#pathtraversal search results
ESET warns of an actively exploited WinRAR zero-day (CVE-2025-8088). The path traversal flaw allows attackers to execute code by crafting malicious archives. #WinRAR #ZeroDay #PathTraversal #Cybersecurity #PatchNow securityonline.info/winrar-update-…
Critical 9.8 flaws in goshs v2.0.0-beta.2 allow unauthenticated attackers to write or delete any file on your system. Update to v2.0.0-beta.3 immediately! #goshs #PathTraversal #CyberSecurity #InfoSec #RCE #Golang #SecurityPatch securityonline.info/goshs-vulnerab…

A critical flaw (CVE-2025-4517, CVSS 9.4) in Python's tarfile module allows arbitrary file reads/writes outside the extraction directory. PoC is public; update immediately! #PythonSecurity #TarfileVulnerability #PathTraversal #Cybersecurity securityonline.info/critical-pytho…
Another day another bug 🔥 Here's an example for code I found in one of my targets, by searching for the following regex: /res.download\(.*\`$/ And this regex found a #PathTraversal vulnerability for me 🪲 #BugBounty #bugbountytips #codereview


OpenJS Foundation released critical Node.js updates patching two high-severity flaws (CVE-2025-27210, CVE-2025-27209) affecting Windows apps, including path traversal bypass and HashDoS. #Nodejs #SecurityUpdate #PathTraversal #HashDoS #CybersecurityAlert securityonline.info/high-severity-…
A high-severity path traversal flaw (CVE-2025-23092) in Mitel OpenScape Accounting Management allows authenticated admins to upload malicious files for RCE. Update now! #MitelSecurity #OpenScape #PathTraversal #Cybersecurity #Vulnerability securityonline.info/mitel-openscap…
A path traversal flaw (CVE-2025-62725) in Docker Compose lets attackers overwrite host files via remote OCI artifact annotations, triggered by read-only commands. #DockerCompose #PathTraversal #CI_CD #Cybersecurity securityonline.info/docker-compose…
A study reveals widespread path traversal (CWE-22) in open-source projects, exacerbated by LLMs generating insecure code. Automated detection and patching are critical. #PathTraversal #CodeSecurity #LLMVulnerabilities #OpenSourceSecurity securityonline.info/path-traversal…
🚨 New Writeup Alert! 🚨 "Top File Read Bug POCs that made $20000" by It4chis3c is now live on IW! Check it out here: infosecwriteups.com/3043e676d8d5 #tipsandtricks #hacking #pathtraversal #bugbounty #localfileread
🪟 Path traversal in Sleuth Kit’s tsk_recover? Because even forensic tools can’t be trusted with “don’t write outside this folder.” Your disk image just became a write-prank. windowsforum.com/threads/cve-20… #PathTraversal #SleuthKit #Cve202640024 #DfirSecurity
New room from @tryhackme File Inclusion, Path Traversal: Exploit File Inclusion and Path Traversal vulnerabilities. tryhackme.com/room/filepatht… #tryhackme #lfi #PathTraversal #File Inclusion

🗂️ Microsoft: “It’s only exploitable if attackers line up the stars.” Cool cool. Another Windows-style bug: real, but you must suffer the perfect workflow first. windowsforum.com/threads/vim-zi… #PathTraversal #ZipVim #VimSecurity #Cve2026

🛡️ Beware the hidden threat of path traversal attacks! Learn how attackers can bypass web app defenses to access sensitive files and directories. Stay vigilant and secure your digital fortress. #WebSecurity #PathTraversal #Cybersecurity 🛡️ ift.tt/4SAXCx5
🧯 Python’s “trust me bro” path rules just got traversed. CVE-2026-3479 proves docs aren’t defenses—and everyone downstream pays the security tax. windowsforum.com/threads/cve-20… #PathTraversal #PythonSecurity #Cve20263479 #CpythonPatch

