#supplychainsecurity search results
iT4iNT SERVER Poisoned Ruby Gems and Go Modules Exploit CI Pipelines for Credential Theft dlvr.it/TSK60M VDS VPS Cloud #CyberSecurity #SupplyChainSecurity #CredentialTheft #GitHubActions #Malware
Sleeper packages beat SBOM diffs by design. Same publisher, version range you already pinned, clean when you scanned. Then the postinstall shells out to a host nobody allowlisted. Inventory tells you what's installed. Not what it does. #SupplyChainSecurity #DevSecOps
Most apps are built like a puzzle using parts from many different companies. How much do you trust that every hidden part is safe? #Security #Apps #SupplyChainSecurity #CyberSecurity
Supply chain attacks up 742% since 2019. Your pipeline is the target 🎯 Pre-commit secrets. Dependency scanning. Container signing. SLSA compliance. Stop building vulnerabilities Read more by clicking below blog.easecloud.io/cloud-security… #CICD #SupplyChainSecurity #DevSecOps #InfoSec
Four supply chain incidents this week, four ecosystems. Every one rode a hijacked maintainer account or a delayed payload to walk past install-time scanners. We keep auditing the package and ignoring the runtime it eventually executes in. #DevSecOps #SupplyChainSecurity
Security isn't just a checklist; it's a commitment. Joining TAPA and understanding the certification process is key to safeguarding your operations and building trust. Prioritize robust security measures. #SupplyChainSecurity #TAPA
Package managers are trojan horses. npm, PyPI, Docker Hub -- all active attack vectors, cross-platform and cross-language. Hash pinning + lock files aren't optional. They're the minimum. Your dependency tree is an attack surface. Treat it like one. #SupplyChainSecurity #AppSec
Most supply chain payloads now run inside npm or pip install and finish in 15-30 seconds. Cred theft, self-delete, done. By the time the package is yanked, it already ran across every CI runner that pulled it. Catching it means watching install. #SupplyChainSecurity #DevSecOps
Mercor wasn't breached through its own code. It was breached through a dependency it trusted: LiteLLM. In 2026, your attack surface isn't your repo. It's the repo of whoever you import. AI governance starts at the SBOM. #SupplyChainSecurity #AISecurity #GRC #ThirdPartyRisk #CISO
When Trusted Code Turns Malicious: Inside the Mini Shai-Hulud Supply Chain Attack What if a package you trust is already working against you? What if installing code is enough to leak your secrets? #CyberSecurity #SupplyChainSecurity Full Story 👉 cybersecurity88.com/news/mini-shai…

Trivy got hacked. The scanner you run in CI became the attack vector. CI secrets exfiltrated. Backdoors planted. npm worm released. 3 quick fixes: → Pin scanner versions → Isolate scanners from secrets → Audit what your tooling has access to #DevSecOps #SupplyChainSecurity
SILVER47 Joins DARPA-Backed Critical Minerals Forum ⚡ The company is now part of a US Department of Defense initiative aiming to secure critical minerals and counter foreign manipulation in the supply chain. #CriticalMinerals #DARPA #SupplyChainSecurity #DefenseTech
Critical Supply Chain Pandemic? Not a Bug. #criticalmaterials, #supplychainsecurity, #semiconductors, #fertilizers, #foodsecurity, #AI
In 2022, Ukraine's neon supply collapsed. The semiconductor industry panicked, then adapted. It accelerated the migration from deep ultraviolet to extreme ultraviolet lithography. EUV machines do not need neon. Problem solved. The industry congratulated itself for learning the

🔒 Chainguard amplía su repositorio con bibliotecas de código abierto más seguras Accede a componentes Java, JavaScript y Python seguros y compatibles con SLSA. devops.com/chainguard-exp… #SupplyChainSecurity #SLSA #OpenSource #RoxsRoss
🚨 Incus forgot the combined fingerprint check, so an image cache can be “poisoned” in multi-tenant setups. Medium severity ≠ harmless—this is supply-chain trust drift. windowsforum.com/threads/cve-20… #SupplyChainSecurity #ContainerSecurity #IncusVulnerability #ImageCachePoisoning

