#securityframework ผลการค้นหา
The 12 Pillars of Cyber Security! 🛡️ Know your defense: from Encryption to API Security. Are you covering all 12? #CyberSecurity #InfoSec #SecurityFramework #digitalearn #DevOps

#IEMLabs #securityframework #cybersecurity #cybersecurityawareness #cybersecuritytraining #cybersecuritytips #systemsecurity

The U.S. Cybersecurity & Infrastructure Security Agency (CISA) has released 'Decider,' an open-source tool that helps defenders and security analysts quickly generate MITRE ATT&CK mapping reports 👩💻🛡️ #securityframework #securitybaseline buff.ly/3mybej2

The advantage of aligning your or your customer’s #cybersecurity roadmap to a #securityframework is defining a route to follow using established security best practices. bit.ly/3Ke7gWy #cybersecurityroadmap
Proposing a configurable and comprehensive hardware-software #securityframework: “IoTrust - a HW/SW framework supporting security core baseline features for #IoT“ by M. Korona, B. Zabołotny, F. Kozioł, et al. ACSIS Vol. 35 p. 1029–1034; tinyurl.com/j8w56rkb

Join our February 16th #Webinar with #CISO Karl Mattson and learn how to balance security and business priorities, implement robust #SecurityFramework, adopting a business-centric approach. Register now: bit.ly/3vXtqr3 #ECCouncil #Cybersecurity #RiskManagement

Static defenses died when AI entered the chat 🤖 Your AI needs: ✓ Adversarial training ✓ Continuous threat intel ✓ Automated response Because attackers are using AI too. #AI #SecurityFramework #DevSecOps #Resilience

Most frameworks look solid on paper — until attackers use new tactics that bypass them entirely. At HITRUST, we’ve built a framework that learns from the front lines. Learn about the top 5 current threats. hubs.ly/Q03jY3l10 #ThreatIntelligence #SecurityFramework

Embrace the power of Node.js permission model for robust security! Safeguard resources, fortify apps, and navigate modern development confidently with Pedals Up. 🔒 🌐 pedalsup.com 📧 [email protected] #NodeJS #SecurityFramework #CyberSecurity
Applying the Zero Trust Security Principles to SSH Access. One of the major issues of using SSH to share data and information is using the SSH keys. Know more: zurl.co/41CS #ZeroTrust #ZeroTrustSecurity #SecurityFramework #Cybersecurity #NetworkSecurity
Last 48 hours left for our February 16th #Webinar. Join Karl Mattson and learn to build an effective #SecurityFramework, its requirements, and how to maintain a versatile #CybersecurityStrategy to sustain #CyberLeadership. Register now: bit.ly/3vXtqr3 #ECCouncil

Unlock the Power of Data Sharing! The benefits are vast, but so are the risks. Sensitive data needs protection. Learn how Securiti simplifies secure data sharing—maximizing value without compromising security. 🔒 bit.ly/494DnkQ #DataSharing #SecurityFramework

Once you have aligned to a #securityframework, it's time to hit the road and put your cybersecurity roadmap into action. Find out how to get started. bit.ly/3Ud4Bj5 #cyberhygiene #cybersecurityroadmap

Join our February 16th #Webinar with Karl Mattson and explore balancing security and business priorities. Learn the importance of the shift to a business-centric approach, creating a #SecurityFramework. Register now:bit.ly/3vXtqr3 #Cybersecurity #CyberThreat #ECCouncil

With a CIS SecureSuite Membership, your organization will be able to effectively track your implementation of the CIS Controls with our self-assessment tool. bit.ly/40dofNH #cybersecurityroadmap #securityframework

With Readiness 2030, ProtectEU, and ReArm Europe, the EU is building a more autonomous #SecurityFramework. What does this mean for U.S. #tech and defense firms? Read our latest blog: centerforcybersecuritypolicy.org/insights-and-r…

💼 Seamlessly exchange data with external systems using CMDM. By leveraging existing authorization and security rules, organizations establish a unified security framework. Stay ahead in the game of data security with Pretectum CMDM! #SecurityFramework pretectum.com/customer-data-…

#ZeroTrust is an increasingly popular #securityframework requiring all users to be authenticated, authorized, and continuously validated when it comes to #accessmanagement. Join us in June as we discuss the security and business benefits of the framework. hubs.la/Q01Rts5B0

Join our March 26th #Webinar, where cyber expert Sentil Velaytham shares insights on the effectiveness of proactive detection and response, creating a cyber-resilient #SecurityFramework. Register now: bit.ly/3wB676M #CTIA #ECCouncil

8️⃣ THE 4D STRATEGY FOR INTERNAL SECURITY (UPSC-READY) Deter → Detect → Develop → Deliver. Each district’s transformation = synergy of security, social policy, and sustainable livelihoods. #GS3 #SecurityFramework
The 12 Pillars of Cyber Security! 🛡️ Know your defense: from Encryption to API Security. Are you covering all 12? #CyberSecurity #InfoSec #SecurityFramework #digitalearn #DevOps

