#injectionattacks search results
You won't want to keep this doctor away 💉 A new module is available on #HTBAcademy to teach you how to exploit and prevent #injectionattacks like: ✅ XPath injection ✅ LDAP injection ✅ HTML injection in PDF generation libraries Start now: fal.cn/3yco9 #HackTheBox

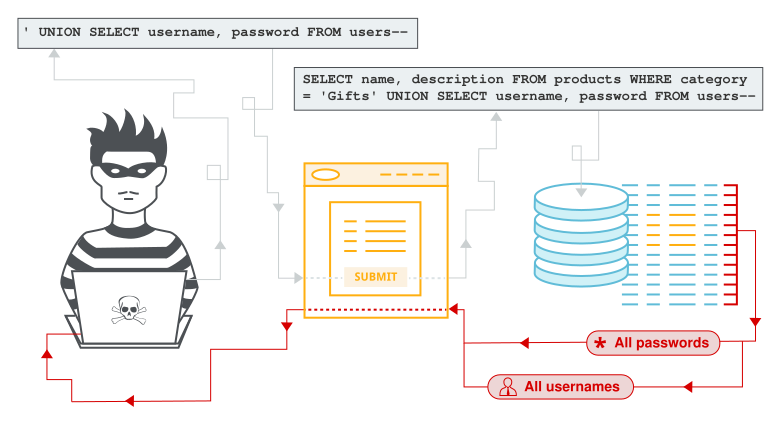
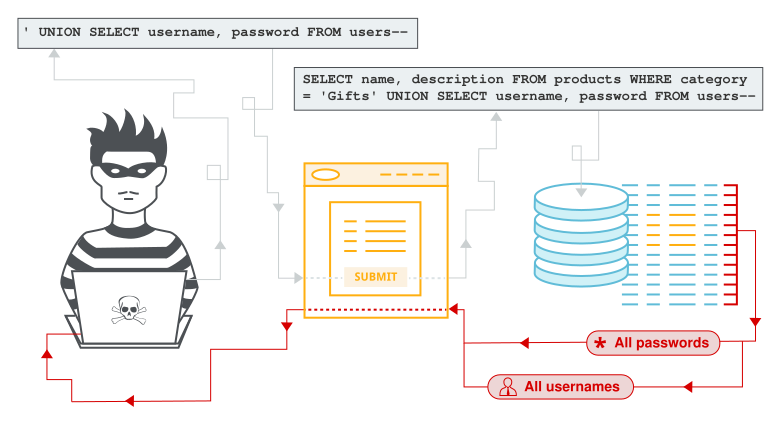
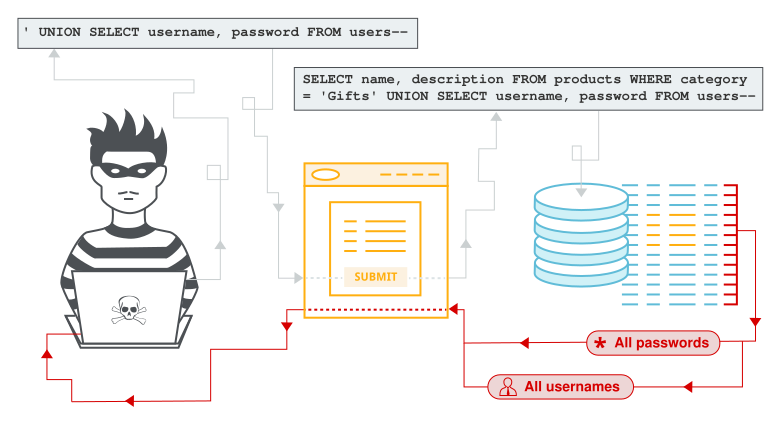
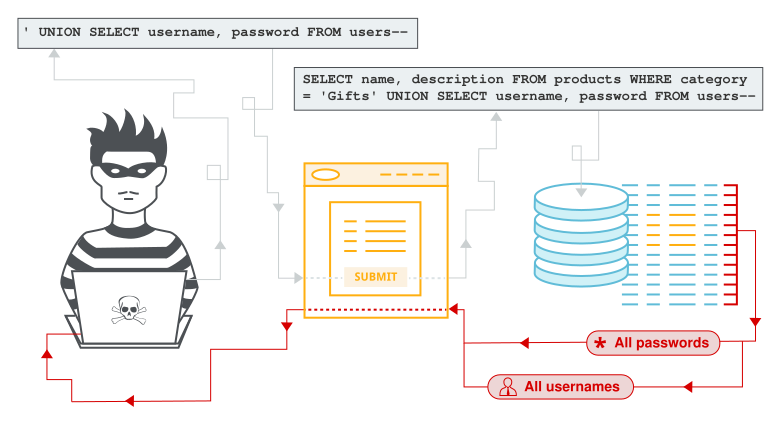
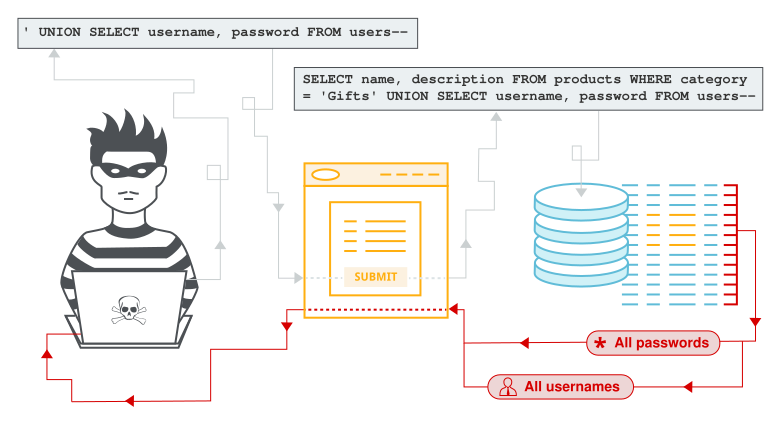
SQL Injection Payload List j.mp/2D5YVkd #InjectionAttacks #InjectionPayloads #SQLInject #SQLInjection #SQLInjectionAttack
[Webinar] 👩💻 Join us on the 8th Sep for How to Secure Your Applications Against #API Attacks. We will explore topics such as #injectionattacks and #deserialization. Secure your space today > bit.ly/3A7NarE
![InfosecurityMag's tweet image. [Webinar] 👩💻 Join us on the 8th Sep for How to Secure Your Applications Against #API Attacks. We will explore topics such as #injectionattacks and #deserialization. Secure your space today > bit.ly/3A7NarE](https://pbs.twimg.com/media/FaXJiHoXoAc-FF8.jpg)
earmas.ga - Pown-Duct - Essential Tool For Finding Blind Injection Attacks j.mp/2YagdZA #InjectionAttacks #Linux #PownDuct #Resolver #SSRF

HBSQLI - Automated Tool For Testing Header Based Blind SQL Injection dlvr.it/SynCXr #HBSQLI #InjectionAttacks #Payload #PenetrationTesting
Beyond Deepfakes: Why Injection Attacks Are the Next Major Threat Read more: financialit.net/news/cybersecu… @Jumio #CyberThreats #InjectionAttacks #CybersecurityTrends #finance #fintech #FinancialIT
Vote begins on biometric injection attack standard @ClrLabs director explains the detail and stakes in EAB presentation @euro_biometrics #biometrics #liveness #injectionattacks biometricupdate.com/202406/vote-be…
biometricupdate.com
Vote begins on biometric injection attack standard | Biometric Update
CLR Labs Director Kévin Carta recently presented the problem and the progress towards the finalization of the prTS 18099 standard to EAB members.
