#botnet search results
React2Shell exploitation explodes as botnets now join the fray #React2Shell #botnet #CyberSecurity cyberinsider.com/react2shell-ex…
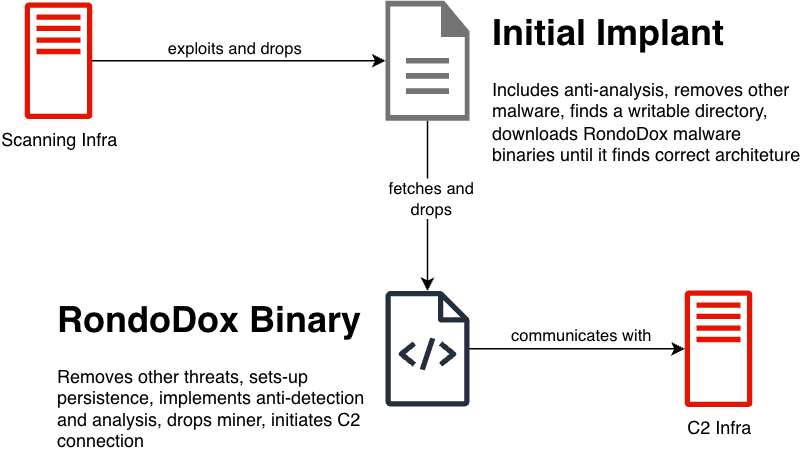
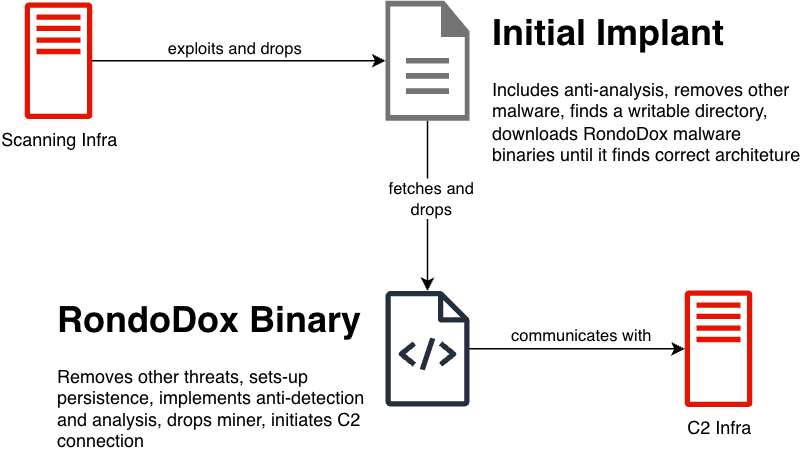
BitSight exposes RondoDox, a relentless IoT botnet using a "shotgun approach" with 174 exploits to hijack residential devices for massive DoS attacks. #RondoDox #Botnet #IoTSecurity #BitSight #CyberSecurity #ThreatIntel #InfoSec #DoS #Malware #TechNews securityonline.info/shotgun-approa…

