#metasploit 搜尋結果
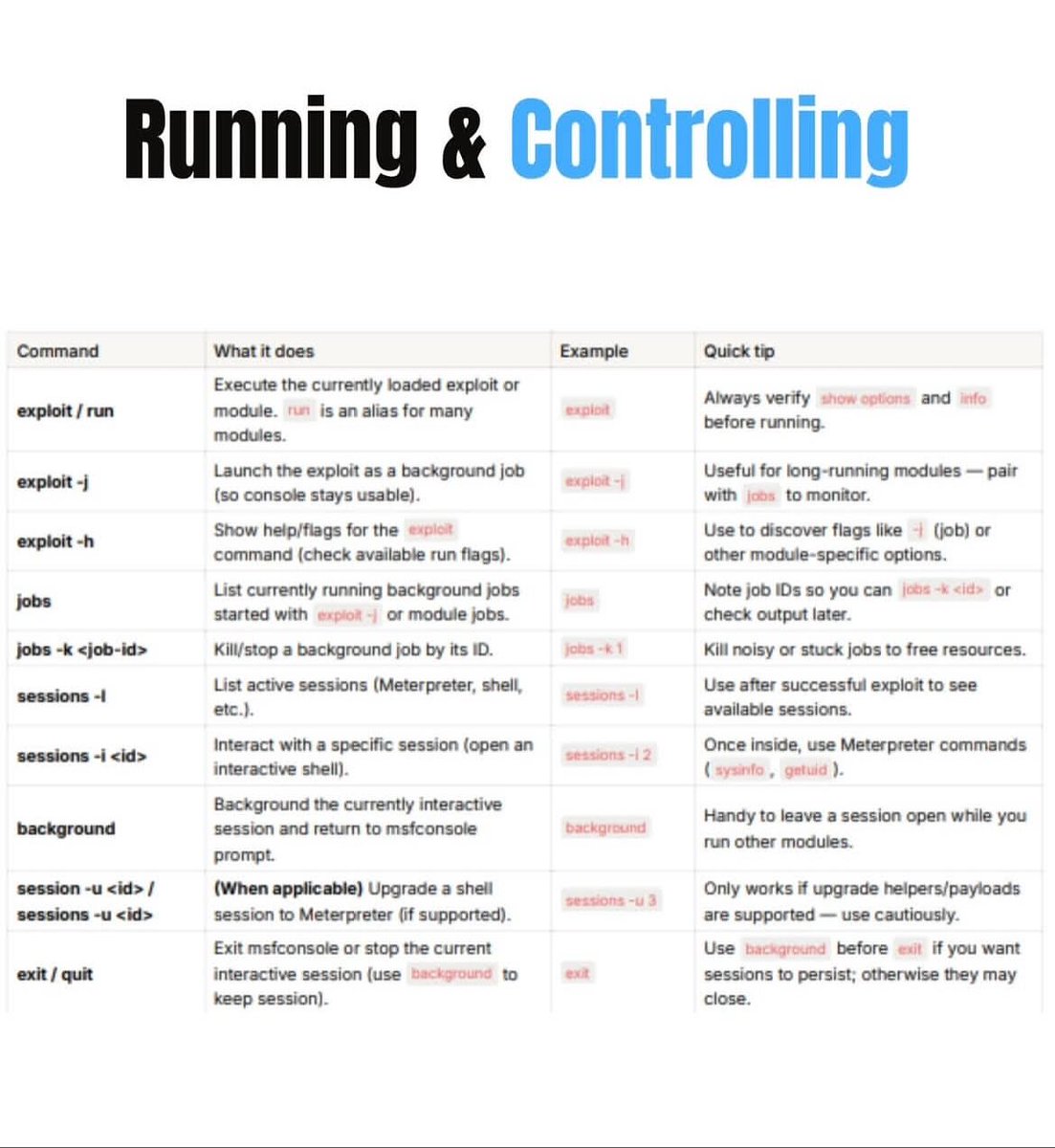
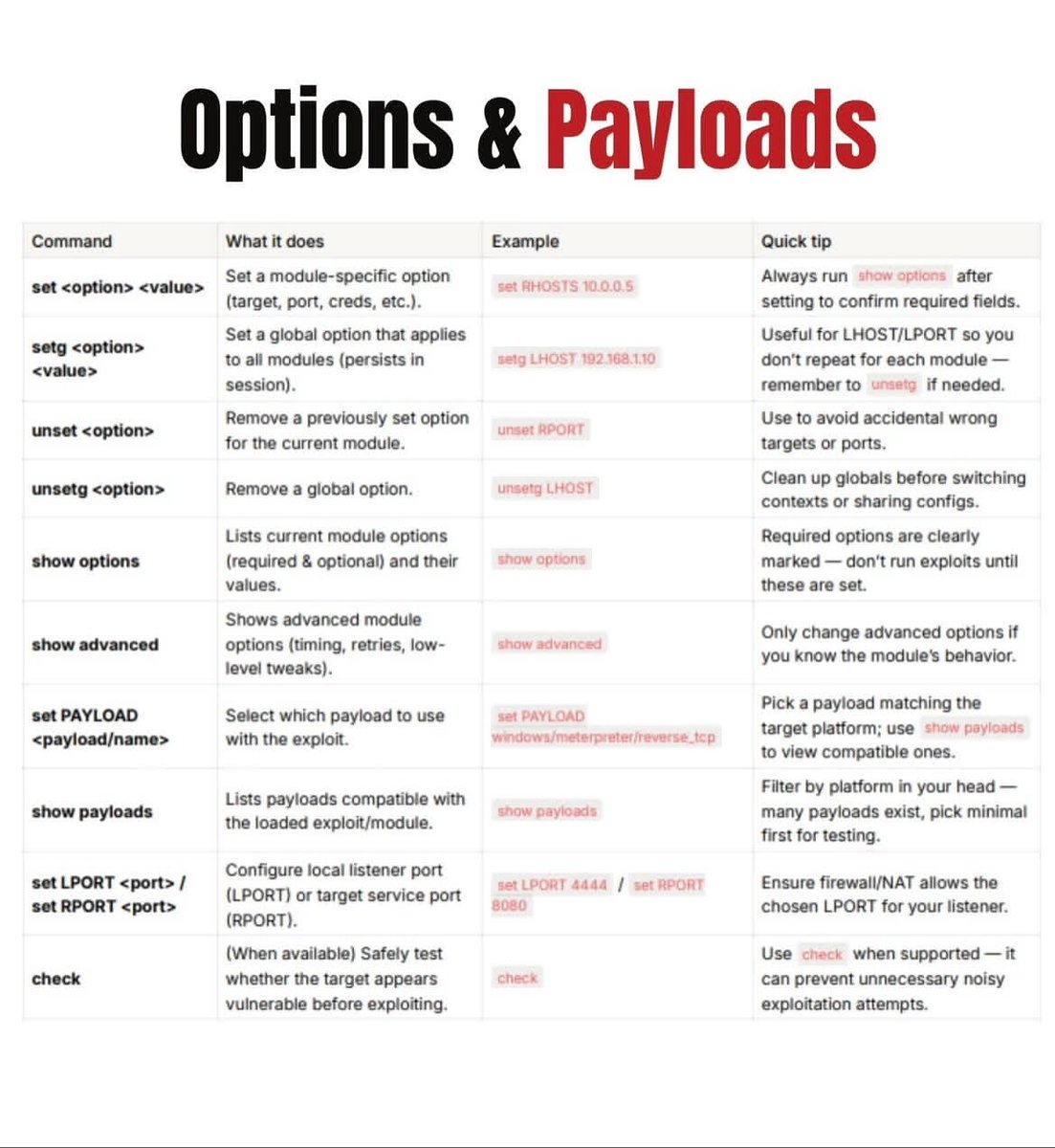
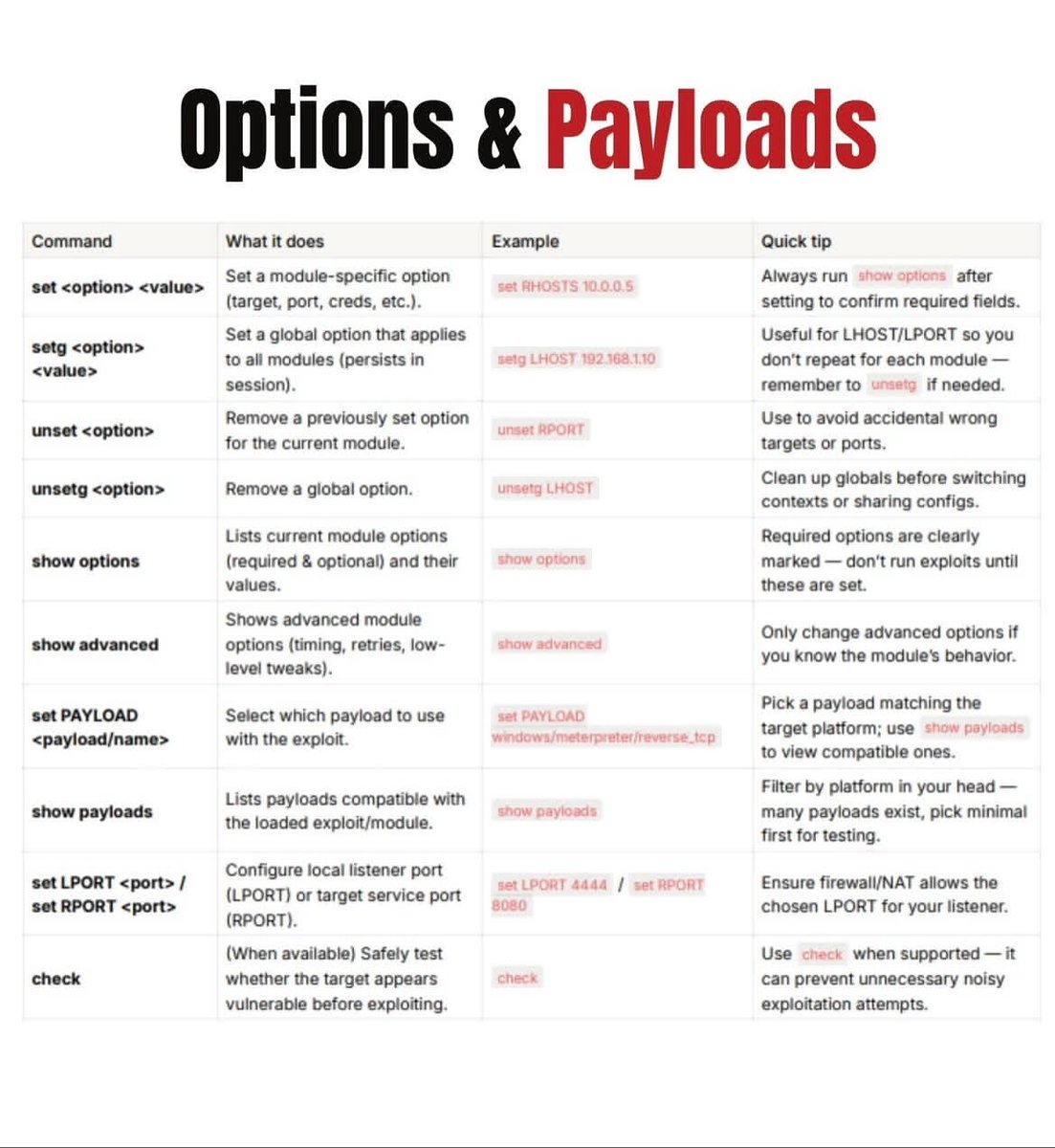
⚡ Metasploit Cheatsheet The Metasploit Framework is one of the most widely used platforms for vulnerability validation, security testing, and exploitation research. 🔖 #Metasploit #RedTeam #Pentesting #CyberSecurity #InfoSec #SecurityTesting #DFIR #EthicalHacking