Server Side Template Injection Payloads j.mp/3gpEaSe #CodeSecurity #InjectionAttacks #Payload #Payloads #RemoteCodeExecution
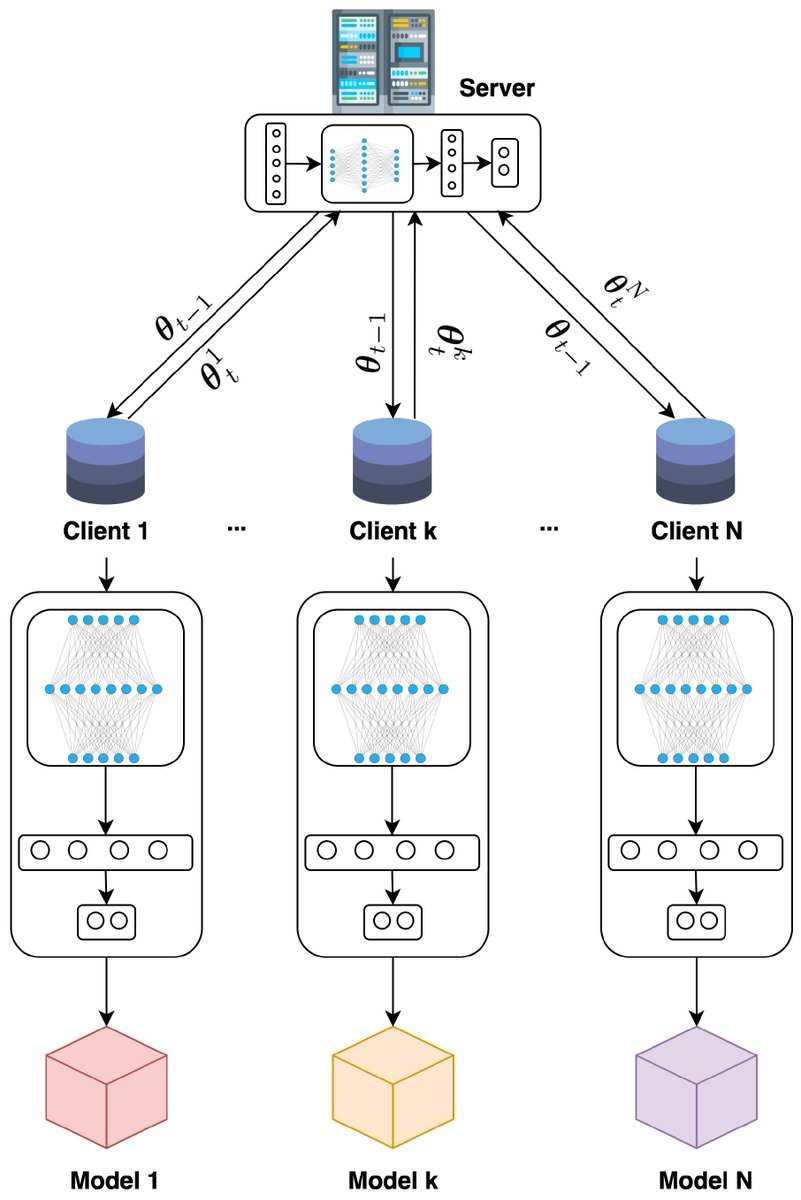
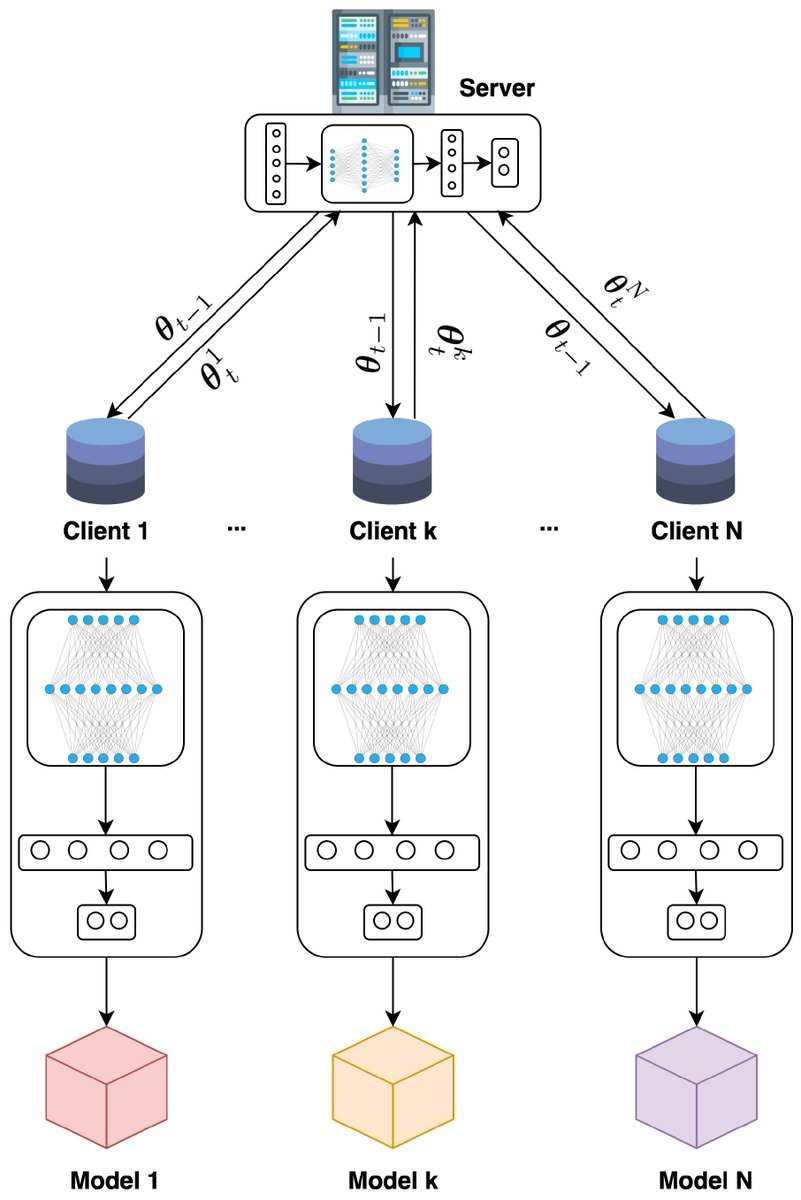
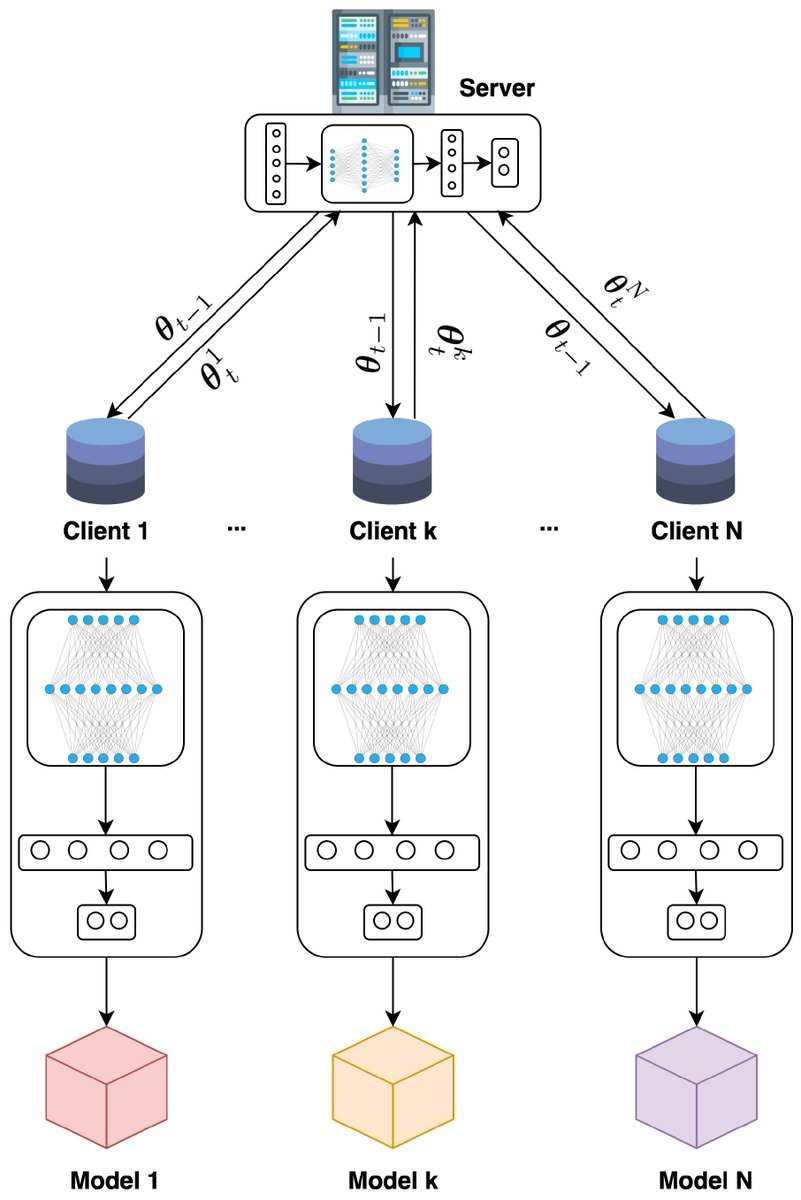
🔥 Read our Highly Cited Paper 📚 CANPerFL: Improve In-Vehicle Intrusion Detection Performance by Sharing Knowledge 🔗 mdpi.com/2076-3417/13/1… 👨🔬 by Nu Thien Hoang et al. #controllerareanetworks #injectionattacks
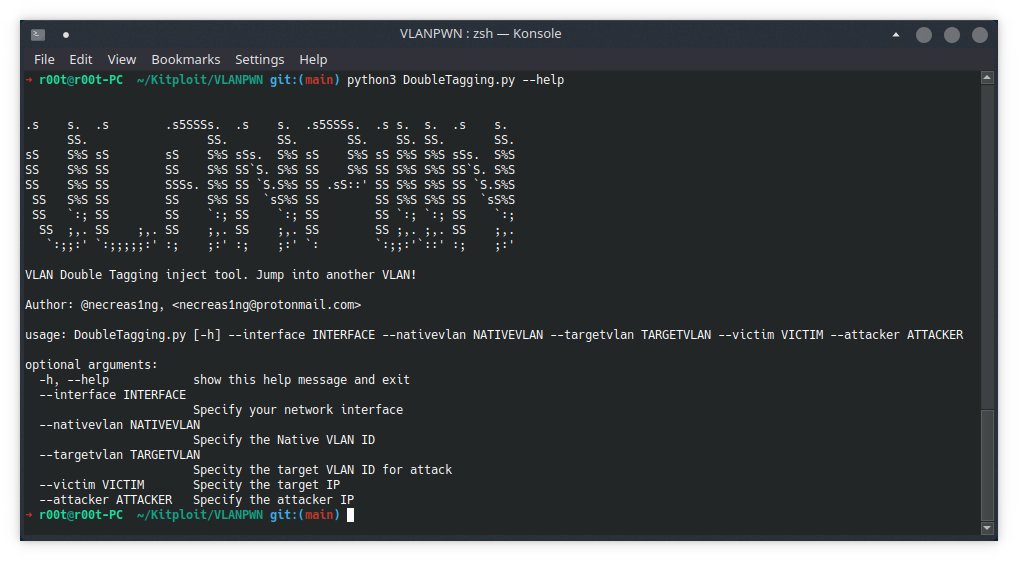
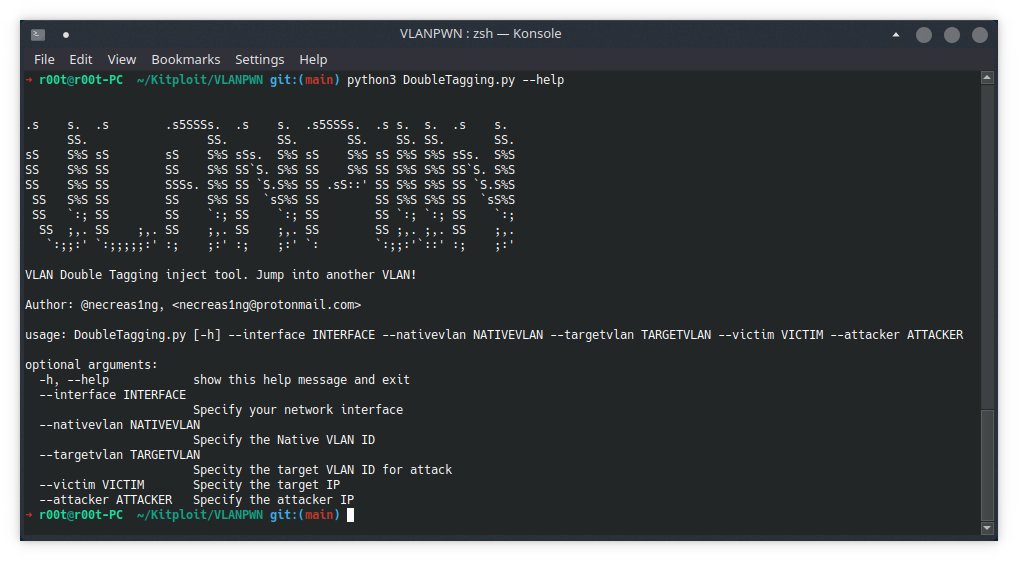
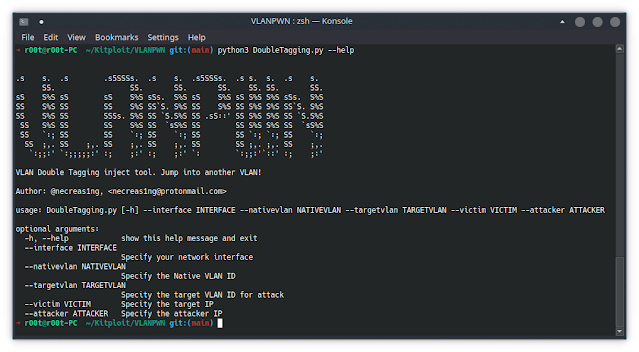
VLANPWN - VLAN Attacks Toolkit bit.ly/3wjcxol #Doubletagging #InjectionAttacks #Vlanhopping #VLANPWN
Pown-Duct - Essential Tool For Finding Blind Injection Attacks j.mp/2YagdZA #InjectionAttacks #Linux #PownDuct #Resolver #SSRF

earmas.ga - SQL Injection Payload List j.mp/2D5YVkd #InjectionAttacks #InjectionPayloads #SQLInject #SQLInjection #SQLInjectionAttack
Digital #injectionattacks are on the rise. The iProov Biometric Encyclopedia explains what they are and how face biometric #authentication can protect against them: bit.ly/3ZvCuhb
What Are The 10 Most Dangerous Injection Attacks? Details: cybersecuritynews.com/injection-atta… #Injectionattacks
Our report explores the rising #deepfake threat in Latin America - covering the rapidly evolving and scalable digital #injectionattacks, how #cybercriminals exploit face verification, and how banks can protect themselves against the threat: bit.ly/3IQli08

