#malwareanalysis نتائج البحث
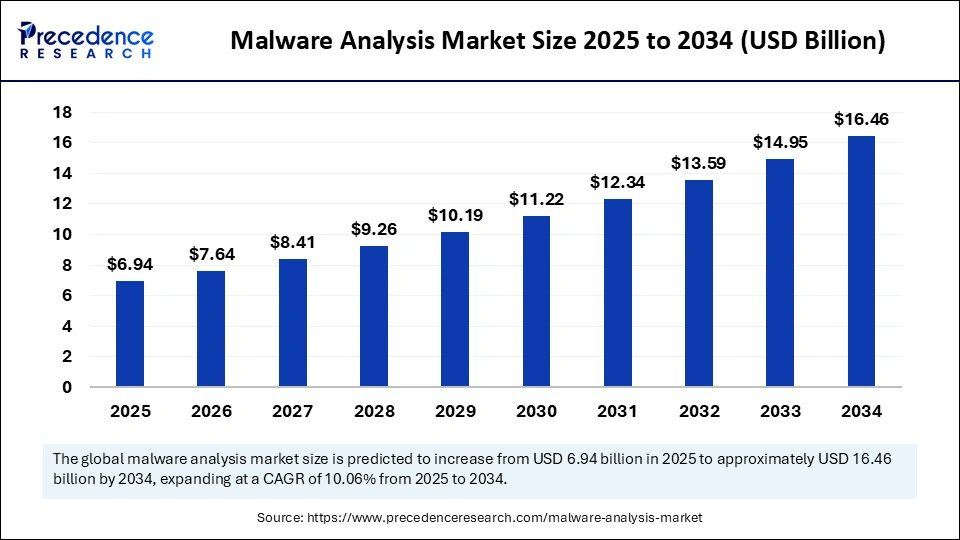
The #malwareanalysis market is rising fast—valued at $6.94B in 2025 and projected to reach $16.46B by 2034 (CAGR 10.06%). With cyberattacks growing more sophisticated, demand for automated threat detection and real-time security intelligence is surging. precedenceresearch.com/malware-analys…
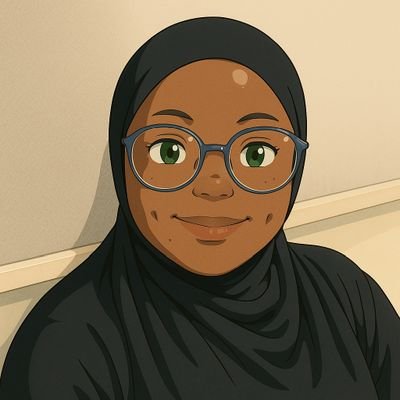
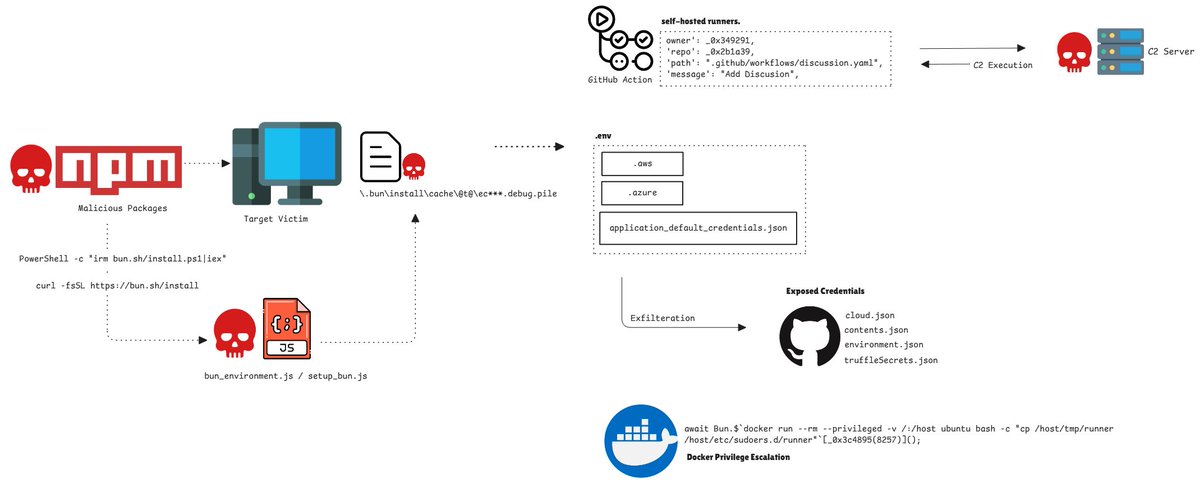
Silent Exfilteration : Sha1-Hulud: The Second Coming. The rise of modern software supply chains has accelerated rapidly—and with it, a new wave of highly sophisticated, often invisible cyberattacks. #SupplyChainAttack #MalwareAnalysis #Sha1Hulud CC: @malwarehuntslab
مستوى متقدم من التخفي البرمجية لا تُكتب على القرص الصلب، بل تعمل من الذاكرة فقط — ما يجعل اكتشافها عبر برامج الحماية التقليدية صعبًا للغاية. كما تستخدم خوارزميات XOR لتشفير الأوامر وإخفاء أنشطتها عن أدوات المراقبة الأمنية. #InfoSec #MalwareAnalysis
Malware Classification on @TryHackMe taught me to identify and categorize threats, from adware and spyware to ransomware, wipers, and keyloggers. Understanding malware families and attack patterns sharpens threat detection skills. #SOC #BlueTeam #MalwareAnalysis

WithSecure's STINGR Group has released a detailed analysis of TangleCrypt, a sophisticated yet buggy Windows malware packer, found in a ransomware attack, outlining its unpacking process and implementation flaws. #CyberSecurity #MalwareAnalysis labs.withsecure.com/publications/t…
#JSAC2026 registration is now open. #DFIR #MalwareAnalysis jsac.jpcert.or.jp/en/registratio…
🚨 New Python-based WhatsApp worm spreading via malicious links. Visit @TheHackersNews for more details #MalwareAnalysis #Python #WhatsApp
رشتو: معرفی تکنیک #ControlFlowFlattening: این تکنیک مبهم سازی، ساختار منطقی و طبیعی یک تابع یا برنامه رو از بین میبره و اون رو به مجموعهای از بلوکهای کد تبدیل میکنه که توسط یک Dispatcher مرکزی و یک متغیر وضعیت (State Variable) کنترل میشن. #آنالیز_بدافزار #MalwareAnalysis 1/6
Your AV says everything's fine, but you feel something's wrong. It's time to look deeper. Here’s why manual process hunting is a critical skill for spotting threats that automated tools miss. #CyberSecurity #ThreatHunting #MalwareAnalysis #InfoSec bl4ckphoenix.com/beyond-the-sca…
