#authorization search results
Tokens in the flow, Guarding paths with silent code, Access granted, safe. #Haiku #Authorization #CodePoetry #DevHaiku #CodingLife #TechHaiku #CodeArt #DeveloperWisdom #CodingPoetry #ProgrammersLife #HaikuOfCode

#AI Agents Are Becoming #Authorization Bypass Paths buff.ly/DGgdVHI @TheHackersNews #tech #AgenticAI #IAM #PAM #NHI #identity #identitymanagement #accessmanagement #governance #CIO #CTO #CISO #cybersecurity #leadership #cyberthreats #cyberattacks #databreaches
How to Set Up #Authorization in a Bookstore Management System with Go, HTMX, and Permit.io #golang #dormosheio #htmx dormoshe.io/trending-news/…
dormoshe.io
How to Set Up Authorization in a Bookstore Management System with Go, HTMX, and Permit.io
Authorization is important when building applications, as it determines what actions and resources a user is allowed to access after they authenticate. In this article, we'll take a look at how to ...
The Rise of AI Agents and the Growing Need for Stronger Authorization Controls cysecurity.news/2025/10/the-ri… #aiagents #authorization #Cybersecurity

Grantex: Delegated Authorization Protocol for AI Agents (Source: GitHub) Grantex is an open standard for managing AI agent permissions, providing a framework for granting, scoping, revoking, and auditing access. #AI #Security #Authorization #OAuth #Agents 🤔 How can we ensure
dailyaiwire.news
Grantex: Delegated Authorization Protocol for AI Agents
Grantex is an open standard for managing AI agent permissions, providing a framework for granting, scoping, revoking, and auditing access.
See how continuous, context-aware policy decisions can constrain autonomous tool use—without embedding brittle authorization logic inside the agent. - hackernoon.com/authorization-… #openclaw #authorization
How do API Keys, OAuth 2.0, JWT, and others stack up? Here’s a simple visual on common authorization methods: - API Keys - Basic Auth - OAuth 2.0 - JWT - OpenID Connect - mTLS Secure your APIs the right way. #MasteringBackend #API #authorization

IBBI Disciplinary Committee Suspends Insolvency Professional’s Authorization for Six Months for Acting Without Valid AFA [Read Order] taxscan.in/top-stories/ib… #ibbi #authorization #insolvency #TaxNews #taxscan
Fine-grained authorization is crucial for managing agent behavior. Without proper guardrails, agents can exhaust all possibilities, posing risks. How can sandboxing serve as a reliable safety measure? #Authorization #AgentSafety #Sandboxing
Trump Confirms CIA Authorization in Venezuela Amid Rising Tensions with Maduro youtu.be/N-e7EztFFlM #Trump #CIA #Authorization #Venezuela #Tensions #Maduro #Politics #InternationalRelations #NewsUpdate #GlobalPolitics #USForeignPolicy #SouthAmerica #VenezuelanCrisis

youtube.com
YouTube
Mirror7 News | Breaking News
🎙️ New Chat! Matthias Reinwarth sits down with Martin Kuppinger and Jonathan Care to unpack the emerging concept of AIdentity and why it's the key to securing agentic AI. Watch in full: okt.to/2Xnd1Y #AIdentity #AgenticAI #Authorization
The Looming #Authorization Crisis >> Why Traditional #IAM Fails Agentic #AI buff.ly/qZWj5Hk #tech #identity #cybersecurity #identitymanagement #PAM #NHI #cyberthreats #databreaches #business #leadership #management #CISO #CIO #CTO #AgenticAI @CyberDefenseMag

Supreme Court upholds Penalty for Violating EOU Scheme by Removing Duty-Free Capital Goods without Authorization [Read Judgement] #SupremeCourt #Penalty #Authorization #taxscan #taxnews Read more: taxscan.in/top-stories/su…
![tax_scan's tweet image. Supreme Court upholds Penalty for Violating EOU Scheme by Removing Duty-Free Capital Goods without Authorization [Read Judgement]
#SupremeCourt #Penalty #Authorization #taxscan #taxnews
Read more: taxscan.in/top-stories/su…](https://pbs.twimg.com/media/G4ZDi7SXQAAHc0N.jpg)
New #AI means new identity challenges. Join @jcmartinezdev, Nelson Matias, & @eddiejaoude for a power-packed masterclass on securing AI apps + agents. ✅ Fortify against AI vulnerabilities 🔐 Master agent #authorization 🤖 Build AI trust & governance Register below ⬇️