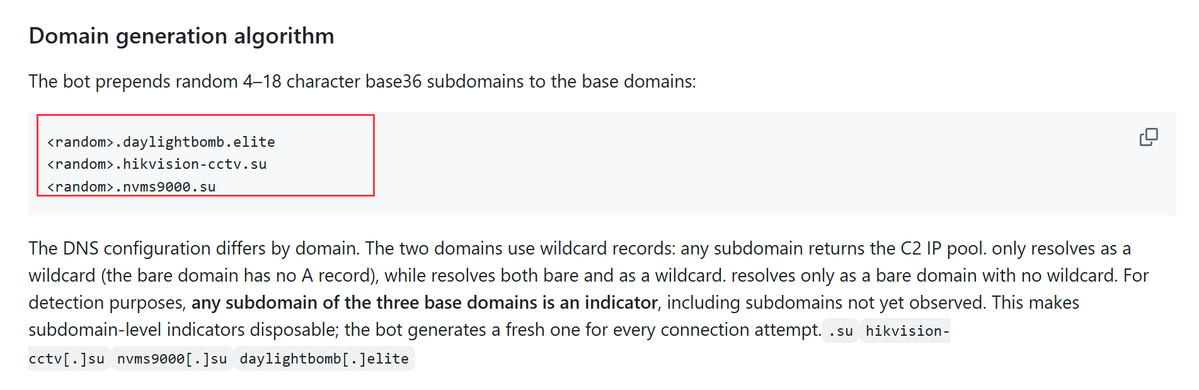
What distinguishes #Botnet "Drifter" is how it hides. Its C2 domains are named after IP camera brands (, ), chosen to blend with the traffic of devices that share a VLAN with the Android TV boxes it infects. github.com/deepfield/publ…
New SSHStalker botnet uses vintage IRC tactics & automated SSH brute-forcing to compromise Linux servers. Flare research reveals a "zombie army" in the making. #SSHStalker #LinuxSecurity #Botnet #CyberSecurity #InfoSec #IRC #CloudSecurity securityonline.info/back-to-the-fu…
Simple FREE Firefox VPN Are free VPNs safe in 2026? Discover why Mozilla's new built-in Firefox VPN might save you from malicious apps and botnets. Protect your web traffic now! #firefox #vpn #botnet
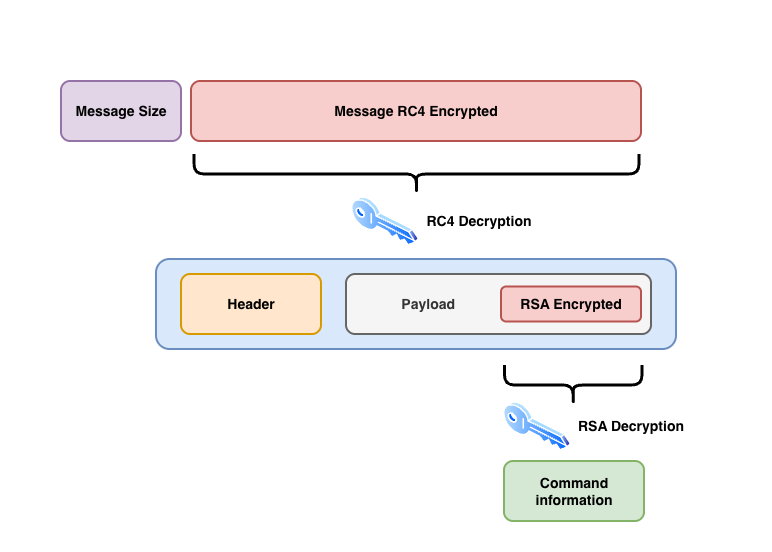
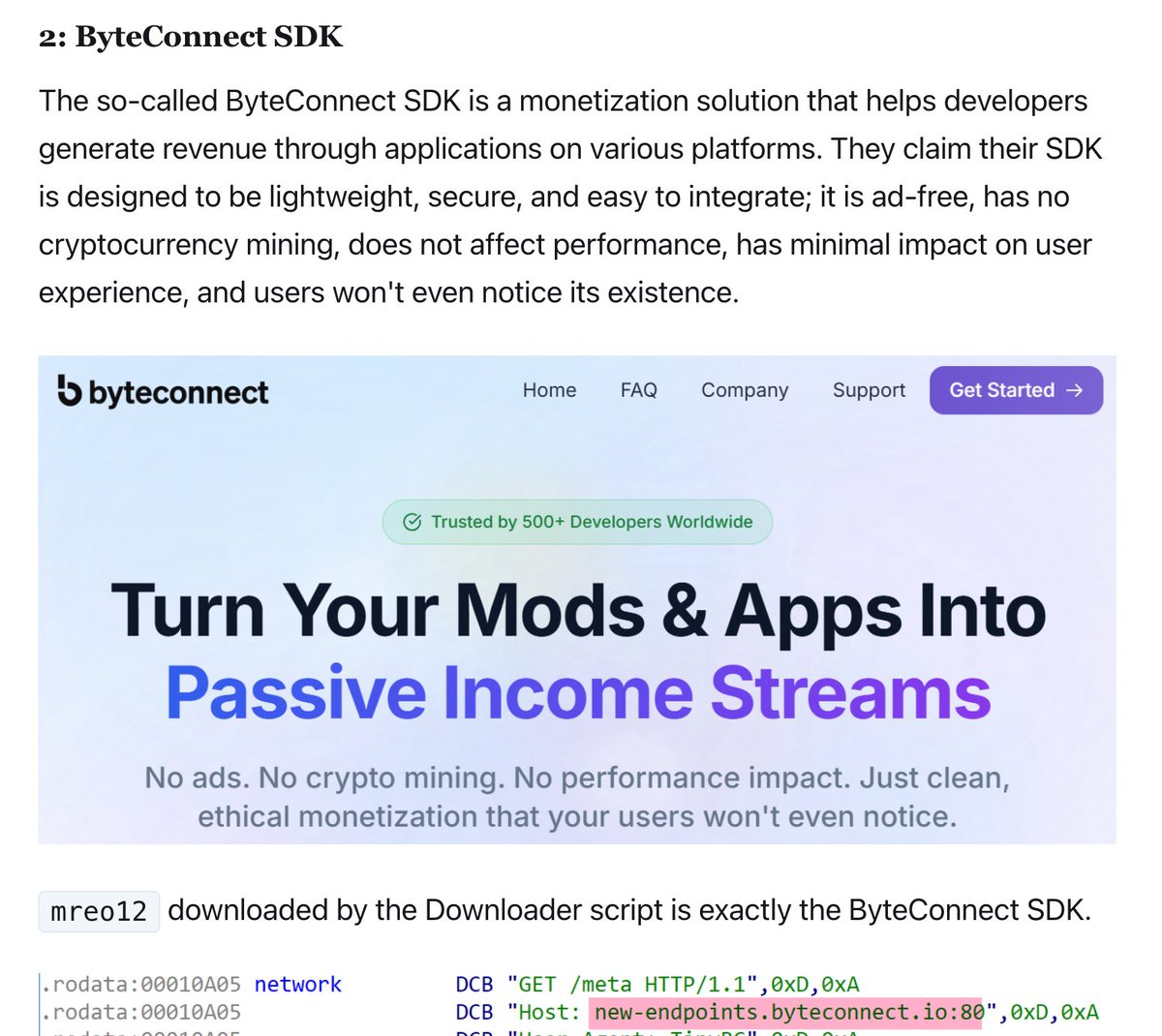
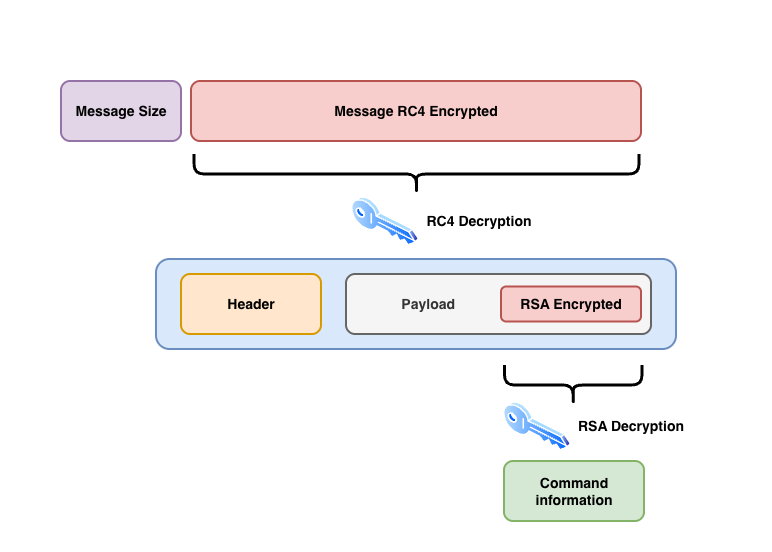
Bitsight unmasks the Phorpiex "Twizt" variant: a self-healing P2P botnet with RSA-encrypted payloads and LFI scanners. See how this 2011 threat stays relevant. #Phorpiex #Botnet #CyberSecurity #InfoSec #MalwareAnalysis #P2P #ThreatIntel #Twizt securityonline.info/phorpiex-botne…
Lumen disrupted the Aisuru and Kimwolf botnets by cutting off 550 command-and-control servers. #botnet #cybersecurity cnews.link/lumen-strikes-…