Persistencia oscura: cuando tu PC jura lealtad al atacante Servicios falsos, WMI persistence, drivers alterados, hooks en explorer.exe. Una vez instalado, solo el Fuego Valyrio lo saca. #Persistence #MalwareAnalysis #DFIR #Rootkits #RedTeam
🚀 MAoS just hit 1,000 reads on ResearchGate! Grateful to see researchers and security professionals diving into the book and using it in real-world work. More research and deep-dive content coming soon. 📖 amazon.com/dp/B0FQDGZGZW #CyberSecurity #MalwareAnalysis…
TangleCrypt is a new Windows packer that hides payloads in PE resources using base64, LZ78 compression, and XOR. It delivers STONESTOP payloads with the ABYSSWORKER driver and has flawed TLS handling. #TangleCrypt #MalwareAnalysis #WindowsSecurity ift.tt/folK6YE
Nimbus Manticore is a 64-bit PE malware using Microsoft toolchains to escalate privileges, move laterally via RPC, and evade sandboxes with timing checks. Only Deep Instinct detected it for a full week. #NimbusManticore #MalwareAnalysis #USA ift.tt/1VrH7vq
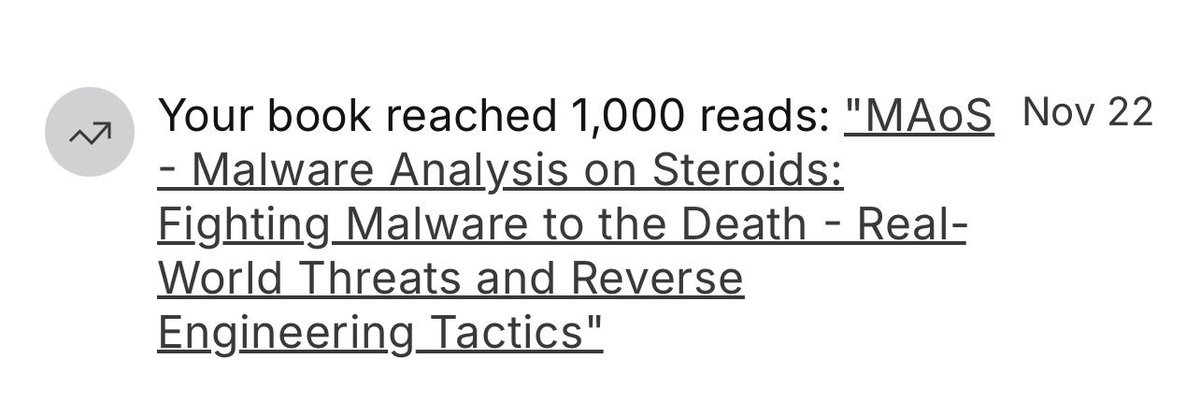
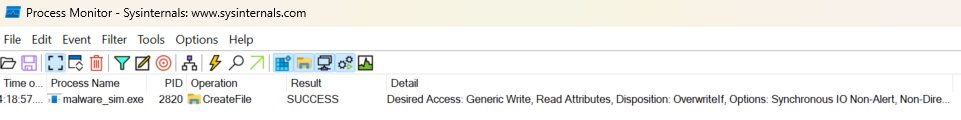
🎯 ProcMon trick: Set filter Path→contains→'Temp' + Operation→is→'CreateFile' to catch malware dropping files. Most malware writes to %TEMP% first. Save this filter for quick malware hunting! #DFIR #ProcMon #MalwareAnalysis #FileSystem

Attackers are getting smarter, using signed Microsoft binaries to hide their tracks. Our latest analysis reveals how a hidden Python fragment injects into cvtres.exe to evade detection. Get the full technical breakdown here labs.k7computing.com/index.php/mask… #CyberSecurity #MalwareAnalysis
Matanbuchus 3.0 enhances a C++ backdoor/downloader with Protobuf-based serialized communication and advanced ChaCha20 encryption, supporting hands-on-keyboard actions in ransomware-linked campaigns. #Matanbuchus #RansomwareOps #MalwareAnalysis ift.tt/gEpwn6c
hendryadrian.com
Technical Analysis of Matanbuchus 3.0
Matanbuchus is a C++ malicious downloader/backdoor offered as MaaS since 2020 that downloads and executes second-stage payloads and supports hands-on-keyboard activity, often observed in ransomware...