DGFT Amends Para 4.84 of HBP 2023: Advance Authorisation Holders Barred from Importing Gold as Replenishment [Read Notice] #DGFT #Authorization #Gold #taxscan #taxnews Read more: taxscan.in/top-stories/dg…
taxscan.in
DGFT Amends Para 4.84 of HBP 2023: Advance Authorisation Holders Barred from Importing Gold as...
The amendment removes the provision allowing import of gold as replenishment under Advance Authorisation, aligning procedural timelines with the Foreign Trade Policy 2023.
Shukra Pharmaceuticals Ltd receives authorization from Univlabs Technologies Pvt. Ltd. #ShukraPharmaceuticals #Authorization #UnivlabsTechnologies equitybulls.com/category.php?i…
equitybulls.com
Shukra Pharmaceuticals Ltd receives authorization from Univlabs Technologies Pvt. Ltd.
Shukra Pharmaceuticals Limited has been authorised by Univlabs Technologies Pvt. Ltd., an established and reputable manufacturer of Laparoscopic Sets.
Clearmind initiates U.S. clinical site for CMND-100 #trial as Filament announces FDA #authorization of Phase 2 study. Catch up in "Psychedelic" weekly from @theflynews $CMND $FLHLF $ATAI $AGNPF $RVVTF tinyurl.com/2tys5rjj
📣 New Podcast! "Barred Spiral Discoveries and Spirit's Final Mission: A Cosmic Journey Unfolds" on @Spreaker #american #astronomical #authorization #barred spreaker.com/episode/barred…
spreaker.com
Spreaker Podcasts
Barred Spiral Discoveries and Spirit's Final Mission: A Cosmic...
Tokens in the flow, Guarding paths with silent code, Access granted, safe. #Haiku #Authorization #CodePoetry #DevHaiku #CodingLife #TechHaiku #CodeArt #DeveloperWisdom #CodingPoetry #ProgrammersLife #HaikuOfCode
The hard part of #authorization is translating "editors can update posts in their department, admins can't touch customer records" into a precise spec We built an agent skill that does it for you. Plain language in, full Cerbos #policy bundle out Guide: bit.ly/492TQbD

🎙️ New Chat! Matthias Reinwarth sits down with Martin Kuppinger and Jonathan Care to unpack the emerging concept of AIdentity and why it's the key to securing agentic AI. Watch in full: okt.to/2Xnd1Y #AIdentity #AgenticAI #Authorization
`GoAuthentik` has an insufficient authorization vulnerability (CVE-2024-42490) impacting API endpoints. This may lead to unauthorized data access or manipulation. Review API access logs. #infosec #authentication #authorization pulsepatch.io/posts/cve-2024…
#Commander Sadiq Doodishe has issued a strict order regarding the protests that took place in the city of #Baidoa, stating that no demonstration can be held without official #authorization.
OWASP found 100% of apps tested had broken access control. Add AI agents (adoption jumped from 11% to 42% in 2025) and fragmented #authorization becomes an #incidentresponse nightmare. Here's how centralized policy governance fixes it 👇 bit.ly/41FOFdK

