#lateralmovement search results
🔍#LateralMovement #ThreatHunting Anomalies • Unsual use of RDP, PsExec, or WMI • Access from non-typical user accounts • Privelege escalation attempts • Access to multiple systems in short time • Unsual file sharing across hosts • Logins at odd hours or from new locations
By implementing effective offense and defense strategies, we can prevent their malicious efforts. Find out more in this blog by Matrium Managing Director, Trent Owens. #CyberSecurity #LateralMovement hubs.la/Q01ZnhXT0
Address security and compliance challenges such as supply chain threats and network blind spots with open source extended detection and response (XDR). #hids #lateralmovement #OSSEC #PCICompliance atomicorp.com/atomic-enterpr…
atomicorp.com
Endpoint Detection and Response (EDR) from Atomicorp - Atomic OSSEC
Atomic OSSEC endpoint detection and response (EDR) provides affordable protection and compliance through endpoint AV, FIM, CVE scanning, and more.
We’re thrilled to announce that Zero Networks has been named a finalist in the 2024 SC Awards (via @SCMagazine) for our innovative platform that halts #LateralMovement and blocks #Ransomware! 🚀 Read the press release here → hubs.li/Q02NQyLy0 #SCawards2024
Your segmentation fails when a SOCKS proxy and MS17-010 pivot deeper. Assume breach. #NetworkSecurity #LateralMovement #SOCKSProxy #network #networking #devsecops #devops #sysadmin #cisco #mikrotik #netgear valtersit.com/vault/2026/04/…
Abusing CI/CD Pipelines for #LateralMovement and #Persistence Continuous #Integration and Continuous #Deployment (CI/CD) pipelines have become essential for streamlining software development and delivery. CI/CD tools make it easier for development teams to collaborate and deploy

🚨 LIVE in 1 hour! Run PTH, Kerberoasting, and WinRM abuse in AD with guidance on how to spot each step. If you're learning AD internals, don’t miss this FREE workshop. 📅 10:00 AM ET 🔗 sans.org/u/1CAH #RedTeam #LateralMovement #ActiveDirectory #SEC565

aptm.in/protip/0086 - telnet zawsze warto mieć przy sobie! Nie tylko, żeby obejrzeć #StarWars czy podłączyć się do #BBS-a, ale i zdebugować sieciową usługę czy zwiększyć swoje możliwości #LateralMovement w sieci wewnętrznej klienta podczas #RedTeaming-u.
In this article, the Arista Threat Research team discusses techniques for #lateralmovement using #DLLhijacking. Our Arista NDR identified attacks involving initial access and lateral movement. Check out the blog for more information; bit.ly/3JVxCvX #ndr