💥 Metasploit — Comprehensive Guide: Framework, Workflows & Safe Use ☣️ A compact overview of Metasploit’s core components (msfconsole, msfvenom, modules, and Meterpreter), common workflows for authorized validation, and how to document findings responsibly. #Metasploit



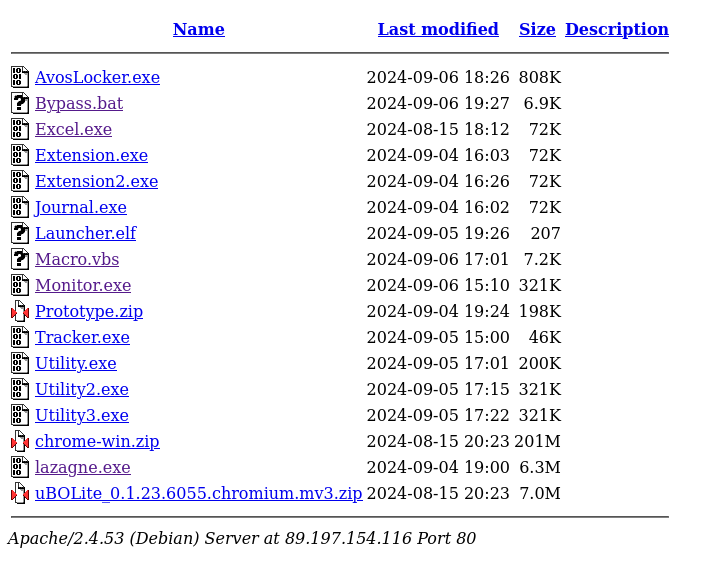
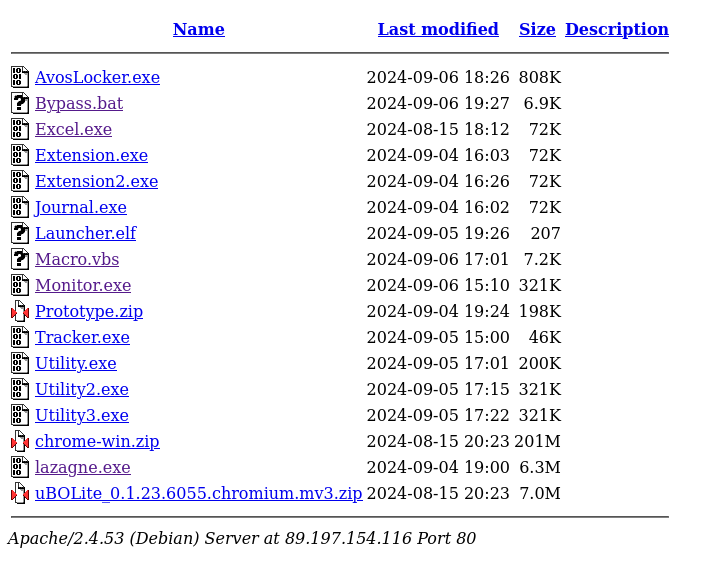
#Metasploit #Malware 💣89.197.154.116💣 Files: Excel.exe - Meterpreter Shell Macro.vbs - Creates and Executes an Exe named uWeBbVRuMcAR.exe (connects to C2) Monitor.exe - Marte Beacon C2:89.197.154.116:7810 app.any.run/tasks/c2eebee7… tria.ge/240908-q53hba1… virustotal.com/gui/file/5e436…