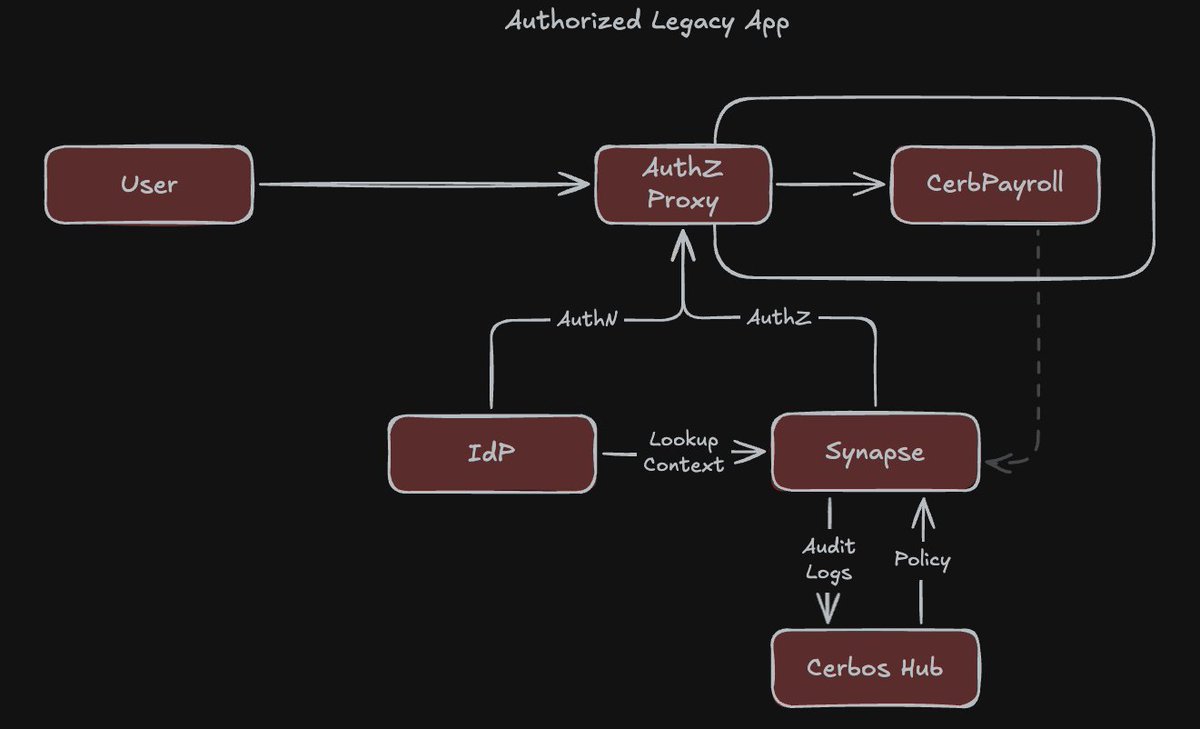
Cerbos Newsletter April 2026 📢 bit.ly/4enQweH ✅Cerbos Synapse - context for #authorization decisions ✅#IAM security checklist for 2026 ✅Authz for #legacyapps ✅Authorization policy for #utilities ✅Blind spots auditors flag Subscribe: bit.ly/3MGNwuW

Legacy app authorization never gets fixed because engineering can't modify the app and security can't govern what they can't see. Cerbos Synapse puts an #authorization layer in front of it instead. No code changes, no rewrite. Walkthrough 👉 bit.ly/3Q0zQjx #Legacyapp
🔑 JWT Tokens Stateless authorization using tokens for scalable, secure authentication in modern apps. 🔗 pixelburn.tech/en/jwt-token-e… 🔖 #JWT #authentication #authorization #security #API
may be punished by death with. There will be no martial court for US soldiers. All will be executed if enters Iran territory. Must be done with superpower opening whatever it costs after deescalation and UN #authorization.
Continue karte hai authenticaton ki kahani.. #ChaiAuthProMax #Authentication #Authorization @ChaiCodeHQ @Hiteshdotcom @nirudhuuu @piyushgarg_dev @BlazeisCoding @surajtwt_

Day 31: WebDev Cohort 2026 Topics covered: Authentication and Authorisation, Bcrypt, Nodemailer, Logout service, How to send verification mail #ChaiAuthProMax #Authentication #Authorization @Hiteshdotcom @ChaiCodeHQ @nirudhuuu @piyushgarg_dev @BlazeisCoding @surajtwt_

Day 31: WebDev Cohort 2026 Topics covered: Authentication and Authorisation, Bcrypt, Nodemailer, Logout service, How to send verification mail #ChaiAuthProMax #Authentication #Authorization @Hiteshdotcom @ChaiCodeHQ @nirudhuuu @piyushgarg_dev @BlazeisCoding @surajtwt_

Authentication = WHO you are. Authorization = WHAT you can do. Still mixing them up? Clear breakdown with examples 👇 sslinsights.com/authentication… #Authentication #Authorization #CyberSecurity #AppSecurity #WebDev #OAuth #SSLInsights
Why #authentication and #authorization are becoming central to enterprise #security - bit.ly/4bNChNw | #technews #technology #futuretech
Authentication vs Authorization. Authentication → Who are you? Authorization → What can you do? Login verifies identity. Permissions control access. Both are required for secure applications. #Authentication #Authorization #FullStack #Nodejs #WebSecurity #MERNStack