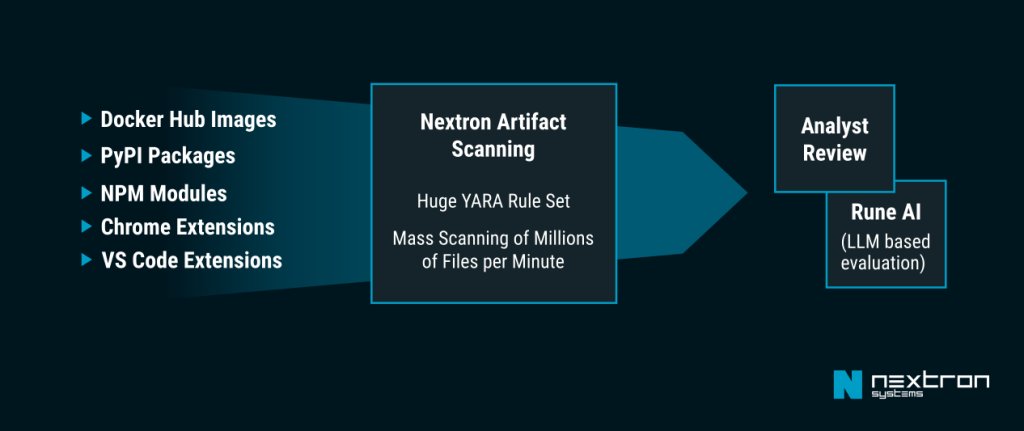
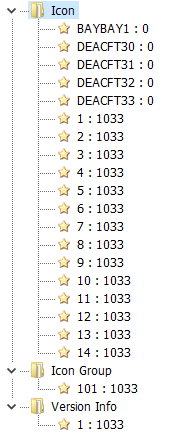
A recent analysis reveals that a malicious VS Code extension, masquerading as "Material Icon Theme," deploys Rust implants to fetch C2 instructions via a Solana wallet, using stealthy methods like Google Calendar for fallback. #MalwareAnalysis #CyberSecu… nextron-systems.com/2025/11/29/ana…
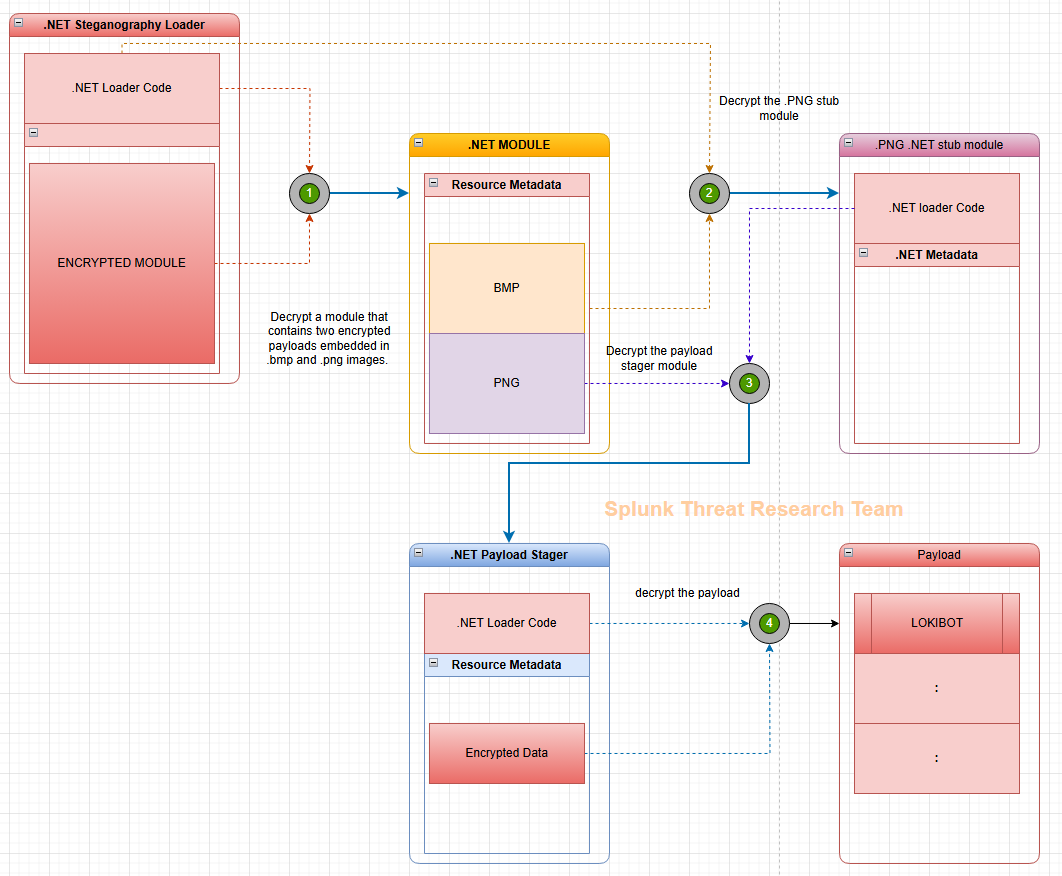
A new .NET steganographic loader disguises as a business document, hiding Lokibot payloads in images, enabling credential theft, code injection, and persistence via scheduled tasks. #Lokibot #Steganography #MalwareAnalysis ift.tt/VT0U1XO
A malicious VS Code extension "Icon Theme: Material" with hidden Rust implants was found in the marketplace, using Solana and Google Calendar for C2. Artifacts discovered via THOR Thunderstorm pipeline. #VisualStudio #MalwareAnalysis #USA ift.tt/bTl3q4I
A malicious VS Code extension "Icon Theme: Material" with hidden Rust implants was found in the marketplace, using Solana and Google Calendar for C2. Artifacts discovered via THOR Thunderstorm pipeline. #VisualStudio #MalwareAnalysis #USA ift.tt/bTl3q4I
TangleCrypt is a new Windows packer that hides payloads in PE resources using base64, LZ78 compression, and XOR. It delivers STONESTOP payloads with the ABYSSWORKER driver and has flawed TLS handling. #TangleCrypt #MalwareAnalysis #WindowsSecurity ift.tt/folK6YE
Nimbus Manticore is a 64-bit PE malware using Microsoft toolchains to escalate privileges, move laterally via RPC, and evade sandboxes with timing checks. Only Deep Instinct detected it for a full week. #NimbusManticore #MalwareAnalysis #USA ift.tt/1VrH7vq
Matanbuchus 3.0 enhances a C++ backdoor/downloader with Protobuf-based serialized communication and advanced ChaCha20 encryption, supporting hands-on-keyboard actions in ransomware-linked campaigns. #Matanbuchus #RansomwareOps #MalwareAnalysis ift.tt/gEpwn6c
hendryadrian.com
Technical Analysis of Matanbuchus 3.0
Matanbuchus is a C++ malicious downloader/backdoor offered as MaaS since 2020 that downloads and executes second-stage payloads and supports hands-on-keyboard activity, often observed in ransomware...