How to secure APIs from injection attacks? 🛡️ Explore the best practices to protect APIs, prevent SQL injections & safeguard data. Learn how to fortify your APIs against common vulnerabilities! zurl.co/3D57 #APISecurity #InjectionAttacks #Cybersecurity #InstaSafe
instasafe.com
How to Secure APIs from SQL Injection and Other Attacks | InstaSafe
Discover how to protect APIs from injection attacks like SQL Injection, Command Injection, and XSS. Learn key prevention techniques like input validation, parameterised queries, and API gateways.
Worried about #deepfakes? The iProov report covers research into the rapidly evolving and scalable digital #injectionattacks - find out the solution in our new report:
earmas.ga - Server Side Template Injection Payloads j.mp/3gpEaSe #CodeSecurity #InjectionAttacks #Payload #Payloads #RemoteCodeExecution #earmas
#WordPress Fixes #SecurityFlaw that Opened Users to Content #InjectionAttacks ht.ly/yud6308Edqa
Your face is no longer your password. In 2026, it's just "data" and data can be faked. New "Injection Attacks" bypass 30% of biometric systems. Pelican doesn't check your pixels; we check your hardware-bound cryptographic proof. 🛡️💻 #Deepfakes #CyberSecurity #InjectionAttacks
Injection is back and broader than ever. From SQL to GraphQL to prompt injection, APIs expand the surface. Quick read with practical mitigations. downloads.wallarm.com/4mSs71v #APISecurity #InjectionAttacks #AIsecurity #Cybersecurity #DevSecOps