Learn about path traversal attack techniques and how they can lead to Remote Code Execution (RCE). Understand the importance of filtering user input to prevent such security risks. #CyberSecurity #PathTraversal #RCE #SecurityAwareness ift.tt/miqcoWI
🚨 CVE-2026-27897: Vociferou... CORS wildcard + unauthenticated path traversal = instant RCE via malicious webpage writing shells anywhere on disk. #CSRF #PathTraversal #RCE. zerodaysignal.com/vulnerability/… #netsec #vulnerability #CVE #sysadmin #zeroday
zerodaysignal.com
CVE-2026-27897 - Security Alert
Vociferous provides cross-platform, offline speech-to-text with local AI refinement. Prior to 4.4.2, the vulnerability exists in src/api/system.py wit...
A critical path traversal flaw in Fortinet FortiWeb (≤8.0.1) is exploited via HTTP POST to create admin users without authentication. Update to 8.0.2, restrict access, and monitor logs. #FortinetExploit #PathTraversal #FortiWebVulnerability ift.tt/0tlLFaJ
🚨 CVE-2026-5627: Pat... LLM platforms with path traversal = API key goldmine; `path.join` + `normalizePath` bypass screams amateur hour security #PathTraversal #LLM #APIKeys. zerodaysignal.com/vulnerability/… #netsec #vulnerability #CVE #sysadmin #zeroday
zerodaysignal.com
CVE-2026-5627 - Security Alert
A path traversal vulnerability exists in mintplex-labs/anything-llm versions up to and including 1.9.1, within the `AgentFlows` component. The vulnera...
The CVE-2025-8088 WinRAR path traversal flaw exploits Alternate Data Streams to hide and execute malicious files from decoy archives, enabling persistent attacks since July 2025, including zero-day use by RomCom. #WinRARFlaw #PathTraversal #RomCom ift.tt/2gQn36K
CVE-2026-41211: vite-plus Path Traversal Escapes VP_HOME Cache thecybrdef.com/cve-2026-41211… #CVE202641211 #PathTraversal #CyberSecurity
🚨 @evomap/evolver alert Path traversal via --out → arbitrary file write ⚠️ Update to v1.69.3+ now. #CyberSecurity #PathTraversal #Vulert

A path traversal vulnerability (GHSA-r466-rxw4-3j9j) in `Evolver` allows arbitrary file writes via the `fetch` command's `--out` flag. Review input sanitization for `Evolver` commands. #PathTraversal #Evolver #InfoSec pulsepatch.io/posts/evolver-…
🚨 CVE-2026-40576: Im... Zero-auth path traversal + 0.0.0.0 bind = instant RCE playground for anyone who can reach your Excel server's network port. #PathTraversal #RCE #MCP. zerodaysignal.com/vulnerability/… #netsec #vulnerability #CVE #sysadmin #zeroday
zerodaysignal.com
CVE-2026-40576 - Security Alert
excel-mcp-server is a Model Context Protocol server for Excel file manipulation. A path traversal vulnerability exists in excel-mcp-server versions up...
A service invocation path traversal vulnerability (GHSA-85gx-3qv6-4463) in #Dapr could lead to ACL bypass. Review configurations and prepare for patches. #PathTraversal #SecurityAdvisory pulsepatch.io/posts/dapr-ser…
A critical path traversal vulnerability (GHSA-xjvp-7243-rg9h) in `Wish` allows arbitrary file read/write via SCP. Assess exposure. #ThreatIntel #PathTraversal #Cybersecurity pulsepatch.io/posts/ghsa-xjv…
A path traversal flaw impacts `excel-mcp-server`, identified as CVE-2026-40576. This can enable unauthorized file access. Review systems and apply patches as they become available. #PathTraversal #CVE #InfoSec pulsepatch.io/posts/cve-2026…
🪟 Path traversal in Sleuth Kit’s tsk_recover? Because even forensic tools can’t be trusted with “don’t write outside this folder.” Your disk image just became a write-prank. windowsforum.com/threads/cve-20… #PathTraversal #SleuthKit #Cve202640024 #DfirSecurity
A path traversal flaw (GHSA-j98m-w3xp-9f56) affects `excel-mcp-server`, potentially allowing unauthorized file access. Mitigate by validating inputs and restricting file permissions. #PathTraversal #InfoSec #Vulnerability pulsepatch.io/posts/ghsa-j98…
A critical path traversal vulnerability (CVE-2026-40157) in `PraisonAI` allows arbitrary file write via `recipe unpack`. Processing untrusted recipe files can lead to system compromise. Monitor for patches. #PraisonAI #infosec #pathtraversal pulsepatch.io/posts/cve-2026…
A Zip Slip path traversal flaw in `gramps-webapi` (CVE-2026-40258) could allow arbitrary file writes. Evaluate your `gramps-webapi` deployments for this #PathTraversal #grampswebapi #infosec vulnerability. pulsepatch.io/posts/cve-2026…
Critical 9.8 flaws in goshs v2.0.0-beta.2 allow unauthenticated attackers to write or delete any file on your system. Update to v2.0.0-beta.3 immediately! #goshs #PathTraversal #CyberSecurity #InfoSec #RCE #Golang #SecurityPatch securityonline.info/goshs-vulnerab…