🧠 Metasploit – Automate Security Testing Like a Pro 🛡️ Metasploit is one of the most advanced and widely used cybersecurity frameworks for testing and strengthening system defenses. #CyberSecurity #Metasploit #EthicalTesting #SecurityFramework #VulnerabilityAssessment


24664a5adc23a7df4e6f55e81ca25977d9ef469b066ac39d53a845ea6a4481e7 193[.]161[.]193[.]99:29675 #Metasploit
![skocherhan's tweet image. 24664a5adc23a7df4e6f55e81ca25977d9ef469b066ac39d53a845ea6a4481e7
193[.]161[.]193[.]99:29675
#Metasploit](https://pbs.twimg.com/media/Gmr9xJ9bkAAjtum.jpg)
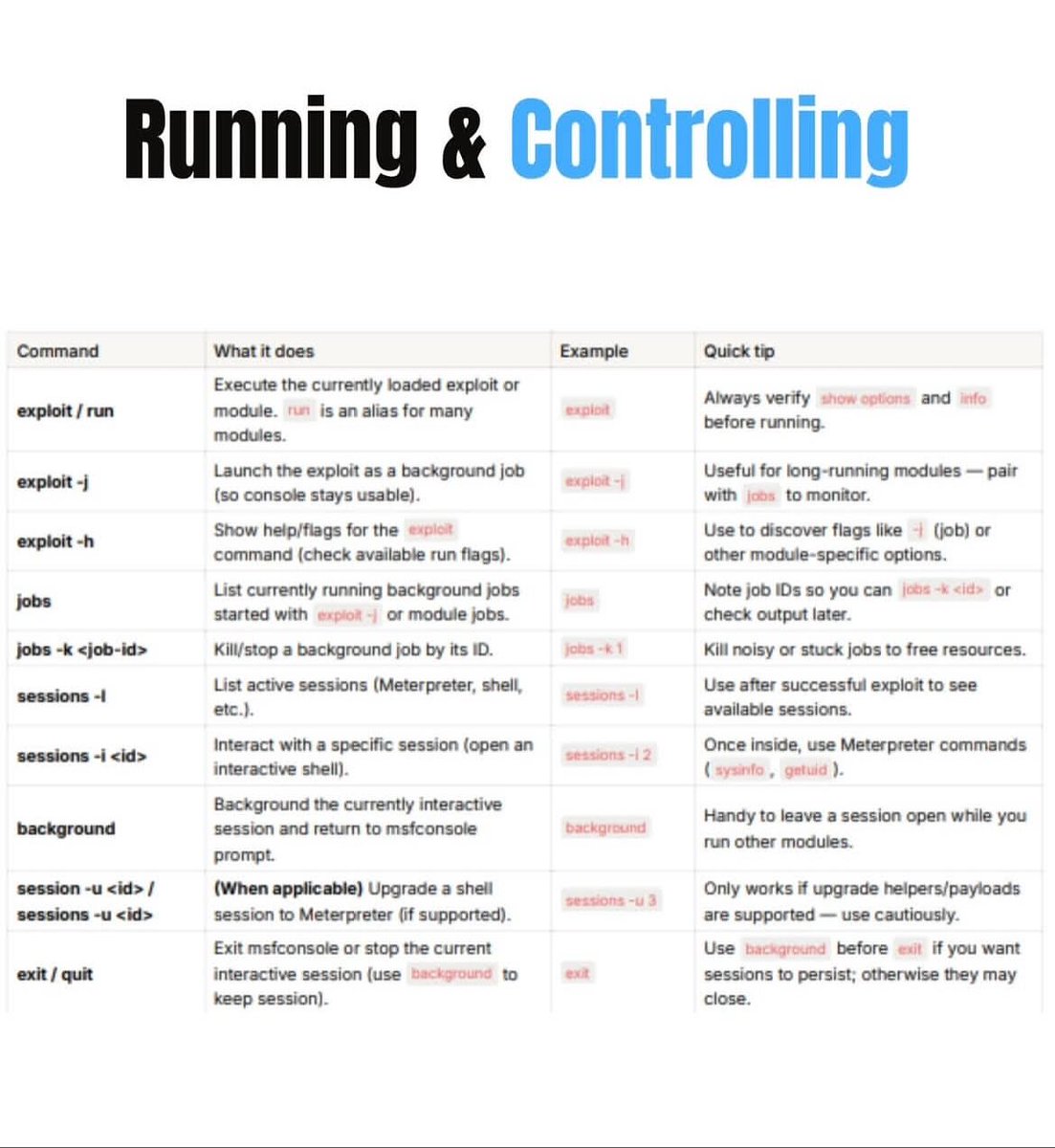
🚨 #OpenDir: 178.61.171[.67 🦠 #Metasploit [Shikata Ga Nai]: neq32.exe 💡 Shikata Ga Nai (SGN), meaning “nothing can be done about it,” is an evasion tool used for hiding payloads. It helps make malicious code harder to detect 🛡️. 🎯 C2: 178.61.171[.67:1336
![karol_paciorek's tweet image. 🚨 #OpenDir: 178.61.171[.67
🦠 #Metasploit [Shikata Ga Nai]: neq32.exe
💡 Shikata Ga Nai (SGN), meaning “nothing can be done about it,” is an evasion tool used for hiding payloads. It helps make malicious code harder to detect 🛡️.
🎯 C2: 178.61.171[.67:1336](https://pbs.twimg.com/media/GaKNteXWQAA_BVV.png)
#الأمن_السيبراني 🛡️ من الاختراق إلى السيطرة، كشف أسرار وحدات ما بعد الاستغلال المتقدمة في Metasploit 💣☢️.. 🛡️ ما هي وحدات ما بعد الاستغلال (Post-Exploitation Modules)؟ ☠️ هي مكونات برمجية (أدوات أو سكربتات) مدمجة في إطار عمل #Metasploit ،،، تابع 👇🏻

#opendir #metasploit 💣89.197.154.116💣 Files: - Mile.exe - C2: 89.197.154.116:7810 - Trial.exe - C2: 89.197.154.116:7810 virustotal.com/gui/file/19970… virustotal.com/gui/file/4246f…

