#mitreattack search results
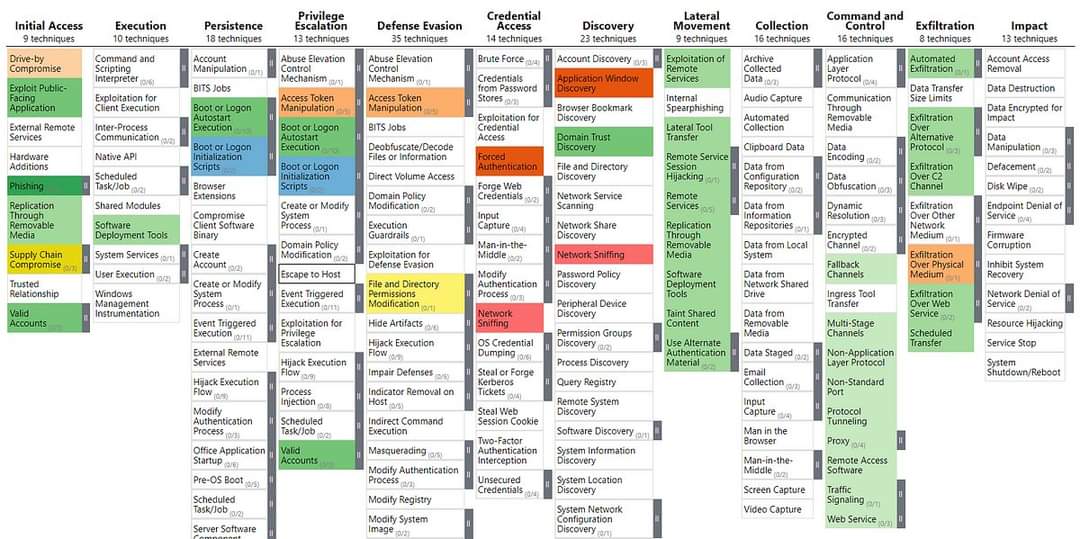
Game-changer for SecTeams! 🚀 Kaspersky just dropped a transparent MITRE ATT&CK® Coverage Map. See your defense gaps before the attackers do. See the Map → kas.pr/pq6z #MITREATTACK #CyberSecurity #ThreatIntelligence #ThreatIntel #InfoSec #Kaspersky #OpenTIP
Mapping to #MITREATTACK is the first step. Ensuring your defenses are truly active and effective—that’s where real resilience begins! Join Pete Constantine (CPO, @preludeorg Security) and Todd Cramer (Sr. Director, Security Ecosystem, Intel) for a live technical session on how
ATT&CK makes detection engineering measurable by mapping real TTPs to your content, exposing visibility gaps attackers rely on to stay hidden. - hackernoon.com/why-the-mitre-… #mitreattandck #mitreattack
hackernoon.com
Why the MITRE ATT&CK Framework Actually Works | HackerNoon
ATT&CK makes detection engineering measurable by mapping real TTPs to your content, exposing visibility gaps attackers rely on to stay hidden.
The MITRE ATT&CK framework turns alert noise into clarity. 🎯 Map real adversary behavior 🛠️ Uncover gaps 📊 Structure investigations Tag alerts with ATT&CK IDs to boost speed and precision. 💬 Got a tip? Share it below ⬇️ #CyberDefenders #MITREATTACK #DFIR #ThreatDetection

🚨 Kali Linux 2025.2 est là ! Nouveau menu basé sur le MITRE ATT&CK 🔍 Outils mieux classés, + de lisibilité pour les pros de la cybersécurité 👉 it-connect.fr/kali-linux-202… #KaliLinux #MITREATTACK #Linux #Cybersecurity #Pentest #Hacking #IT
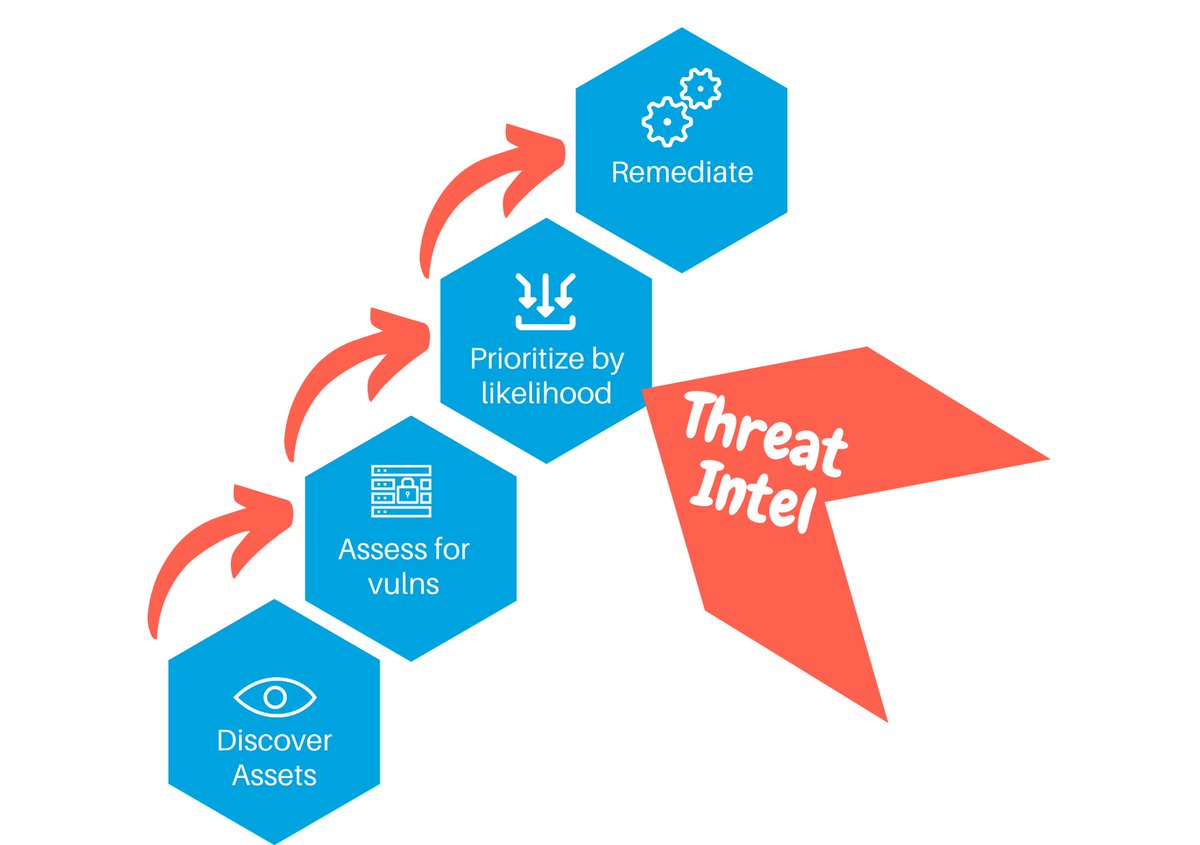
Effective detection hinges on prioritizing critical assets and attack paths over broad coverage. Leveraging threat modeling and strategic metrics demonstrates cybersecurity’s impact to leadership. #AttackPaths #DetectionFocus #MITREATTACK ift.tt/cPgBfRL
WatchGuard’s results in the @MITREattack Round 7 Evaluation highlight how far we’ve come in our mission to deliver strong security that’s easy to use. See the full MITRE ER7 results: wgrd.tech/4a55aWc #MITREATTACK #EndpointSecurity #Cybersecurity #WatchGuard