Persistencia oscura: cuando tu PC jura lealtad al atacante Servicios falsos, WMI persistence, drivers alterados, hooks en explorer.exe. Una vez instalado, solo el Fuego Valyrio lo saca. #Persistence #MalwareAnalysis #DFIR #Rootkits #RedTeam
iT4iNT SERVER Researchers Capture Lazarus APT's Remote-Worker Scheme Live on Camera dlvr.it/TPb8X5 VDS VPS Cloud #CyberSecurity #MalwareAnalysis #APTThreats #LazarusGroup #RemoteWork
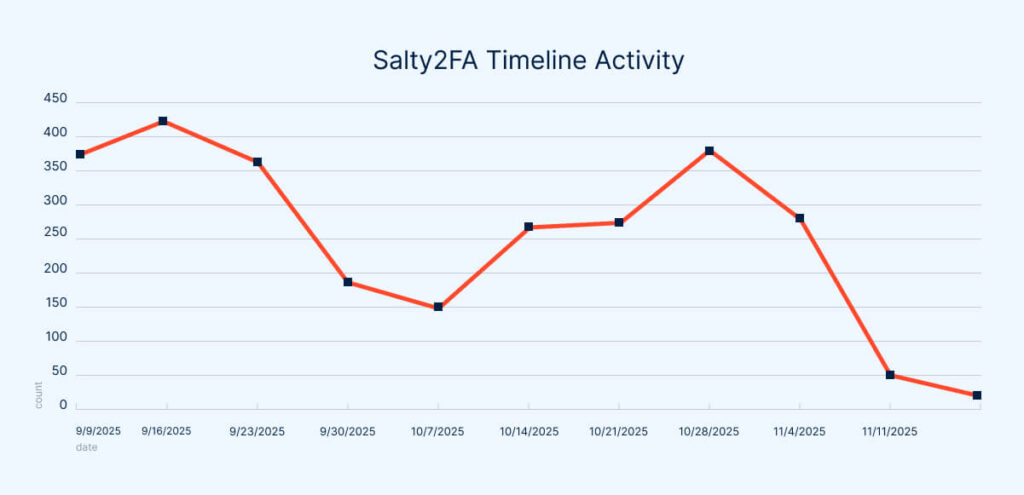
The Salty2FA infrastructure collapse in late Oct 2025 revealed hybrid malware combining Salty2FA and Tycoon2FA code, complicating detection and linking both as a single threat cluster for enterprises. #MalwareAnalysis #InfoSec #UnitedStates ift.tt/h4AHTM6
رشتو: معرفی تکنیک #ControlFlowFlattening: این تکنیک مبهم سازی، ساختار منطقی و طبیعی یک تابع یا برنامه رو از بین میبره و اون رو به مجموعهای از بلوکهای کد تبدیل میکنه که توسط یک Dispatcher مرکزی و یک متغیر وضعیت (State Variable) کنترل میشن. #آنالیز_بدافزار #MalwareAnalysis 1/6
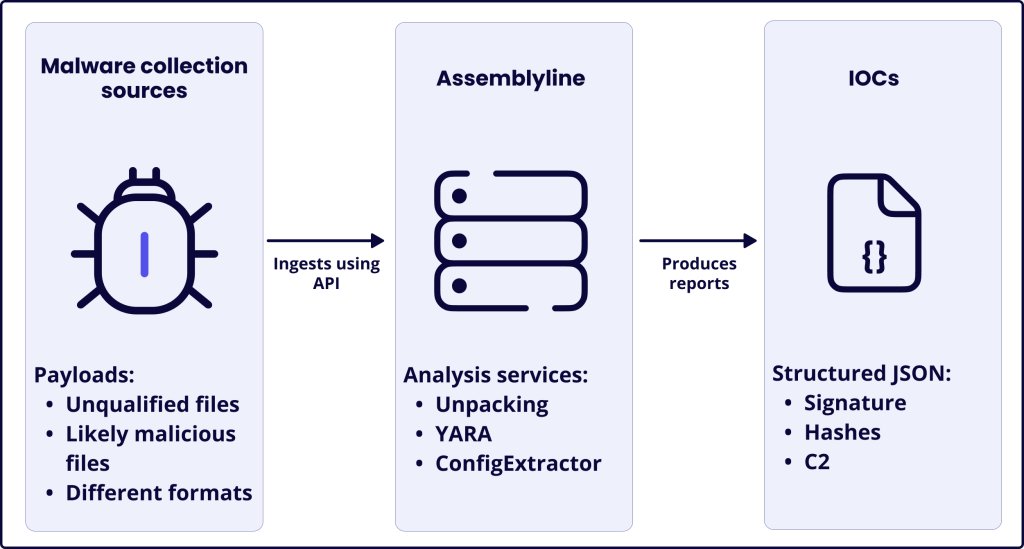
Sekoia TDR leverages Assemblyline's staged pipeline and ConfigExtractor to automate malware config extraction, demonstrated on Kaiji IoT botnet. Uses YARA detection and Python decoding for C2:Port data. #IoTSecurity #MalwareAnalysis #Canada ift.tt/FXU0K2W
The #malwareanalysis market is rising fast—valued at $6.94B in 2025 and projected to reach $16.46B by 2034 (CAGR 10.06%). With cyberattacks growing more sophisticated, demand for automated threat detection and real-time security intelligence is surging. precedenceresearch.com/malware-analys…
WithSecure's STINGR Group has released a detailed analysis of TangleCrypt, a sophisticated yet buggy Windows malware packer, found in a ransomware attack, outlining its unpacking process and implementation flaws. #CyberSecurity #MalwareAnalysis labs.withsecure.com/publications/t…
Malware Analysis Report 🔥🫡 medium.com/@nanaaisha1030… @ireteeh @judeosamor @TemitopeSobulo @segoslavia #CyberSecurity #MalwareAnalysis
2/8 Instant Risk Scoring: Get 0-100 security scores in seconds! The tool automatically detects: Packed malware (UPX unpacking built-in) Suspicious imports & API patterns Future timestamps & fake signatures 186+ embedded URLs & IP addresses #MalwareAnalysis #ThreatDetection
#JSAC2026 registration is now open. #DFIR #MalwareAnalysis jsac.jpcert.or.jp/en/registratio…
Attackers are getting smarter, using signed Microsoft binaries to hide their tracks. Our latest analysis reveals how a hidden Python fragment injects into cvtres.exe to evade detection. Get the full technical breakdown here labs.k7computing.com/index.php/mask… #CyberSecurity #MalwareAnalysis
