#detectionengineering ผลการค้นหา
Your stack isn’t perfect—but detection engineering shows you where it’s slipping. Our #guide explains how modern teams stay ahead of misconfigs, silent failures, and constant change. 👉 Read the #DetectionEngineering Guide: hubs.ly/Q03WQ-bZ0
I’m excited to launch our latest online course, YARA for Security Analysts. We built this course for people who want to learn to write YARA rules for detection engineering, system triage, incident response, and threat intel research. #Yara #DetectionEngineering #DFIR #Malware
🚨Bad news for defenders, good news for red teamers: Linkable token identifiers in Entra ID are useful only in an AiTM scenario. Doesn't even cover Device Code Phishing. Blog soon. #ThreatHunting #DetectionEngineering #redteam

What people often overlook in #DetectionEngineering is that there’s no "one-size-fits-all" rule to detect a threat. It depends on your goals. How specific should the rule be? Are you tracking a threat actor, detecting the tool/malware, or focusing on the technique? Should it be…

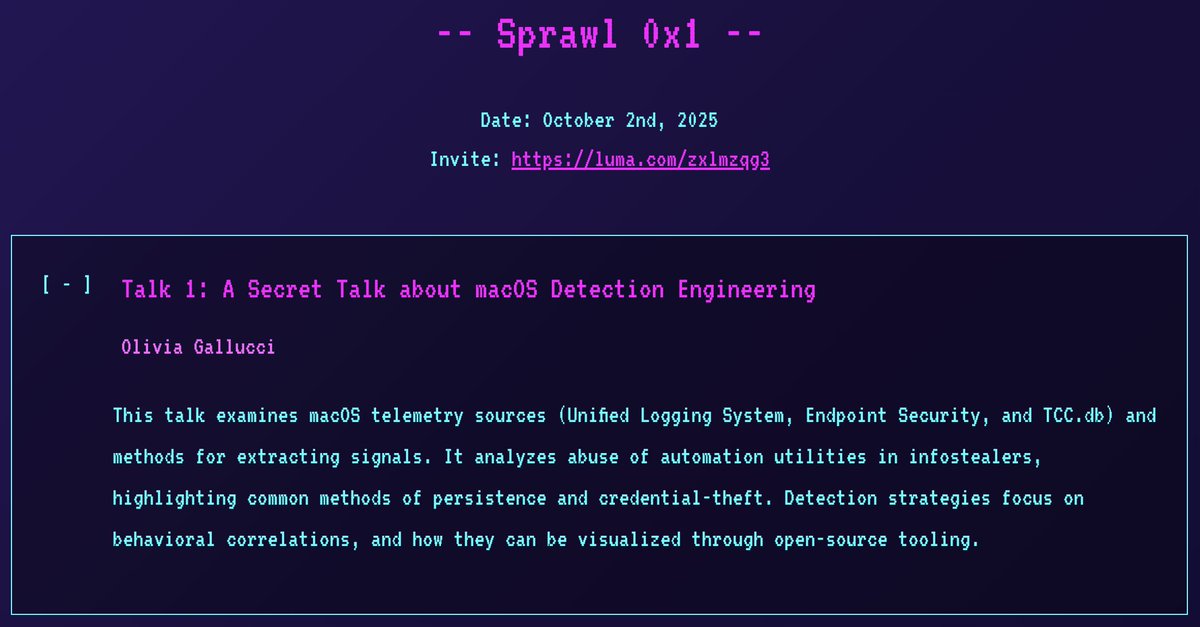
I'm thrilled to announce I'll be giving a *secret* macOS detection engineering talk at the 1st Spraw, a new NYC security meetup! Hope to see you there! 😄 📅 Date: 2 October 2025 🎟️ Registration: sprawl.nyc #InfoSec #NYC #DetectionEngineering
🚨 Detect Suspicious SPN logon from Workstations. The new Credential Dump technique that bypasses Credential Guard leaves an interesting artifact to hunt for. #KQL #ThreatHunting #DetectionEngineering