When Open-Source Turns Against You: Inside the CI/CD Supply Chain Attack One malicious package and your entire pipeline is compromised. #CyberSecurity #SupplyChainSecurity Full Story 👉 cybersecurity88.com/news/poisoned-…

Supply chain attack via third-party AI tool Context.ai exposed @vercel systems, with hackers claiming to sell stolen data for $2M. #AI #AIAgents #SupplyChainSecurity #CloudSecurity #DevSecOps #CryptoSecurity #Infosec Read more here ⤵️ blockhead.co/2026/04/20/ver…
LiteLLM just became a credential-stealing vector. 🔓 119K installs in 40 minutes - that’s how fast things break. Your AI gateway can expose everything behind it. 🚨 Audit deps. Lock versions. Trust nothing. kagex.ai #AISecurity #SupplyChainSecurity #CyberThreats

The FCC just banned foreign-made routers! 🛡️ Is your network safe? This move shines a light on the importance of knowing what's connected. ➡️ dataconomy.com/2026/04/23/fcc… #FCCBan #SupplyChainSecurity
AI-generated code means AI-generated supply chain risk. 🛡️ A Build Artifact CDN like Develocity doesn't just speed things up—it gives you provenance on everything that shipped. See how >> gradl.es/4uUnsBx #Develocity #DevSecOps #SupplyChainSecurity
Four supply chain incidents this week, four ecosystems. Every one rode a hijacked maintainer account or a delayed payload to walk past install-time scanners. We keep auditing the package and ignoring the runtime it eventually executes in. #DevSecOps #SupplyChainSecurity
LiteLLM just became a credential-stealing vector. 🔓 119K installs in 40 minutes - that’s how fast things break. Your AI gateway can expose everything behind it. 🚨 Audit deps. Lock versions. Trust nothing. kagex.ai #AISecurity #SupplyChainSecurity #CyberThreats

Sleeper packages beat SBOM diffs by design. Same publisher, version range you already pinned, clean when you scanned. Then the postinstall shells out to a host nobody allowlisted. Inventory tells you what's installed. Not what it does. #SupplyChainSecurity #DevSecOps
Postinstall hooks are still the cleanest exfil channel in npm. They run with whatever creds the CI runner has, before any test or scanner kicks in. If your supply chain story doesn't cover what install scripts actually do, you don't have one. #DevSecOps #SupplyChainSecurity
Package managers are trojan horses. npm, PyPI, Docker Hub -- all active attack vectors, cross-platform and cross-language. Hash pinning + lock files aren't optional. They're the minimum. Your dependency tree is an attack surface. Treat it like one. #SupplyChainSecurity #AppSec
Mercor wasn't breached through its own code. It was breached through a dependency it trusted: LiteLLM. In 2026, your attack surface isn't your repo. It's the repo of whoever you import. AI governance starts at the SBOM. #SupplyChainSecurity #AISecurity #GRC #ThirdPartyRisk #CISO
When Trusted Code Turns Malicious: Inside the Mini Shai-Hulud Supply Chain Attack What if a package you trust is already working against you? What if installing code is enough to leak your secrets? #CyberSecurity #SupplyChainSecurity Full Story 👉 cybersecurity88.com/news/mini-shai…

When Open-Source Turns Against You: Inside the CI/CD Supply Chain Attack One malicious package and your entire pipeline is compromised. #CyberSecurity #SupplyChainSecurity Full Story 👉 cybersecurity88.com/news/poisoned-…

iT4iNT SERVER Poisoned Ruby Gems and Go Modules Exploit CI Pipelines for Credential Theft dlvr.it/TSK60M VDS VPS Cloud #CyberSecurity #SupplyChainSecurity #CredentialTheft #GitHubActions #Malware
How many of this week's dependency updates did you actually verify? 👀 Most teams merge → ship. One malicious package and you're explaining to your CEO. #CodeSecurity #DevSecOps #SupplyChainSecurity