Lateral movement lets attackers expand across networks to find sensitive data. Stamus Networks' open-source Suricata ruleset detects lateral movement in Microsoft Windows environments, helping secure your network. hubs.la/Q02_WY7J0 #LateralMovement #Suricata #OpenSource
To understand the environment and spread through the network, threat actors use #lateralmovement techniques. Here are 5 early warning signs of lateral movement during a #ransomware attack. Have a look! #ndr #ransomware
NetExec (nxc) enables penetration testers to execute commands remotely via SMB, WinRM, WMI, MSSQL, RDP using credentials, hashes, tickets, or certificates. Supports Pass-the-Hash, Pass-the-Ticket, and PKINIT. #NetExec #LateralMovement ift.tt/qn19do6
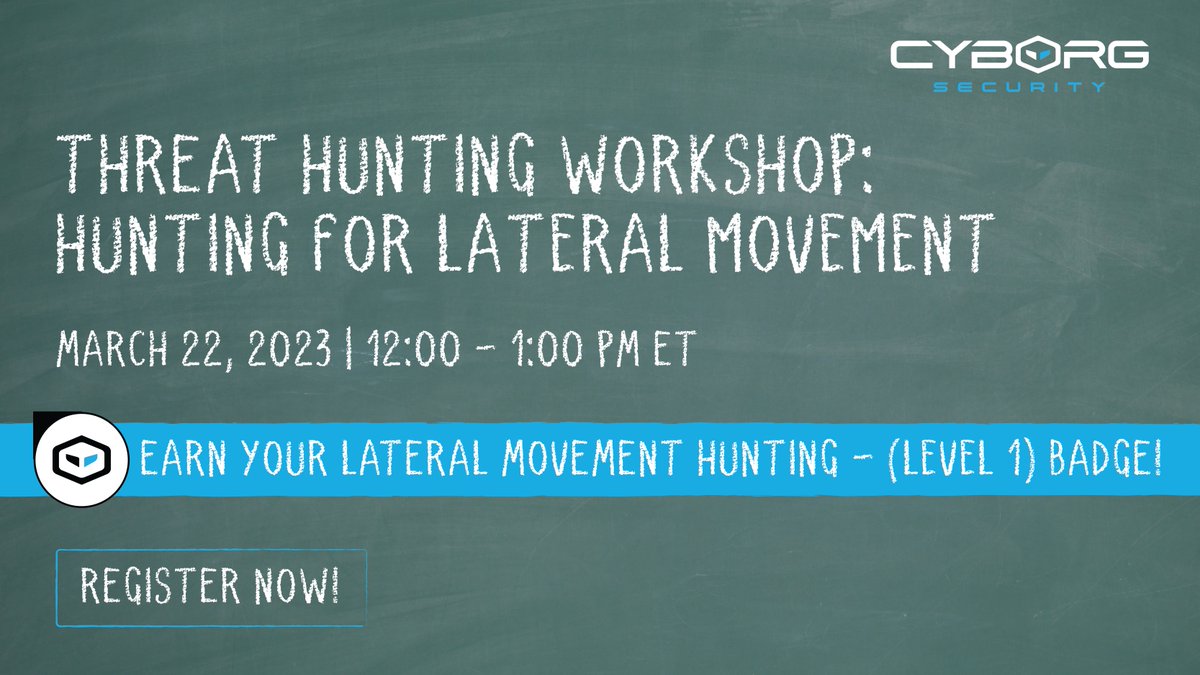
Join us for our fully interactive #LateralMovement workshop! Our expert threat hunters will guide you through the process of hunting for signs and traces of lateral movement in a realistic environment. Register now 👉 huntwithcyb.org/3Tn3FrP #threathunting #cybersecurity
Lateral Movement and Pivoting - I have just completed this room! Check it out: tryhackme.com/room/lateralmo… #tryhackme #redteam #lateralmovement #pivoting #windows #pass-the-hash #pass-the-ticket #overpass-the-hash #AD #lateralmovementandpivoting via @tryhackme
Mitigate lateral movement with Zero Trust access! Learn how Cisco's latest security measures combat threats in this informative blog post. hubs.ly/Q02q6FrN0 #ZeroTrust #Cybersecurity #LateralMovement
Once an attacker gains access to your network, they use that access to move deeper, explore the network & escalate their control. This process is called #lateralmovement. Learn everything you need to know about lateral movement and how to detect it here:

CVE-2026-6348 affects the WinMatrix agent by Simopro Technology, allowing an authenticated local attacker to execute arbitrary code. Assessed as Tier 2: high impact Full analysis: github.com/alan-turing-in… #cybersecurity #privilegeescalation #lateralmovement #cve
Are you concerned about #lateralmovement in your #cloudenvironment? 😰 We can help! Prisma Cloud provides granular visibility into cloud resources, allowing you to identify over-permissive privileges and take action to correct them. Learn more: bit.ly/42GA68G

CVE-2026-6348 affects the WinMatrix agent by Simopro Technology, allowing an authenticated local attacker to execute arbitrary code. Assessed as Tier 2: high impact Full analysis: github.com/alan-turing-in… #cybersecurity #privilegeescalation #lateralmovement #cve
Your segmentation fails when a SOCKS proxy and MS17-010 pivot deeper. Assume breach. #NetworkSecurity #LateralMovement #SOCKSProxy #network #networking #devsecops #devops #sysadmin #cisco #mikrotik #netgear valtersit.com/vault/2026/04/…
Micro-Segmentation and Network Controls to Reduce Lateral Movement beefed.ai/en/micro-segme… #Microsegmentation #LateralMovement #NetworkSegmentation #SoftwareDefinedPerimeter #EastwestTrafficControl
Most cyberattacks aren’t loud—they’re quiet. 😱 Lateral Movement lets hackers move silently through your network, escalating access until they reach critical systems. Learn how it works & how to stop it: youtu.be/fDy3G5BBkVI #Cybersecurity #OTSecurity #LateralMovement