Authentication and Authorization in ASP.NET Core Technotonics | 2026 #ASPNetCore #Authentication #Authorization #WebSecurity #DotNet #CSharp #JWT #BackendDevelopment #ProgrammingTutorial #TechnoTonicsAssignment #TechnoTonics
100+ permissions in my SaaS. Zero in AuthServiceProvider. All defined in one config file. All auto-registered as Gates on boot. Sync with `php artisan permissions:sync`. Done. #LaraFoundry #Laravel #Authorization #BuildInPublic
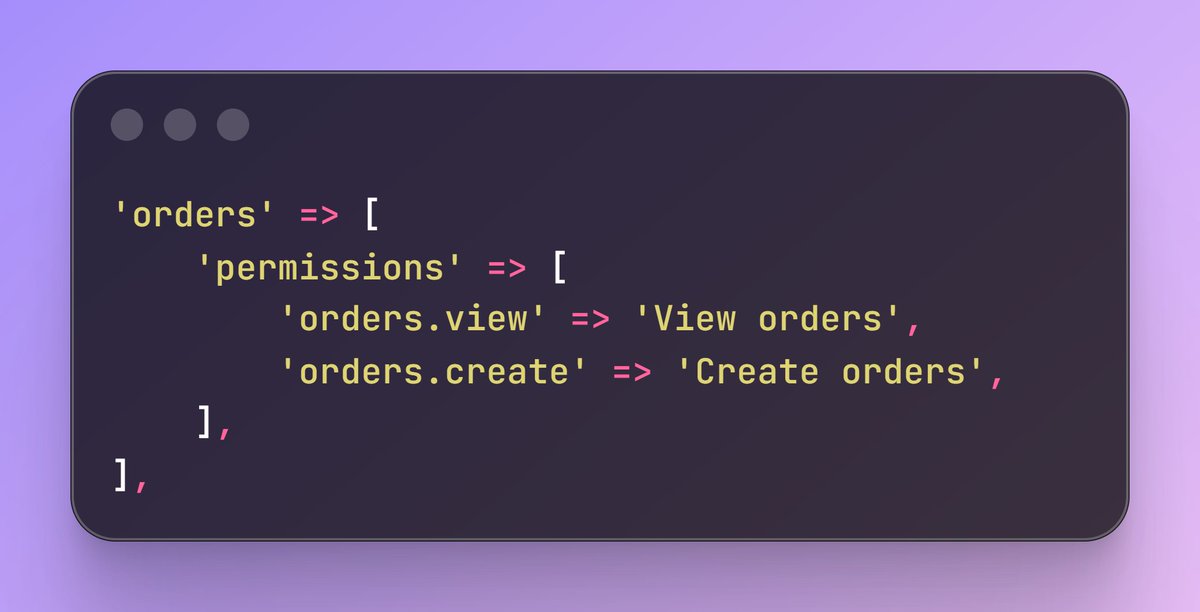
I’m building LaraFoundry in public - the modular SaaS engine for Laravel. Rebuilding auth, roles, and multi-tenancy every time is a waste. So I’m creating a battle-tested core to skip the boring stuff. 🛠️ First 3 modules are officially DONE. > Moving to the next ones! Follow
Authentication = who you are. Authorization = what you can do ✅ Understanding the difference is foundational to secure app design. Full guide: sslinsights.com/authentication… #Authentication #Authorization #CyberSecurity #AppSecurity #SSLInsights

Authentication verifies identity, while authorization defines access. Together, they form the backbone of modern cybersecurity. Read more - cybrpro.com/authorization-… #CyberSecurity #Authentication #Authorization #DigitalSecurity #CybrPro #cyberpromagazine

The Rise of AI Agents and the Growing Need for Stronger Authorization Controls cysecurity.news/2025/10/the-ri… #aiagents #authorization #Cybersecurity

New #AI means new identity challenges. Join @jcmartinezdev, Nelson Matias, & @eddiejaoude for a power-packed masterclass on securing AI apps + agents. ✅ Fortify against AI vulnerabilities 🔐 Master agent #authorization 🤖 Build AI trust & governance Register below ⬇️

Here’s how credit cards are protected: 🛡️ EMV chips that provide a unique code each time you buy 🛡️ AI and machine learning to analyze the legitimacy of the transactions 🛡️ A 4-digit number printed above the account number as additional #authorization 🫶 Follow for more.