リリース: MITRE ATT&CK v17.0、ESXi攻撃TTPを追加 Released: MITRE ATT&CK v17.0, now with ESXi attack TTPs #HelpNetSecurity (Apr 23) #MITREATTACK #ESXiセキュリティ #サイバー脅威インテリジェンス #仮想化セキュリティ #攻撃手法分析 helpnetsecurity.com/2025/04/23/rel…
helpnetsecurity.com
Released: MITRE ATT&CK v17.0, now with ESXi attack TTPs - Help Net Security
MITRE ATT&CK v17.0 includes a new section to cover the tactics, techniques and procedures (TTPs) used to target VMware ESXi hypervisors.
Hurry! Only a few days left to join our #Webinar on #MitreAttack framework. Hear Sergey Chubarov discuss the advantages of #MITREAttack framework in ethical hacking. Register now: bit.ly/3O3yAHw #ECCouncil #Mitre #Cybersecurity

On August 21st, join our #Webinar with Sergey Chubarov as he discusses how security teams can use MITRE ATT&CKs TTPS to help with their cyber risk analysis. Register now: bit.ly/3O3yAHw #EthicalHacking #MitreAttack #ECCouncil #Cybersecurity

MiTRE ATT&CK v14 - Released: #MITRE #MitreAttack #RedTeam #BlueTeam #PurpleTeam #InfoSec #CyberSecurity #Hacking
Ransomfeed is proud to be cited in a peer-reviewed study on ransomware attack patterns, published on Journal of Information Security and Applications. Grateful to the authors for acknowledging our dataset. @melillopietro #CyberSecurityResearch #Ransomware #MITREATTACK
📢 New blog! Operationalizing MITRE ATT&CK with Microsoft Security (Part 2) ...by understanding Active & Simulated coverage, an Analyst could take advantage of a well disciplined path to build threat-informed defenses. #MicrosoftSecurity #MitreAttack michalos.net/2024/03/25/ope…
michalos.net
Operationalizing MITRE ATT&CK with Microsoft Security (Part 2)
It has been some time since Part 1 of this blog has been posted, you may find it here. First part, focused mainly on the benefits and how to operationalize MITRE ATT&CK at Microsoft Defender XD…
Automated detection engineering now enhanced with Atomic Red Team MCP attack simulations and Splunk MCP validation for end-to-end detection accuracy. Ensures syntax, CIM compliance, and real-world effectiveness. #DetectionEngineering #MITREATTACK ift.tt/4zxIZjJ
hendryadrian.com
Agentic Detection Creation Now With Atomic Red Team and Splunk MCP Integration
This article describes an extended automated detection engineering workflow that includes attack testing via Atomic Red Team MCP and detection validation with Splunk MCP. These additions enable a...
🚨 New Writeup Alert! 🚨 "Introduction to MITRE ATT&CK: A Beginner’s Guide" by Nipun Negi is now live on IW! Check it out here: infosecwriteups.com/36a348b4607d #framework #cybersecurity #mitreattack #mitreattackframework
infosecwriteups.com
Introduction to MITRE ATT&CK: A Beginner’s Guide
Cybersecurity has become a critical concern in today’s digital world. With the increasing complexity of cyber threats, organizations need a…
Strengthen your data security strategies with the MITRE ATT&CK framework. Download our solution brief to improve your data risk posture and fortify your defenses against cyber threats. bit.ly/3Ucsh94 #cybersecurity #MITREATTACK #datasecurity

Sentinel2ATTACKv2 is a Python script designed for Microsoft Sentinel that extracts the TTPs from alerts generated and subsequently generates a MITRE ATT&CK navigation layer. #MicrosoftSentinel #MitreAttack blueteams.academy/docs/Microsoft…
Enterprise SIEMs miss 79% of known MITRE ATT&CK techniques - helpnetsecurity.com/2025/06/09/sie… - @CardinalOps - #MITREATTACK #SIEM #ThreatDetection #SOC #CyberSecurity #netsec #security #InfoSecurity #CISO #ITsecurity #CyberSecurityNews #SecurityNews