From internal threats to external risks, our new catalog has you covered. It's an indispensable resource for creating a robust security framework. Discover it on Etsy! #InternalThreats #ExternalRisks #SecurityFramework #CyberSecurity #GRC atelyedr.etsy.com/listing/433708…
From vulnerability management to policy enforcement, our GRC framework covers it all. Stop guessing and start strategizing with a proven system. Discover our product on Etsy. #VulnerabilityManagement #CyberPolicy #SecurityFramework #GRC #CyberSecurity atelyedr.etsy.com/listing/436630…
Static defenses died when AI entered the chat 🤖 Your AI needs: ✓ Adversarial training ✓ Continuous threat intel ✓ Automated response Because attackers are using AI too. #AI #SecurityFramework #DevSecOps #Resilience

Static frameworks quickly become obsolete. HITRUST is different as it adapts with emerging threats. Explore the top 5 attack techniques and how HITRUST helps organizations stay one step ahead. hubs.ly/Q03CX2zG0 #ThreatIntelligence #ThreatManagement #SecurityFramework

Improving existing security protocols can help prevent AI security breaches and maintain trust in AI ecosystems #securityframework
Regular audits and security assessments can help identify and mitigate potential threats #securityframework
Enhancing AI agent security requires a detailed plan, leveraging expertise in blockchain forensics and AI security to protect AI ecosystems ~ #securityframework
The 12 Pillars of Cyber Security! 🛡️ Know your defense: from Encryption to API Security. Are you covering all 12? #CyberSecurity #InfoSec #SecurityFramework #digitalearn #DevOps

🟢Join us live today at 4 PM IST for our next webinar by Sid @sidnext2none @BellLabs find out about Bhadra framework & get a chance to contribute to this framework Register now➡️bit.ly/3DqGRzb #Nullcon #telcomsecurity #securityframework #infosec #cybersecurity #5G

The U.S. Cybersecurity & Infrastructure Security Agency (CISA) has released 'Decider,' an open-source tool that helps defenders and security analysts quickly generate MITRE ATT&CK mapping reports 👩💻🛡️ #securityframework #securitybaseline buff.ly/3mybej2

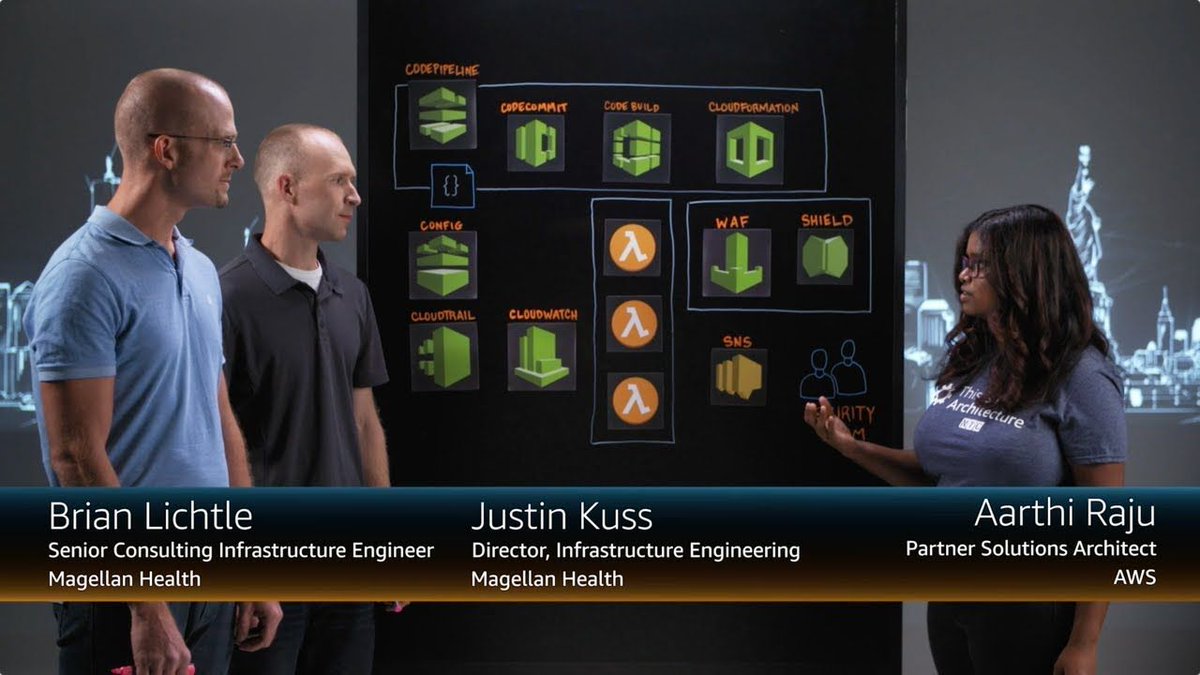
Check it out. See how Magellan Health is using #AWS to build a new centralized #securityframework: buff.ly/2JmQPGh
Join our February 16th #Webinar with #CISO Karl Mattson and learn how to balance security and business priorities, implement robust #SecurityFramework, adopting a business-centric approach. Register now: bit.ly/3vXtqr3 #ECCouncil #Cybersecurity #RiskManagement