youtube.com
YouTube
Archer
Telemetry source mapping (Event IDs, Sysmon, CloudTrail, auditd, EDR) Interactive D3FEND defensive technique diagrams per ATT&CK technique No server, no dependencies, no internet required. Open index.html in any modern browser. #lolbin #lateralmovement #mitre #d3fend #blueteam
NetExec (nxc) enables penetration testers to execute commands remotely via SMB, WinRM, WMI, MSSQL, RDP using credentials, hashes, tickets, or certificates. Supports Pass-the-Hash, Pass-the-Ticket, and PKINIT. #NetExec #LateralMovement ift.tt/qn19do6
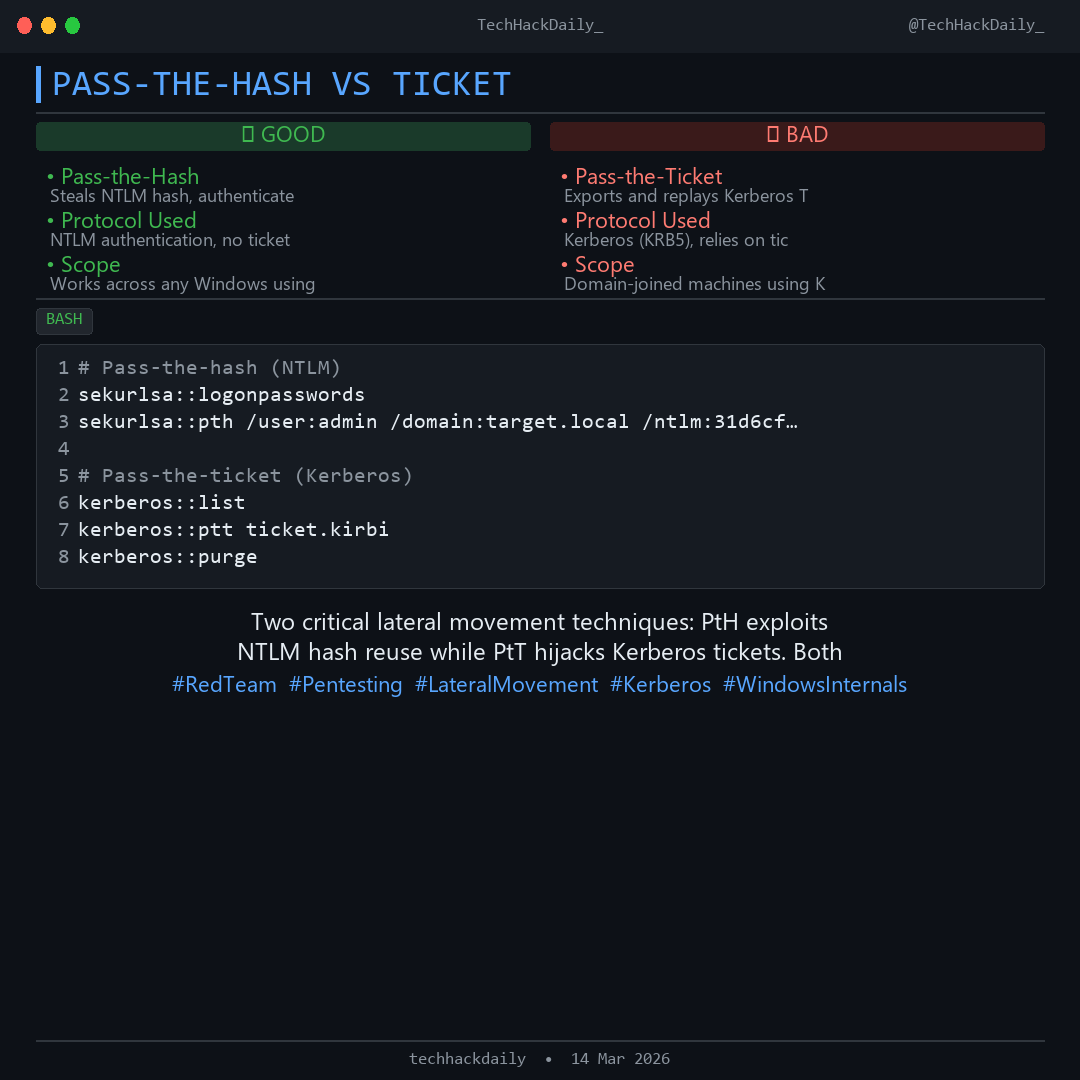
PASS-THE-HASH VS TICKET Two critical lateral movement techniques: PtH exploits NTLM hash reuse while PtT