🚨#Opendir #Malware🚨 🧵1 hxxps://tiger-checkout-draws-basketball.trycloudflare.com/ It's a nice time to learn how some TAs carry out their TTPs and at once invest time in #DetectionEngineering ☣️📸tp.bat➡️f136138d2e16aad30f27c6f30742dd7b Drops and execute a few runtimes⤵️


We are now developing @elastic threat hunting queries, alongside our detection rules, and openly sharing these as well! 🎉🎉 Can visually explore these with rulexplorer.io! 🔥🔥 #ThreatHunting #DetectionEngineering



Threat hunting just got easier! This new repo of detection rules is crafted by our veteran detection engineers and powered by different Elastic query languages. Get the details of what’s included and see the future of this repo here: go.es.io/4h2JsTX #ElasticSecurityLabs
Highlights from the @MsftSecIntel and joint CSA reports animated. #ThreatHunting #DetectionEngineering
I do love #KQL, but not having support for features like complete window functions (over (partition by ...)) and allowing only equality-based joins are huge blockers, especially in the detection engineering field. #DetectionEngineering

🚨Spoiler: You can't detect #BadSuccessor with default configuration on AD/DC. Blog is almost finished. #ThreatHunting #DetectionEngineering

The lolol.farm continues to grow! Introducing a new project: LoFP - Living off the False Positive Where you can blend into the noise, or leverage it for triage and rule writing. 🎊🍻 br0k3nlab.com/LoFP/ #DetectionEngineering #Security

Just updated lolol.farm with a few more entries Also, let me know if there are any others that should be added

