#authentication search results
Scenario Question 👨💻 You need to build a login system. What things will you consider for security? 👇 #WebSecurity #Authentication #DevCommunity
Doesn't matter if you work in tech, setting up a new phone will always take you to the #2FA/ #authentication hell. One login at a time. #patience #caseoftheMondays
Weaponized cPanelSniper PoC Supercharges Global Exploitation of CVE-2026-41940 thecybrdef.com/weaponized-cpa… #cPanel #Vulnerability #Authentication #Cyberattack #Cybersecurity
NewswireToday / NEC Receives Company of the Year recognition in Global Biometric Solutions from Frost & Sullivan #NEC_Corp #Frost_Sullivan #Authentication #DigitalTransformation #DX #BluStellar #ValueDriver #Innovation #Biometric #Forensic - newswiretoday.com/news/186083/
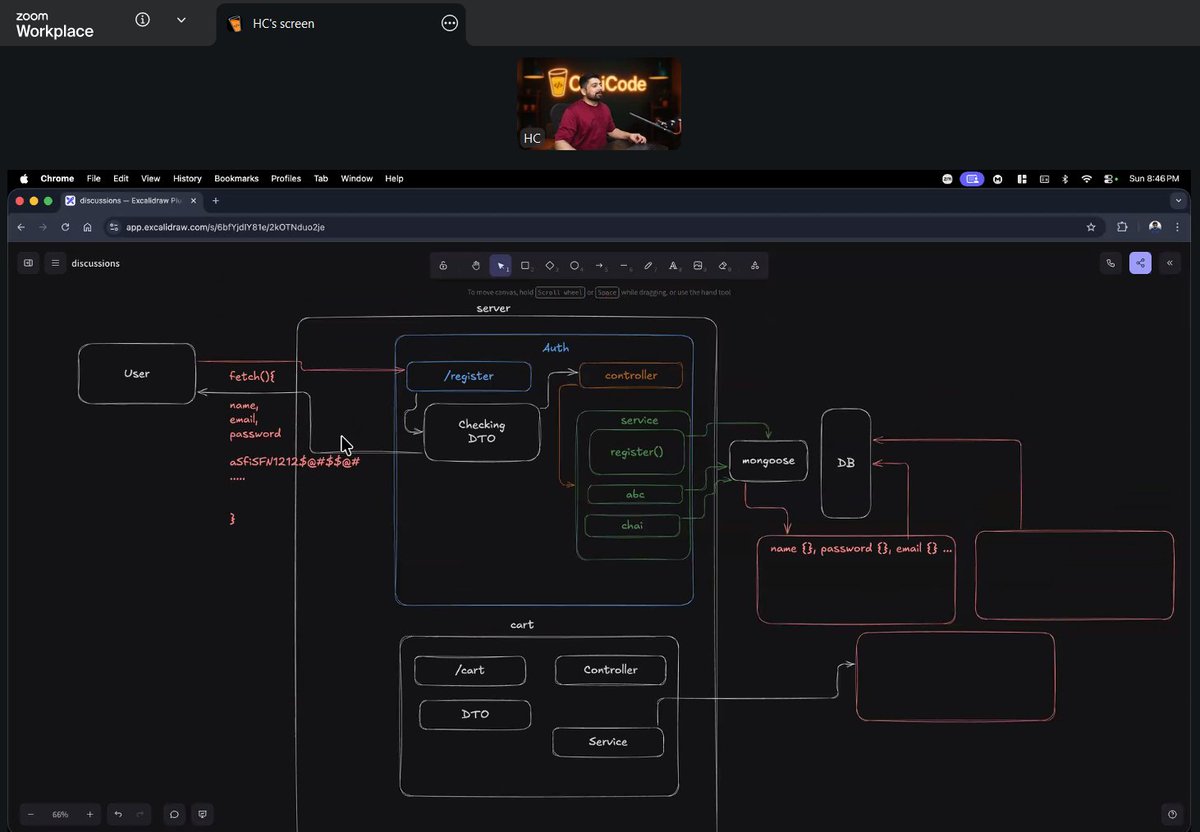
Completed an authentication assignment using freeapi.app 🚀 User register and login flow with API. Good hands-on practice of React. @Hiteshdotcom @ChaiCodeHQ #react #authentication #api #webdevelopment #chaicode #learninginpublic