hijacks Kerberos tickets. Both bypass password re-entry by stealing authentication credentials. #RedTeam #Pentesting #LateralMovement #Kerberos #WindowsInternals
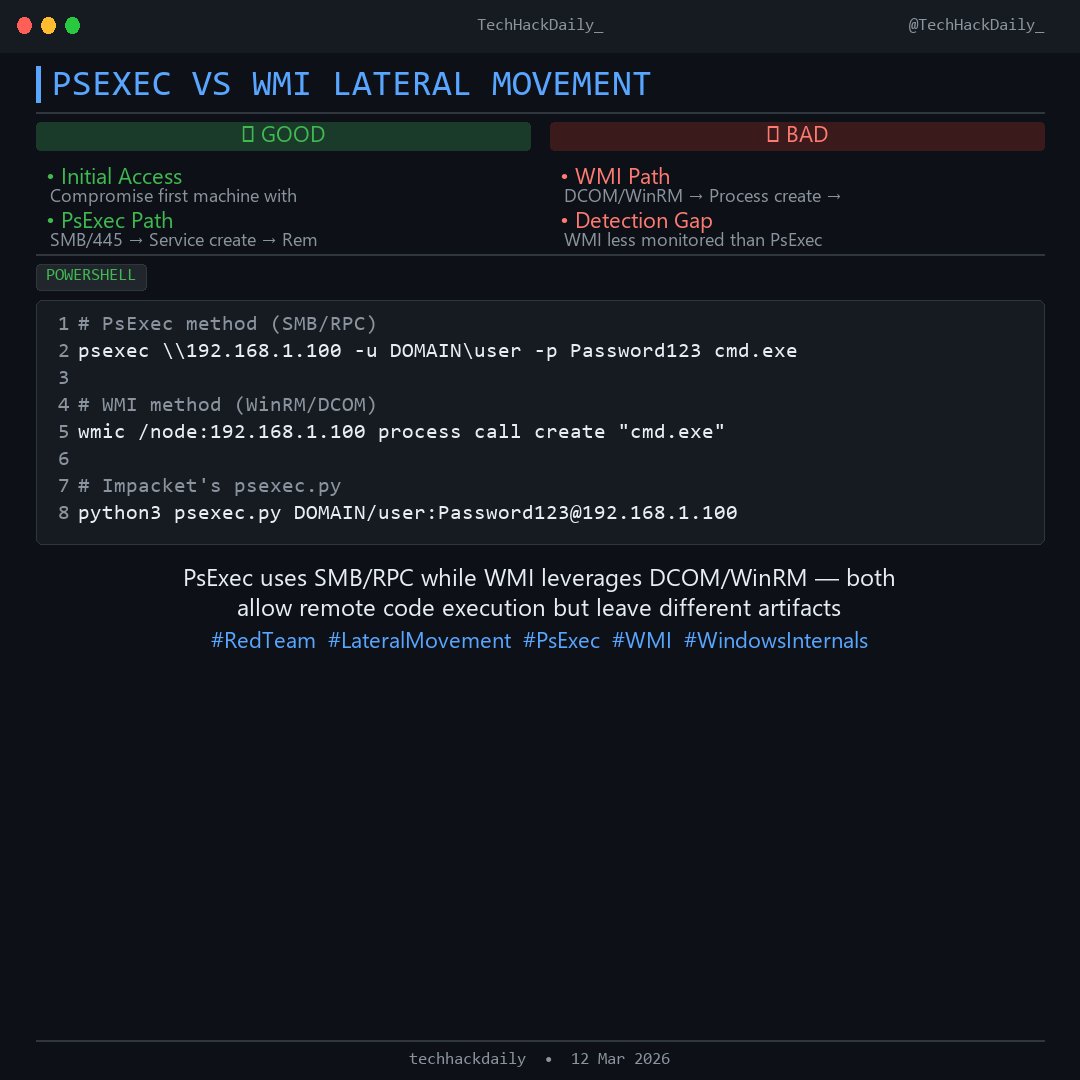
PSEXEC VS WMI LATERAL MOVEMENT PsExec uses SMB/RPC while WMI leverages DCOM/WinRM — both allow remote code execution but leave different artifacts on target systems, critical for threat hunting. #RedTeam #LateralMovement #PsExec #WMI #WindowsInternals
🚨 LIVE in 1 hour! Run PTH, Kerberoasting, and WinRM abuse in AD with guidance on how to spot each step. If you're learning AD internals, don’t miss this FREE workshop. 📅 10:00 AM ET 🔗 sans.org/u/1CAH #RedTeam #LateralMovement #ActiveDirectory #SEC565