#security concerns with the use of input() in #Python are: - #InjectionAttacks - #Denial of Service (#DoS) - #Insecure Deserialization Python Code Audit finds #vulnerabilities in #Python code: github.com/nocomplexity/c… #appsec #infosec #owasp #CyberSecurity #oss #opensource
Beyond Deepfakes: Why Injection Attacks Are the Next Major Threat Read more: financialit.net/news/cybersecu… @Jumio #CyberThreats #InjectionAttacks #CybersecurityTrends #finance #fintech #FinancialIT
8️⃣ Why Stored Procedures Aren’t Always Safe Even parameterized stored procedures can be vulnerable if: ❌ Queries are concatenated inside ❌ EXECUTE IMMEDIATE is used Safe APIs & ORM tools are better choices! #CyberSecurity #InjectionAttacks
3️⃣ Why Injection Is Dangerous If user-supplied data isn’t validated or sanitized, attackers can: 🔻 Extract sensitive data 🔻 Modify or delete records 🔻 Take over entire systems Don't trust input—always validate & escape! #AppSec #InjectionAttacks
#TrustedPartner │ Biometric solution providers must improve their liveness detection systems to prevent #deepfake and #injectionattacks. Fime can help you to ensure the #security of your #biometrics solution. Contact us ▶️ [email protected] Learn more ▶️ bit.ly/3UbTmIR
🚨 Understanding Web Application Injection Attacks 🚨 Injection attacks are among the most dangerous vulnerabilities in web applications. 🔗 Read the full blog: buff.ly/4gLYLj4 #WebSecurity #InjectionAttacks #CyberSecurity #OWASP #PenetrationTesting #BugV #AppSecurity
Learn about the top 5 injection attacks that threaten your systems and how they can lead to serious breaches. 💥Explore essential prevention techniques to fortify your applications and keep secure. modshieldsb.com/top-5-injectio… #InjectionAttacks