It’s a reminder that adoption of #authentication methods doesn’t come from technology alone. It comes from making the user experience seamless and easy to understand which is how we’ve designed #IPification. howtogeek.com/i-tried-to-go-…
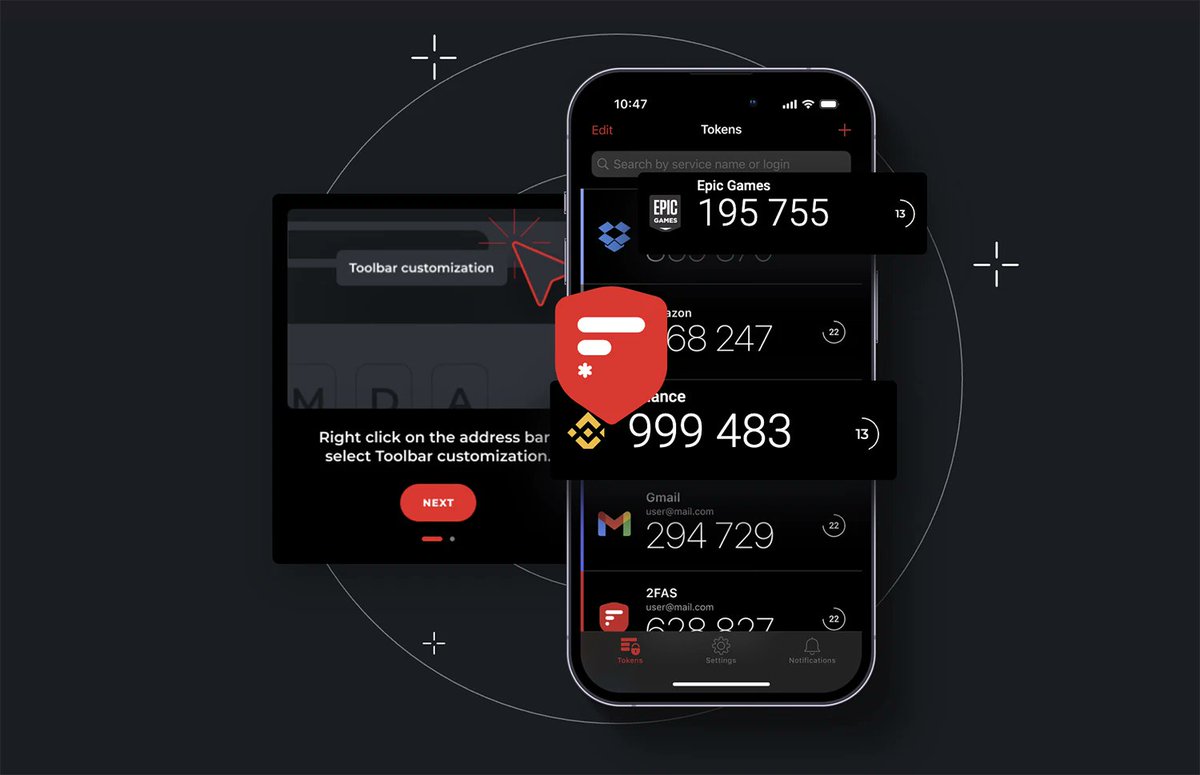
Protectimus vs RSA — which MFA solution to choose? 🔐 RSA — strong in passwordless and enterprise IAM 🔐 Protectimus — flexible OATH-based MFA (HOTP, TOTP, OCRA), cloud + on-prem, easy integration 👉 Full comparison: zurl.co/z4mm3 #MFA #CyberSecurity #Authentication
Weaponized cPanelSniper PoC Supercharges Global Exploitation of CVE-2026-41940 thecybrdef.com/weaponized-cpa… #cPanel #Vulnerability #Authentication #Cyberattack #Cybersecurity
Hot take 🔐 Two-factor authentication should be mandatory on every website admin panel no exceptions. Agree or disagree? And why? 👇 #EthicalHacking #CyberSecurity #Authentication #InfoSec #WebSecurity
Companies Have Started Moving Away from AI antonmb.com/en/blog/compan… #AI #Authentication #Cybersecurity #Infrastructure #AgenticAi
𝗦𝗦𝗢 & 𝗠𝗼𝗱𝗲𝗿𝗻 𝗔𝘂𝘁𝗵 🔐 Week 13 @ Chai + Code ☕️ Learned: • SSO flow • JWT (create, verify, share) • Public vs Private keys • OIDC & auth providers Grateful to @piyushgarg_dev 🙌🏻 #chaicode #WebDevJourney #Authentication