A critical path traversal vulnerability (CVE-2026-39847) affects the `Emmett` internal assets handler. This flaw could lead to unauthorized information disclosure from internal systems. #PathTraversal #AppSec #CVE pulsepatch.io/posts/cve-2026…
🗂️ Microsoft: “It’s only exploitable if attackers line up the stars.” Cool cool. Another Windows-style bug: real, but you must suffer the perfect workflow first. windowsforum.com/threads/vim-zi… #PathTraversal #ZipVim #VimSecurity #Cve2026

PraisonAI FileTools has a path traversal flaw (CVE-2026-35615) allowing unauthorized file access. Review systems for exposure. #PraisonAI #PathTraversal #InfoSec pulsepatch.io/posts/cve-2026…
🚨 CVE-2026-5627: Pat... LLM platforms with path traversal = API key goldmine; `path.join` + `normalizePath` bypass screams amateur hour security #PathTraversal #LLM #APIKeys. zerodaysignal.com/vulnerability/… #netsec #vulnerability #CVE #sysadmin #zeroday
zerodaysignal.com
CVE-2026-5627 - Security Alert
A path traversal vulnerability exists in mintplex-labs/anything-llm versions up to and including 1.9.1, within the `AgentFlows` component. The vulnera...
A critical path traversal flaw (CVE-2026-35471) impacts `goshs`, potentially allowing unauthorized file access. Review usage contexts and strengthen input validation. #PathTraversal #infosec pulsepatch.io/posts/cve-2026…
A critical path traversal flaw (CVE-2026-35392) affects `goshs` PUT upload, enabling arbitrary file writes. This could lead to system compromise. Monitor for `goshs` security updates. #PathTraversal #InfoSec #CyberSecurity pulsepatch.io/posts/cve-2026…
A path traversal flaw in `goshs` POST multipart upload (CVE-2026-35393) could lead to arbitrary file writes. Validate upload paths and monitor `goshs` for patches. #infosec #pathtraversal #go pulsepatch.io/posts/cve-2026…
A path traversal flaw (CVE-2026-33236) impacting `NLTK` downloader components could lead to arbitrary file overwrite. Review `NLTK` usage with untrusted inputs. #NLTK #PathTraversal #InfoSec pulsepatch.io/posts/cve-2026…
Another day another bug 🔥 Here's an example for code I found in one of my targets, by searching for the following regex: /res.download\(.*\`$/ And this regex found a #PathTraversal vulnerability for me 🪲 #BugBounty #bugbountytips #codereview


Critical 9.8 flaws in goshs v2.0.0-beta.2 allow unauthenticated attackers to write or delete any file on your system. Update to v2.0.0-beta.3 immediately! #goshs #PathTraversal #CyberSecurity #InfoSec #RCE #Golang #SecurityPatch securityonline.info/goshs-vulnerab…

🗂️ Microsoft: “It’s only exploitable if attackers line up the stars.” Cool cool. Another Windows-style bug: real, but you must suffer the perfect workflow first. windowsforum.com/threads/vim-zi… #PathTraversal #ZipVim #VimSecurity #Cve2026

New room from @tryhackme File Inclusion, Path Traversal: Exploit File Inclusion and Path Traversal vulnerabilities. tryhackme.com/room/filepatht… #tryhackme #lfi #PathTraversal #File Inclusion