🌐 Adam Rusbridge from @pingidentity explores how authorization works in the context of shared finance 🔄 Learn more on how to leverage #authorization for financial empowerment 👥💡 thepaypers.com/thought-leader…

Join our #Webinar led by Rodney Gullatte Jr., where he will shed light on balancing #HolisticSecurity with proper #Authorization through #PenetrationTesting. Register now: buff.ly/4fwwGeN #ECCouncil #Cybersecurity #PenTesting #PenetrationTester #EthicalHacker

🚨 LIVE in 1 hour! See how GenAI agents act on user behalf and the security implications that follow. MCP, delegation, and authorization with Ahmed Abugharbia. 📅 1:00 PM EST 🔗 buff.ly/5Bs78iF #GenAI #AppSec #Authorization #SEC545
Excited for #KubeCon + #CloudNativeCon 2024? Check out this @VMblog Q&A with Gabriel Manor of @permit_io on fine-grained #authorization & what's in store at their booth! 🎤👨💻 Learn how they're shaping the future of cloud security. vmblog.com/archive/2024/1… #Kubernetes

Addressing challenges in #authorization processes and reimbursement complexity to combat #provider abrasion! 🤝⚕️ Proactive strategies pave the way to operational and financial triumph, enhancing #STARratings. Learn more: hubs.ly/Q02bH1W40 🚀

CISOs consider zero trust a hot security ticket - helpnetsecurity.com/2023/07/28/zer… - @plainID_authZ #ZeroTrust #authorization #CyberSecurity #netsec #security #InfoSecurity #CISO #ITsecurity #CyberSecurityNews #SecurityNews

It's Day 2 of Launch Week! 🎉 Today, we're excited to launch the Warrant Query Language (WQL), a declarative, SQL-like language to query Warrant for lists of access controlled data from the context of an application. #launch #devtools #authorization #accesscontrol #opensource

⚙️ GenAI agents need controls, not just prompts. Join Ahmed Abugharbia to explore MCP, secure delegation, and the critical role of authN/authZ in agent-driven AI systems. 📅 Jan 20 | 1:00 PM EST 🔗 buff.ly/5Bs78iF #GenAI #AppSec #Authorization #SEC545 #AIArchitecture
Learn Crypto with BitVenus #APIKey #Authentication #Authorization #Cybersecurity #DataSecurity #APISecurity #DigitalSecurity #AuthenticationCodes #CryptographicSignatures #OnlineSecurity #Cyberattacks #FinancialLoss #DataProtection

'Google Pay is a mere third-party app provider, no authorization required from RBI'; Delhi HC dismisses PIL to cease Google Pay's operations scconline.com/blog/post/2023… #DelhiHighCourt #authorization #GooglePay #npci #UPI #reservebankofindia #GPay #GooglePayIndia #scconline #SCC

If you want to learn more about #authentication and #authorization concepts in AI Agents with #SemanticKernel, #Auth0, and #OpenFGA, watch my latest video: youtu.be/HPheV5OTf0c?si… #AI #Identity

Thank you @okta and @auth0 for a nice gift! The town of IAMdale has just arrived. :) #Identity #Authentication #Authorization

Proposed DHS Rule Would Revise Asylum‑Based Work Authorization Eligibility: Employer Considerations natlawreview.com/article/propos… #DHS #authorization #asylum #employer @GT_Law

One of the most secure #authorization services that enable #SSO features is #Keycloak. We've used it in several projects for our clients and summed up our know-how in one comprehensive analysis of Keycloak implementation 👉 bit.ly/3PiraAL #security #iam

The @openid #AuthZEN interop event at @FIDOAlliance #Authenticate2024 was a great success! 🌟 11 implementations conform with AuthZEN 1.1 🌟 3 more 1.0-compliant implementations are in the process of supporting 1.1 🌟 2 ReBAC-centric around the corner #authorization at #FIDO



Learn how to control access in Ambient Mesh! 🌟 Free, on-demand lab includes: ✔️ Managing Kubernetes workloads ✔️ Enforcing Layer 4 policies ✔️ Implementing Layer 7 policies Start now: solo.io/resources/lab/… #ServiceMesh #Authorization #CloudNative

Something went wrong.
Something went wrong.
United States Trends
- 1. Good Thursday N/A
- 2. #TexasHockey N/A
- 3. Atreus N/A
- 4. Caruso N/A
- 5. And the Lord N/A
- 6. #mnwild N/A
- 7. Draft Day N/A
- 8. Counseling N/A
- 9. Devin Booker N/A
- 10. Benn N/A
- 11. Stars N/A
- 12. Leftover N/A
- 13. Double OT N/A
- 14. Dillon Brooks N/A
- 15. #beyondthevilla N/A
- 16. #Survivor50 N/A
- 17. Jalen Williams N/A
- 18. Quinn Hughes N/A
- 19. Boldy N/A
- 20. JDub N/A