#botnet The KimWolf botnet (also known as "niggabox") is a large-scale Android malware targeting TV boxes, set-top boxes, and tablets, infecting over 1.8 million devices across 222 countries. It evolved from the Aisuru botnet and focuses on proxy services and DDoS attacks.
Researchers report that the Kimwolf botnet has infected over 2 million Android devices through residential proxies, executing massive DDoS attacks and highlighting the risks posed by unsecured proxy networks. #cybersecurity #botnet securityaffairs.com/186559/malware…
Panne mondiale 🌎 d’Amazon : un #botnet a profité du chaos pour lancer des #cyberattaques, et infecter en douce des objets connectés Le botnet exploite au moins 8 failles identifiées dans les IoTs buff.ly/ywezagL
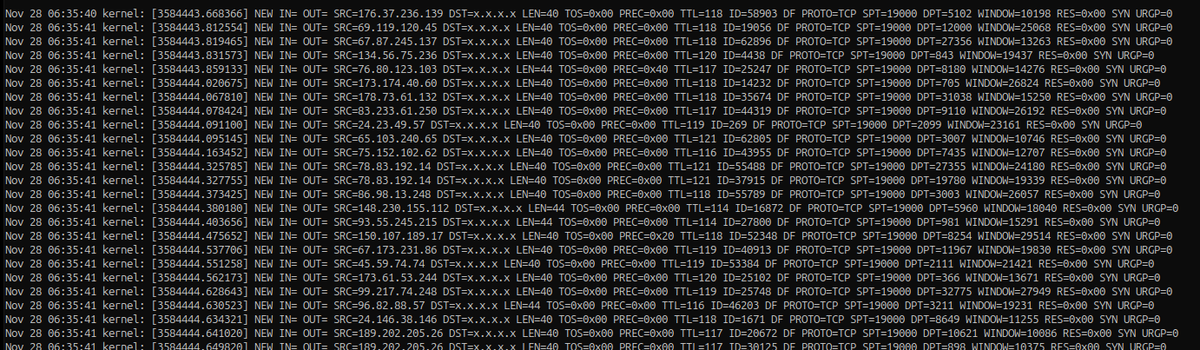
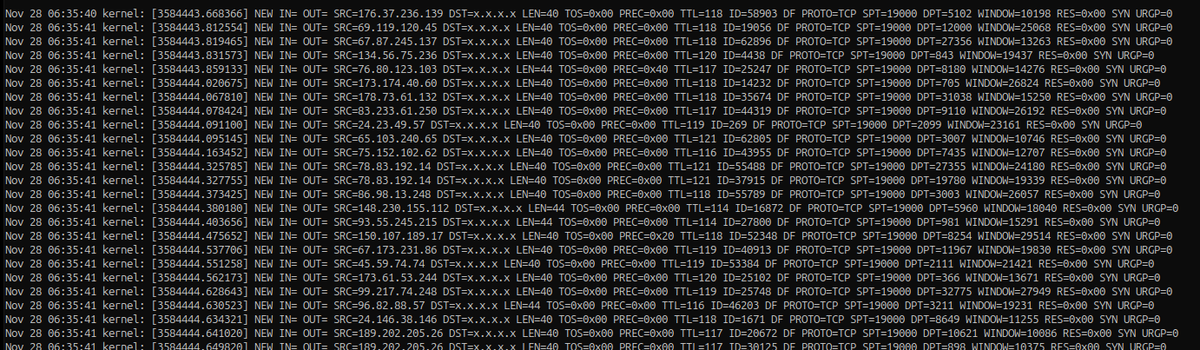
An unusually large, moments ago #botnet scan all from source port 19000 (not the "usual" Amazon sourced scans that I see every morning like clockwork at 06:45). Raw logs and source IP's: gist.github.com/silence-is-bes…
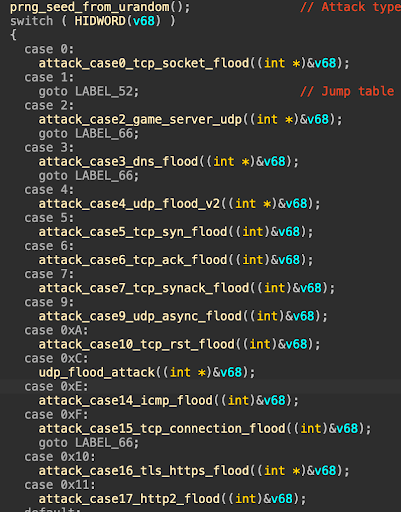
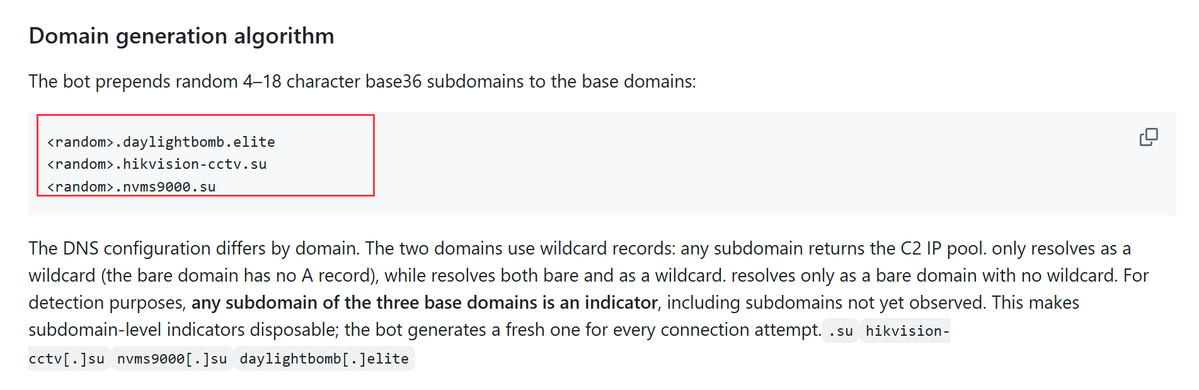
#Kimwolf v7: The updated #IoT #botnet behind record #DDoS attacks adds HTTP/2 floods with Chrome fingerprint spoofing, #Tor backup C2, and five Ethereum RPC endpoints for resilient blockchain-based infrastructure. Details at bit.ly/4s2U894
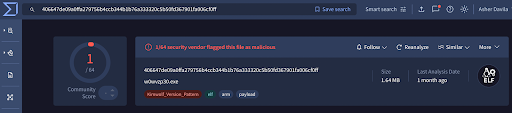