Most apps are built like a puzzle using parts from many different companies. How much do you trust that every hidden part is safe? #Security #Apps #SupplyChainSecurity #CyberSecurity
Most supply chain payloads now run inside npm or pip install and finish in 15-30 seconds. Cred theft, self-delete, done. By the time the package is yanked, it already ran across every CI runner that pulled it. Catching it means watching install. #SupplyChainSecurity #DevSecOps
Supply chain attacks up 742% since 2019. Your pipeline is the target 🎯 Pre-commit secrets. Dependency scanning. Container signing. SLSA compliance. Stop building vulnerabilities Read more by clicking below blog.easecloud.io/cloud-security… #CICD #SupplyChainSecurity #DevSecOps #InfoSec
Pinning to a Git tag isn't pinning, it's resolving. Tags are mutable pointers - a compromised token can move them post-review, and your next CI build picks up whatever's there. Hash-pin or accept the silent rollover. #SupplyChainSecurity #DevSecOps
Security isn't just a checklist; it's a commitment. Joining TAPA and understanding the certification process is key to safeguarding your operations and building trust. Prioritize robust security measures. #SupplyChainSecurity #TAPA
Pre-install hooks are the new RCE primitive and we keep treating them as a packaging detail. In every ecosystem, install means execute on the most privileged box in your org. Stop only scanning what got installed. Watch what the install just did. #DevSecOps #SupplyChainSecurity
🚨 Incus forgot the combined fingerprint check, so an image cache can be “poisoned” in multi-tenant setups. Medium severity ≠ harmless—this is supply-chain trust drift. windowsforum.com/threads/cve-20… #SupplyChainSecurity #ContainerSecurity #IncusVulnerability #ImageCachePoisoning

Trivy got hacked. The scanner you run in CI became the attack vector. CI secrets exfiltrated. Backdoors planted. npm worm released. 3 quick fixes: → Pin scanner versions → Isolate scanners from secrets → Audit what your tooling has access to #DevSecOps #SupplyChainSecurity
Three things that were "trusted" this week: → A PyPI package with 1M monthly downloads → A patched federal Cisco firewall → A Checkmarx GitHub Action feeding npm All three were compromised. Our weekly roundup: openv.pn/4cTyH4N #SupplyChainSecurity #InfoSec

A clean SBOM and a valid signature don't catch what we keep seeing: install hooks that exfil creds in seconds, then erase themselves. The malicious work happens at runtime on your build host. Static inventory doesn't see it. #SupplyChainSecurity #DevSecOps
Master Supply Chain Cybersecurity with these Q&As. Much more detail here: supplychaintoday.com/supply-chain-c… #SupplyChain #Cybersecurity #SupplyChainSecurity #CyberAwareness

Your software supply chain could hide vulnerabilities attackers hope you’ll miss. ⚠️ Attacks slip into updates, SaaS, and open-source deps. Learn Zero Trust, PoLP & vendor risk defenses: bit.ly/3MnrgJH #SupplyChainSecurity

Vimeo metadata and customer emails were exposed via a breach at third-party vendor Anodot. Internal systems remain secure. Learn how to manage vendor risk. #VimeoBreach #SupplyChainSecurity #InfoSec #ThirdPartyRisk #CyberSecurity #DataPrivacy securityonline.info/vimeo-anodot-d…

US, Philippines To Set Up Joint Economic Security Zone To Strengthen Supply Chains dlvr.it/TS4y12 #USEconomy #Philippines #SupplyChainSecurity #EconomicZone #IndustrialHub

Our research on npm, PyPI, and Docker Hub supply chain attacks was picked up by Slashdot. The same weak points keep showing up across ecosystems — trust, provenance, and detection lag. #SupplyChainSecurity #OpenSource #npm bit.ly/4n10Tps

🚀 Part 2 is live! Dive into the evolution of SBOMs from Release to Production in our final installment. Enhance your software security today. Read here 👉 anchore.com/blog/the-evolu… #SBOM #DevSecOps #SupplyChainSecurity

Shai-Hulud 2.0 supply chain attack compromises 700+ npm pkgs from Zapier, Postman & more exfiltrating secrets from 25K+ repos! We've added a Nuclei template to detect it in your codebase. Secure your chain: github.com/projectdiscove… #Nuclei #supplychainsecurity

#ETAutoUnplugged Commercial Vehicles at crossroads: Technology, efficiency & growth Watch at: shorturl.at/xNM0l 🎙️@ArunMalhotra_07 #supplychainsecurity #SustainableOperations #CommercialMobilityLandscape #ETAuto