Reused credentials make lateral movement easy for attackers. One shared password across VPN and payroll? That’s all it takes. Test beyond the perimeter. buff.ly/3GjvWfX #PentestTip #CredentialSecurity #LateralMovement #PenTesting #CyberSecurity #InfoSec

#DFIR It might be an good starting point if you want to set up your own Windows clean process baseline to compare with possible #Malware processes?. On the other hand you can find interesting Widows event IDs for #LateralMovement #RemoteExecution detection in your #SIEM.
🔎 Want to #ThreatHunt more effectively? Start by knowing what’s normal on a #Windows box. The Hunt Evil poster by @robtlee & @mikepilkington is your go-to process baseline resource. 📄 Download your copy today: sans.org/u/1Bp4 #DFIR

5/ Tactic 4: Lateral Movement: Using SSH, ICMP, DNS, and GTP, attackers slipped through to SGSN nodes. Blue Teams, monitor these for odd traffic. #LateralMovement #GTP
Just earned the Credential Access, Discovery, Lateral Movement & Collection cert from INFOSEC🛡️ #CyberSecurity #Infosec #LateralMovement #CredentialAccess #BlueTeam #InfoSecCertified #CyberDefense #HackerHunting #TechX Check out my certification: coursera.org/share/fe13e92f…
🚨 New Blog Alert! Ever wondered how attackers move across networks undetected? Our latest blog breaks down Multi-Hop Pivoting with Ligolo-ng like never before! 💻 🔗 Check it out now: cyberwarfare.live/lateral-moveme… #LateralMovement #LigoloNG #RedTeamOps #CyberSecurityBlog #CWL

From @StamusNetworks: A free #Suricata ruleset to detect lateral movement inside the network - PsExec, WMI, service creation & more. Built by researchers. Easy to deploy. Get the ruleset and full documentation: hubs.la/Q03vjDbT0 #ThreatDetection #LateralMovement
🧠 Inside an attacker's mind: lateral movement. 🔓 From one compromised device to full domain control—hackers use trust, permissions & stealth to climb. See how Dela IEM detects, disrupts, and traps them before it's too late. ➡️ youtu.be/sGXRBiJvq_Q #DelaIEM #LateralMovement