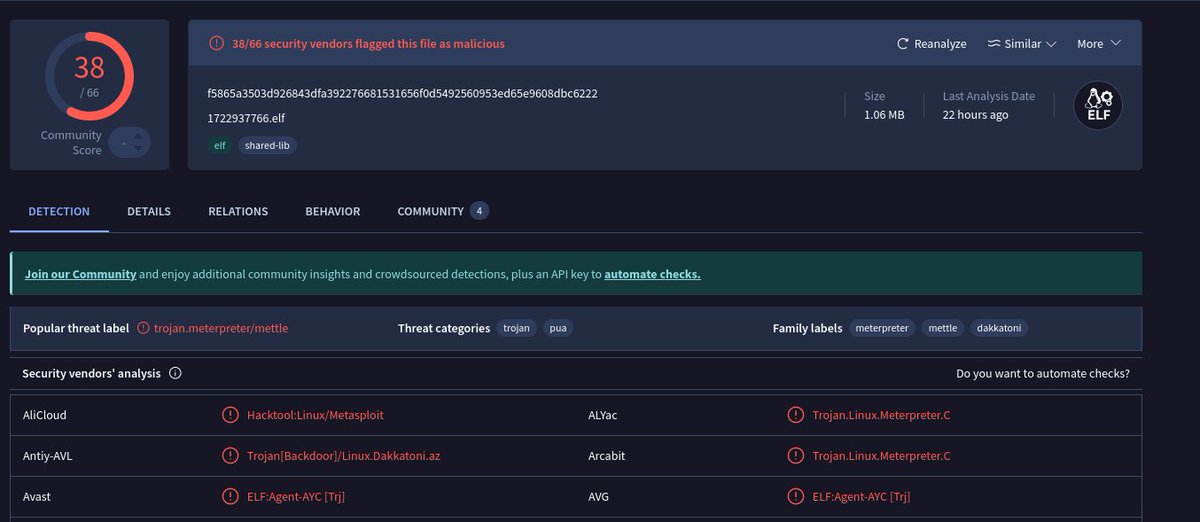
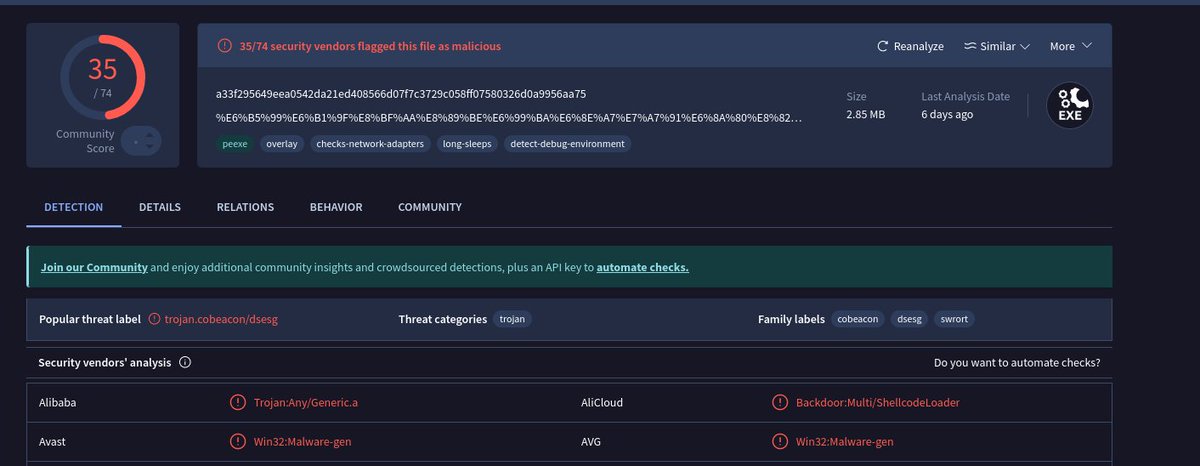
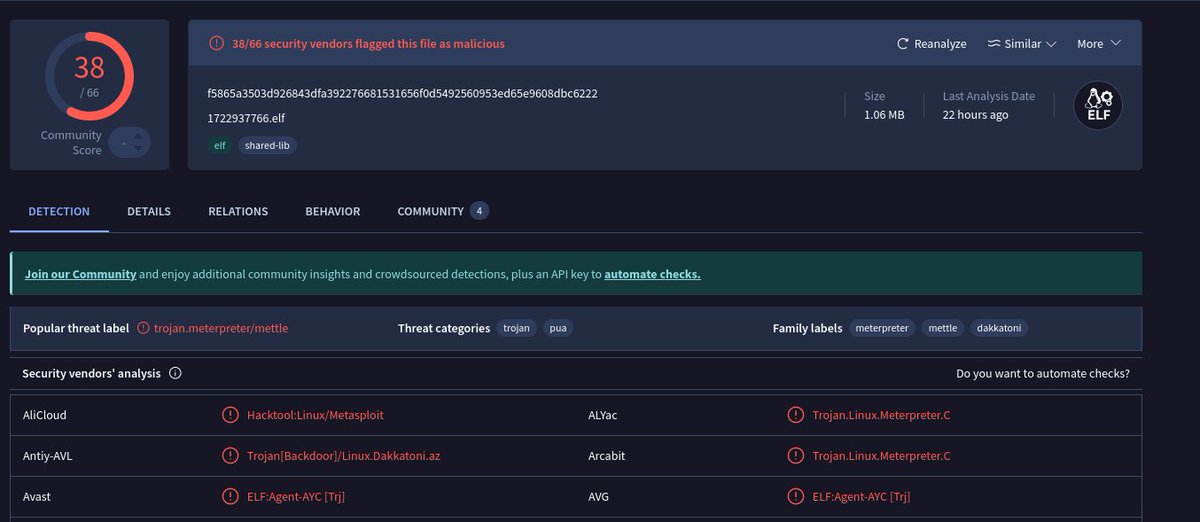
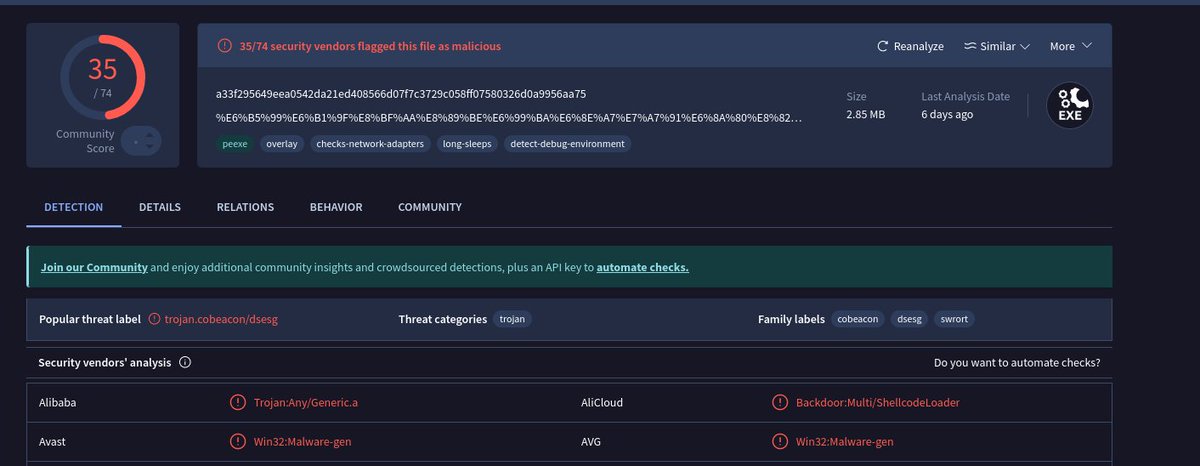
#Malware #Backdoor #Metasploit 💣123.60.104.67:9999💣 - 1722937766.elf - Metasploit C2: 36.138.146.107:8554 - 浙江迪艾智控科技股份有限公司-薪资表.exe - Metasploit C2: hxxp://123.60.104.67:32132/EoDd virustotal.com/gui/file/f5865… virustotal.com/gui/file/a33f2…