New #Sigma rule to spot Click-Fix + Cache-Smuggling chains on Windows 🎯 Unified for Sysmon ID1 & Sec. 4688 🫡 YAML 👉 pastebin.com/A3Wgjjyi Please any comment, suggestions, experiences are more than welcome (I'm not an expert with Sigma). #DetectionEngineering #SOC
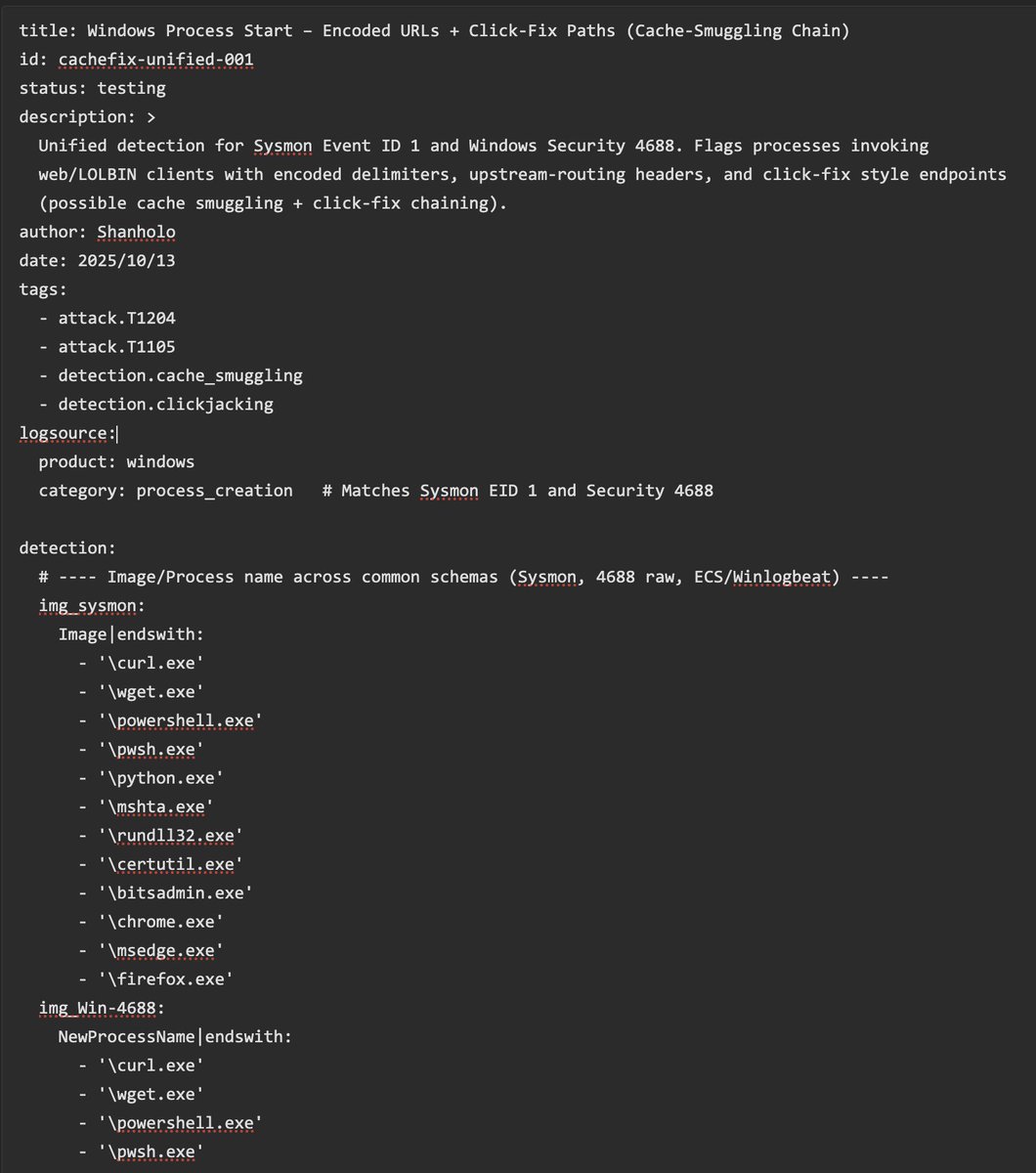
So I have been told threat actors use my Browser Cache Smuggling technique to compromise people: expel.com/blog/cache-smu… Remember, detection is really easy: any process touching a browser's cache file and moving it to a .dll one IS A RED FLAG. Detection rule is easy to set ;)!
This is the follow-up you've been waiting for: The #DetectionEngineering Blog Post Part 6 by @_st0pp3r_ blog.nviso.eu/2025/09/23/det… You'll gain insights on manual, release-based, automatic and multitenant deployments to optimize #ContinuousDeployment processes and more.

Frank @r3c0nst created a neat #Yara workshop some time ago and released the materials this weekend. If you want to learn Yara (or know someone who does) - this is a very good place to start. #threatintel #detectionengineering

Very excited to release PANIX, a highly flexible Linux persistence tool for security research and detection engineering. Test your security posture and learn about Linux persistence. github.com/Aegrah/PANIX #DetectionEngineering #SecurityResearch #Persistence #Linux #Security


My book “Web Application Defender’s Cookbook” is in the @blackhat book store if folks are looking for web application #detectionengineering guidance 👍

Your stack isn’t perfect—but detection engineering shows you where it’s slipping. Our #guide explains how modern teams stay ahead of misconfigs, silent failures, and constant change. 👉 Read the #DetectionEngineering Guide: hubs.ly/Q03WQ-bZ0
Good news everyone! 25% off my "Detection Engineering with Sigma" course! Use code "ALLYALL" at checkout. LearnSigmaRules.com #DetectionEngineering #InfoSec #SIGMA @sigma_hq @NetworkDefense
@DatadogHQ is hiring for two roles on our Threat Detection Engineering team! 🐶 - Senior Security Engineer - Insider in NYC: careers.datadoghq.com/detail/7391209… - Security Engineer 2 in Paris: careers.datadoghq.com/detail/7379791… #InfoSec #Datadog #DetectionEngineering
Cobalt Strike has a chokepoint that is great for robust detection. 👇 #ThreatHunting #DetectionEngineering academy.bluraven.io/blog/detecting…
Risk-based alerting (only surfacing alerts that *truly* pose a risk to your organization) is all the rage in detection engineering. I threw together a guide to quickly getting started with RBA in Microsoft Sentinel. isaacdunham.github.io/posts/risk-bas… #DetectionEngineering #SIEM #Sentinel
What happens when training goes beyond theory? You get stories like these. 🌐 Real SOC workflows ⚡ Ready-for-the-job skills 🔥 Performance that speaks for itself These aren’t testimonials. They’re real stories. #CybersecurityTraining #SOCAnalyst #DetectionEngineering…