🔥 Read our Highly Cited Paper 📚 CANPerFL: Improve In-Vehicle Intrusion Detection Performance by Sharing Knowledge 🔗 mdpi.com/2076-3417/13/1… 👨🔬 by Nu Thien Hoang et al. #controllerareanetworks #injectionattacks
#TrustedPartner │ Biometric solution providers must improve their liveness detection systems to prevent #deepfake and #injectionattacks. Fime can help you to ensure the #security of your #biometrics solution. Contact us ▶️ [email protected] Learn more▶️ bit.ly/3UbTmIR
What is Injection and Jailbreak Attacks in the world of LLMs dlvr.it/TFG9cf #InjectionAttacks #JailbreakAttacks #LLMs #ChatGPT #Gemini
generativeai.pub
What is Injection and Jailbreak Attacks in the world of LLMs
The rise of Large Language Models (LLMs) like ChatGPT and Gemini has ushered in a new era of technological advancement, enabling us to…
How to secure APIs from injection attacks? 🛡️ Explore the best practices to protect APIs, prevent SQL injections & safeguard data. Learn how to fortify your APIs against common vulnerabilities! zurl.co/3D57 #APISecurity #InjectionAttacks #Cybersecurity #InstaSafe
instasafe.com
How to Secure APIs from SQL Injection and Other Attacks | InstaSafe
Discover how to protect APIs from injection attacks like SQL Injection, Command Injection, and XSS. Learn key prevention techniques like input validation, parameterised queries, and API gateways.
