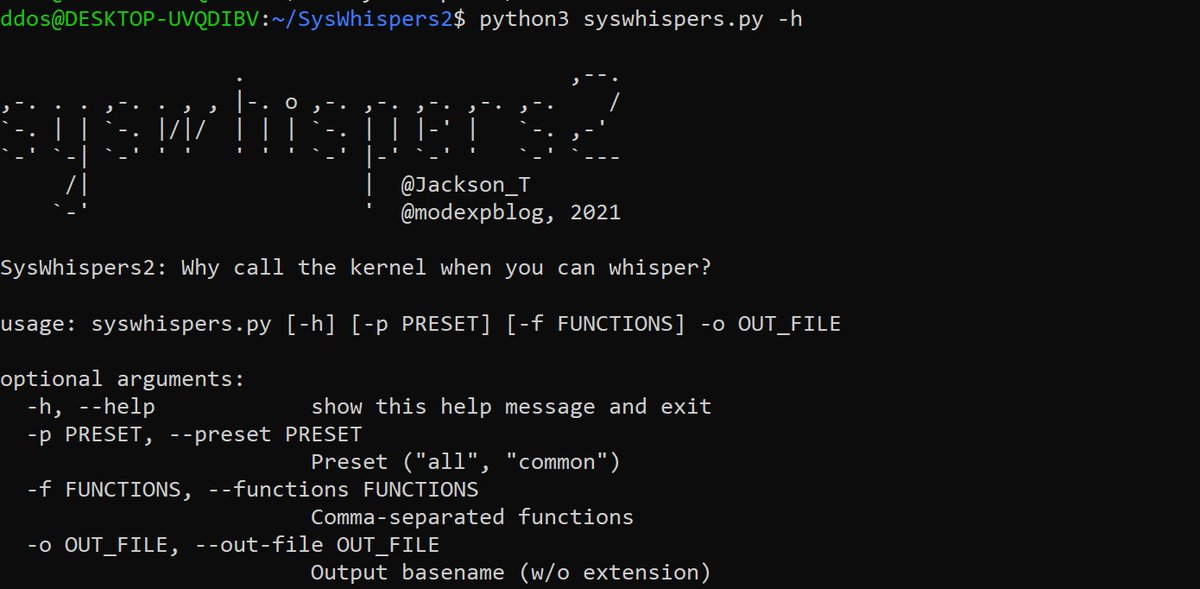
#Hacking #EDREvasion #Malware #Vulnerability #CyberCrime #CyberAttack #CyberSecurity SysWhispers2: AV/EDR evasion via direct system calls. securityonline.info/syswhispers2-a…
How attackers dynamically adapt PowerShell, JavaScript, and loaders during live campaigns to evade EDR (Lumma, RansomHub, GhostPairing examples). redsecuretech.co.uk/blog/post/dyna… #CyberSecurity #Malware #EDREvasion #ThreatHunting #PowerShell

2 Days Left! Join Modern Red Teaming & EDR Evasion Techniques with Milton Araújo on Feb 13, 2026. Register now – attendee.gotowebinar.com/register/15920… #CyberSecurity #RedTeaming #EDREvasion #HTMLSmuggling #Webinar

Threat actors exchange beacons for badgers to evade endpoint security - helpnetsecurity.com/2022/07/07/bru… - @Unit42_Intel @NinjaParanoid #BRc4 #BruteRatel #EDRevasion #MalwareDetection #Redteam #enterprise #CybersecurityNews

We ran the engagement clean. No alerts, no detection, full dwell time. That's the goal. Bharath's course at @BlackHatEvents teaches you how to actually get there. blackhat.com/us-26/training… #BHUSA #RedTeam #EDREvasion

We’re excited to meet all of you at @RSAConference! Book a demo at RSAC 2025, take home a free gift, and discover how Lumu strengthens your security operations with real-time threat visibility and response. >> zurl.co/yfMuj #RSAC #RSAC2025 #EDREvasion #Cybersecurity