Back with a new blog post! #DetectionEngineering: Practicing #DetectionAsCode – Tuning - Part 8 👉 blog.nviso.eu/2025/11/25/det… If you missed the rest of the parts you can find them here: blog.nviso.eu/tag/detection-…
Wondering how to make your #DetectionSystems more responsive during infrastructure changes? Read the latest blog post by @kristo_b & @_st0pp3r_ on #DetectionEngineering 👉blog.nviso.eu/2025/11/25/det…
Wondering how to make your #DetectionSystems more responsive during infrastructure changes? Read the latest blog post by @kristo_b & @_st0pp3r_ on #DetectionEngineering 👉blog.nviso.eu/2025/11/25/det…
I’m excited to launch our latest online course, YARA for Security Analysts. We built this course for people who want to learn to write YARA rules for detection engineering, system triage, incident response, and threat intel research. #Yara #DetectionEngineering #DFIR #Malware
🚨Bad news for defenders, good news for red teamers: Linkable token identifiers in Entra ID are useful only in an AiTM scenario. Doesn't even cover Device Code Phishing. Blog soon. #ThreatHunting #DetectionEngineering #redteam

What people often overlook in #DetectionEngineering is that there’s no "one-size-fits-all" rule to detect a threat. It depends on your goals. How specific should the rule be? Are you tracking a threat actor, detecting the tool/malware, or focusing on the technique? Should it be…

New module is up on aceresponder.com - UAC Bypasses! Gain valuable experience investigating a variety of UAC bypasses. Come level up with us! #ThreatHunting #DetectionEngineering
🚨New Module on ACEResponder.com! Want to get started with detection engineering? Why not jump in and build some?🕵️♂️🔎 In this module we cover the core principles and put them to use making kerberoasting detections. Let's do it! #DetectionEngineering #DFIR

🚨New Detection Engineering Challenge on ACEResponder.com You're tasked with creating a detection to uncover any residual presence following a high-impact intrusion. Can you build a performant detection for a stealthy Cobalt Strike beacon? #DetectionEngineering #DFIR
🚨#Opendir #Malware🚨 🧵1 hxxps://tiger-checkout-draws-basketball.trycloudflare.com/ It's a nice time to learn how some TAs carry out their TTPs and at once invest time in #DetectionEngineering ☣️📸tp.bat➡️f136138d2e16aad30f27c6f30742dd7b Drops and execute a few runtimes⤵️


😁So excited about the improvements and upgrades open-source projects like atomicredteam.io and sigmahq.io are going through to bring 🛡️#DetectionEngineering capabilities to everyone! @nas_bench and @cyb3rbuff your impact has been on 🔥

In May, #ElasticSecurityLabs published 52 new rules! Take a look at the overview and learn how we manage these rulesets: go.es.io/45JHiVR #detectionengineering #SIEM #EDR

🚨 Detect Suspicious SPN logon from Workstations. The new Credential Dump technique that bypasses Credential Guard leaves an interesting artifact to hunt for. #KQL #ThreatHunting #DetectionEngineering

We are now developing @elastic threat hunting queries, alongside our detection rules, and openly sharing these as well! 🎉🎉 Can visually explore these with rulexplorer.io! 🔥🔥 #ThreatHunting #DetectionEngineering