Last 48 hours left for our February 16th #Webinar. Join Karl Mattson and learn to build an effective #SecurityFramework, its requirements, and how to maintain a versatile #CybersecurityStrategy to sustain #CyberLeadership. Register now: bit.ly/3vXtqr3 #ECCouncil

Join our February 16th #Webinar with Karl Mattson and explore balancing security and business priorities. Learn the importance of the shift to a business-centric approach, creating a #SecurityFramework. Register now:bit.ly/3vXtqr3 #Cybersecurity #CyberThreat #ECCouncil

Proposing a configurable and comprehensive hardware-software #securityframework: “IoTrust - a HW/SW framework supporting security core baseline features for #IoT“ by M. Korona, B. Zabołotny, F. Kozioł, et al. ACSIS Vol. 35 p. 1029–1034; tinyurl.com/j8w56rkb

We’re delighted to have been selected as a supplier for YPO’s Data Centres, Maintenance Cloud Hosting and Security Framework @ypoinfo #CloudHosting #DateCentre #SecurityFramework

Join our March 26th #Webinar, where cyber expert Sentil Velaytham shares insights on the effectiveness of proactive detection and response, creating a cyber-resilient #SecurityFramework. Register now: bit.ly/3wB676M #CTIA #ECCouncil

Once you have aligned to a #securityframework, it's time to hit the road and put your cybersecurity roadmap into action. Find out how to get started. bit.ly/3Ud4Bj5 #cyberhygiene #cybersecurityroadmap

Static defenses died when AI entered the chat 🤖 Your AI needs: ✓ Adversarial training ✓ Continuous threat intel ✓ Automated response Because attackers are using AI too. #AI #SecurityFramework #DevSecOps #Resilience

Applying the Zero Trust Security Principles to SSH Access. One of the major issues of using SSH to share data and information is using the SSH keys. Know more: zurl.co/41CS #ZeroTrust #ZeroTrustSecurity #SecurityFramework #Cybersecurity #NetworkSecurity
Static frameworks quickly become obsolete. HITRUST is different as it adapts with emerging threats. Explore the top 5 attack techniques and how HITRUST helps organizations stay one step ahead. hubs.ly/Q03CX2zG0 #ThreatIntelligence #ThreatManagement #SecurityFramework

Most frameworks look solid on paper — until attackers use new tactics that bypass them entirely. At HITRUST, we’ve built a framework that learns from the front lines. Learn about the top 5 current threats. hubs.ly/Q03jY3l10 #ThreatIntelligence #SecurityFramework

With so many potential threats, it’s vital to understand what #cybersecurity is, the available solutions, and how to create a robust #SecurityFramework to mitigate risks and keep protected. @NETSCOUT bit.ly/3C6sW0U
Methods to Upgrade your M365 Security Framework - Threat Protection - Identity and Access Management - Information Protection - Security Management Read more about it:lnkd.in/daHrB8Z #M365 #securityframework #microsoft365 #bitscape

With a CIS SecureSuite Membership, your organization will be able to effectively track your implementation of the CIS Controls with our self-assessment tool. bit.ly/40dofNH #cybersecurityroadmap #securityframework

Unlock the Power of Data Sharing! The benefits are vast, but so are the risks. Sensitive data needs protection. Learn how Securiti simplifies secure data sharing—maximizing value without compromising security. 🔒 bit.ly/494DnkQ #DataSharing #SecurityFramework

Something went wrong.
Something went wrong.
United States Trends
- 1. GTA 6 51.2K posts
- 2. GTA VI 18.1K posts
- 3. Rockstar 47.4K posts
- 4. GTA 5 1,792 posts
- 5. Antonio Brown 4,519 posts
- 6. Nancy Pelosi 120K posts
- 7. #LOUDERTHANEVER 1,503 posts
- 8. Rockies 3,870 posts
- 9. Ozempic 16.8K posts
- 10. Paul DePodesta 1,930 posts
- 11. Justin Dean 1,307 posts
- 12. GTA 7 1,126 posts
- 13. Grand Theft Auto VI 39.9K posts
- 14. Luke Fickell N/A
- 15. Elon Musk 221K posts
- 16. Grisham 1,739 posts
- 17. $TSLA 54.4K posts
- 18. RFK Jr 28.4K posts
- 19. Oval Office 41.5K posts
- 20. Pete Fairbanks N/A