Ofuscar = ganar tiempo. Mientras vos peleás con el rompecabezas, el malware se instala. #MalwareAnalysis #CyberDefense #IngenieriaInversa
Silent Exfilteration : Sha1-Hulud: The Second Coming. The rise of modern software supply chains has accelerated rapidly—and with it, a new wave of highly sophisticated, often invisible cyberattacks. #SupplyChainAttack #MalwareAnalysis #Sha1Hulud CC: @malwarehuntslab
🚀 MAoS just hit 1,000 reads on ResearchGate! Grateful to see researchers and security professionals diving into the book and using it in real-world work. More research and deep-dive content coming soon. 📖 amazon.com/dp/B0FQDGZGZW #CyberSecurity #MalwareAnalysis…
مستوى متقدم من التخفي البرمجية لا تُكتب على القرص الصلب، بل تعمل من الذاكرة فقط — ما يجعل اكتشافها عبر برامج الحماية التقليدية صعبًا للغاية. كما تستخدم خوارزميات XOR لتشفير الأوامر وإخفاء أنشطتها عن أدوات المراقبة الأمنية. #InfoSec #MalwareAnalysis
🚨 New Python-based WhatsApp worm spreading via malicious links. Visit @TheHackersNews for more details #MalwareAnalysis #Python #WhatsApp
🔥Lumma Stealer - Manually Unpacking and Extracting C2's 🔥 Let's analyse a Lumma malware sample and manually unpack it with Dnspy and x32dbg. We'll then leverage Ghidra and x32dbg to locate and decrypt four C2 addresses. [1/24] 🖊️ #Malwareanalysis #Ghidra
![embee_research's tweet image. 🔥Lumma Stealer - Manually Unpacking and Extracting C2's 🔥
Let's analyse a Lumma malware sample and manually unpack it with Dnspy and x32dbg.
We'll then leverage Ghidra and x32dbg to locate and decrypt four C2 addresses.
[1/24] 🖊️
#Malwareanalysis #Ghidra](https://pbs.twimg.com/media/GC0gG0vaUAAkrE4.jpg)
![embee_research's tweet image. 🔥Lumma Stealer - Manually Unpacking and Extracting C2's 🔥
Let's analyse a Lumma malware sample and manually unpack it with Dnspy and x32dbg.
We'll then leverage Ghidra and x32dbg to locate and decrypt four C2 addresses.
[1/24] 🖊️
#Malwareanalysis #Ghidra](https://pbs.twimg.com/media/GC0gOFMbIAA2_rv.jpg)
![embee_research's tweet image. 🔥Lumma Stealer - Manually Unpacking and Extracting C2's 🔥
Let's analyse a Lumma malware sample and manually unpack it with Dnspy and x32dbg.
We'll then leverage Ghidra and x32dbg to locate and decrypt four C2 addresses.
[1/24] 🖊️
#Malwareanalysis #Ghidra](https://pbs.twimg.com/media/GC0gVA0bMAAeWzo.jpg)
![embee_research's tweet image. 🔥Lumma Stealer - Manually Unpacking and Extracting C2's 🔥
Let's analyse a Lumma malware sample and manually unpack it with Dnspy and x32dbg.
We'll then leverage Ghidra and x32dbg to locate and decrypt four C2 addresses.
