#securityvulnerabilities 検索結果
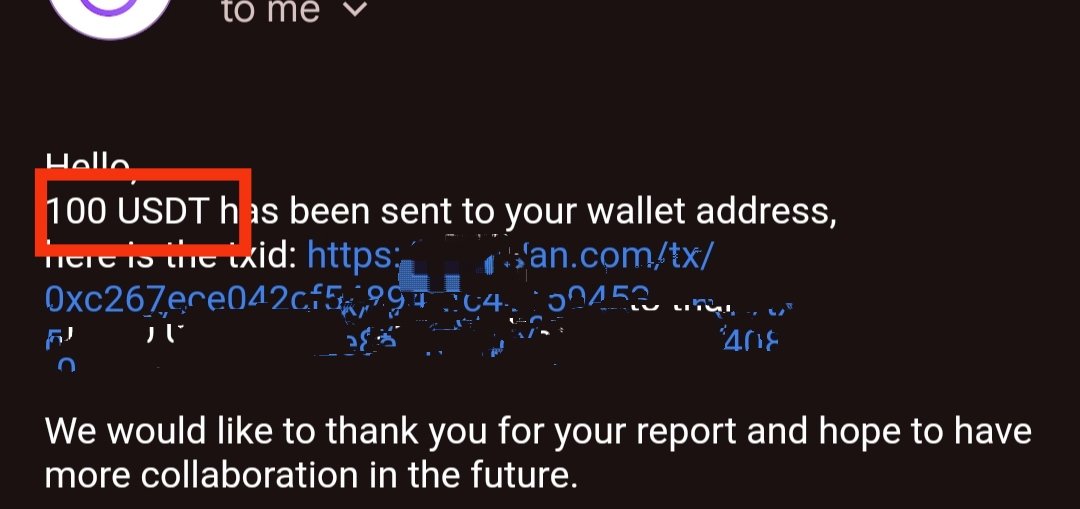
Jai shri Ram 🙏 got Bounty $$$ Thanks lord Krishna for this ! #BugBounty #SecurityVulnerabilities #InfoSec #CyberSecurity #EthicalHacking #BugHunting #WhiteHat #server #unblock #WebSecurity #HackerCommunity #CyberAware
#DigitalTransformation Brings #SecurityVulnerabilities, Canon Research Says - MSSP Alert bit.ly/2MxHik8

#Jenkins released a new version that fixes multiple #SecurityVulnerabilities. Update now bitn.am/2JCHo3T

Episode 3 of The @ActiveState Podcast is out! In this episode, Nicole Schwartz and Martin Drohmann dive into the challenges of managing #SecurityVulnerabilities while meeting development deadlines. Watch the full episode: bit.ly/3VVUHVD
#AI systems can be leveraged to insert hard-to-detect #SecurityVulnerabilities into computer chip designs, enabling even those with limited expertise to create sophisticated hardware attacks. @NYUTandon doi.org/g9576h techxplore.com/news/2025-10-a…
HOW TO TRAIN YOUR #Ghidra 🐉 a complex collection of #sourcecode with many third-party dependencies that are known to contain #securityvulnerabilities.👉 kas.pr/4kvx #cybersecuritytraining #ittraining #infosec #reverseengineering
The Indian Computer Emergency Response Team (CERT-In) issued a critical advisory on August 2, warning of severe #securityvulnerabilities in various #Apple products. Read more: bit.ly/3yyGmFy
#SecurityVulnerabilities – a zero-day exploit had been discovered in #log4j, a popular #Java logging library. All the library’s versions between 2.0 and 2.14.1 included are affected. Find out more on #InfoQ: bit.ly/31Ldtpz @olimpiupop #SoftwareArchitecture #DevOps

Understanding the human factor of #digitalsafety techradar.com/pro/understand… @TechRadarPro #securityvulnerabilities

Severe weather events cause disruptions that could lead to #SecurityVulnerabilities. @barracuda's @GregArnette shares tips on protecting #data in the age of #ClimateChange, via @ITProToday @karendschwartz: ow.ly/8qtD30oLbYb #Cybersecurity #BCDR

#Log4shell was one of the most critical #SecurityVulnerabilities of the current history. Read the #InfoQ Q&A with Arshan Dabirsiaghi and learn how #ContrastSecurity took an alternative approach to fix the issues: bit.ly/34Xbr6Y @olimpiupop #Java #DependencyManagement

Congrats to @Dooflin5 + Jesse Victors for having their research accepted to @thotcon 2023! Their selection demonstrates the high level of expertise our #SecurityEngineers have and places them among the best for identifying + solving even the most unique #securityvulnerabilities.