Attackers disable Windows Event Logging (T1562.002) to conceal their malicious activities, leaving defenders blind. Real-world examples include GhostEngine and Mallox ransomware. Learn how to detect and mitigate: hubs.li/Q03mV-0b0 #MITREATTACK #CyberSecurity
Research HAFNIUM. Extract TTPs. Map to ATT&CK. Then automate it with AI agents. Hands-on workshop with Jean-François Maes on Mar 26. 📅 10AM–12PM ET 🔗 go.sans.org/s7OjDr #ThreatIntel #MITREATTACK #RedTeam #SEC565
To all my virtual friends around the world, if you're at #BlackHatAsia, let's meet in human form! 😺 Bonus: I'm carrying stickers from my #mitreattack days and I'm not afraid to use them as bait. 🎟️ 😉 Drop a reply or message me.
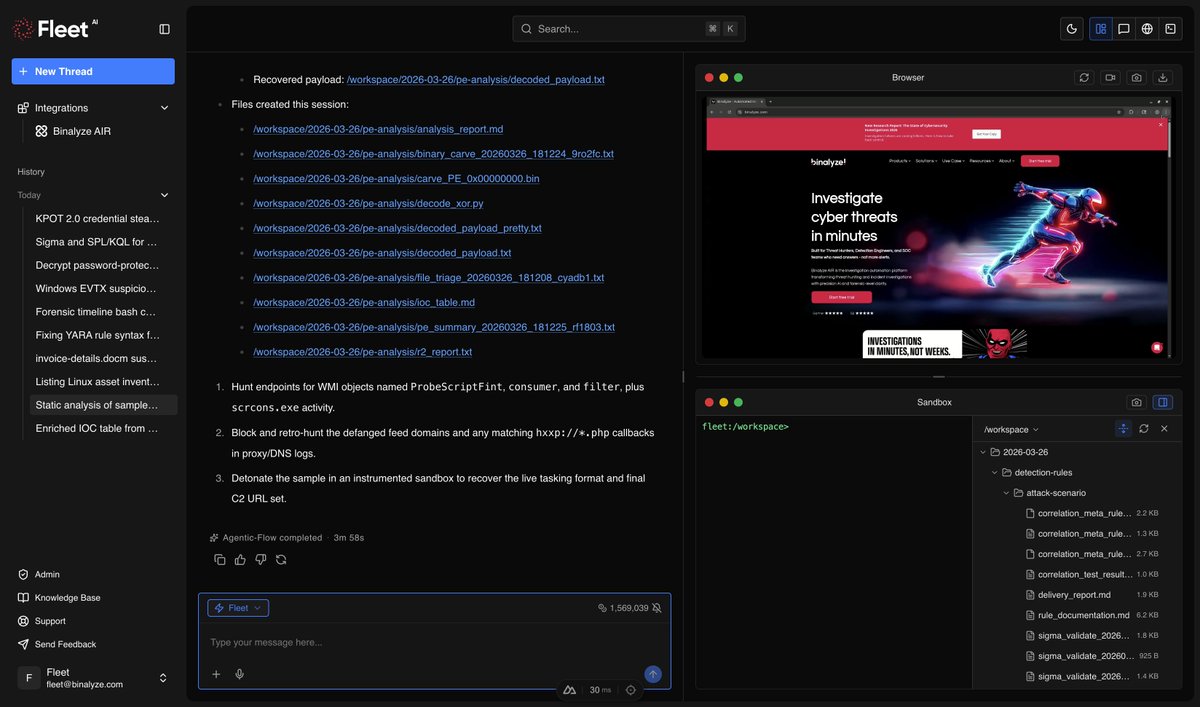
Stop mapping MITRE ATT&CK after the fact. With Fleet, every finding is mapped in real time, so investigation and reporting speak the same language, natively. See it in action: bit.ly/4temBd3 #DFIR #SOC #MITREATTACK #ThreatHunting #IR #EDR #XDR

🔐 🤖 AI meets cybersecurity! IPTC researchers use MITRE ATT&CK to detect & mitigate attacks in real time 🎯 📌 short.upm.es/27h5e #Cybersecurity #AI #MITREATTACK #TechInnovation