youtube.com
YouTube
Inside an Attacker’s Mind: Lateral Movement (Dela IEM)
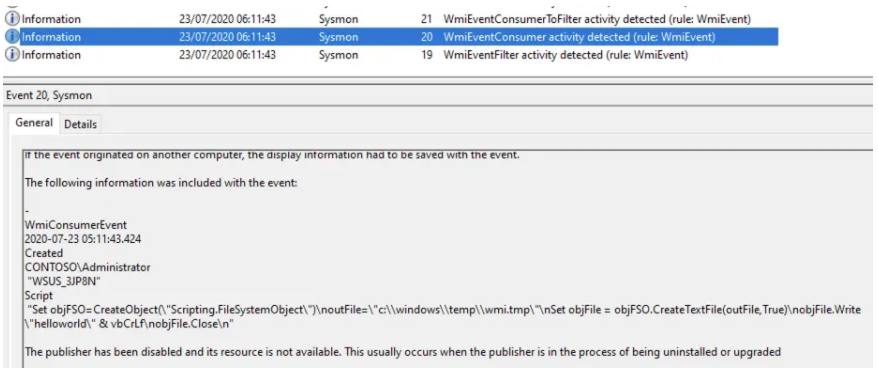
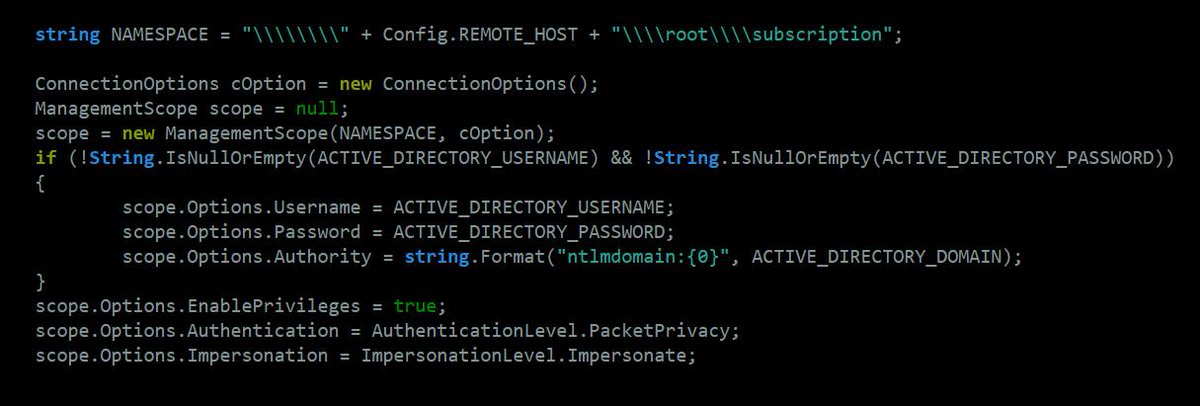
Excellent writeup by @cybergentix on #WMI #LateralMovement Didn't mention mitigation via #RPCFirewall, which could be achieved by blocking remote #DCOM operations blog.fndsec.net/2024/09/11/wmi…
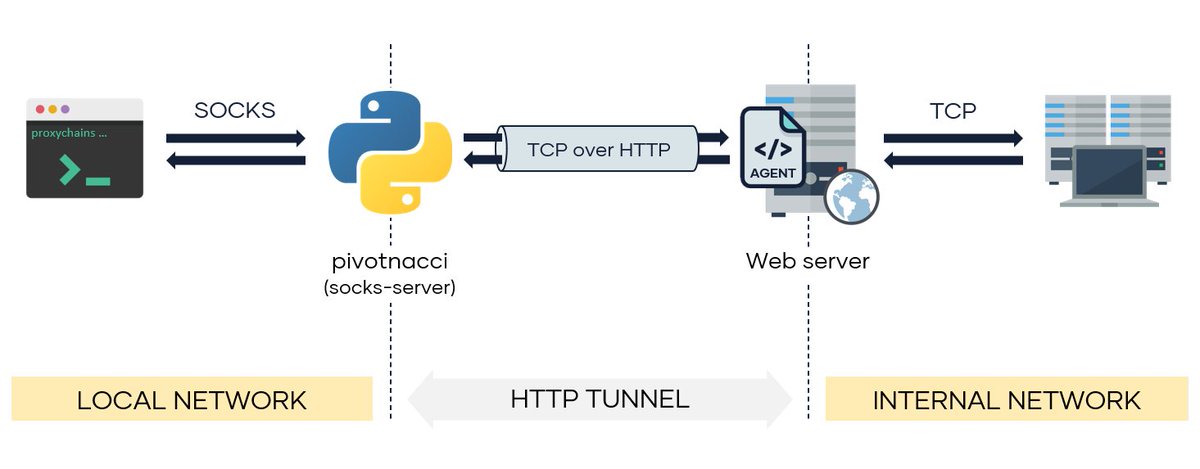
Pivotnacci - A Tool To Make Socks Connections Through HTTP Agents j.mp/2zAYArN #Aspx #LateralMovement #Pivotnacci #Socks
Want to detect and prevent #LateralMovement attacks in real time? Learn how @CrowdStrike #IdentityProtection can help: bit.ly/3ueLgzL

Everyone’s talking about #ZeroTrust, but what does it mean for identity? Watch this demo to find out: bit.ly/3sBhQeE #lateralmovement #conditionalaccess #identityprotection

See how Falcon #ZeroTrust can detect #LateralMovement threats without relying on logs or complex correlation rules: bit.ly/3wjRjUA #cybersecurity

CrowdStrike #Falcon Identity Protection detects & prevents #LateralMovement. Watch video to learn more: bit.ly/3Jc5QsX