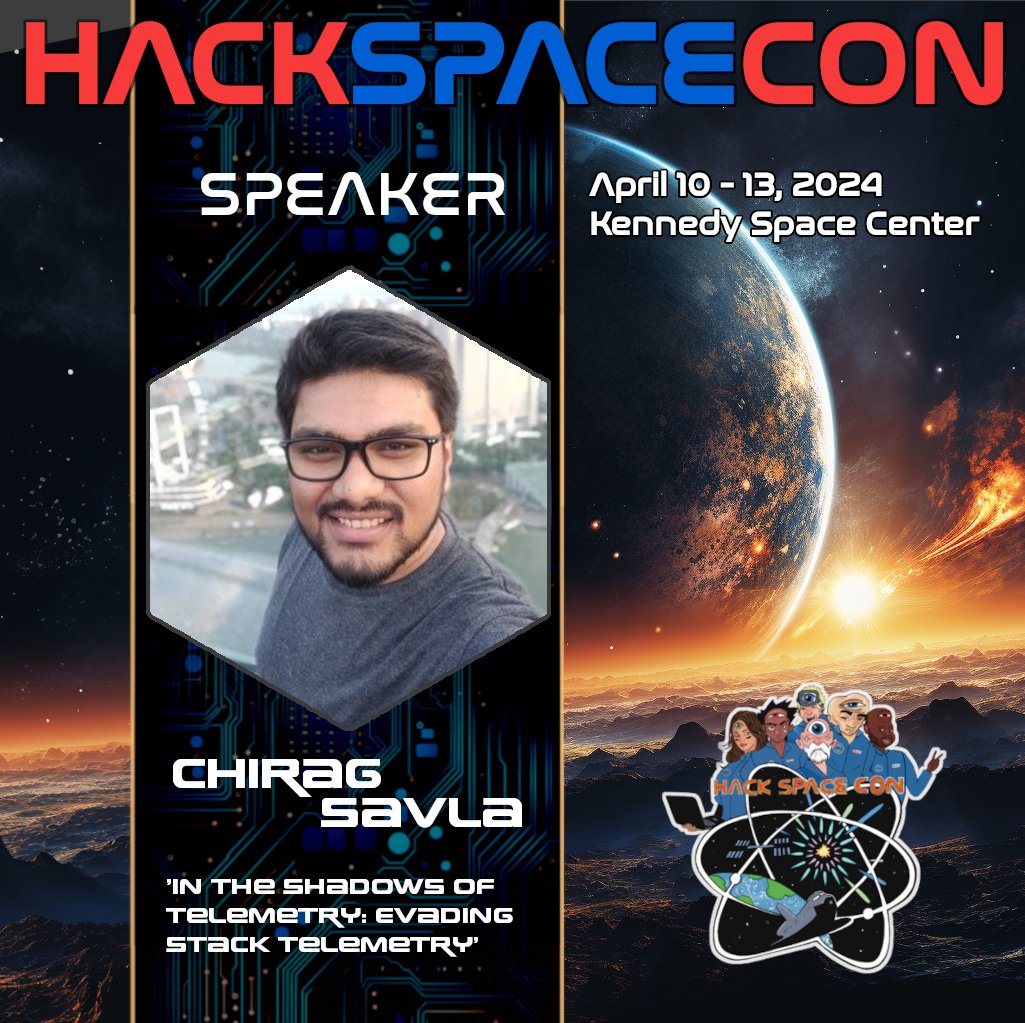
Dive into "In the Shadows of Telemetry" to learn about evading stack telemetry in EDR systems with @chiragsavla94! Explore advanced evasion techniques and new undocumented API calls for proxy loading. A must for cybersecurity pros! #CyberSecurity #EDREvasion #maldev #redteam
EDR evasion is getting smarter. Attackers are customizing the open-source Sliver framework to slip past detection, turning red-team tools into stealth weapons and testing how fast defenses can adapt. READ: bit.ly/4h0Rsoz #CanaryTrap #EDR #EDRevasion

SilentMoonwalk - PoC Implementation Of A Fully Dynamic Call Stack Spoofer dlvr.it/SmCvx7 #AvEvasion #EdrEvasion #SilentMoonwalk #StackSpoofing via KitPloit
Cyber attackers are constantly developing new techniques to bypass endpoint defenses. Are you up to date on the latest EDR evasion tactics? Learn how to better protect your organization against these stealthy attacks. >> zurl.co/DiY9 #Cybersecurity #EDR #EDREvasion

Discover #EDR evasion tactics, from CPL Side-Loading to Code Injection, and how hackers employ ChatGPT for polymorphic keyloggers. Learn how to elevate your defenses against these sophisticated threats in our blog. >> zurl.co/FpKx #Cybersecurity #EDREvasion #Hacker

Tired of payloads being caught by signature scans? The ODPC teaches you to engineer custom reflective DLL loaders and tailored AMSI bypasses from scratch to outmaneuver modern EDR. Explore more at whiteknightlabs.com/?utm_campaign=… #ODPC #RedTeaming #EDREvasion #Infosec

Something went wrong.
Something went wrong.
United States Trends
- 1. SPLC N/A
- 2. Southern Poverty Law Center N/A
- 3. TACO Tuesday N/A
- 4. Cursor N/A
- 5. Jaylen Brown N/A
- 6. Chelsea N/A
- 7. David Wilcock N/A
- 8. #LightningStrikes N/A
- 9. #CashAppFriday N/A
- 10. Steven Seagal N/A
- 11. Marc Davis N/A
- 12. Smallpox N/A
- 13. Giancarlo Stanton N/A
- 14. Save America Act N/A
- 15. Tifa N/A
- 16. Big G N/A
- 17. Matt Ryan N/A
- 18. Rosenior N/A
- 19. Unite the Right N/A
- 20. Reynaldo Lopez N/A