Software companies typically provide #softwareupdates for 3 reasons: to add new features, fix known bugs, and #upgradesecurity. Always update to the latest version of your software to protect yourself from new or existing #securityvulnerabilities. 💻 #cybercrime #datasecurity

#SecurityVulnerabilities - A new vulnerability in the CRI-O container runtime used by many #Kubernetes installations allows a malicious user to gain root access to the host. The vulnerability was fixed by the CRI-O project: bit.ly/3uI3Bat @talonx #InfoQ #Containers
MS-LLTD, MDNS, and ICMPv6 represent three commonly employed #networkprotocols, carrying potential #securityvulnerabilities that might not have caught your attention. Check out our #PenteraLabs research to learn more about the business risk they pose: okt.to/nm4UED
33 vulnerabilities found in embedded open source networking stacks @Forescout #Amnesia33 #SecurityVulnerabilities #IoT #TCPIP #Authentication #EmbeddedSoftware tinyurl.com/y3pncwg9

Some risks -- like #SecurityVulnerabilities and system downtime -- are obvious, others not so much. Good #PatchManagement also requires weighing the possible risks of patching: bit.ly/4ajdA8M

Thanks everybody who came to the Talented x White Hat Hackers -event on Wednesday! If you couldn't join us, you can watch Lea Viljanen & Antti Ollila's presentations here: bit.ly/2P4S6ba #securityvulnerabilities #hacking #BugBounty #whitehathackers #CTF #Cyberlympics

Qodana’s intuitive interface makes team onboarding easier! You can use the sunburst diagram to filter, identify, and address issues directly in your IDE. Try it now: jb.gg/vtt82l #CodeQuality #SecurityVulnerabilities #QodanaCloud
Insufficient logging and monitoring can slow down breach detection and worsen the impact of #SecurityVulnerabilities! ⚠️ Make sure you follow security logging standards, like #OWASP Logging Cheat Sheet guidelines, and enforce separate, restricted access controls. You can use…

🚨 New Writeup Alert! 🚨 "Ehxb | File Upload Vulnerabilities I" by Ehxb is now live on IW! Check it out here: infosecwriteups.com/6ed033539682 #hackthebox #securityvulnerabilities #portswigger #tryhackme #hacking
Jai shri Ram 🙏 got Bounty $$$ Thanks lord Krishna for this ! #BugBounty #SecurityVulnerabilities #InfoSec #CyberSecurity #EthicalHacking #BugHunting #WhiteHat #server #unblock #WebSecurity #HackerCommunity #CyberAware
#Jenkins released a new version that fixes multiple #SecurityVulnerabilities. Update now bitn.am/2JCHo3T

#DigitalTransformation Brings #SecurityVulnerabilities, Canon Research Says - MSSP Alert bit.ly/2MxHik8

#SmartHomes #SecurityNews #SecurityVulnerabilities #CyberAttack #CyberSecurityUpdates #CyberSecurityEvent #CyberSecurityReport #CyberSecurity #Infosec #TCSP #TheCyberSecurityPlace

🌟 Meet Sahil Bugade, a passionate cybersecurity enthusiast from MIT ADT University! 🚀 Recently, he made history by entering NASA's Hall of Fame for uncovering a security vulnerability in their digital assets. 🛡️ #CybersecurityHero #NASA #SecurityVulnerabilities #MITADT

33 vulnerabilities found in embedded open source networking stacks @Forescout #Amnesia33 #SecurityVulnerabilities #IoT #TCPIP #Authentication #EmbeddedSoftware tinyurl.com/y3pncwg9

Severe weather events cause disruptions that could lead to #SecurityVulnerabilities. @barracuda's @GregArnette shares tips on protecting #data in the age of #ClimateChange, via @ITProToday @karendschwartz: ow.ly/8qtD30oLbYb #Cybersecurity #BCDR