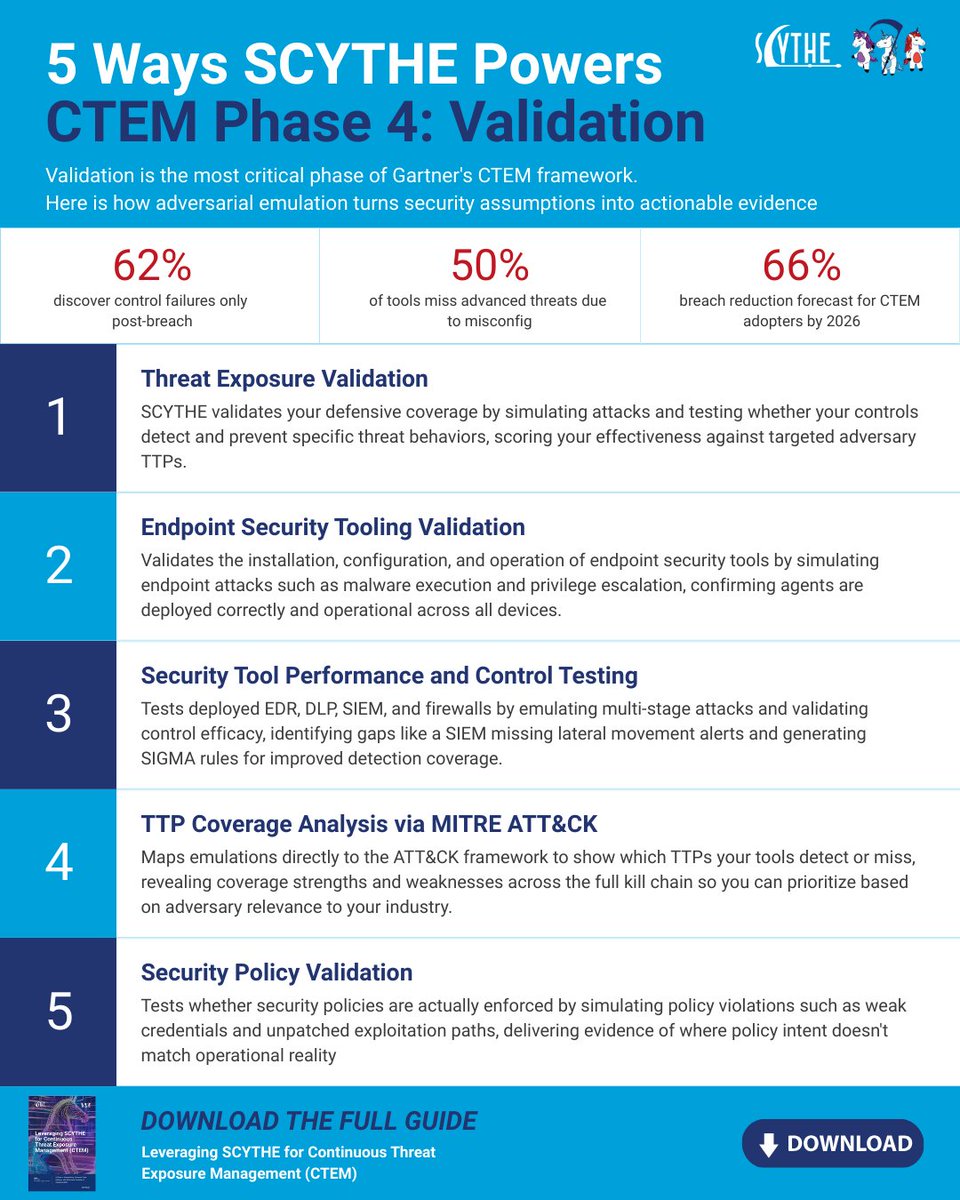
50% of security tools miss advanced threats due to misconfig or outdated rules. Our CTEM guide shows how to fix that with continuous adversarial validation. Download it here: hubs.ly/Q049QsN50 #CTEM #MITREATTACK #ThreatEmulation
Attackers don’t just get in, they run their code. 💻 Learn how hackers execute malicious code (TA0002) and how you can stop it before it spreads. Watch the full breakdown! 👇 #CyberSecurity #MITREATTACK #Execution #Malware #Integsec #NetworkSecurity #Infose #CyberDefense
Hackers don’t just appear — they find a way in. 🚪💻 Learn how attackers gain Initial Access (TA0001) and how you can stop them before they breach your network. Watch our quick breakdown! 👇 #CyberSecurity #MITREATTACK #InitialAccess #Phishing #NetworkSecurity #Integsec”
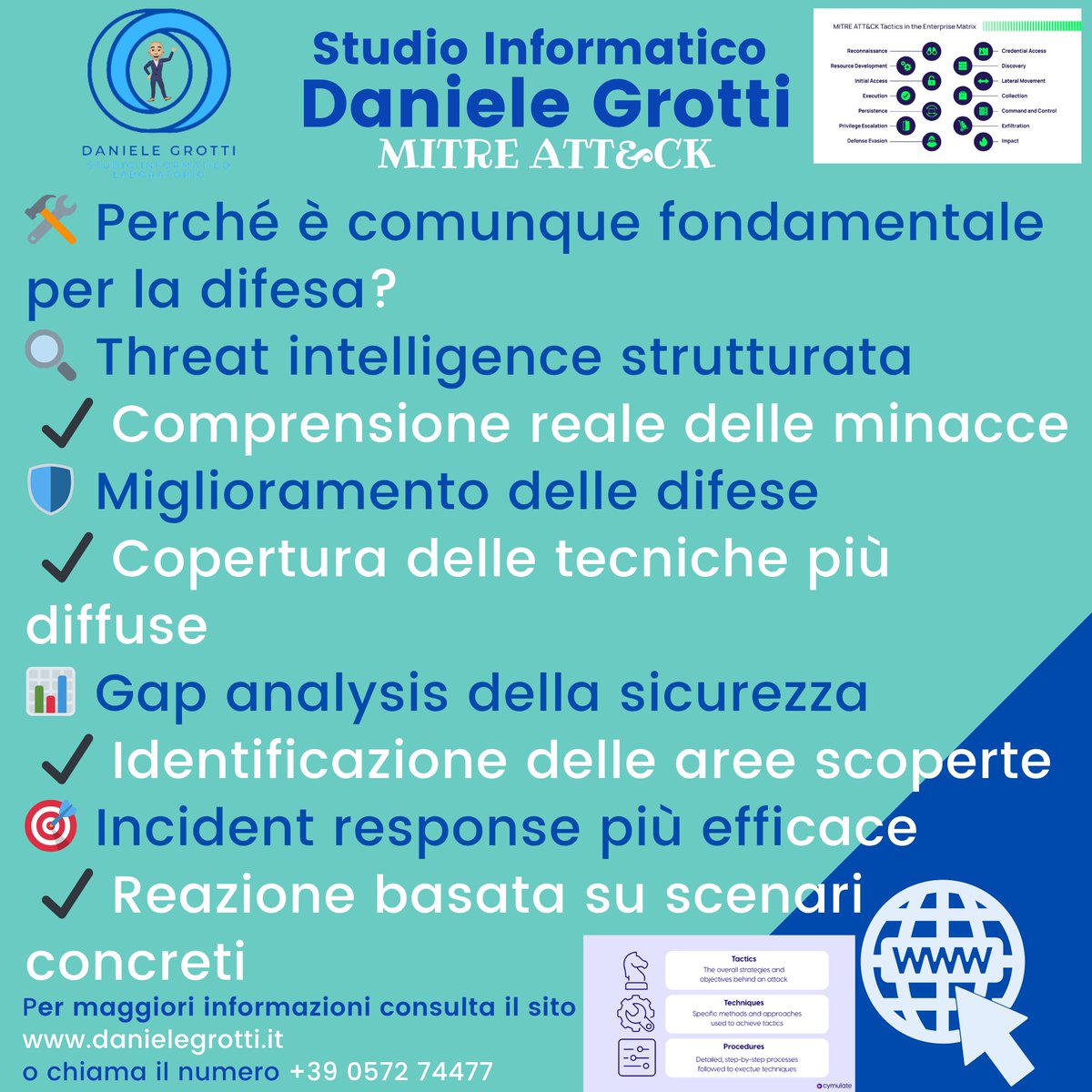
🛡️📊 𝐌𝐈𝐓𝐑𝐄 𝐀𝐓𝐓&𝐂𝐊 𝐅𝐫𝐚𝐦𝐞𝐰𝐨𝐫𝐤 — Conoscere l’attacco per difendersi meglio . . . #MITREATTACK #CyberSecurity #ThreatIntelligence #TTP #SOC #CyberDefense #RiskManagement #consulenteinformatico #massaecozzile #pistoia #montecatiniterme #studioinformaticodg



🔍 Cyber Threat Spotlight: Scanning IP Blocks Attackers scan before they strike mapping your systems, finding open ports, and spotting weak points. ⚠️ Would you catch it in time? #CyberSecurity #RedTeaming #MITREATTACK #ThreatDetection #InfoSec #IntegSec