🧯 Python’s “trust me bro” path rules just got traversed. CVE-2026-3479 proves docs aren’t defenses—and everyone downstream pays the security tax. windowsforum.com/threads/cve-20… #PathTraversal #PythonSecurity #Cve20263479 #CpythonPatch

Bishop Fox researchers identified a #pathtraversal #vulnerability in #CRAN – the default packet manager for the R programming language. Update to version 4.0.3 to ensure you’re unaffected by this #security issue. hubs.la/H0Dyq-P0

CVE-2023-39141 - WebUI-Aria2 - Path traversal Root cause: github.com/ziahamza/webui… CVE: cve.mitre.org/cgi-bin/cvenam… #Security #PathTraversal


Una mala configuración en servidores #NGINX puede exponer archivos sensibles a través de la vulnerabilidad #PathTraversal. Descubre cómo proteger tu infraestructura y mantener segura la información en nuestro último artículo de #SecurityArtWork: hubs.la/Q02PhMjS0

🚨 Fortinet warns of a critical vulnerability (CVE-2023-34990) in FortiWLM, allowing remote attackers to exploit sensitive info through path traversal. High risk of unauthorized access! 🔒 #FortiWLMFlaw #PathTraversal #FortinetAdvisory #CybersecurityNews… ift.tt/9uDflka

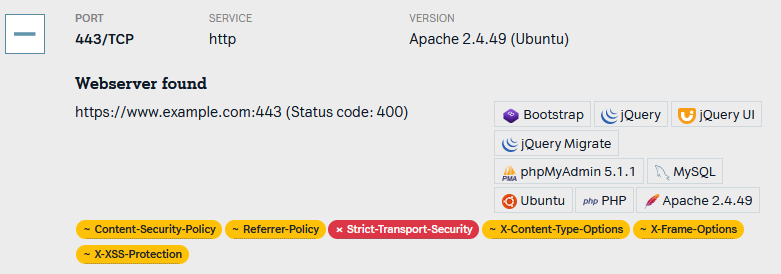
Apache #PathTraversal (CVE-2021-41773) was checked for all of our customers. Offensity users can also check their Apache versions manually at reporting.offensity.com/reports/infras…
Critical vulnerability CVE-2024-13059 in AnythingLLM (<1.3.1) allows remote code execution via path traversal. Update to v1.3.1 to secure systems. ⚠️ #AnythingLLM #PathTraversal #USA link: ift.tt/TmiLw68

🚨 @evomap/evolver alert Path traversal via --out → arbitrary file write ⚠️ Update to v1.69.3+ now. #CyberSecurity #PathTraversal #Vulert