New research reveals that eight #Microsoft apps for #macOS are vulnerable to library #injectionattacks, which could let attackers steal app permissions and access sensitive data. Here are the impacted apps and CVEs. bit.ly/3X8wo7k
A03:2021 - Injection Attacks 💉#Injectionattacks #SQLInjection #CommandInjection #CodeInjection #Injectionvulnerability #PreventingInjection #Injectionmitigation #Securecodingpractice #OWASPInjection #SQLInjectionprevention #CommandInjectionprotection 👇 youtu.be/nJIizqNRhMg
youtube.com
YouTube
What is A03 - 2021 Injection? #Injectionattacks #owasptop10
🔒 OWASP Top 10: Injection Attacks 🚨 Stay secure! #CyberSecurity #OWASP #InjectionAttacks #OWASPInjection #SQLInjectionattack #PreventSQLInjection #Injectionvulnerability #CommandInjection #Injectionsecurityrisk #Webappsecurity 👇 youtu.be/GD66mri7VR8
youtube.com
YouTube
OWASP Top 10 - 2017 : Injection Vulnerability #owasptop10 #OWASPInj...
We're thrilled to unveil our latest innovation: an AI-powered solution designed to defend against Deep Fakes and Injection Attacks. 💡🔒 👉 𝗟𝗲𝗮𝗿𝗻 𝗺𝗼𝗿𝗲: investors.truststamp.ai/press-release?… #injectionattacks #deepfake #technology #innovation #DeepFakeAwareness

Vote begins on biometric injection attack standard @ClrLabs director explains the detail and stakes in EAB presentation @euro_biometrics #biometrics #liveness #injectionattacks biometricupdate.com/202406/vote-be…
biometricupdate.com
Vote begins on biometric injection attack standard | Biometric Update
CLR Labs Director Kévin Carta recently presented the problem and the progress towards the finalization of the prTS 18099 standard to EAB members.