つまり👇 ・世界は正確ではない ・でも安定して見える Gyro Logicは 👉 正しさではなく安定性を見る #GyroLogic #Authentication #Security
Weaponized cPanelSniper PoC Supercharges Global Exploitation of CVE-2026-41940 thecybrdef.com/weaponized-cpa… #cPanel #Vulnerability #Authentication #Cyberattack #Cybersecurity
Security at the Edge for Resource-Limited IoT Devices mdpi.com/1424-8220/24/2… #authentication #cybersecurity
Warning: Critical #authentication bypass vulnerability in #Apache Druid allows unauthenticated remote attackers to log in using the druid-basic-security extension with LDAP authentication. Disable anonymous LDAP bind and upgrade to Druid 36.0.0+. lists.apache.org/thread/2x9rv3k… #Patch
In an exclusive article by @WIRED’s @JulianChokkattu, @MetalenzNews breaks down their #PolarID facial #authentication system and how it could scale to mass production for consumer devices by 2027. Read here: wired.com/story/metalenz…
wired.com
This Company Has Figured Out a Way to Make Face ID Invisible
Metalenz’s Polar ID face-scanning technology works even when the camera is hidden under the display.
These efforts aim to define trusted mechanisms for how AI agents authenticate, act, and transact on behalf of users. ➡️Get the details, read our news release: fidoalliance.org/fido-alliance-… #AgenticAI #passkeys #authentication #interoperable #agenticcommerce
📢 #Journalists #contentcreators Friday game changer for you! You're welcome 😁 #authentication @OpenOrigins
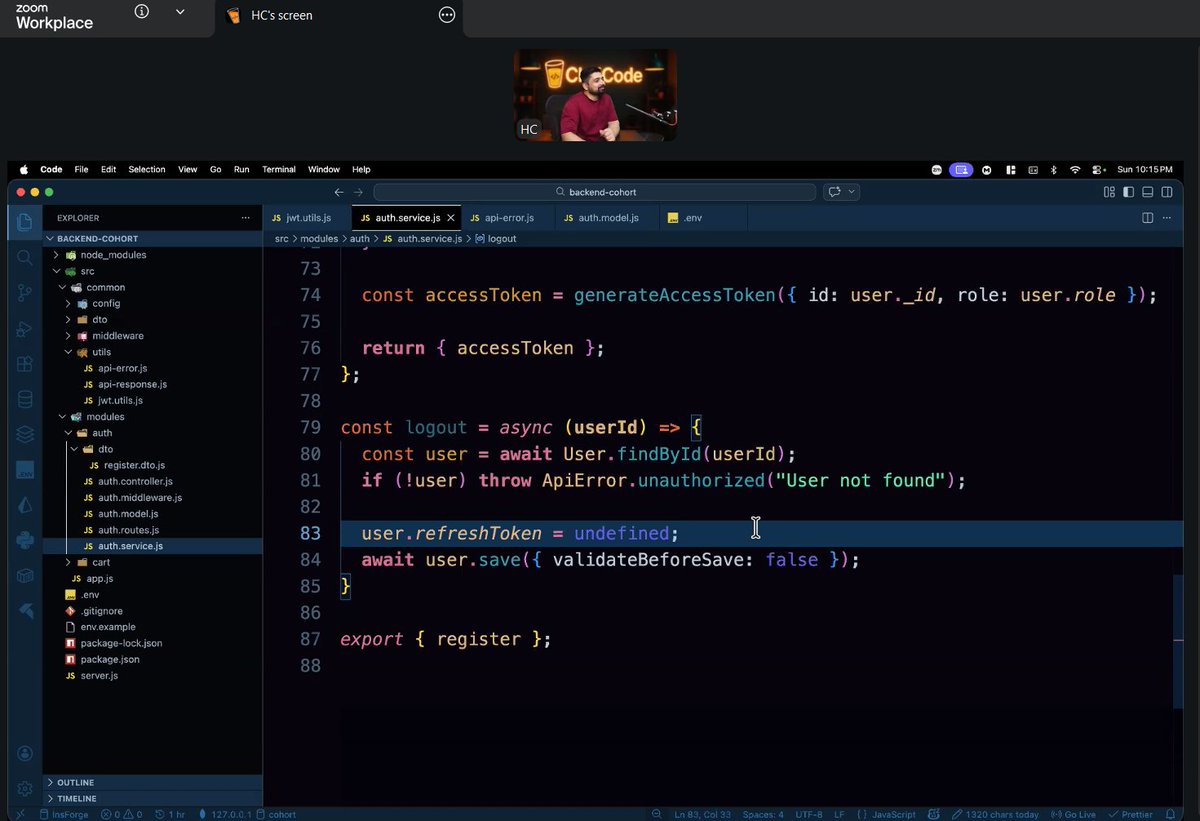
Day 29: REST API with Express class by @Hiteshdotcom and @piyushgarg_dev sir was all about understanding access tokens, refresh tokens, and how #authentication flow works #chaicode @nirudhuuu @ChaiCodeHQ @yntpdotme @BlazeisCoding @surajtwt_