[CVE-2025-26534: HIGH] Vulnerability in Helloprint allows Path Traversal due to improper pathname limitation. Versions affected: n/a to 2.0.7. #CyberSecurity #PathTraversal #Helloprint#cybersecurity,#vulnerability cvefind.com/CVE-2025-26534
![CveFindCom's tweet image. [CVE-2025-26534: HIGH] Vulnerability in Helloprint allows Path Traversal due to improper pathname limitation. Versions affected: n/a to 2.0.7. #CyberSecurity #PathTraversal #Helloprint#cybersecurity,#vulnerability cvefind.com/CVE-2025-26534](https://pbs.twimg.com/media/GlHxGv7XEAAH_xZ.jpg)
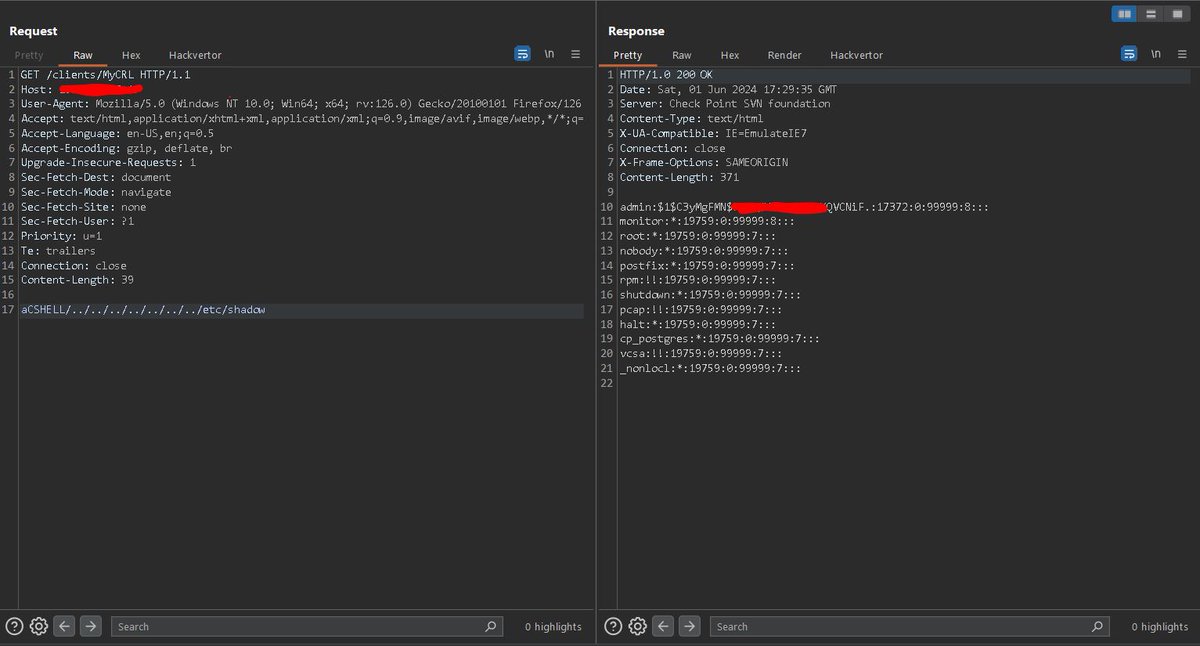
Nuevo video sobre la #vulnerabilidad de #PathTraversal y su impacto en la seguridad web utilizando los labs de #PortSwigger youtu.be/NmNDpLx4Yvk?si…

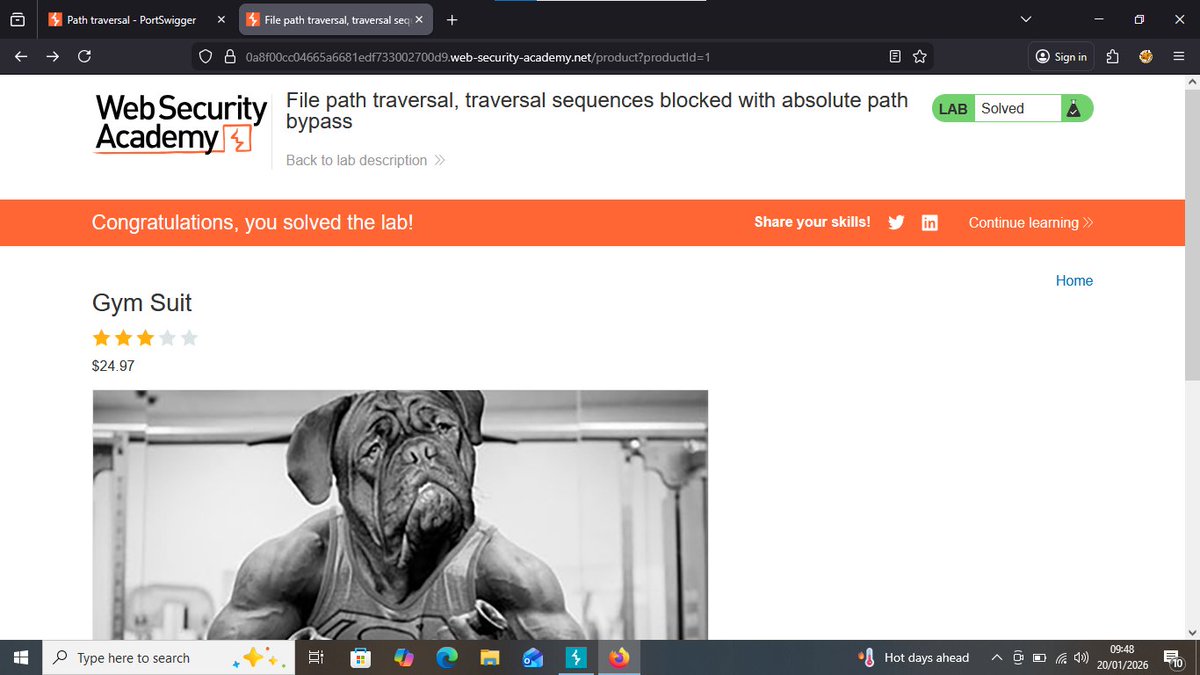
Day 19 ⚜️ PC let me hit today. 🔥 Solved 5 labs and completed the path traversal path on portswigger. They weren't that hard to understand to be honest #100DaysOfCybersecurity #portswigger #pathtraversal