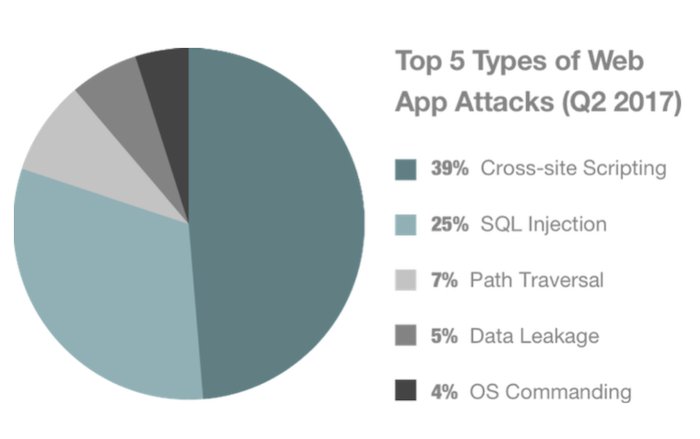
How to correct #SecurityVulnerabilities in #WebApplications? @RStyleLab shares some useful tips for businesses buff.ly/2HEELlc #WebDevelopment #WebApps #WebAppSecurity #CyberSecurity #CrossSiteScripting #SQLinjection #OpenSource via @clutch_co
Common Python Security Problems - websystemer.no/common-python-… #programming #python #securityvulnerabilities

Know how #MachineLearning is being used to handle #securityvulnerabilities by @farwa_sajjad96 via @datamadesimple bigdata-madesimple.com/machine-learni… #artificialintelligence #AI #ML #Cybersecurity #Security #technology #mistralsolutions

Understanding the human factor of #digitalsafety techradar.com/pro/understand… @TechRadarPro #securityvulnerabilities

Systemic Racism Is a Cybersecurity Threat on.cfr.org/3fzsdZw #CyberSecurity #SecurityVulnerabilities #AppsUnify

Is your company ready to face #cyberattacks? Komodo Consulting helps you identify #securityvulnerabilities in your application before hackers do. bit.ly/3tJCixt #datasecurity #cyberattacks #quotes

If you are using this plugin, we strongly recommend that you update to the latest version immediately to protect your site. Stay safe and secure online! #WordPress #OnlineCourses #SecurityVulnerabilities #ProtectYourSite
“Found means fixed,” says @github's @_mph4 of the transformation unfolding with #AIAgents able to identify and fix software development #SecurityVulnerabilities in real-time. Watch Hanley, #OutshiftByCisco's @vijoy, and @VentureBeat's @LouisColumbus. 🎦 cs.co/6012m8CKm

Congrats to @Dooflin5 + Jesse Victors for having their research accepted to @thotcon 2023! Their selection demonstrates the high level of expertise our #SecurityEngineers have and places them among the best for identifying + solving even the most unique #securityvulnerabilities.

#SecurityVulnerabilities – a zero-day exploit had been discovered in #log4j, a popular #Java logging library. All the library’s versions between 2.0 and 2.14.1 included are affected. Find out more on #InfoQ: bit.ly/31Ldtpz @olimpiupop #SoftwareArchitecture #DevOps

Something went wrong.
Something went wrong.
United States Trends
- 1. $BNKK N/A
- 2. Pond 196K posts
- 3. Good Monday 37.8K posts
- 4. #MondayMotivation 36.3K posts
- 5. Happy 250th 4,155 posts
- 6. Semper Fi 4,964 posts
- 7. Obamacare 217K posts
- 8. Rudy Giuliani 24K posts
- 9. Go Birds 3,341 posts
- 10. #Talus_Labs 1,004 posts
- 11. Victory Monday 1,503 posts
- 12. #SoloLaUniónNosHaráLibres N/A
- 13. #MondayVibes 2,589 posts
- 14. #USMC N/A
- 15. LINGLING BA HERHYNESS 503K posts
- 16. The BBC 476K posts
- 17. Edmund Fitzgerald 4,365 posts
- 18. Mark Meadows 21.8K posts
- 19. Devil Dogs 1,482 posts
- 20. $LMT $450.50 Lockheed F-35 N/A