Security experts have exposed Kimwolf, a massive Android botnet infecting over 1.8 million devices, utilizing advanced techniques like DNS over TLS and EtherHiding to evade detection and launch large-scale DDoS attacks. #CyberSecurity #Botnet blog.xlab.qianxin.com/kimwolf-botnet…
Cydome warns that the Mirai-based Broadside botnet is exploiting a vulnerability in TBK DVRs, posing serious threats to maritime logistics by enabling DDoS attacks and compromising critical systems on vessels. #CyberSecurity #Botnet securityaffairs.com/185491/malware…
A new botnet called "Broadside" is threatening shipping companies by stealing credentials from infected TBK DVR devices and launching DDoS attacks, according to SecurityWeek. #CyberSecurity #Botnet securityweek.com/new-broadside-…
🚨 Active exploitation alert: New Mirai botnet campaign exploiting CVE-2025-29635 (RCE) on End-of-Life D-Link routers. If your network still runs EoL devices, you're volunteering compute power to threat actors. Replace or isolate NOW. #IoTSecurity #Mirai #Botnet #CVE
📡🦠 mirai campaign exploits d-link routers for botnet growth Attackers target vulnerable routers to expand botnets using a known RCE flaw. learn more bleepingcomputer.com #mirai #iot #botnet #cybersecurity #infosec