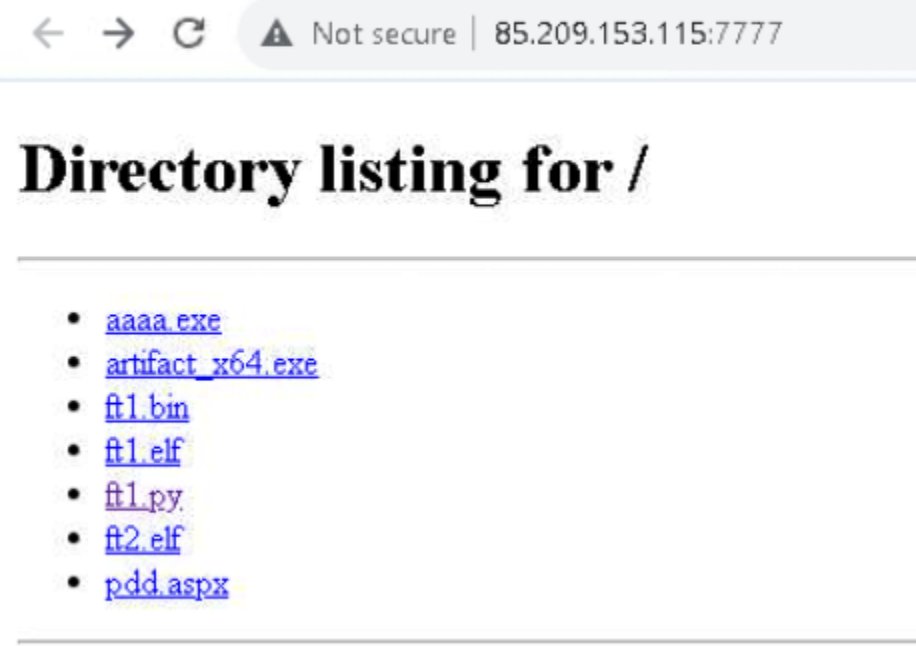
#cobaltstrike and #metasploit spotted on hxxp://85.209.153.115:7777/ VT: virustotal.com/gui/file/61132…

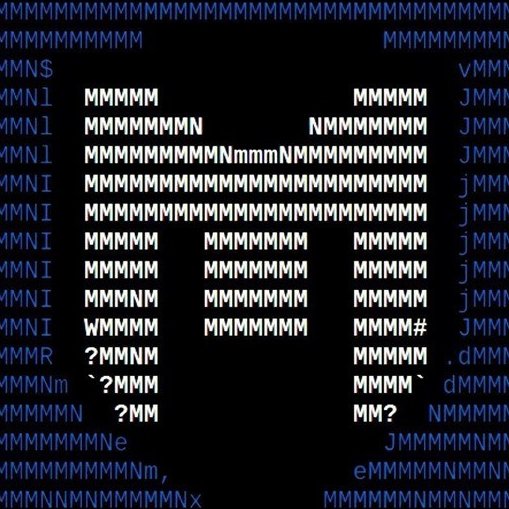
#Metasploit cafc9d45da602fdf794421fc90375024 ab.exe 4237219a330b61e02294897eccfafcd0 test.html 9021c9c1bc08ff874db8e1677f25923c goodfile.iso c2 : 45.76.180.]12 VULTR VPS hosted in Singapore kellington-group.]com - 7days ago Impersonating Kelington Group in #Malaysia @frdfzi
![salmanvsf's tweet image. #Metasploit
cafc9d45da602fdf794421fc90375024 ab.exe
4237219a330b61e02294897eccfafcd0 test.html
9021c9c1bc08ff874db8e1677f25923c goodfile.iso
c2 : 45.76.180.]12 VULTR VPS hosted in Singapore
kellington-group.]com - 7days ago
Impersonating Kelington Group in #Malaysia
@frdfzi](https://pbs.twimg.com/media/G0iq4c8agAAePds.jpg)
🚨#Opendir #Metasploit🚨 hxxp://54.158.34.216/ ☣️lumer.exe 📡54.158.34.216:8080/7Hsk2YaixMw38DbxUNIOiAZX-9aPyK-zT_U2iSasJx9jV9QpI3bF4FGfb_6gogRwb_I5htpqkHcOXW2GC3IVnOreL1LJ36bDtSCPFtK_2_byVOZkZqWrsqvyFf837ZYjEmyn6ni2BWxst55Y5nmdfA8mMvlYE98sHjuB8cPmCC
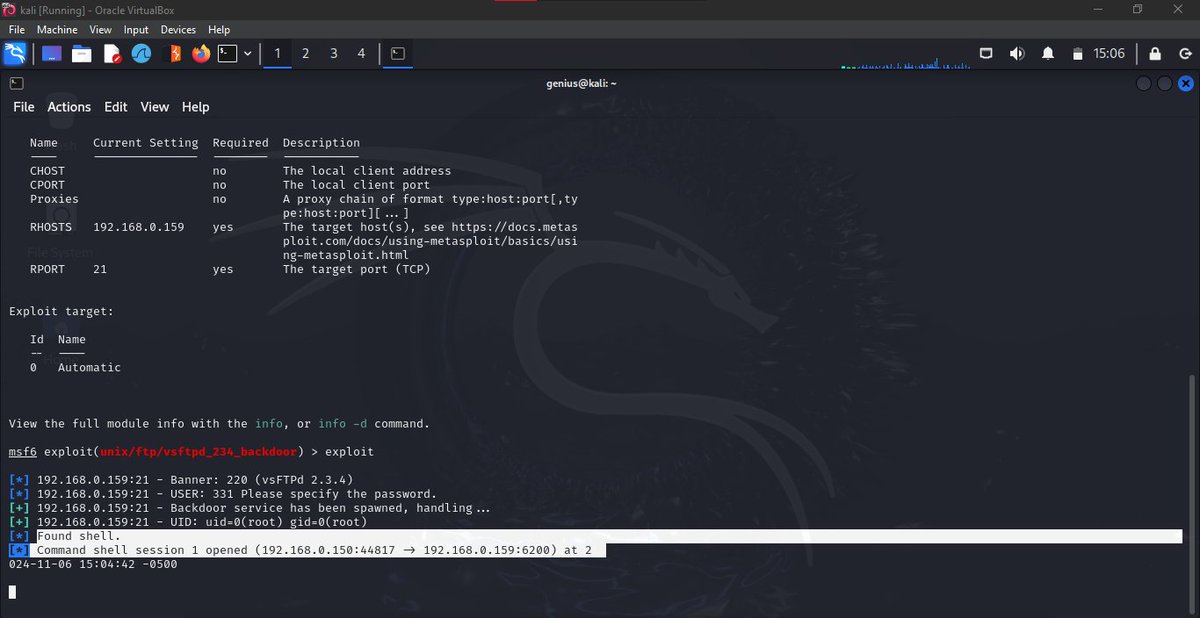
#الامن_السيبراني 🛡️ كيف يتم استغلال البورتات المفتوحة باستخدام #Metasploit 🧑🏻💻.. يجب أن تكون على معرفة بأساسيات الأمان السيبراني، بالإضافة إلى معرفة كيفية استخدام الأدوات بشكل فعال، سأقوم بشرح الخطوات الأساسية لذلك مع مثال عملي 🔥.. تابع 👇🏻

