#exploitkit search results
Firefox RCE from Hack2Win bugzilla.mozilla.org/show_bug.cgi?i… #exploitkit
What is an #ExploitKit? #Wordoftheweek For the definitions to other #IT-related words, visit our encyclopedia 📖: kas.pr/fz27

New #ExploitKit roundup: How malware campaigns are using malvertising and installing banking Trojans on victims' machines. bit.ly/2BXbTn9
After a short hiatus in early January, the Fallout #ExploitKit is back in #business again with some new features for the new year: blog.malwarebytes.com/threat-analysi… by @jeromesegura #cybersecurity #infosec
Improved Fallout #ExploitKit comes back after short hiatus | #Malwarebytes Labs blog.malwarebytes.com/threat-analysi… by @jeromesegura #cybersecurity #infosec #cybersecurityeurope
⛓️RIG Exploit Kit Chain Internals - by @VK_Intel labs.sentinelone.com/reversing-rig-… #RIG #ExploitKit #infosec
Kraken Ransomware Now Being Distributed by Fallout Exploit Kit twi.li/d7LCCb #Ransomware #exploitkit

#Fallout #exploitkit now installing the #KrakenCryptor #ransomware ehackingnews.com/2018/10/fallou… #infosec #malware #cybersecuritymonth

Our researchers discovered a new #ExploitKit named #Underminer that exploits a vulnerability in Internet Explorer and 2 security flaws in Adobe Flash Player. Report: bit.ly/2OijbCT
An #exploitkit such as #Rig usually starts off with a threat actor compromising a website to inject a malicious script/code that eventually redirects would-be victims to the exploit kit’s landing page. bit.ly/2xJnO5z via @TrendLabs

#ExploitKit #vulnerability #cybercrime #CyberSecurity #virtualpatching come proteggi i tuoi sistemi fuori patch? trendmicro.com/it_it/business…
NEW #threatspotlight: read about #GrandSoft, an 8 year old #exploitkit back in action and serving up #cryptomining malware: bit.ly/2q5CiGj
Active #malvertising campaigns in December and the new year have kept #exploitkit activity from hibernating in winter 2019. Read our full review of the major exploit kits causing havoc: blog.malwarebytes.com/threat-analysi…. by @jeromesegura #cybersecurit #infosec #cybersecurityeurope
A great report has been published by @jeromesegura from @Malwarebytes . We also published our analysis to the #ShadowGate campaign and Greenflash Sundown exploit kit activity we worked on since last week. @TrendMicroRSRCH #exploitkit
New post: Shadowgate Returns to Worldwide Operations With Evolved Greenflash Sundown Exploit Kit bit.ly/2ISiyzN @TrendMicroRSRCH
Cybersecurity researchers have discovered a very sophisticated #ExploitKit that is targeting countries in the Asia-Pacific region to deliver ransomware via #advertising. …ndequity.economictimes.indiatimes.com/news/digital/n…
A new exploit kit, called Capesand, is being actively used in attacks while still under development. The kit reuses old and new shared-exploits #capesand #exploitkit #infosec #tools #cybersecurity blog.trendmicro.com/trendlabs-secu…
#ThreatProtection #RIG #ExploitKit delivers #WastedLoader malware, read more: broadcom.com/support/securi…

WarZone Desktop Exploit Kit (Early Alpha) DEMO youtu.be/Sjr1Udjg-Po via @YouTube #exploit #exploitkit #malware #sploit #ie #demo #alpha

youtube.com
YouTube
Claes
#ExploitKit, #FalloutExploitKit, #Hackers, #InformationStealer, #RigExploitKit, #Malware, #CyberAttack, #CyberSecurity Russian Hackers Compromised 100,000+ Computers Using Raccoon Malware Via Fallout & RIG Exploit Kits. cybereason.com/blog/hunting-r… gbhackers.com/raccoon-malwar…


Vladimirovich Tarasov built the Angler Exploit Kit. Likhogray Maxim Alexandrovich bought network access. #CyberSecurity #ExploitKit
🔐 @kaspersky Links Coruna Exploit Kit to Triangulation Framework 🔗 Read more: bit.ly/41hMcGp #Kaspersky #CyberThreats #ExploitKit #CyberSecurity #ThreatIntelligence #SecurityResearch