Threat hunting just got easier! This new repo of detection rules is crafted by our veteran detection engineers and powered by different Elastic query languages. Get the details of what’s included and see the future of this repo here: go.es.io/4h2JsTX #ElasticSecurityLabs
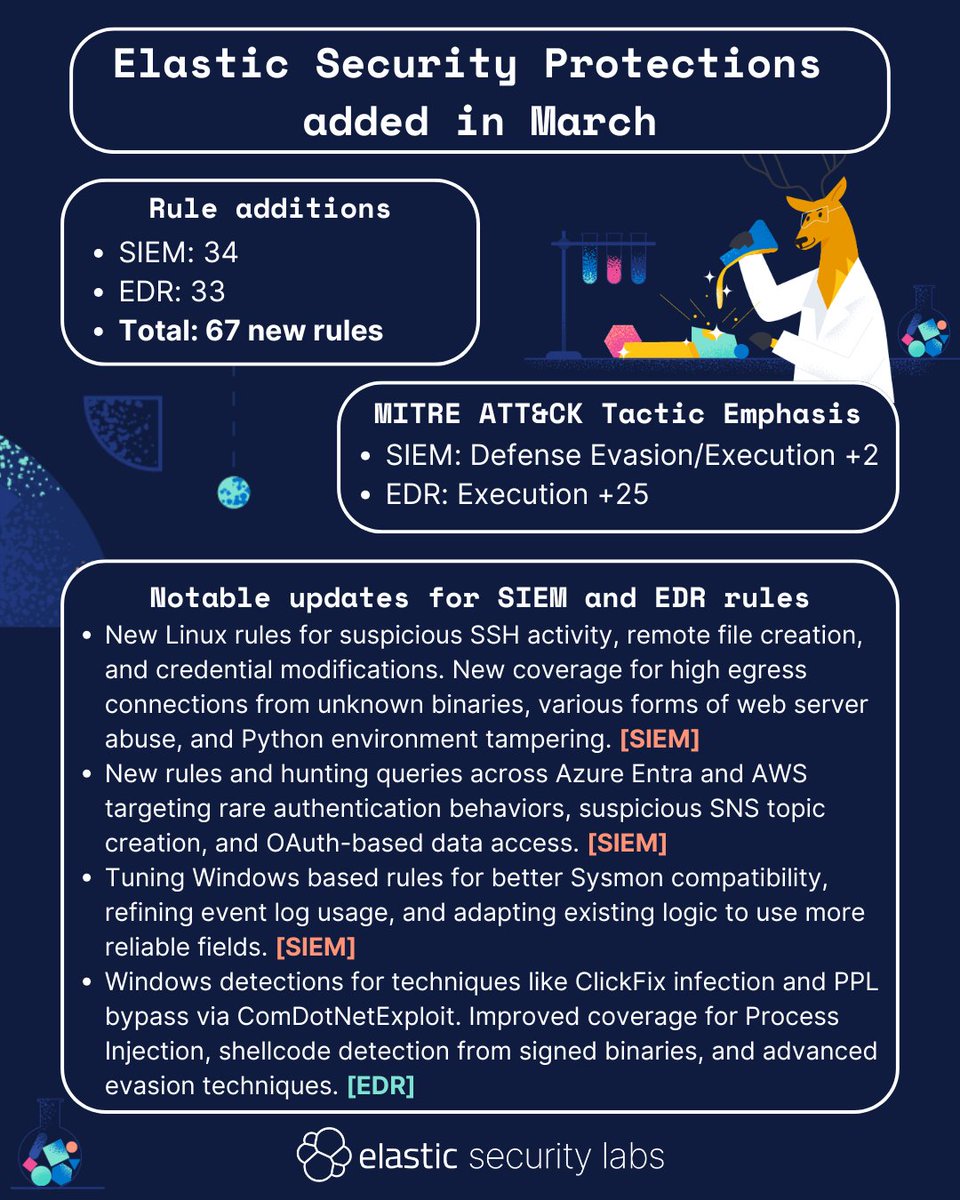
In March, #ElasticSecurityLabs published 67 new rules! Take a look at the overview, or check out our entire library of protections here: go.es.io/42qPQhc #detectionengineering #SIEM #EDR
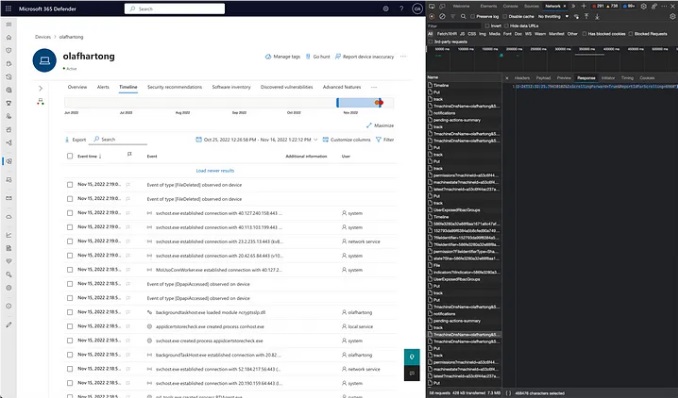
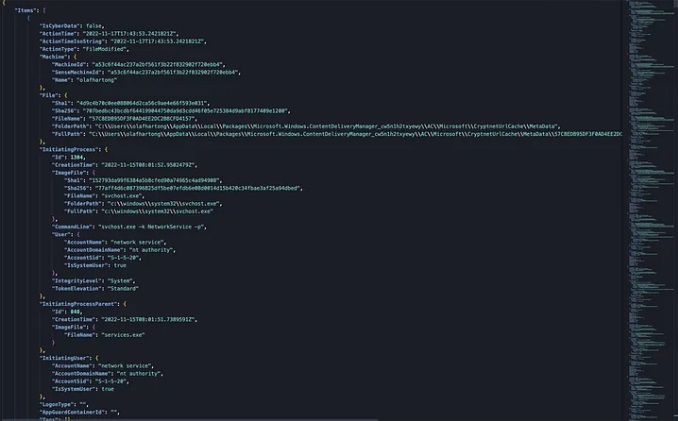
Microsoft Defender for Endpoint Internals 0x04 — Timeline telemetry medium.com/falconforce/mi… #Pentesting #DetectionEngineering #CyberSecurity #Infosec
🚨Spoiler: You can't detect #BadSuccessor with default configuration on AD/DC. Blog is almost finished. #ThreatHunting #DetectionEngineering