2/ MITRE ATT&CK framework identifies Tactics, Techniques, and Procedures (TTPs) used by threat actors. Integrate this with EDR for proactive defense. #MITREATTACK #ThreatHunting
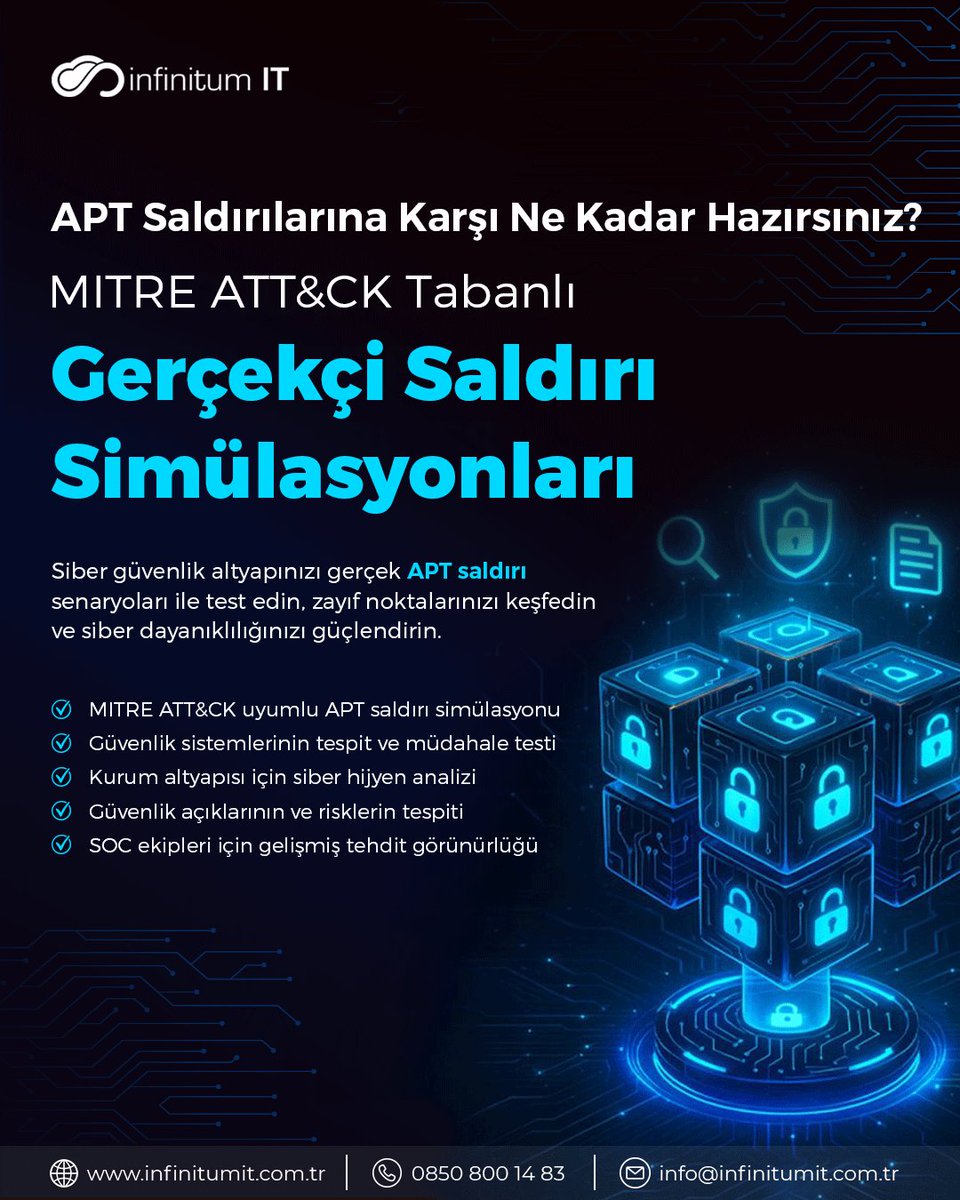
MITRE ATT&CK metodolojisine dayanan APT Tespit ve Siber Hijyen Analiz hizmetleri, kurumların savunma yeteneklerini gerçek saldırı senaryoları üzerinden ölçmelerini sağlayan kritik bir güvenlik yaklaşımıdır. 🚀 #APT #MITREATTACK #ThreatDetection #CyberSecurity #SOC #SiberHijyen
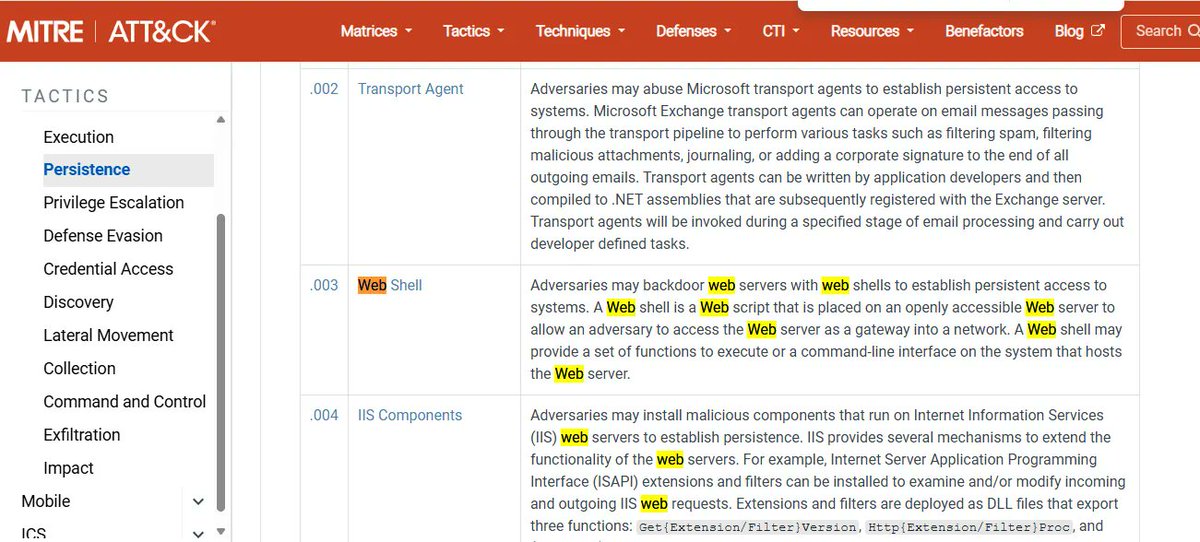
Day 68 Web Shells 🕵️♂️ Learned how attackers use web shells for remote command execution and persistence on compromised servers. Mapped to MITRE ATT&CK technique T1505.003 Web Shell. #Cybersecurity #BlueTeam #MITREATTACK #100DaysOfCybersecurity
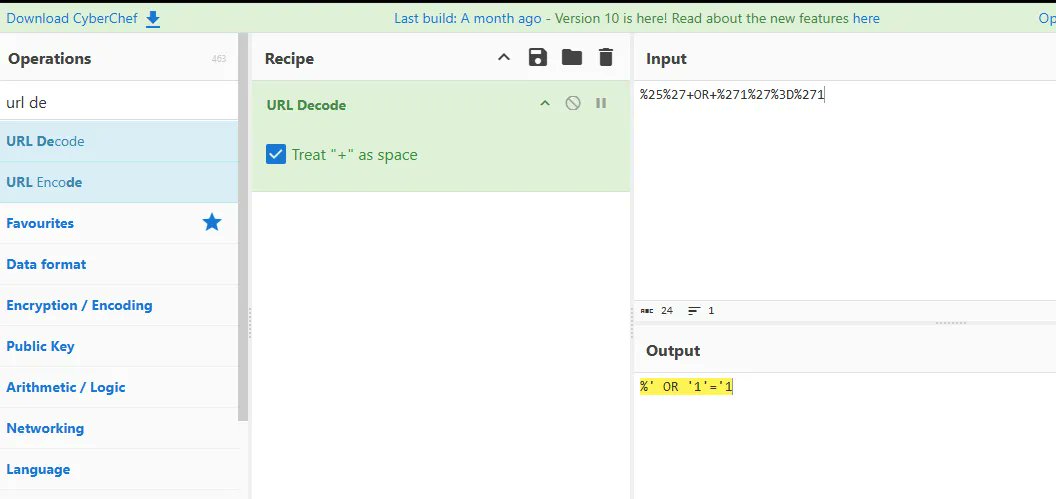
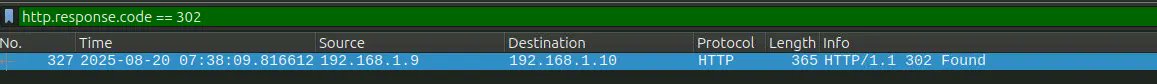
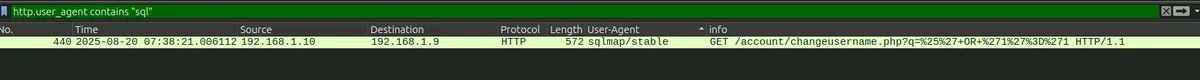
Day 67 of #100DaysOfCybersecurity: Deep dive into Traffic Analysis & Payload Decoding! 🕵️♂️ Today's breakdown: 🔹 Used #Wireshark to flag brute-force attempts (Hydra) and automated scans (sqlmap). 🔹 Decoded hidden SQLi payloads using #CyberChef
Research HAFNIUM. Extract TTPs. Map to ATT&CK. Then automate it with AI agents. Hands-on workshop with Jean-François Maes on Mar 26. 📅 10AM–12PM ET 🔗 go.sans.org/s7OjDr #ThreatIntel #MITREATTACK #RedTeam #SEC565
A huge thanks to everyone who joined our fireside chat, "Moving at the Speed of Threat" with Jeff Schiemann and Ronan Lavelle. If you missed the live chat, watch the recording here: 👉 bit.ly/4bhHpKV #CyberSecurity #MITREAttack #CyberThreat #Webinar
⏳ We go live in 2 hours. If you're responsible for proving your security controls then this conversation is for you. Secure your spot now. bit.ly/3OTSDMB #Cybersecurity #SecurityControls #MITREATTACK