@Akamai #Mirai #Botnet exploits CVE-2025-29635 to target legacy D-Link routers securityaffairs.com/191135/malware… #securityaffairs #hacking #malware
Demon botnet — new multi-arch samples (2026-04-22) SH4, MIPS-LE, MIPS variants | 43-45 VT detections ns3.jpg: ELF disguised as JPEG (44 VT) — evades file-type filters bins.sh: multi-arch Mirai downloader (36 VT) TLP:WHITE #ThreatIntel #BotNet #MalwareAnalysis
New Mirai variants target routers and DVRs in parallel campaigns - helpnetsecurity.com/2026/04/22/new… - @Akamai @akamai_research @FortiGuardLabs @Fortinet #Botnet #DDoS #DVR #Malware #Router #SMBs #Cybersecurity #CybersecurityNews

The Gentlemen ransomware-as-a-service has expanded rapidly, infecting 1,570+ corporate networks via SystemBC proxy using tactics like GPO abuse and Defender disabling across Windows, Linux, NAS, and ESXi. #Ransomware #Botnet #Israel ift.tt/gYqfOtT
🤖🦠 gentlemen ransomware uses botnet for attacks A large botnet is powering ransomware operations, increasing scale and impact of attacks. #ransomware #botnet #malware #cybersecurity #infosec