Watch this simulation of a real attack to learn how to set up blocking policies to prevent lateral movement → bit.ly/2P7ZX8w #Falcon #ZeroTrust #LateralMovement #AD #DemoTuesday

packetStrider - A Network Packet Forensics Tool For SSH j.mp/2Ok6qgv #golang #HASSH #LateralMovement #MachineLearning #Metadata
Good article #mustRead [Article] Lateral movement risks in the cloud and how to prevent them – Part 1: the network layer (VPC) buff.ly/3gw58gg #LateralMovement #VPC #Networking #CyberSecurity
![david_das_neves's tweet image. Good article #mustRead
[Article] Lateral movement risks in the cloud and how to prevent them – Part 1: the network layer (VPC)
buff.ly/3gw58gg
#LateralMovement #VPC #Networking #CyberSecurity](https://pbs.twimg.com/media/FfxTPKuWYAEyuY9.jpg)
🚨 LIVE in 1 hour! Run PTH, Kerberoasting, and WinRM abuse in AD with guidance on how to spot each step. If you're learning AD internals, don’t miss this FREE workshop. 📅 10:00 AM ET 🔗 sans.org/u/1CAH #RedTeam #LateralMovement #ActiveDirectory #SEC565

Good read for pentesters - P.S.: already integrated in Mimikatz [Article] Dumping Plaintext RDP credentials from svchost.exe n00py.io/2021/05/dumpin… #Pentesting #Credentials #LateralMovement
![david_das_neves's tweet image. Good read for pentesters - P.S.: already integrated in Mimikatz
[Article] Dumping Plaintext RDP credentials from svchost.exe
n00py.io/2021/05/dumpin…
#Pentesting #Credentials #LateralMovement](https://pbs.twimg.com/media/E2S8L4CXoAEBJjk.jpg)
Fantastic article by Huy - for my redteamers/pentesters [Article] Lateral Movement With Managed Identities Of Azure Virtual Machines buff.ly/3Fxxe2c #MicrosoftAzure #CyberSecurity #LateralMovement
![david_das_neves's tweet image. Fantastic article by Huy - for my redteamers/pentesters
[Article] Lateral Movement With Managed Identities Of Azure Virtual Machines
buff.ly/3Fxxe2c
#MicrosoftAzure #CyberSecurity #LateralMovement](https://pbs.twimg.com/media/FHrlMmxXsAImhTz.jpg)
¿Cómo ven los atacantes al Directorio Activo? Recuerden que todas las cuentas pueden volverse privilegiadas en algun momento. #LateralMovement #PrivilegeEscalation #CrownJewels

Cos’è il #LateralMovement? È una tecnica di #attacco #cyber in cui dall'utente 0 ci si muove nella rete per accedere a informazioni più sensibili. Come si blocca? Con software automatici e l’analisi della rete da parte di tecnici specializzati, soprattutto, sugli #endpoint.

Good overview [Article] Lateral Movement Detection with Windows Event Logs buff.ly/3nWCSU5 #LateralMovement #Event #CyberSecurity
![david_das_neves's tweet image. Good overview
[Article] Lateral Movement Detection with Windows Event Logs
buff.ly/3nWCSU5
#LateralMovement #Event #CyberSecurity](https://pbs.twimg.com/media/FDXbK9LXIAM_huK.png)
Join @Regiteric on 5 July at 14:35 CET at @passthesaltcon in #Lille for a talk on how you can use #Suricata to detect #lateralmovement in #Windows environment, including the SMB lateral ruleset by Stamus Networks. Learn more and reserve your seat here: hubs.la/Q01VX0Kp0

#InfoSec professionals are aware of the Principle of Least Privilege. So why has it become a lost art? Read more about how #PoLP can reduce #lateralmovement risk and make #incidentresponse easier in a blog post from Chief Strategy Officer @jdsherry: cnto.io/On2pUjAir