We’re diving deep into the tools and frameworks (like DORA and Continuous Detection Testing) that make this possible in our upcoming webinar this Thursday! Join us here: bit.ly/40C5sOa #Cybersecurity #SecurityControls #MITREATTACK

2/ Begin by mapping potential threats using the MITRE ATT&CK framework. Identify which techniques are relevant to your environment. #ThreatHunting #MITREATTACK
2/ Map your findings to MITRE ATT&CK. Techniques like T1071, Application Layer Protocol, offer insights into common attacker methods. #SIEM #InfoSec #MITREATTACK
@TidalCyber Cyber CTO Richard Struse joins MITRE ATT&CK Advisory Council to guide threat intelligence strategy and advance procedure-led defense. 🔗 𝐑𝐞𝐚𝐝 𝐌𝐨𝐫𝐞: tinyurl.com/nhd5jtp4 #CyberSecurity #MITREATTACK #ThreatIntel #ThreatLedDefense #CyberResilience

This fireside chat webinar focuses on the "how" of modern security - bridging the gap between tool acquisition and actual protection. Register here: bit.ly/4rLFq7i #Cybersecurity #SecurityControls #MITREATTACK

Cyberattacks aren’t random — they follow known behaviors. MITRE ATT&CK helps organizations understand attacker tactics, detect threats faster, and reduce ransomware impact. #ZefaiInsights #MITREATTACK #CyberSecurity #ThreatIntel #zeenath556
An Alternative Way of Using MITRE ATT&CK® for Threat Hunting and Detection posts.bluraven.io/an-alternative… #Pentesting #MitreAttack #ThreatIntelligence #CyberSecurity #Infosec
WatchGuard’s results in the @MITREattack Round 7 Evaluation highlight how far we’ve come in our mission to deliver strong security that’s easy to use. See the full MITRE ER7 results: wgrd.tech/4a55aWc #MITREATTACK #EndpointSecurity #Cybersecurity #WatchGuard

The MITRE ATT&CK framework turns alert noise into clarity. 🎯 Map real adversary behavior 🛠️ Uncover gaps 📊 Structure investigations Tag alerts with ATT&CK IDs to boost speed and precision. 💬 Got a tip? Share it below ⬇️ #CyberDefenders #MITREATTACK #DFIR #ThreatDetection