'dbghelp.dll' #metasploit seen from Virgin Islands @abuse_ch bazaar.abuse.ch/sample/f568efd… Domain: is25(.)in

00f0c2f3687ab8bf0990084d1e3af62246005c32084fa598aca1d65bdc0740c9 First Submission 2025-01-14 06:43:14 UTC 51[.]89[.]44[.]68:8848 AS16276 OVH SAS 🇬🇧 5[.]75[.]234[.]8:5050 AS24940 Hetzner Online GmbH 🇩🇪 #AsyncRAT #Metasploit #c2
![skocherhan's tweet image. 00f0c2f3687ab8bf0990084d1e3af62246005c32084fa598aca1d65bdc0740c9
First Submission 2025-01-14 06:43:14 UTC
51[.]89[.]44[.]68:8848
AS16276 OVH SAS 🇬🇧
5[.]75[.]234[.]8:5050
AS24940 Hetzner Online GmbH 🇩🇪
#AsyncRAT #Metasploit #c2](https://pbs.twimg.com/media/Gma6CSia8AA6aEb.png)
⚡ Metasploit Cheatsheet The Metasploit Framework is one of the most widely used platforms for vulnerability validation, security testing, and exploitation research. 🔖 #Metasploit #RedTeam #Pentesting #CyberSecurity #InfoSec #SecurityTesting #DFIR #EthicalHacking
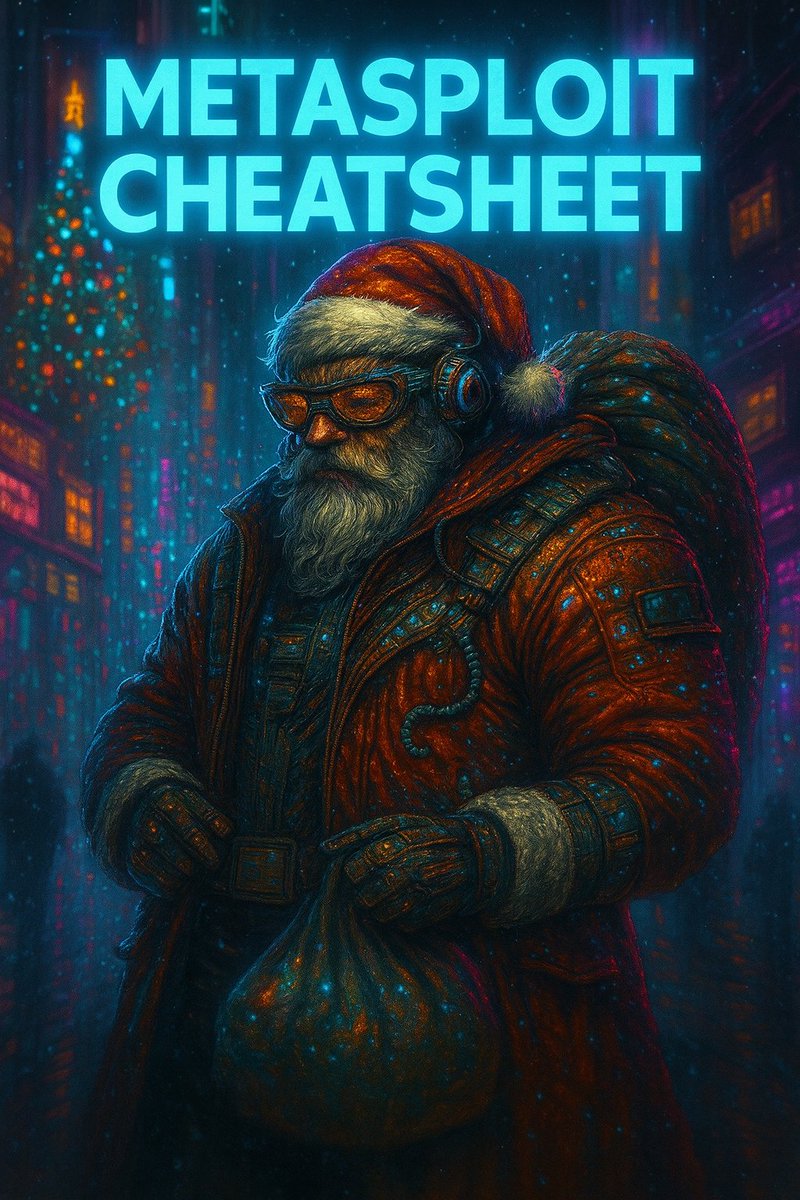