New honeypot signals — Apr 14-21 SIP port 5060 scanning: 220 events (first observed) Mirai creds dominating SSH: 345gs5662d34:345gs5662d34 (691 attempts) IoT botnet still spreading via Mirai credential cycling. #ThreatIntel #Honeypot #BotNet #SSH
🔴 BOTNET ALERT: Nexcorium (Mirai variant) exploits CVE-2024-3721 to hijack TBK DVRs for DDoS attacks. Millions of IoT devices still unpatched & vulnerable. Update your firmware NOW. #IoTSecurity #DDoS #Botnet
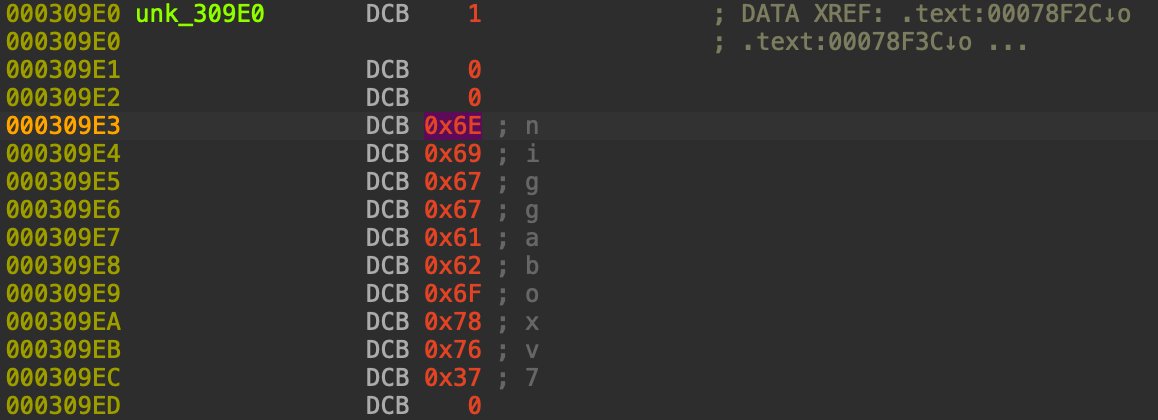
BitSight unmasks RondoDox: a modular botnet using "nanomites" to dodge debuggers while hijacking 18 architectures for Monero mining and gaming DoS attacks. #RondoDox #Botnet #CyberSecurity #InfoSec #Malware #GamingSecurity #IoT #Nanomites securityonline.info/rondodox-botne…
#ThreatProtection #Nexcorium #botnet - a new #Mirai variant, read more about Symantec's protection: broadcom.com/support/securi… #malware
2/2 ↳ Persists via crontab + systemd ↳ Launches DDoS over UDP, TCP & SMTP ↳ EoL TP-Link routers also in the crosshairs 🎯 IoT devices = sitting ducks. Patch. Isolate. Replace. #Botnet #InfoSec #BotnetAlert
Cisco Talos uncovers PowMix, a stealthy botnet targeting Czech HR via AMSI bypass and Heroku-hosted C2. Learn how this malware evades modern EDR systems. #PowMix #Botnet #CyberSecurity #InfoSec #CzechRepublic #Malware #CiscoTalos #AMSIBypass securityonline.info/powmix-botnet-…