What a learning journey... @MITREengenuity 's Certified MITRE ATT&CK Defender roadmap has probably been the most intense and diverse training I've ever followed. A 🧵[1/5] #MitreAttack #ThreatIntelligence #CyberThreatIntelligence #ThreatHunting #CyberSecurity
![Cyb3rMik3's tweet image. What a learning journey...
@MITREengenuity 's Certified MITRE ATT&CK Defender roadmap has probably been the most intense and diverse training I've ever followed.
A 🧵[1/5]
#MitreAttack #ThreatIntelligence #CyberThreatIntelligence #ThreatHunting #CyberSecurity](https://pbs.twimg.com/media/FsH_asHWwAAqOjM.jpg)
What is the MITRE ATT&CK framework and how can organizations leverage it to enhance their defenses? To learn join our session: okt.to/63zgl5 #MitreAttack #Ransomware #NetworkSecurity #SASE #SSE
Ridge IT & Picus Security break down real-world malware tactics, analyzing 1M malware samples to reveal the top 10 MITRE ATT&CK techniques behind 93% of attacks. 📺 Watch the full webinar here 👉 hubs.li/Q03bhvjZ0 #CyberSecurity #Infostealers #MITREATTACK #Malware

New room Eviction from @tryhackme : Unearth the monster from under your bed. This room is all about MITRE ATT&CK, you will use MITRE ATT&CK Navigator layer, and investigation the APT28 group tryhackme.com/room/eviction #tryhackme #mitreattack #mitre #apt28
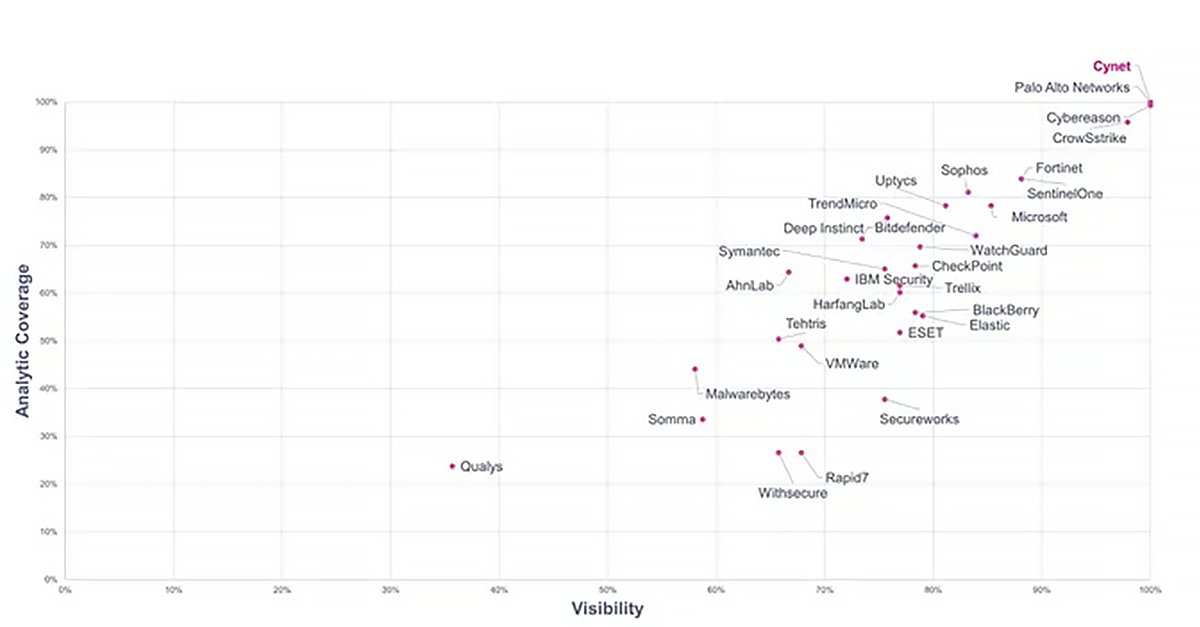
2023 @MITREengenuity ATT&CK Evaluations: 𝗖𝘆𝗻𝗲𝘁 𝗮𝗰𝗵𝗶𝗲𝘃𝗲𝘀 𝗮 𝗵𝗶𝘀𝘁𝗼𝗿𝗶𝗰 𝟭𝟬𝟬% Our all-in-one platform delivered: – 100% Detection – 100% Visibility – 100% Analytic coverage – 100% Real-time detections More #MITREattack key takeaways: hubs.ly/Q022X5MB0
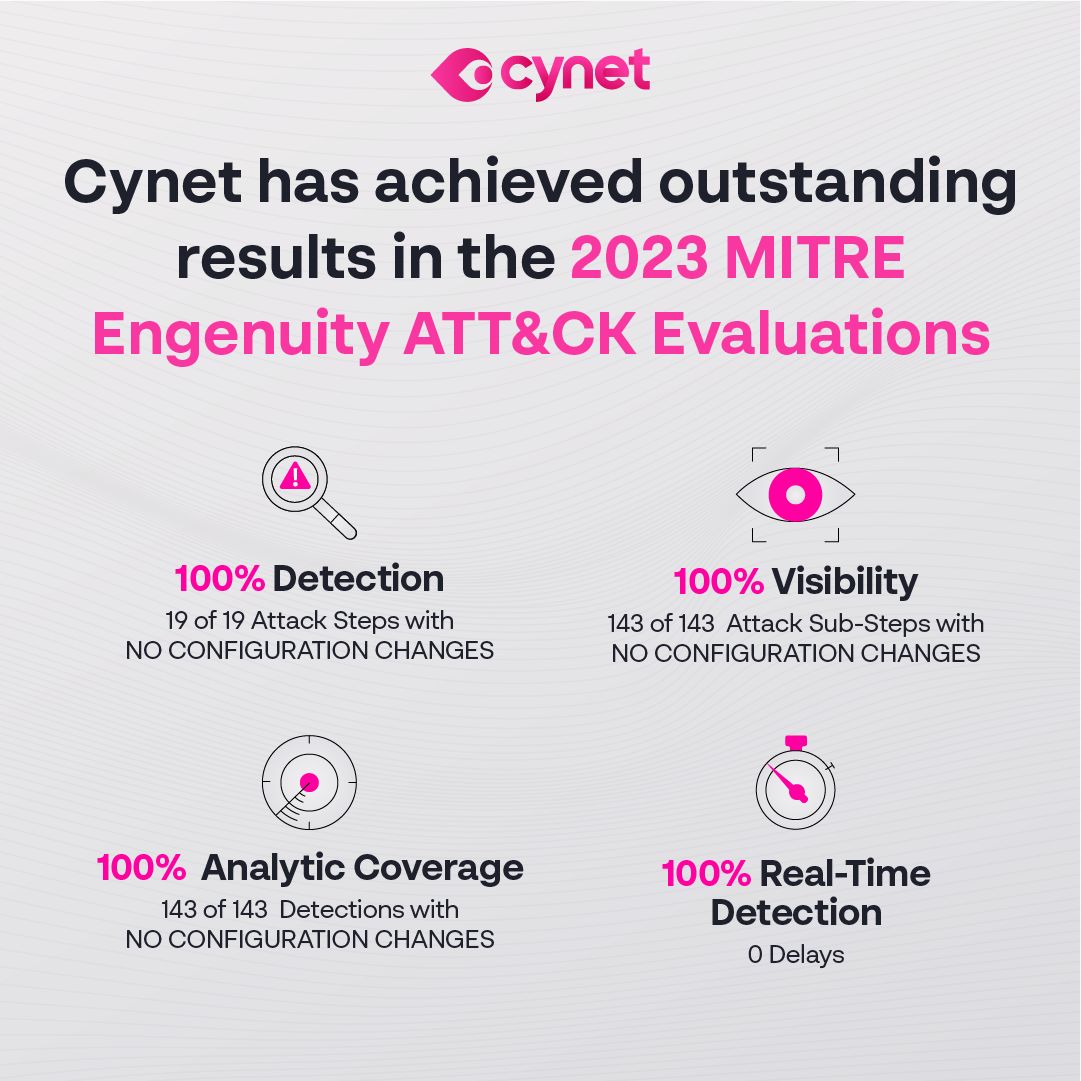
𝐑𝐄𝐋𝐄𝐀𝐒𝐄𝐃 𝐓𝐎𝐃𝐀𝐘: 2023 @MITREengenuity ATT&CK Evaluation results 👀 Key takeaways for #cybersecurity leaders + guidance to interpret the results: hubs.ly/Q022XyLw0 via @DarkReading #MITREattack
10章くらいになる予定で、1章を書きました。 セキュリティ監視入門! MITRE ATT&CK編 その①フレームワークの理解 blog.kaname.dev/2023/10/mitre-… #CyberSecurity #InformationSecurity #MitreAttack
Attackers frequently capture keystrokes, GUI inputs, and clipboard data to steal credentials and sensitive info (MITRE ATT&CK T1056). See real-world techniques from DarkVision RAT, Trinper backdoor & Lumma Stealer here: hubs.li/Q03mcqym0 #MITREATTACK #RedReport2025