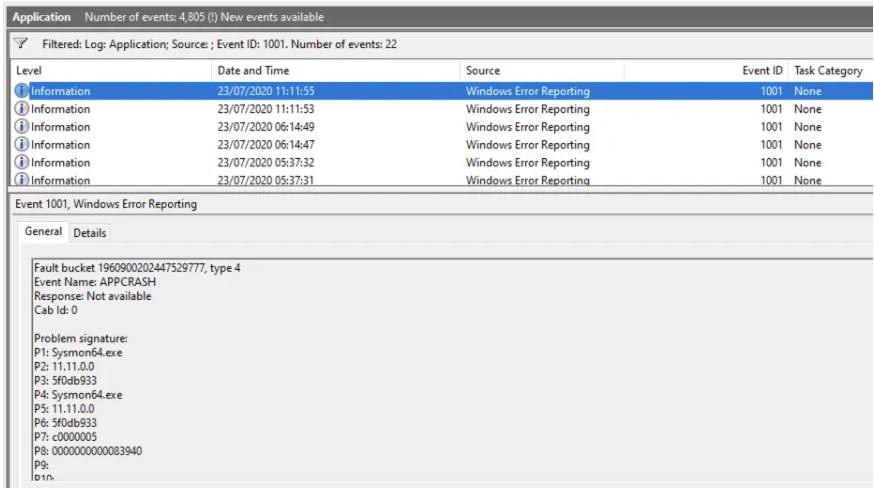
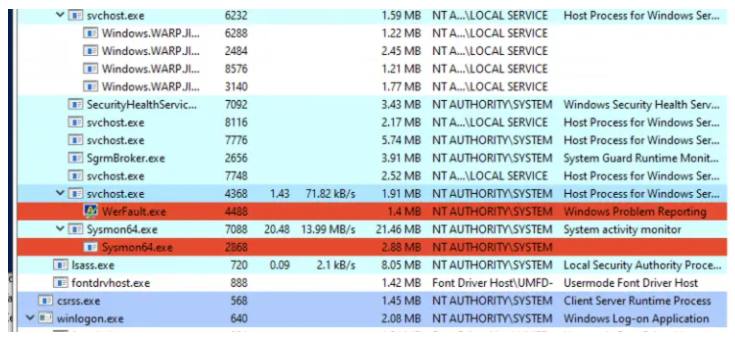
#RedTeaming: I Like To Move It, #Windows #LateralMovement Pt1 #WMIEvent Subscription - bit.ly/2DEhGPI-Ttx @domchell @Cyb3rWard0g via @MDSecLabs 𝞝 #Organizations #Enterprises #CyberThreats #PenTesting #InfoSec #CyberSecurity #CyberSecurity #OpSec #ITsecurity #CyberDefense
Mike Rogers, Senior Advisor at @Team8Group, and former @NSA Director and retired Admiral of the @USNavy, gives insights on how attackers view #lateralmovement and the importance of understanding their POV. To watch the full video visit: okt.to/tCJ8EK

Lateral Movement with MSSQL - with Detection and Response guide [Article] MSSQL Lateral Movement research.nccgroup.com/2021/01/21/mss… #MSSQL #LateralMovement #CyberSecurity
![david_das_neves's tweet image. Lateral Movement with MSSQL - with Detection and Response guide
[Article] MSSQL Lateral Movement
research.nccgroup.com/2021/01/21/mss…
#MSSQL #LateralMovement #CyberSecurity](https://pbs.twimg.com/media/EsVN-qbXMAAgt97.jpg)
Good overview [Article] Alternative ways to Pass the Hash (PtH) n00py.io/2020/12/altern… #PTH #LateralMovement #CyberSecurity
![david_das_neves's tweet image. Good overview
[Article] Alternative ways to Pass the Hash (PtH)
n00py.io/2020/12/altern…
#PTH #LateralMovement #CyberSecurity](https://pbs.twimg.com/media/E2Tke6tWQAE-IjE.jpg)
Something went wrong.
Something went wrong.
United States Trends
- 1. #CashAppFriday N/A
- 2. Taco Tuesday N/A
- 3. Save America Act N/A
- 4. Matt Ryan N/A
- 5. Brighton N/A
- 6. Oona N/A
- 7. Virginia N/A
- 8. Game Pass N/A
- 9. #BHACHE N/A
- 10. Tucker N/A
- 11. Payton N/A
- 12. Call of Duty N/A
- 13. Rosenior N/A
- 14. Tifa N/A
- 15. Michael N/A
- 16. Jeter N/A
- 17. FEMA N/A
- 18. Warsh N/A
- 19. Chris Murphy N/A
- 20. ChatGPT Images 2.0 N/A