Day 18 ⚜️ Couldn't work today. PC has been acting up for some reason I don't yet know 💔 I only studied some concepts on isc's domain 2. Access Control concepts. Also saved my streak on thm 😂. No premium for now #100DaysOfCybersecurity #tryhackme #sendhelp

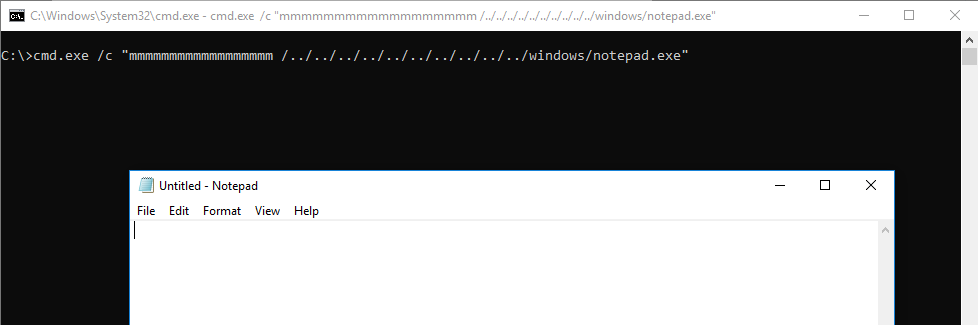
cmd hijack that resulted in the discovery of a very interesting (and potentially dangerous🤭) behavior: cmd.exe /c "ipconfig /all/../../../../../../../../../../windows/notepad.exe" #cmd #windows #pathtraversal #vulnerability #security #vulnerabilityresearch
🚨 Why it matters: Path Traversal attacks expose sensitive server files by exploiting directory paths 🛡️ Action: Enable WAF traversal rules to detect and block suspicious “../” patterns before access occurs quttera.com/web-applicatio… #PathTraversal #CyberSecurity #Hacking

Path Traversal Attack ⚠️Why it matters: Hackers exploit directory paths to access private files. Action: Sanitize input and use WAF to block unauthorized file access. quttera.com #PathTraversal #CyberSecurity #WebAppSecurity

False assumptions = vulnerabilities. Don't assume this #NodeJS code is enough to prevent #PathTraversal attacks. Don't overlook the power of URL encoding! Ensure proper decoding & sanitization of filenames for robust #CyberSecurity. Stay ahead of the game. #WebSecurity 💡

Something went wrong.
Something went wrong.
United States Trends
- 1. #WWERaw N/A
- 2. Kimmel N/A
- 3. World War Eleven N/A
- 4. Cooper Flagg N/A
- 5. #AmericanIdol N/A
- 6. ROTY N/A
- 7. Dennis Santana N/A
- 8. Luis Castillo N/A
- 9. Vladar N/A
- 10. Mantha N/A
- 11. #Jeopardy N/A
- 12. Dylan Cease N/A
- 13. Alex Bump N/A
- 14. Bron Breakker N/A
- 15. Lindsey N/A
- 16. Learing Center N/A
- 17. Kon Knueppel N/A
- 18. Lee Zeldin N/A
- 19. JJ Wetherholt N/A
- 20. Rookie of the Year N/A