🚨The mentioned zero-day flaws can be weaponized by threat actors to bypass authentication and run arbitrary commands on the infected system. Read more here: thehackernews.com/2024/04/mitre-… #cybernews #cybernewsmonday #mitreattack #cybercrime #malware #threatactor


Attackers disable Windows Event Logging (T1562.002) to conceal their malicious activities, leaving defenders blind. Real-world examples include GhostEngine and Mallox ransomware. Learn how to detect and mitigate: hubs.li/Q03mV-0b0 #MITREATTACK #CyberSecurity
漢字ATT&CK Tacticsの使用例 #NIRVANA改 #interop23 #mitreattack




NIRVANA改にMITRE ATT&CKによる攻撃記述を組み込むために、ATT&CK Tacticsを漢字一字で表現してみました。ご自由にお使いください。 偵: Reconnaissance 資: Resource Development 初: Initial Access 実: Execution 続: Persistence 権: Privilege Escalation 避: Defense Evasion 認: Credential

Adversaries leverage #ListPlanting (MITRE ATT&CK T1055.015), injecting malicious code through Windows list-view controls to evade detection. Discover how this stealthy technique works with detailed examples in our latest technical blog👇 hubs.li/Q03k-f_W0 #MITREATTACK

Attackers regularly disable security tools like Windows Defender, AMSI, Antivirus, and EDR to evade detection (MITRE ATT&CK T1562.001). Our latest article covers real-world cases (INC, BlackCat, RansomHub) and attacker tactics: hubs.li/Q03mblRR0 #MITREATTACK #ThreatIntel

MITRE ATT&CK v18.0 is here. The framework now uses Detection Strategies and Analytics to move defense from static rules to behavior-driven telemetry. This is a critical update for SOC teams. Picus supports v18.0. See the full analysis: hubs.li/Q03S-t3k0 #MITREATTACK

Strengthen your data security strategies with the MITRE ATT&CK framework. Download our solution brief to improve your data risk posture and fortify your defenses against cyber threats. bit.ly/3Ucsh94 #cybersecurity #MITREATTACK #datasecurity

Adversaries use fake security alerts (MITRE ATT&CK T1562.011) to overwhelm defenders and mask real threats. Our blog explains how attackers exploit this tactic and how to defend against it. Read more: hubs.li/Q03s6Ln_0 #CyberSecurity #MITREATTACK

Static threat models are outdated. FORK enables real-time, risk-centric modeling using PASTA and MITRE ATT&CK. versprite.com/cybersecurity-… #ThreatModeling #CyberSecurity #MITREATTACK #DevSecOps

Something went wrong.
Something went wrong.
United States Trends
- 1. Wemby N/A
- 2. #MetGala N/A
- 3. #WWERaw N/A
- 4. Mike Conley N/A
- 5. Anthony Edwards N/A
- 6. Knicks N/A
- 7. #bucciovertimechallenge N/A
- 8. Michael Conforto N/A
- 9. Pagan N/A
- 10. Keldon Johnson N/A
- 11. Spurs N/A
- 12. Brunson N/A
- 13. Julius Randle N/A
- 14. Dylan Harper N/A
- 15. De'Aaron Fox N/A
- 16. #TheRookie N/A
- 17. Taylor Hall N/A
- 18. Castle N/A
- 19. Davis Martin N/A
- 20. Victor Wembanyama N/A