You can access our #detectionengineering repos, but how about a closer look? The 2025 State of Detection Engineering at Elastic is a new #report from #ElasticSecurityLabs detailing how we create and assess our prebuilt rules. Check it out: go.es.io/4jnrXhA

Register now for our webinar and see how our new #Impede Detection Platform is changing the game for #DetectionEngineering. You'll see demos of theTechnique Catalog, Community Catalog, and other advanced capabilities integrated into the platform. @Ben0xA hubs.la/Q029FZH70

In April, #ElasticSecurityLabs published 62 new rules! Take a look at the overview and learn how we manage these rulesets: go.es.io/3EX0NiN #detectionengineering #SIEM #EDR

Something went wrong.
Something went wrong.
United States Trends
- 1. Cloudflare 32.5K posts
- 2. Cowboys 74.2K posts
- 3. #heatedrivalry 30.8K posts
- 4. Happy Farmers 2,121 posts
- 5. LeBron 115K posts
- 6. Warner Bros 34.5K posts
- 7. Wizkid 183K posts
- 8. Pickens 15.4K posts
- 9. Lions 93.9K posts
- 10. Jake Tapper 45K posts
- 11. fnaf 2 28.2K posts
- 12. rUSD N/A
- 13. Paramount 22.2K posts
- 14. Gibbs 21.2K posts
- 15. #PowerForce N/A
- 16. Shang Tsung 36.8K posts
- 17. Davido 101K posts
- 18. scott hunter 7,028 posts
- 19. The Gong Show N/A
- 20. Hiroyuki Tagawa 32.5K posts