You won't want to keep this doctor away 💉 A new module is available on #HTBAcademy to teach you how to exploit and prevent #injectionattacks like: ✅ XPath injection ✅ LDAP injection ✅ HTML injection in PDF generation libraries Start now: fal.cn/3yco9 #HackTheBox

SQL Injection Payload List j.mp/2D5YVkd #InjectionAttacks #InjectionPayloads #SQLInject #SQLInjection #SQLInjectionAttack
Server Side Template Injection Payloads j.mp/3gpEaSe #CodeSecurity #InjectionAttacks #Payload #Payloads #RemoteCodeExecution
[Webinar] 👩💻 Join us on the 8th Sep for How to Secure Your Applications Against #API Attacks. We will explore topics such as #injectionattacks and #deserialization. Secure your space today > bit.ly/3A7NarE
![InfosecurityMag's tweet image. [Webinar] 👩💻 Join us on the 8th Sep for How to Secure Your Applications Against #API Attacks. We will explore topics such as #injectionattacks and #deserialization. Secure your space today > bit.ly/3A7NarE](https://pbs.twimg.com/media/FaXJiHoXoAc-FF8.jpg)
VLANPWN - VLAN Attacks Toolkit bit.ly/3wjcxol #Doubletagging #InjectionAttacks #Vlanhopping #VLANPWN
🔥 Read our Highly Cited Paper 📚 CANPerFL: Improve In-Vehicle Intrusion Detection Performance by Sharing Knowledge 🔗 mdpi.com/2076-3417/13/1… 👨🔬 by Nu Thien Hoang et al. #controllerareanetworks #injectionattacks
Pown-Duct - Essential Tool For Finding Blind Injection Attacks j.mp/2YagdZA #InjectionAttacks #Linux #PownDuct #Resolver #SSRF

earmas.ga - SQL Injection Payload List j.mp/2D5YVkd #InjectionAttacks #InjectionPayloads #SQLInject #SQLInjection #SQLInjectionAttack
#SaltLabs found that nearly every organization using #Elastic Stack is affected by a new vulnerability, which makes users susceptible to #injectionattacks that could result in #denialofservice (#DoS) events. securitymagazine.com/articles/96222… #cybersecurity #security
Our report explores the rising #deepfake threat in Latin America - covering the rapidly evolving and scalable digital #injectionattacks, how #cybercriminals exploit face verification, and how banks can protect themselves against the threat: bit.ly/3IQli08

earmas.ga - Pown-Duct - Essential Tool For Finding Blind Injection Attacks j.mp/2YagdZA #InjectionAttacks #Linux #PownDuct #Resolver #SSRF

earmas.ga - Server Side Template Injection Payloads j.mp/3gpEaSe #CodeSecurity #InjectionAttacks #Payload #Payloads #RemoteCodeExecution #earmas
Digital #injectionattacks are on the rise. The iProov Biometric Encyclopedia explains what they are and how face biometric #authentication can protect against them: bit.ly/3ZvCuhb
VLANPWN - VLAN Attacks Toolkit dlvr.it/SWkNnS #Doubletagging #InjectionAttacks #Vlanhopping #VLANPWN via KitPloit
👉 #NoSQL #InjectionAttacks may lead to data breaches, system compromise, and reputational damage. Stay proactive, fortify your defenses, and ensure business resilience: (Link in thread) @tumblr #SQLi #cyberattacks #sqlinjection #appsec #cybersecurity #apptrana #indusface

Pown-Duct - Essential Tool For Finding Blind Injection Attacks j.mp/2YagdZA #InjectionAttacks #Linux #PownDuct #Resolver #SSRF

"RT SQL Injection Payload List j.mp/2D5YVkd #InjectionAttacks #InjectionPayloads #SQLInject #SQLInjection #SQLInjectionAttack https://t.co/MdfmRQb6tV"
We're thrilled to unveil our latest innovation: an AI-powered solution designed to defend against Deep Fakes and Injection Attacks. 💡🔒 👉 𝗟𝗲𝗮𝗿𝗻 𝗺𝗼𝗿𝗲: investors.truststamp.ai/press-release?… #injectionattacks #deepfake #technology #innovation #DeepFakeAwareness

Something went wrong.
Something went wrong.
United States Trends
- 1. #UFCPerth N/A
- 2. Wes Schultz N/A
- 3. Spirit Airlines N/A
- 4. #DMDLAND3DAY1 N/A
- 5. Ben Johnston N/A
- 6. Kody Steele N/A
- 7. DMD LAND SHOW NOW N/A
- 8. Morales N/A
- 9. Gorimbo N/A
- 10. Micallef N/A
- 11. WILLIAMEST NIVEA GLOW N/A
- 12. #กันแดดนีเวียเกาหลีxWilliamEst N/A
- 13. #NIVEASUNxWilliamEst N/A
- 14. #LakeShow N/A
- 15. Dom Mar Fan N/A
- 16. McAvoy N/A
- 17. Lakers in 7 N/A
- 18. Thunder in 5 N/A
- 19. Toronto N/A
- 20. JetBlue N/A