Phantom carriers are surging worldwide. Truckloads vanish through digital deception, not violence — fake docs, shell firms, stolen credentials. IUMI + TAPA EMEA urge urgent action + stronger vetting Read more: ajot.com/news/iumi-and-… #SupplyChainSecurity #CargoCrime #Trucking

Anchore and Chainguard have partnered to improve #supplychainsecurity. Our collaboration integrates Chainguard's minimal, zero-CVE container images with Anchore's policy and scanning framework to help you "start safe, stay secure, and compliant". This m... anchore.com/press/chaingua…

Stop choosing between speed and security! 🛡️ Join our webinar with @Chainguard to learn how to Accelerate & Secure: Optimizing Your Software Supply Chain with DevSecOps. Get the roadmap to a res... webinars.techstronglearning.com/accelerate-sec… #DevSecOps #SupplyChainSecurity #Cybersecurity #Chainguard

Anthropic backs Python Software Foundation security work with $1.5 million - helpnetsecurity.com/2026/01/14/ant… - @AnthropicAI @ThePSF - #OpenSource #Python #SupplyChainSecurity #Cybersecurity #CyberSecurityNews #SecurityNews

95% of orgs use AI for development - but only 24% fully assess IP, license, security & quality risks in AI-generated code. New research shows SBOM validation directly improves response speed. #SupplyChainSecurity #AI #AppSec

Cybersecurity failures now start in the software supply chain. Tom Hollingsworth, Mitch Ashley, and Steve Puluka discuss why secure code distribution must be an architectural priority. #Cybersecurity #SupplyChainSecurity #DevSecOps #AIinNetworking

Latest survey of professionals in bio/#Pharmaceutical industry garnered ~90 completions that reveal the profound impact on operations and supply chains! Dive into the full survey results here: pharmtech.com/view/biopharma… #supplychainsecurity #BioPharma #Tariffs #SupplyChain #Biotech

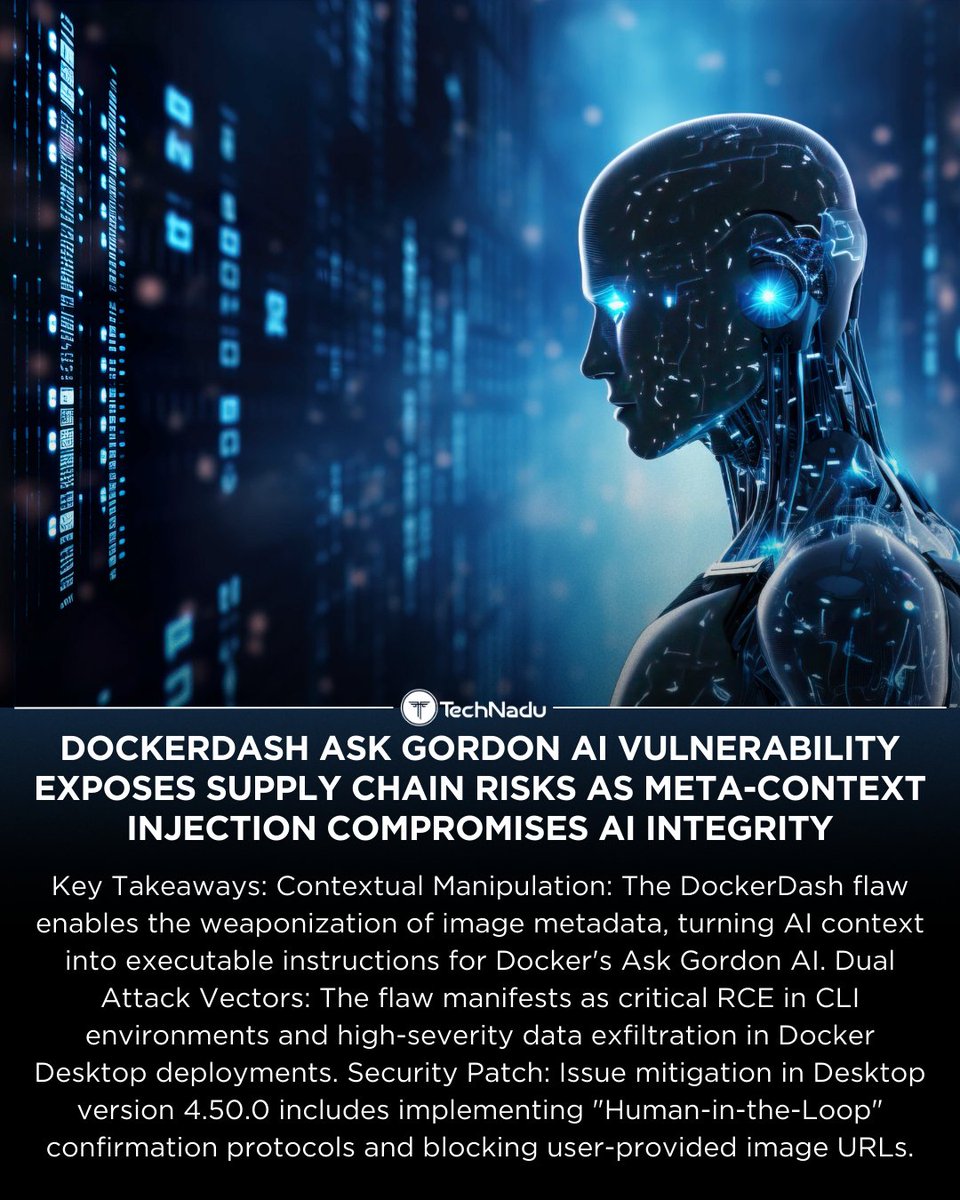
Docker’s Ask Gordon AI flaw shows how image metadata can become executable instructions. Meta-context injection → RCE & data exfiltration risks. Link in pinned comment 👇 #AIsecurity #Docker #SupplyChainSecurity #PromptInjection #CyberRisk
Zero‑trust isn’t just for your company, apply it to your suppliers too. @AssureTechnical shares why it matters 👉assuretechnical.com/supply-chain-r… #CyberRisk #SupplyChainSecurity #UKBusiness #Ransomware #ALFED