🔐 Day 24/45 — Metasploit Expansion Worked with additional exploit modules and practiced post-exploitation using meterpreter (commands like sysinfo, shell, getuid). Steadily improving my exploitation workflow. #Metasploit #TryHackMe #45DaysChallenge
Metasploit C2s Stats New C2s Found: 1 Current C2s Live: 33 #Metasploit #c2
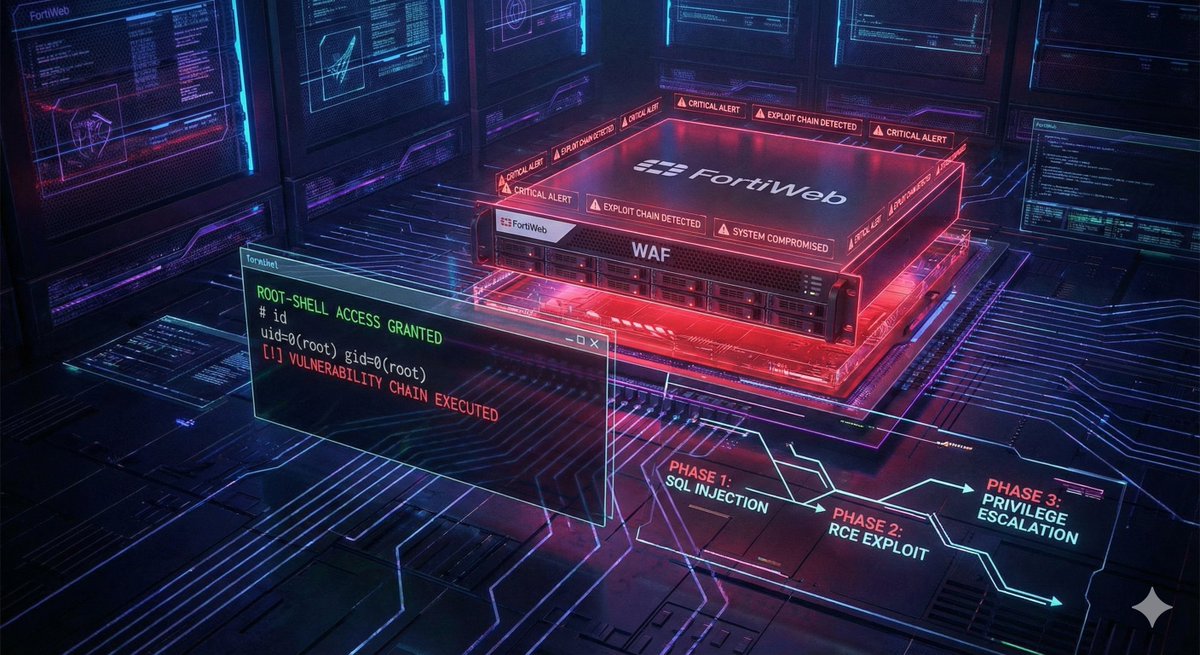
🚨 New #Metasploit module just weaponized two FortiWeb 0-days — CVE-2025-64446 & CVE-2025-58034. Attackers can now go from no auth → full root RCE in seconds. Read More: findsec.org/index.php/blog… #CyberSecurity #Fortinet #Canada #CanadaCyberAwareness
Metasploit C2s Stats New C2s Found: 2 Current C2s Live: 33 #Metasploit #c2
🌐 FortiWeb Fiasco: How a Silent Patch Sparked a #Metasploit RCE Frenzy undercodetesting.com/fortiweb-fiasc… Educational Purposes!
undercodetesting.com
FortiWeb Fiasco: How A Silent Patch Sparked A Metasploit RCE Frenzy - Undercode Testing
FortiWeb Fiasco: How a Silent Patch Sparked a Metasploit RCE Frenzy - "Undercode Testing": Monitor hackers like a pro. Get real-time updates, AI-powered
🚨 #Metasploit Raises Alarm With New FortiWeb Exploit Chain Targeting Critical WAF Flaws undercodenews.com/metasploit-rai…
undercodenews.com
Metasploit Raises Alarm With New FortiWeb Exploit Chain Targeting Critical WAF Flaws - UNDERCODE...
A major red flag has just been raised in the cybersecurity world. Rapid7’s Metasploit Framework has introduced a powerful new exploit module that targets two
Metasploit Releases New Exploit for Fresh FortiWeb 0-Day Vulnerabilities gbhackers.com/metasploit-rel… via @GBHackers Security #cybersecurity #infosec #metasploit #fortinet #fortiweb #zeroday #vulnerability
Day 17 I found misconfigured SMB services, outdated Samba versions, and even a shell that opened simply because of a tiny username-mapping flaw. Then a brute-force demo reminded me that default passwords are still one of the biggest risks. #CyberSecurity #Metasploit
Metasploit C2s Stats New C2s Found: 1 Current C2s Live: 30 #Metasploit #c2
Metasploit C2s Stats New C2s Found: 4 Current C2s Live: 27 #Metasploit #c2
Metasploit Framework Explained: The Ultimate Guide for Beginners! Watch here - youtu.be/CDgNCwJtn_w?si… #metasploit #ethicalhacking #penetrationtesting #cybersecuritytools #infosectrain

youtube.com
YouTube
Metasploit Framework Explained: The Ultimate Guide for Beginners!
Hacking Ético con Metasploit Framework ⏱️ 3.0 hours ⭐ 4.39 👥 34,882 🔄 Nov 2025 💰 $17.99 → 100% OFF comidoc.com/udemy/hacking-… #udemy #EthicalHacking #Metasploit #Pentesting

Metasploit C2s Stats New C2s Found: 1 Current C2s Live: 27 #Metasploit #c2
Looks like a #metasploit from Russia to Russia 😂 @abuse_ch 'finally.ps1' bazaar.abuse.ch/sample/2672a43… IP: 31.130.147(.)55 (RU)

Completed the Metasploitable module! Gained hands on experience using Metasploit Framework to identify, exploit, and analyze system vulnerabilities in a controlled environment. A solid step forward in my ethical hacking & penetration testing journey. #CyberSecurity #Metasploit

Metasploit Found C2 IP: 83[.]147[.]18[.]16:8445 C2 Server: hxxp://83[.]147[.]18[.]16:8445 Country: United Kingdom (AS215311) ASN: REGXA-CLOUD #C2 #metasploit
How skilled are you in cybersecurity? Serious learners will get this one right. Comment the answer below. Then, keep the momentum going with 25+ free cybersecurity courses. Create your free no-obligation CodeRed account today #CyberSecurity #EthicalHacking #Metasploit…


Pentest-Cheat-Sheets A collection of snippets of codes and commands to help our lives! The main purpose is not be a crutch, this is a way to do not waste our precious time! This repo also helps who trying to get OSCP. You'll find many ways to do something without #Metasploit…

تعلم الميتاسبلويت من الصفر للاحتراف مقدمة عن الـ Metasploit bit.ly/3Gmc8qW للحصول على دورة كاملة لشرح الميتاسبلويت : bit.ly/3grf9vp #Metasploit #Infosec4tc

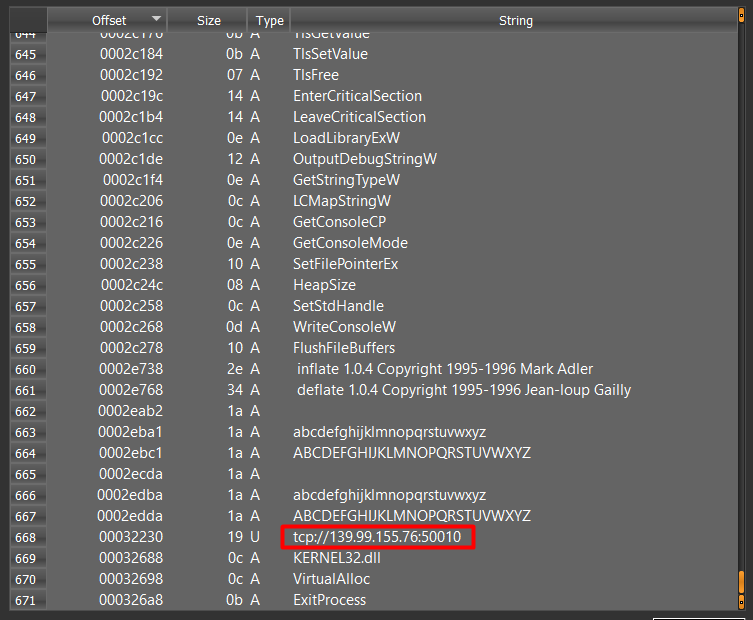
#Metasploit > C2 139.99.155.76:50010 reverse.exe > bazaar.abuse.ch/sample/935d4f8… + Friday #opendir on port 80 🔎