[1/24] 🖊️
#Malwareanalysis #Ghidra](https://pbs.twimg.com/media/GC0hjgObwAAyIRM.png)
It just warms my heart ❤️ #CyberSecurity #MalwareAnalysis #ReverseEngineering #Infosec #MAoS #TrainSec #OffensiveSecurity #Malware
PolySwarm empowers security teams with private, scalable malware analysis and real-time intelligence, designed for today’s threat landscape. #CyberSecurity #ThreatIntelligence #MalwareAnalysis
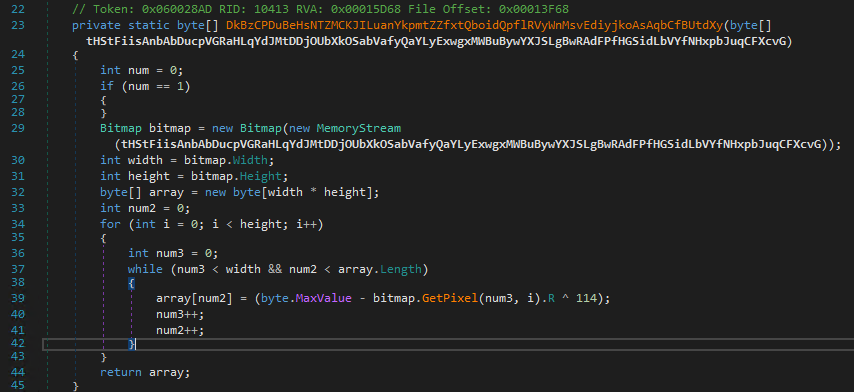
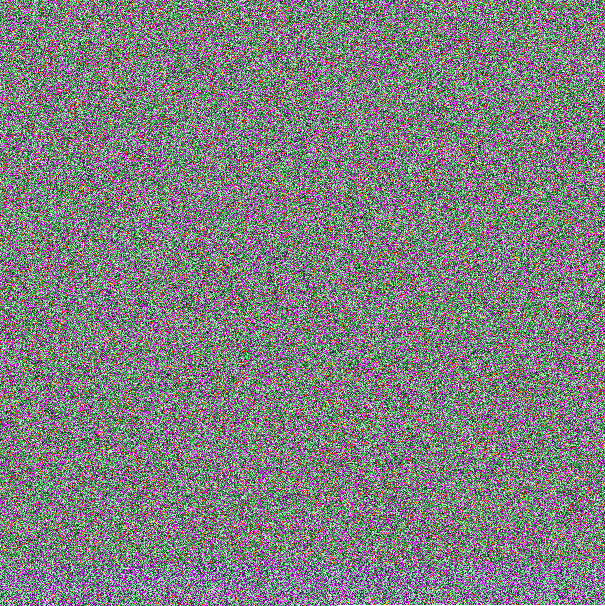
🧵New: "From Pixels to Payloads" — We reverse-engineered a multi-stage .NET loader hiding Lumma Stealer in BMPs via stego trick: (255-R)^0x72. Donut Loader → C# Injector → Lumma in memory. 🧠👇 github.com/ShadowOpCode/S… #LummaStealer #Infosec #MalwareAnalysis #ThreatIntelligence

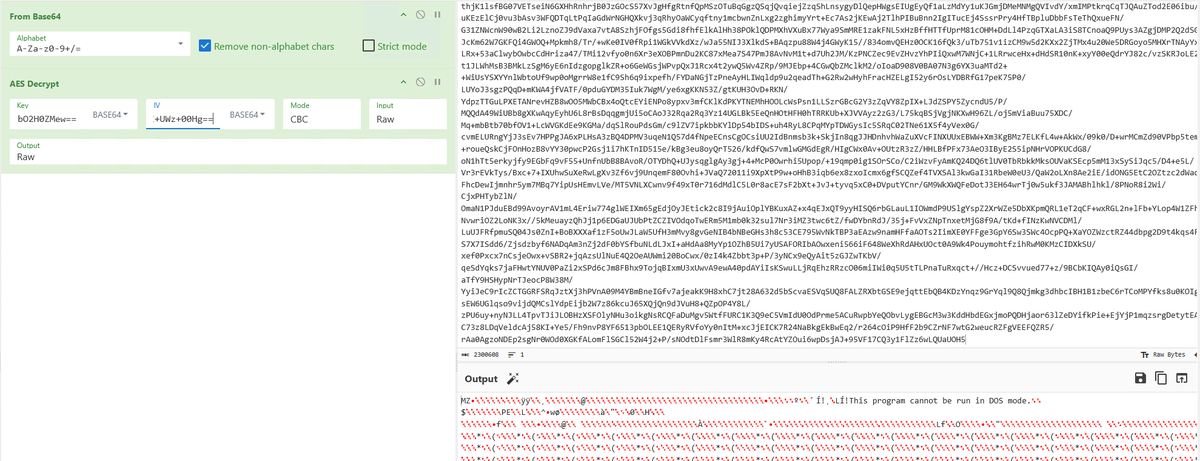
CyberChef Tips - Creating and Accessing Variables #CyberChef has a little known "registers" operation that allows you to create and reference values later on in your analysis. [1/2] #malware #malwareanalysis
![embee_research's tweet image. CyberChef Tips - Creating and Accessing Variables
#CyberChef has a little known "registers" operation that allows you to create and reference values later on in your analysis.
[1/2]
#malware #malwareanalysis](https://pbs.twimg.com/media/GPpGQTCaMAECV1x.jpg)
![embee_research's tweet image. CyberChef Tips - Creating and Accessing Variables
#CyberChef has a little known "registers" operation that allows you to create and reference values later on in your analysis.
[1/2]
#malware #malwareanalysis](https://pbs.twimg.com/media/GPpGQTabwAAd1RG.jpg)
![embee_research's tweet image. CyberChef Tips - Creating and Accessing Variables
#CyberChef has a little known "registers" operation that allows you to create and reference values later on in your analysis.
[1/2]
#malware #malwareanalysis](https://pbs.twimg.com/media/GPpGQTNa4AAkCq3.jpg)
![embee_research's tweet image. CyberChef Tips - Creating and Accessing Variables
#CyberChef has a little known "registers" operation that allows you to create and reference values later on in your analysis.