Coruna IOS Kit Reuses 2023 Exploit Code Read More: buff.ly/R5RiVuH #Coruna #iOSSecurity #ExploitKit #MobileSecurity #SpywareThreat #OperationTriangulation #ZeroDay #ThreatIntel
CISA orders U.S. federal agencies to patch three iOS vulnerabilities exploited by DarkSword, targeting iOS 18.4–18.7 with sandbox escapes, privilege escalation, and remote code execution. #DarkSword #ExploitKit #USA ift.tt/WUMgKwP
Darksword Ios Kit Uses 3 Zero-Days Read More: buff.ly/rBqNXNR #DarkSword #iOSZeroDay #ExploitKit #MobileSecurity #SpywareThreat #CredentialTheft #CryptoTheft #AppleSecurity
New DarkSword iOS exploit kit leveraging 6 flaws is being actively used by threat actors. Apply patches ASAP! #Cybersecurity #InfoSec #ExploitKit thehackernews.com/2026/03/darksw…
DarkSword: Researchers uncover another iOS exploit kit - helpnetsecurity.com/2026/03/19/dar… - @Google @Lookout @IsMyPhoneHacked #CyberEspionage #DataTheft #ExploitKit #iPhone #iOS #Cybersecurity #CybersecurityNews
New DarkSword iOS exploit kit leveraging 6 vulnerabilities is actively used. Apple urges patching for CVE-2026-20131. #Cybersecurity #InfoSec #ExploitKit thehackernews.com/2026/03/darksw…
Unusual browser or plugin behavior Early detection prevents drive-by infections and automated compromise. #ExploitKit #BrowserAttacks #SOCDetection #VulnerabilityExploitation #CyberDefense #scorpion_drogon
Exploit kits target your software's weak spots. Keep everything patched to stay protected. Is your software up-to-date? #ExploitKit #InfoSecurity $AIMASTER
Seit 2015 gesucht: Mutmaßlicher #Ransomware-Pionier verhaftet und ausgeliefert #ExploitKit #Festnahme #Polizei glm.io/188000?s
#PurpleFox #ExploitKit #EK Is still a thing. #pcap #IOC #TTP oernatel[.]shop GET /index.php?key=128744493849 - Redirect to PurpleFox EK gcoholrger.idsotbedine[.]site - PurpleFox EK github.com/firstwatchcybe…
![FirstWatchCyber's tweet image. #PurpleFox #ExploitKit #EK Is still a thing. #pcap #IOC #TTP
oernatel[.]shop GET /index.php?key=128744493849 - Redirect to PurpleFox EK
gcoholrger.idsotbedine[.]site - PurpleFox EK
github.com/firstwatchcybe…](https://pbs.twimg.com/media/F3Q0o86XsAY17pF.jpg)
![FirstWatchCyber's tweet image. #PurpleFox #ExploitKit #EK Is still a thing. #pcap #IOC #TTP
oernatel[.]shop GET /index.php?key=128744493849 - Redirect to PurpleFox EK
gcoholrger.idsotbedine[.]site - PurpleFox EK
github.com/firstwatchcybe…](https://pbs.twimg.com/media/F3Q05hOW8AE_Ohu.jpg)
![FirstWatchCyber's tweet image. #PurpleFox #ExploitKit #EK Is still a thing. #pcap #IOC #TTP
oernatel[.]shop GET /index.php?key=128744493849 - Redirect to PurpleFox EK
gcoholrger.idsotbedine[.]site - PurpleFox EK
github.com/firstwatchcybe…](https://pbs.twimg.com/media/F3Q074JWYAAxw0M.jpg)
. Whoa, looks like the RIG exploit kit is still going strong with an all-time high successful exploitation rate of nearly 30%! Time to double-check those security protocols! #CyberSecurity #ExploitKit thehackernews.com/2023/02/resear…
thehackernews.com
Researchers Share New Insights Into RIG Exploit Kit Malware's Operations
Researchers have uncovered crucial insights into the inner workings of RIG Exploit Kit and its administrators.
Still running Internet Explorer? Researchers have discovered a new malware campaign that uses an attack method that has fallen out of favour in recent months, called the Exploit Kit. Read more on this in the linked article below. #redline #exploitkit links.nuageit.ca/3Ntj062
Still running Internet Explorer? Researchers have discovered a new malware campaign that uses an attack method that has fallen out of favour in recent months, called the Exploit Kit. Read more on this in the linked article below. #redline #exploitkit links.nuageit.ca/3Ntj062
#RIG #ExploitKit drops #RedLine malware via Internet Explorer bug bleepingcomputer.com/news/security/…
The #Rig #ExploitKit has been seen actively exploiting CVE-2018-8174 to deliver a #cryptocurrency-mining #malware. Its infection chain detailed: bit.ly/2H94PAw

Our researchers discovered a new #ExploitKit named #Underminer that exploits a vulnerability in Internet Explorer and 2 security flaws in Adobe Flash Player. Report: bit.ly/2LoV7kw

What is an #ExploitKit? #Wordoftheweek For the definitions to other #IT-related words, visit our encyclopedia 📖: kas.pr/fz27

#Fallout #exploitkit now installing the #KrakenCryptor #ransomware ehackingnews.com/2018/10/fallou… #infosec #malware #cybersecuritymonth

#CyberSecurity #exploitkit To the attention of Internet Explorer users: the browser has been targeted by Purple Fox and Magnitude Exploit Kits. Learn more here: sensorstechforum.com/cve-2020-0674-…