Learn how to control authentication flows using AMHandler in ForgeRock Identity Gateway, enhancing your security infrastructure seamlessly. #authentication #forgeock #amhandler
It’s a reminder that adoption of #authentication methods doesn’t come from technology alone. It comes from making the user experience seamless and easy to understand which is how we’ve designed #IPification. howtogeek.com/i-tried-to-go-…
In an exclusive article by @WIRED’s @JulianChokkattu, @MetalenzNews breaks down their #PolarID facial #authentication system and how it could scale to mass production for consumer devices by 2027. Read here: wired.com/story/metalenz…
wired.com
This Company Has Figured Out a Way to Make Face ID Invisible
Metalenz’s Polar ID face-scanning technology works even when the camera is hidden under the display.
Doesn't matter if you work in tech, setting up a new phone will always take you to the #2FA/ #authentication hell. One login at a time. #patience #caseoftheMondays
Companies Have Started Moving Away from AI antonmb.com/en/blog/compan… #AI #Authentication #Cybersecurity #Infrastructure #AgenticAi
Microsoft 365 May 2026 Mega Update: New E7 Suite, Retirements, Fresh Copilot Upgrades, and a New Release Model #Authentication #Azure #Copilot #Enterprise #Keyboardshortcuts #Microsoft #Microsoft365 #MicrosoftDefender #MicrosoftTeams #OneDrive #Outlook ... msftnewsnow.com/microsoft-365-…