Counterfeit defenses built on paper have blind spots - helpnetsecurity.com/2025/12/24/cou… - @IEEEorg #Cybersecurity #SupplyChainSecurity #AntiCounterfeiting #Infosec #HardwareSecurity

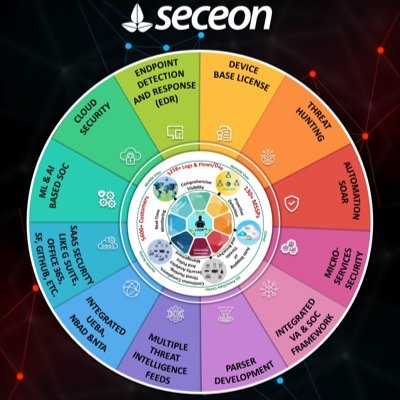
🚨 Developers Under Attack: North Korean hackers are distributing malicious npm packages, turning trusted tools into attack vectors that can steal credentials and compromise systems. 🔎 Read more: seceon.com/north-korean-h… #ThreatIntelligence #SupplyChainSecurity @Seceon_Inc

New research reveals critical gaps in supply chain security frameworks. Ten major frameworks leave organizations vulnerable to SolarWinds-style attacks. jpmellojr.blogspot.com/2025/12/securi… #SolarWinds #SupplyChainSecurity #SecurityFrameworks

Something went wrong.
Something went wrong.
United States Trends
- 1. Celtics N/A
- 2. Embiid N/A
- 3. Embiid N/A
- 4. Sixers N/A
- 5. Tatum N/A
- 6. Jaylen Brown N/A
- 7. Philly N/A
- 8. #saturdaynightliv N/A
- 9. Golden Tempo N/A
- 10. Emerson Hancock N/A
- 11. Paul George N/A
- 12. Derrick White N/A
- 13. Mazzulla N/A
- 14. Knicks in 6 N/A
- 15. #AEWCollision N/A
- 16. Duarte N/A
- 17. Shuri N/A
- 18. Queta N/A
- 19. #OPLive N/A
- 20. Live by the 3 N/A