[1/2]
#malware #malwareanalysis](https://pbs.twimg.com/media/GPpGQR2bEAAPiZM.png)
It’s finally here! 📦 Just received my own printed copies of MAoS – Malware Analysis on Steroids 🔥 There’s nothing like holding your work after months of writing, research, and late-night debugging. Get your copy here👉amazon.com/dp/B0FQDGZGZW #CyberSecurity #MalwareAnalysis…


🚨 New variant spotted: Matanbuchus 3.0 — a rebuilt malware loader advertised on underground forums. Features DNS/HTTPS C2, in-memory execution, reverse shell, morphing builds & multitenant panel. Price: $10K–$15K/month. Active threat. #CyberThreat #Infosec #MalwareAnalysis

In one of the #MalwareAnalysis communities I’m in, we were talking about Go malware. Someone mentioned CAPA as a good tool. I have to say, it’s really helpful for finding the 50kb of interesting code buried inside a 5mb Go binary 😎What other tools do you use?

Revisited my malware analysis project using FLARE VM and upgraded it with a custom YARA rule to hunt AgentTesla variants. Proud of how it turned out. Shoutout to @ireteeh and @Cyblackorg for this opportunity 🙂 #MalwareAnalysis #YARARules #Cybersecurity #ThreatHunting #FLAREVM
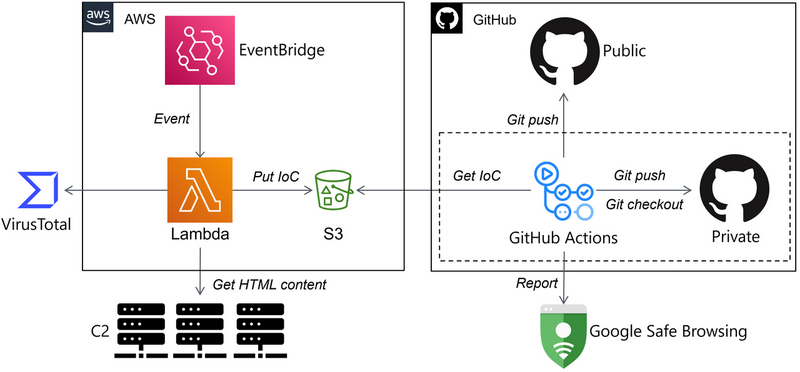
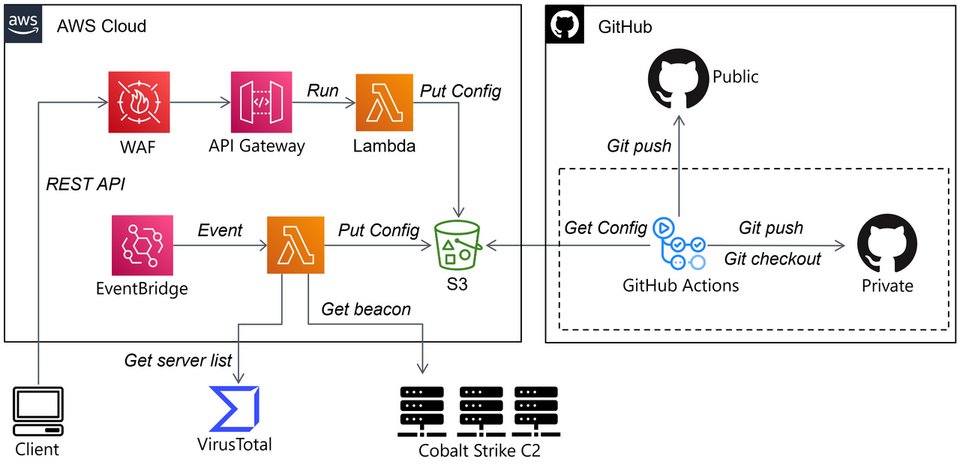
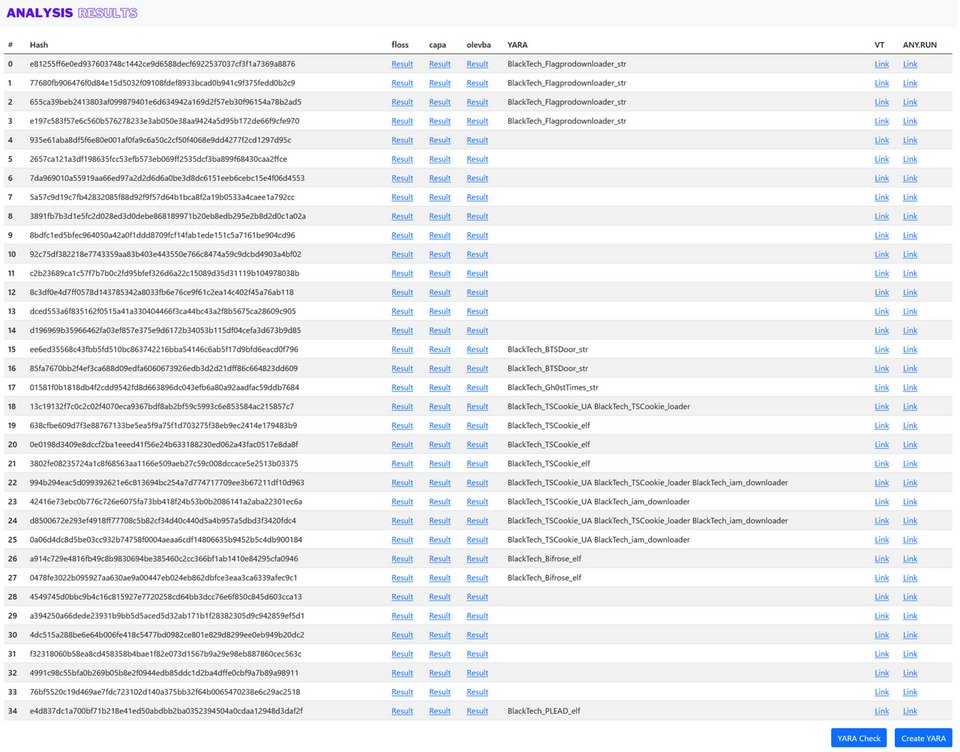
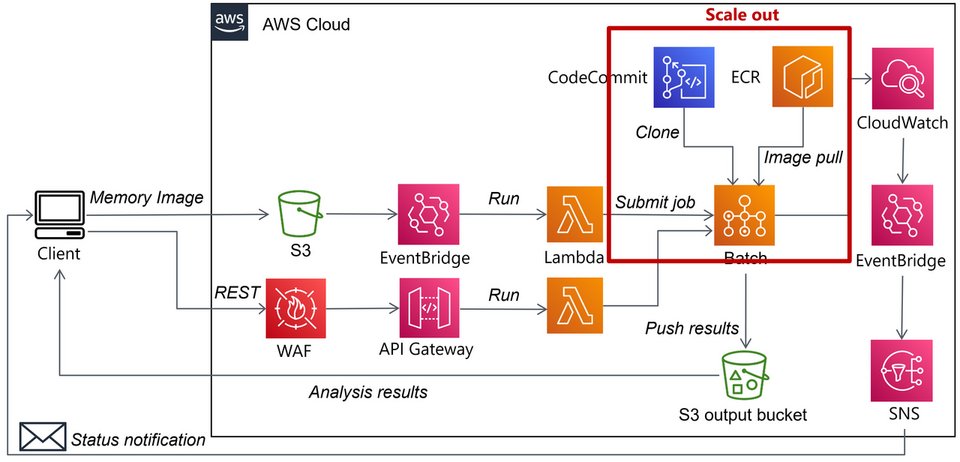
Automating Malware Analysis Operations (MAOps) blogs.jpcert.or.jp/en/2023/01/clo… #Pentesting #MalwareAnalysis #CyberSecurity #Infosec
FLARE floss applied to all unpacked+dumped samples in Malpedia Nice project by Daniel Plohmann (@push_pnx) Blog post: danielplohmann.github.io/blog/2024/03/0… Github repo: github.com/malpedia/malpe… #malwareanalysis #infosec


🦠💻Explore Part 2 of our Windows Malware blog series on process injections: 8ksec.io/dissecting-win… 📈Ready to sharpen your skills? Browse our courses here: academy.8ksec.io/course/practic… #MalwareAnalysis #Windows #ReverseEngineering

🔍 #Opendir Alert! 📂 Target: ⚠️ hxxps://m[.]bureaux[.]fr/ 📄 Sample Files: Advanced IP Scanner.exe AnyDesk.exe AnyDesk.apk ⚡ Repository contains .apk & .exe files. Handle with caution! 🛡️ 🎯 Potential resource for malware analysts. #CyberSecurity #MalwareAnalysis…