Weaponized cPanelSniper PoC Supercharges Global Exploitation of CVE-2026-41940 thecybrdef.com/weaponized-cpa… #cPanel #Vulnerability #Authentication #Cyberattack #Cybersecurity
Scenario Question 👨💻 You need to build a login system. What things will you consider for security? 👇 #WebSecurity #Authentication #DevCommunity
What is API Authentication and Authorisation? 🛡️ API Authentication verifies identity, while Authorisation controls what users can access. Together, they secure data. 👉zurl.co/N6WUK #API #Authentication #Authorization #CyberSecurity #InstaSafe
Reduce login barriers, not security. With SAAM, Shibboleth and Azure AD or ADFS work together through one trusted authentication flow. t.ly/overtSAAM #saam #singlesignon #authentication #itsecurity #accesscontrol

📣 New Podcast! "How to share business data with users outside of your organization with Nicholas Hayduk [MVP]" on @Spreaker #architecture #authentication #automation #copilot #customization spreaker.com/episode/how-to…

spreaker.com
Spreaker Podcasts
How to share business data with users outside of your organization...
Weaponized cPanelSniper PoC Supercharges Global Exploitation of CVE-2026-41940 thecybrdef.com/weaponized-cpa… #cPanel #Vulnerability #Authentication #Cyberattack #Cybersecurity
Learn how to control authentication flows using AMHandler in ForgeRock Identity Gateway, enhancing your security infrastructure seamlessly. #authentication #forgeock #amhandler
Weaponized cPanelSniper PoC Supercharges Global Exploitation of CVE-2026-41940 thecybrdef.com/weaponized-cpa… #cPanel #Vulnerability #Authentication #Cyberattack #Cybersecurity
Completed an authentication assignment using freeapi.app 🚀 User register and login flow with API. Good hands-on practice of React. @Hiteshdotcom @ChaiCodeHQ #react #authentication #api #webdevelopment #chaicode #learninginpublic
Hot take 🔐 Two-factor authentication should be mandatory on every website admin panel no exceptions. Agree or disagree? And why? 👇 #EthicalHacking #CyberSecurity #Authentication #InfoSec #WebSecurity
@SelvaKtm2 Weaponized cPanelSniper PoC Supercharges Global Exploitation of CVE-2026-41940 thecybrdef.com/weaponized-cpa… #cPanel #Vulnerability #Authentication #Cyberattack #Cybersecurity
🔒 Authentication vs Authorization: Key Differences Every Developer Must Know 💡 Confusing authentication with authorization is one of the most common security design flaws. ➡️ sslinsights.com/authentication… #Authentication #Authorization #CyberSecurity #IAM #SSLInsights
Big realization: 👉 Auth is not just login/signup 👉 It’s about session security Most tutorials skip this part. Don’t. #Authentication #Security #MERN #NodeJS
Unified Digital Identity for Seamless Authentication Across Platforms Read More:- bi-journal.com/unified-digita… #DigitalIdentity #CyberSecurity #Authentication #ZeroTrust #IAM #CloudSecurity #DigitalTransformation #EnterpriseSecurity

GyroAuth approaches this differently: → observe multi-dimensional state → evaluate stability → continuous loop Authentication = State Convergence #GyroAuth #Security #Authentication
Old #authentication habits die hard buff.ly/tfMLdfW @HelpNetSecurity @Yubico #cybersecurity #security #infosec #tech #identity #IAM #MFA #accessmanagement #identitymanagement #business #leadership #management #CISO #CIO #CTO #CEO #securityawareness #securitytraining

SMS and OTP Bombing Tools Evolve into Scalable, Global Abuse Infrastructure cysecurity.news/2026/02/sms-an… #APIexploitation #Authentication #MFAfatigue

Product showcase: Proton Authenticator is an end-to-end encrypted, open source 2FA app - helpnetsecurity.com/2026/04/06/pro… - @ProtonPrivacy #Authentication #Privacy #IdentityProtection #Cybersecurity #CybersecurityNews

Where Multi-Factor #Authentication Stops and Credential Abuse Starts buff.ly/Nv5RRAi @TheHackersNews #tech #MFA #cybersecurity #identity #identitymanagement #accessmanagement #IAM #leadership #management #leaders #CISO #CIO #CTO #cyberthreats #cyberattacks

Product showcase: 2FAS Auth – Free, open-source 2FA for iOS - helpnetsecurity.com/2026/02/03/pro… - @2FAS_com #Authentication #IdentityManagement #IdentityProtection #2FA #Cybersecurity #CybersecurityNews
1Password ora può sbloccarsi da solo con il computer Mac e Windows: basta il volto, impronta o PIN 🔐 Blocchi meno frequenti, sicurezza uguale #1Password #Cybersecurity #Authentication

One stolen credential is all it takes to compromise everything - helpnetsecurity.com/2026/02/18/ide… - @PaloAltoNtwks @Unit42_Intel - #authentication #credentials #CyberCrime #CISO #CyberSecurity #CyberSecurityNews #SecurityNews