☣️ Mirai Variant Nexcorium Exploits CVE-2024-3721 to Hijack TBK DVRs for DDoS Botnet thehackernews.com/2026/04/mirai-… #iot #ddos #botnet #cybersecurity
Mirai Malware Spreads Through Vulnerable TBK DVR Devices cysecurity.news/2026/04/mirai-… #Botnet #CVEvulnerability #DVR

A recent campaign exploiting CVE-2024-3721 in TBK DVR devices to deliver a multi-architecture Mirai variant called Nexcorium #botnet fortinet.com/blog/threat-re…

Mirai Malware Evolves into Hundreds of Variants Driving Botnet Growth buff.ly/3BKMg7j #infosec #cybersecurity #botnet #malware

Cisco Talos uncovers 'PowMix,' a new botnet targeting the Czech Republic. Uses randomized C2 beaconing and embeds data in URL paths to evade detection. 🇨🇿 #Botnet #PowMix #Malware #ThreatIntel #CiscoTalos 🔗 cyber.netsecops.io/articles/steal…
Newly Discovered #PowMix #Botnet Hits Czech Workers Using Randomized #C2 Traffic scyscan.com/news/newly-dis…
scyscan.com
Newly Discovered PowMix Botnet Hits Czech Workers Using Randomized C2 Traffic | ScyScan
Cybersecurity researchers have warned of an active malicious campaign that's targeting the workforce in the Czech Republic with a previously undocumented bot...
What distinguishes #Botnet "Drifter" is how it hides. Its C2 domains are named after IP camera brands (, ), chosen to blend with the traffic of devices that share a VLAN with the Android TV boxes it infects. github.com/deepfield/publ…
BitSight unmasks RondoDox: a modular botnet using "nanomites" to dodge debuggers while hijacking 18 architectures for Monero mining and gaming DoS attacks. #RondoDox #Botnet #CyberSecurity #InfoSec #Malware #GamingSecurity #IoT #Nanomites securityonline.info/rondodox-botne…
A recent campaign exploiting CVE-2024-3721 in TBK DVR devices to deliver a multi-architecture Mirai variant called Nexcorium #botnet fortinet.com/blog/threat-re…

BitSight exposes RondoDox, a relentless IoT botnet using a "shotgun approach" with 174 exploits to hijack residential devices for massive DoS attacks. #RondoDox #Botnet #IoTSecurity #BitSight #CyberSecurity #ThreatIntel #InfoSec #DoS #Malware #TechNews securityonline.info/shotgun-approa…

#tracking #moobot #botnet with @silentpush @silentpush_labs html_body_ssdeep #moobot typically has a redirect count down 3,2,1, towards fbi[.]gov we are leveraging this unique identicator to track moobot. Lets investigate the first ip: 161.97.175.164
![banthisguy9349's tweet image. #tracking #moobot #botnet with @silentpush @silentpush_labs html_body_ssdeep
#moobot typically has a redirect count down 3,2,1, towards fbi[.]gov we are leveraging this unique identicator to track moobot.
Lets investigate the first ip: 161.97.175.164](https://pbs.twimg.com/media/GeR6u37XoAEcoiT.jpg)
![banthisguy9349's tweet image. #tracking #moobot #botnet with @silentpush @silentpush_labs html_body_ssdeep
#moobot typically has a redirect count down 3,2,1, towards fbi[.]gov we are leveraging this unique identicator to track moobot.
Lets investigate the first ip: 161.97.175.164](https://pbs.twimg.com/media/GeR6_mhXcAIkqWz.jpg)
For those tracking #botnet activity, a rather impressive scan (moments ago) sourced from port 19000; raw logs and source IP's here: gist.github.com/silence-is-bes…