An #exploitkit such as #Rig usually starts off with a threat actor compromising a website to inject a malicious script/code that eventually redirects would-be victims to the exploit kit’s landing page. bit.ly/2xJnO5z via @TrendLabs

Kraken Ransomware Now Being Distributed by Fallout Exploit Kit twi.li/d7LCCb #Ransomware #exploitkit

This week, learn about the span of categories for @TrendMicro’s 2019 Security Predictions. Also, learn about a new #exploitkit that targets home or small office routers which attacks victim’s mobile device or desktop through web applications. bit.ly/2UKtx2j

This week, learn about the span of categories for @TrendMicro’s 2019 Security Predictions. Also, learn about a new #exploitkit that targets home or small office routers which attacks victim’s mobile device or desktop through web applications. bit.ly/2UKtx2j

NEW #threatspotlight: read about #GrandSoft, an 8 year old #exploitkit back in action and serving up #cryptomining malware: bit.ly/2q5CiGj
New Lord #exploitkit is spreading 'Eric' #ransomware, according to Malwarebytes buff.ly/2YJCoGm via @computing_news #informedsecurity

#ExploitKit #ransomware Magnitude EK Is Now Using CVE-2019-1367 to Drop Ransomware ow.ly/1kNQ50AgGqZ

#ExploitKit, #FalloutExploitKit, #Hackers, #InformationStealer, #RigExploitKit, #Malware, #CyberAttack, #CyberSecurity Russian Hackers Compromised 100,000+ Computers Using Raccoon Malware Via Fallout & RIG Exploit Kits. cybereason.com/blog/hunting-r… gbhackers.com/raccoon-malwar…


[BLOG] 👁🗨 Read how threat actors execute #phishing 🎣 attacks. buff.ly/2xw15q3 #Exploit #ExploitKit #ExploitDownload #PhishingWebsite #PhishingInfrastructure #Security
![Area1Security's tweet image. [BLOG] 👁🗨 Read how threat actors execute #phishing 🎣 attacks. buff.ly/2xw15q3 #Exploit #ExploitKit #ExploitDownload #PhishingWebsite #PhishingInfrastructure #Security](https://pbs.twimg.com/media/DnfCQ5fV4AAT2jX.jpg)
#Hacking #ExploitKit #InternetExplorer #RedLine #RIG #Vulnerability #Malware #CyberCrime #CyberAttack #CyberSecurity RIG Exploit Kit drops RedLine malware via Internet Explorer bug. bleepingcomputer.com/news/security/…

The malvertisements delivering the Princess Evolution #ransomware also include #Coinhive — possibly as a way to make a profit even if users aren’t redirected to the #ExploitKit. Our report: bit.ly/2MzR9lH - #CyberSecurity #Security #CyberAttack…

The new #ExploitKit we named #Novidade can allow attackers to execute pharming attacks. Here’s what we’ve learned: bit.ly/2G9hvMv - #CyberSecurity #Security #CyberAttacks #TrendMicro

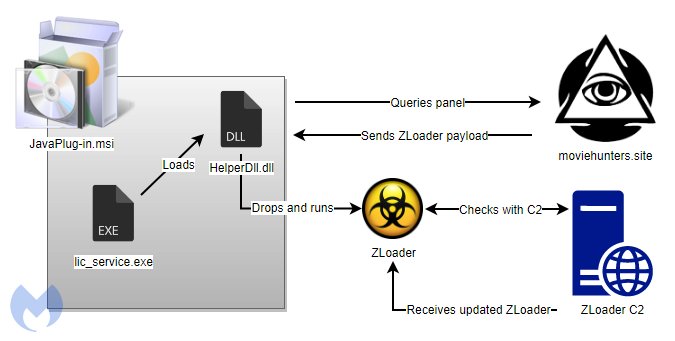
#Hacking #ExploitKit #SmokeLoader #Malware #Vulnerability #CyberCrime #CyberAttack #CyberSecurity Adult site users targeted with ZLoader malware via fake Java update. blog.malwarebytes.com/threat-analysi…
Something went wrong.
Something went wrong.
United States Trends
- 1. Jokic N/A
- 2. Knicks N/A
- 3. Tony Brothers N/A
- 4. #WWERaw N/A
- 5. Rudy Gobert N/A
- 6. Brunson N/A
- 7. Wolves N/A
- 8. Wolves N/A
- 9. Mike Brown N/A
- 10. CJ McCollum N/A
- 11. Braun N/A
- 12. Hawks N/A
- 13. #TexasHockey N/A
- 14. Donte N/A
- 15. Mikal Bridges N/A
- 16. Aaron Gordon N/A
- 17. #bucciovertimechallenge N/A
- 18. Naz Reid N/A
- 19. Anthony Edwards N/A
- 20. Foligno N/A