Hardware Acceleration-Based Privacy-Aware Authentication Scheme for Internet of Vehicles Using Physical Unclonable Function mdpi.com/1424-8220/25/5… #Internet_of_Vehicles #authentication

Users advised to drop passwords and make room for passkeys - helpnetsecurity.com/2026/04/24/ncs… - @NCSC @Sophos #Authentication #Passkeys #Passwordless #Passwords #Cybersecurity #CyberSecurityNews #SecurityNews

UIDAI records 231 crore Aadhaar authentication transactions in November Read the full news here👇 psuconnect.in/news/uidai-rec… #uidai #adhhar #authentication #digitalidentity #egovrnance #PSU #psuconnect @UIDAI

🎉 🔐 Join the Industry to Celebrate World Passkey Day, May 7! We're getting ready for WPD and encouraging other organizations to get ready and start planning too! #WorldPasskeyDay #passkeys #authentication 🧵👇

Attend tomorrow's live Webinar: How the Financial Industry is Smarter with AI, but Safer with Identity Join this Finextra #webinar, in partnership with @auth0, to explore the critical questions surrounding #security and #authentication in the age of #agenticAI, particularly as
Today’s class was -Learned Authentication, -PostgreSQL integration, -and Drizzle ORM @Hiteshdotcom @piyushgarg_dev #ChaiDrizzle #Authentication

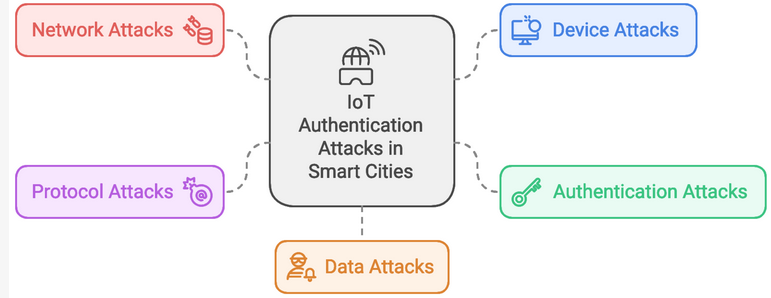
A Review of the Authentication Techniques for Internet of Things Devices in Smart Cities: Opportunities, Challenges, and Future Directions mdpi.com/1424-8220/25/6… #Internet_of_Things #authentication
Brainstorming class on auth service! Code with Diagram. Today's topic: => Register / Login => Authentication => Authorization => JWT and more Thank you sir, @Hiteshdotcom @piyushgarg_dev @nirudhuuu @yntpdotme @devwithjay @BlazeisCoding and @ChaiCodeHQ team #auth #authentication


Microsoft sets a path to switch off NTLM across Windows - helpnetsecurity.com/2026/02/02/mic… - @Microsoft @msftsecurity - #Windows #authentication #CyberSecurity #CyberSecurityNews #SecurityNews

Just wrapped today’s auth class at @ChaiCodeHQ “Frontend pe trust mat karo” hit hard → always validate requests. Deep dived into - JWT -access vs refresh tokens -How JWT-based authentication works and much more Thanks to @Hiteshdotcom #chaicode #auth #authentication



Something went wrong.
Something went wrong.
United States Trends
- 1. Happy Cinco de Mayo N/A
- 2. Good Tuesday N/A
- 3. Wemby N/A
- 4. Met Gala N/A
- 5. Taco Tuesday N/A
- 6. $CHIMP N/A
- 7. Spurs N/A
- 8. TOP CALL N/A
- 9. QUICK TRADE N/A
- 10. Smart Money - Buy N/A
- 11. Wolves N/A
- 12. Travis Kelce N/A
- 13. Whale - Buy N/A
- 14. The Odyssey N/A
- 15. Mike Conley N/A
- 16. Mitch Johnson N/A
- 17. Christopher Nolan N/A
- 18. Julius Randle N/A
- 19. Anthony Edwards N/A
- 20. Sam Smith N/A