#botnet The KimWolf botnet (also known as "niggabox") is a large-scale Android malware targeting TV boxes, set-top boxes, and tablets, infecting over 1.8 million devices across 222 countries. It evolved from the Aisuru botnet and focuses on proxy services and DDoS attacks.
Cisco Talos uncovers PowMix, a stealthy botnet targeting Czech HR via AMSI bypass and Heroku-hosted C2. Learn how this malware evades modern EDR systems. #PowMix #Botnet #CyberSecurity #InfoSec #CzechRepublic #Malware #CiscoTalos #AMSIBypass securityonline.info/powmix-botnet-…

Bitsight unmasks the Phorpiex "Twizt" variant: a self-healing P2P botnet with RSA-encrypted payloads and LFI scanners. See how this 2011 threat stays relevant. #Phorpiex #Botnet #CyberSecurity #InfoSec #MalwareAnalysis #P2P #ThreatIntel #Twizt securityonline.info/phorpiex-botne…
An unusually large, moments ago #botnet scan all from source port 19000 (not the "usual" Amazon sourced scans that I see every morning like clockwork at 06:45). Raw logs and source IP's: gist.github.com/silence-is-bes…
Panne mondiale 🌎 d’Amazon : un #botnet a profité du chaos pour lancer des #cyberattaques, et infecter en douce des objets connectés Le botnet exploite au moins 8 failles identifiées dans les IoTs buff.ly/ywezagL
Botnet was used to launch ransomware attacks against dozens of US businesses. More: cnews.link/russian-cyberc… #botnet #US #crime #ransomware

bobbot[.]xcvx[.]online xcvx[.]online 3 malware samples communicating to @Namecheap registered domain virustotal.com/gui/domain/bob… #hailbot #botnet cc: @abuse_ch
![banthisguy9349's tweet image. bobbot[.]xcvx[.]online
xcvx[.]online
3 malware samples communicating to @Namecheap registered domain virustotal.com/gui/domain/bob…
#hailbot #botnet
cc: @abuse_ch](https://pbs.twimg.com/media/G60zj60XMAAo26a.png)
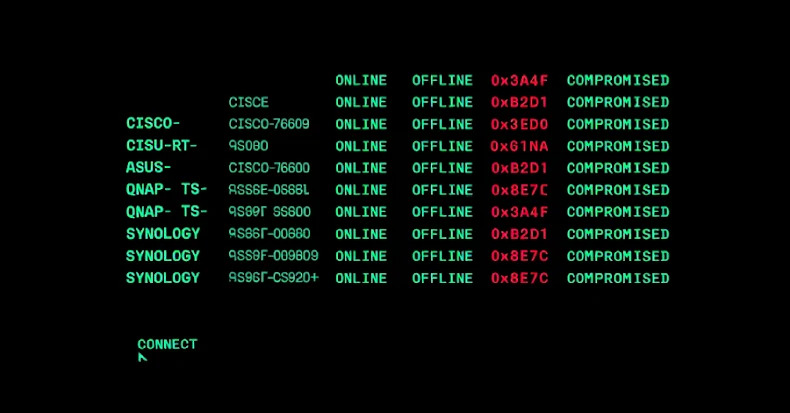
PolarEdge Targets Cisco, ASUS, QNAP, Synology Routers in Expanding Botnet Campaign dlvr.it/TPMQ3F #Cybersecurity #Botnet #Malware #PolarEdge #Cisco
Something went wrong.
Something went wrong.
United States Trends
- 1. #NFLDraft N/A
- 2. Lemon N/A
- 3. Bain N/A
- 4. #wojakcto N/A
- 5. Ty Simpson N/A
- 6. Knicks N/A
- 7. Caleb Downs N/A
- 8. Brunson N/A
- 9. Jets N/A
- 10. AJ Brown N/A
- 11. Stafford N/A
- 12. Eagles N/A
- 13. Steelers N/A
- 14. Mike Brown N/A
- 15. Cowboys N/A
- 16. Reese N/A
- 17. Dolphins N/A
- 18. Browns N/A
- 19. Dillon Thieneman N/A
- 20. Chiefs N/A















































![Eng_braun's profile picture. [Software Engineer]
[Cyber Security Specialist]
🇿🇲](https://pbs.twimg.com/profile_images/1166801998932578304/wGIiemO3.jpg)