![cyberfeeddigest's tweet image. 🔍 #Opendir Alert!
📂 Target:
⚠️ hxxps://m[.]bureaux[.]fr/
📄 Sample Files:
Advanced IP Scanner.exe
AnyDesk.exe
AnyDesk.apk
⚡ Repository contains .apk & .exe files. Handle with caution! 🛡️
🎯 Potential resource for malware analysts.
#CyberSecurity #MalwareAnalysis…](https://pbs.twimg.com/media/GhhcEuqWoAAUj9f.jpg)
Happened to analyze a suspicious macOS file. A developer downloaded Git from a git lookalike domain. Turns out to be #AMOS :) Thanks to @obje tool Lulu @patrickwardle Check out for more in the thread #macos #malwareanalysis #malware #infostealer

🦠💻Discover three key ways malware leverages data encoding to evade detection: 8ksec.io/dissecting-win… 📈Want to deepen your expertise? Explore our courses here: academy.8ksec.io/course/practic… #MalwareAnalysis #Windows #ReverseEngineering
Faculty Updation Program on #CyberSecurity and #MalwareAnalysis at @iitropar (IIT Ropar) as part of @InfoSecAwa of @GoI_MeitY is scheduled from 24th to 28th Feb 2025. @mygovindia @_DigitalIndia @SecretaryMEITY @abhish18 @cdacindia @IndianCERT @NICMeity @PIB_MeitY


Something went wrong.
Something went wrong.
United States Trends
- 1. Good Thursday 26.8K posts
- 2. Merry Christmas 68.8K posts
- 3. #thursdayvibes 1,626 posts
- 4. Happy Friday Eve N/A
- 5. #thursdaymotivation 2,144 posts
- 6. #DMDCHARITY2025 1.72M posts
- 7. Hilux 7,793 posts
- 8. Halle Berry 3,828 posts
- 9. Toyota 27K posts
- 10. #PutThatInYourPipe N/A
- 11. Earl Campbell 2,286 posts
- 12. Omar 184K posts
- 13. Steve Cropper 8,163 posts
- 14. Metroid Prime 4 16.5K posts
- 15. #ALLOCATION 736K posts
- 16. The BIGGЕST 1.03M posts
- 17. Milo 13.2K posts
- 18. Cafe 174K posts
- 19. Rogan 32.4K posts
- 20. Mike Lindell 24.8K posts


















![K7CyberSecurity's tweet card. During a routine analysis at K7 Labs, we encountered a Python-based malware sample that uses multi-stage obfuscation. The de-obfuscated result […]](https://pbs.twimg.com/card_img/1996453678287654912/EN_wHrSx?format=jpg&name=orig)