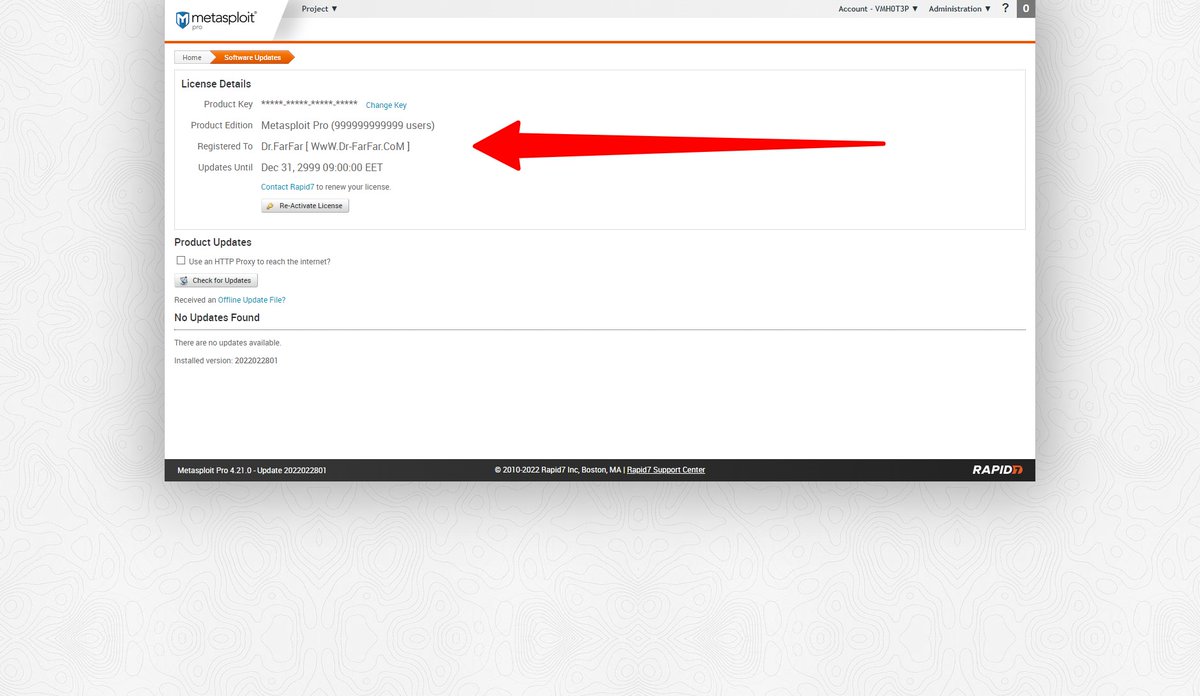
#FREE 2ಠ23 ♥ Metasploit Pro 4.22.0-2023013001 Full Activated - CyberSecurity Tools - Discount 100% OFF Dr-FarFar.CoM Link: t.me/Dr_FarFar_Chan… #Metasploit #HackerOne #Synack #BugCrowd #BugBounty #BugBountyTips #InfoSec #CyberSecurity #100DaysOfCode #Malware #XSS
#opendir #metasploit 💣89.197.154.116💣 Files: - Mile.exe - C2: 89.197.154.116:7810 - Trial.exe - C2: 89.197.154.116:7810 virustotal.com/gui/file/19970… virustotal.com/gui/file/4246f…

#الأمن_السيبراني 🛡️ من الاختراق إلى السيطرة، كشف أسرار وحدات ما بعد الاستغلال المتقدمة في Metasploit 💣☢️.. 🛡️ ما هي وحدات ما بعد الاستغلال (Post-Exploitation Modules)؟ ☠️ هي مكونات برمجية (أدوات أو سكربتات) مدمجة في إطار عمل #Metasploit ،،، تابع 👇🏻

#Metasploit #Malware 💣89.197.154.116💣 Files: Excel.exe - Meterpreter Shell Macro.vbs - Creates and Executes an Exe named uWeBbVRuMcAR.exe (connects to C2) Monitor.exe - Marte Beacon C2:89.197.154.116:7810 app.any.run/tasks/c2eebee7… tria.ge/240908-q53hba1… virustotal.com/gui/file/5e436…


#metasploit being used by this threatactor #Opendir http://103.42.55.251:9999/ virustotal.com/gui/file/4d2ea… virustotal.com/gui/file/7d4dc…

تعلم الميتاسبلويت من الصفر للاحتراف مقدمة عن الـ Metasploit free4arab.net/courses/networ… المحاضر : المهندس حسن سعد ولمتابعة كل كورسات المهندس حسن free4arab.net/instructor/has… خصم على دورة كاملة لشرح الميتاسبلويت bit.ly/3grf9vp #Metasploit #Infosec4tc

#Malware #Backdoor #Metasploit 💣123.60.104.67:9999💣 - 1722937766.elf - Metasploit C2: 36.138.146.107:8554 - 浙江迪艾智控科技股份有限公司-薪资表.exe - Metasploit C2: hxxp://123.60.104.67:32132/EoDd virustotal.com/gui/file/f5865… virustotal.com/gui/file/a33f2…


Metasploit Basics for Hackers, Part 1: Getting Started with Metasploit #metasploit #metasploit4hackers #infosec #cybersecurity #cyberwarrior hackers-arise.com/post/2017/01/2…
24664a5adc23a7df4e6f55e81ca25977d9ef469b066ac39d53a845ea6a4481e7 193[.]161[.]193[.]99:29675 #Metasploit
![skocherhan's tweet image. 24664a5adc23a7df4e6f55e81ca25977d9ef469b066ac39d53a845ea6a4481e7
193[.]161[.]193[.]99:29675
#Metasploit](https://pbs.twimg.com/media/Gmr9xJ9bkAAjtum.jpg)
#الامن_السيبراني 🛡️ كيف يتم استغلال البورتات المفتوحة باستخدام #Metasploit 🧑🏻💻.. يجب أن تكون على معرفة بأساسيات الأمان السيبراني، بالإضافة إلى معرفة كيفية استخدام الأدوات بشكل فعال، سأقوم بشرح الخطوات الأساسية لذلك مع مثال عملي 🔥.. تابع 👇🏻

Metasploit Weekly Wrap-Up rapid7.com/blog/post/2023… #pentesting #Metasploit #cybersecurity #infosec

Fake Kali Linux domain used to spread malware. #metasploit found on the domain urlhaus.abuse.ch/host/tools.kal… #xml #opendir

Something went wrong.
Something went wrong.
United States Trends
- 1. Good Sunday 70.9K posts
- 2. Wirtz 10.4K posts
- 3. Ole Miss 43.2K posts
- 4. #AskFFT N/A
- 5. #sundayvibes 5,308 posts
- 6. Gakpo 9,880 posts
- 7. #MUFC 19.8K posts
- 8. Zirkzee 24.6K posts
- 9. Isak 20.1K posts
- 10. #CRYMUN 9,200 posts
- 11. Vidal 3,682 posts
- 12. Amorim 44.3K posts
- 13. Lane Kiffin 53.5K posts
- 14. Duke 35.2K posts
- 15. Crystal Palace 38.1K posts
- 16. Stockton 32.6K posts
- 17. #EMAnniversaryxWilliamEst 327K posts
- 18. Mason Mount 10.1K posts
- 19. Licha 5,291 posts
- 20. WILLIAMEST AT EMQUARTIER 326K posts













![skocherhan's tweet image. 13[.]50[.]225[.]235
#Metasploit #opendir @Huntio](https://pbs.twimg.com/media/GvOU0a5WcAAXqoK.png)