#cybersecurity search results
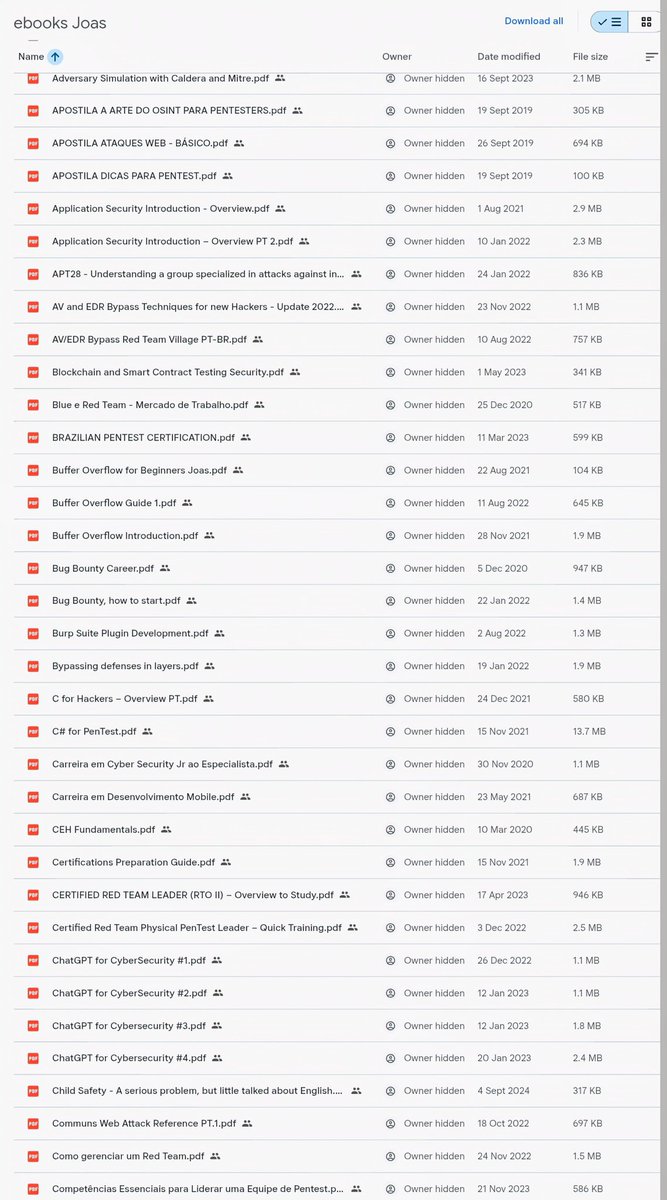
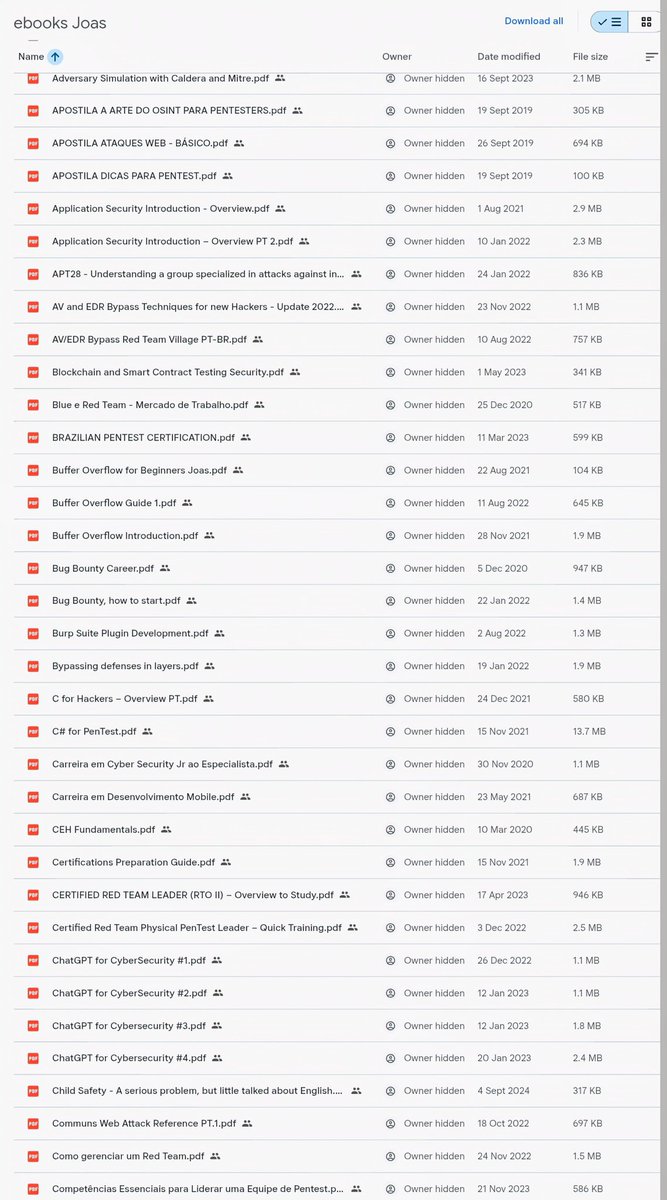
🚨 200+ Cybersecurity eBooks (Red Team / Pentest / Exploit Dev) Not beginner fluff — real material: • AV/EDR bypass • Buffer overflow • AD attacks • OSINT & recon • Bug bounty • SOC & threat hunting Download 👇 drive.google.com/drive/folders/… #CyberSecurity #EthicalHacking



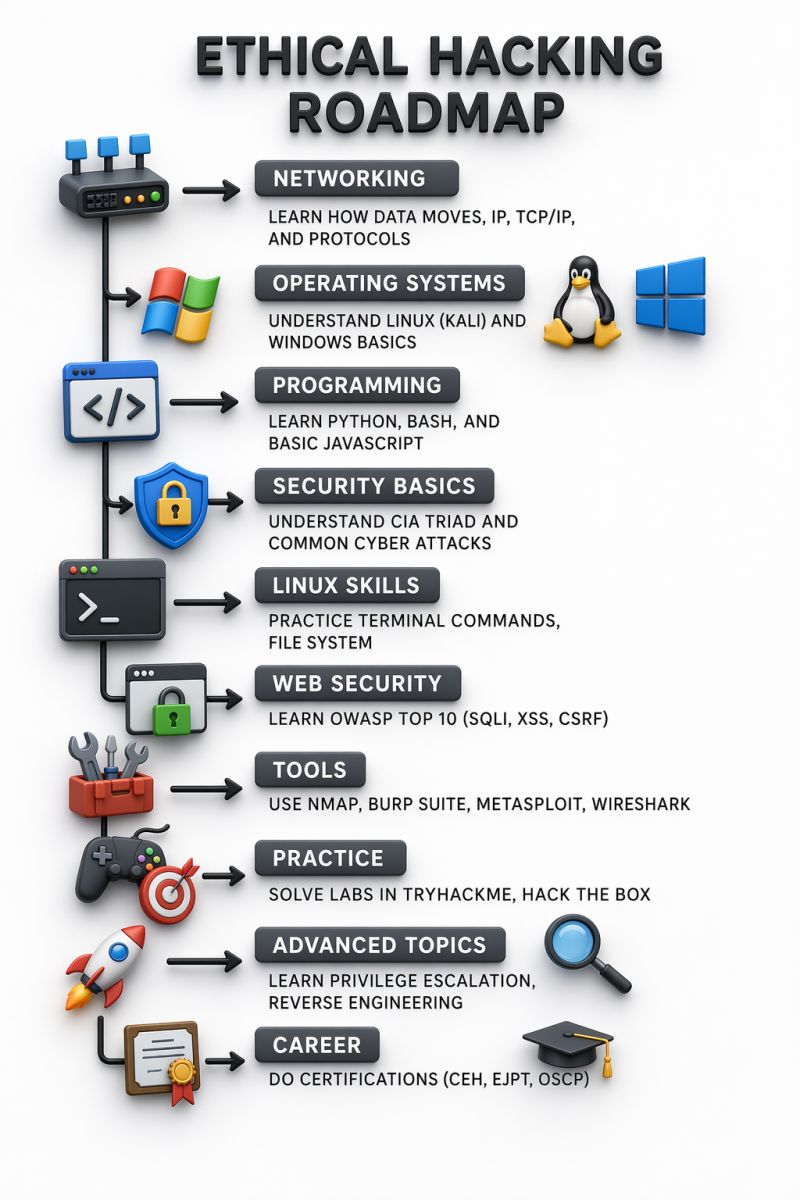
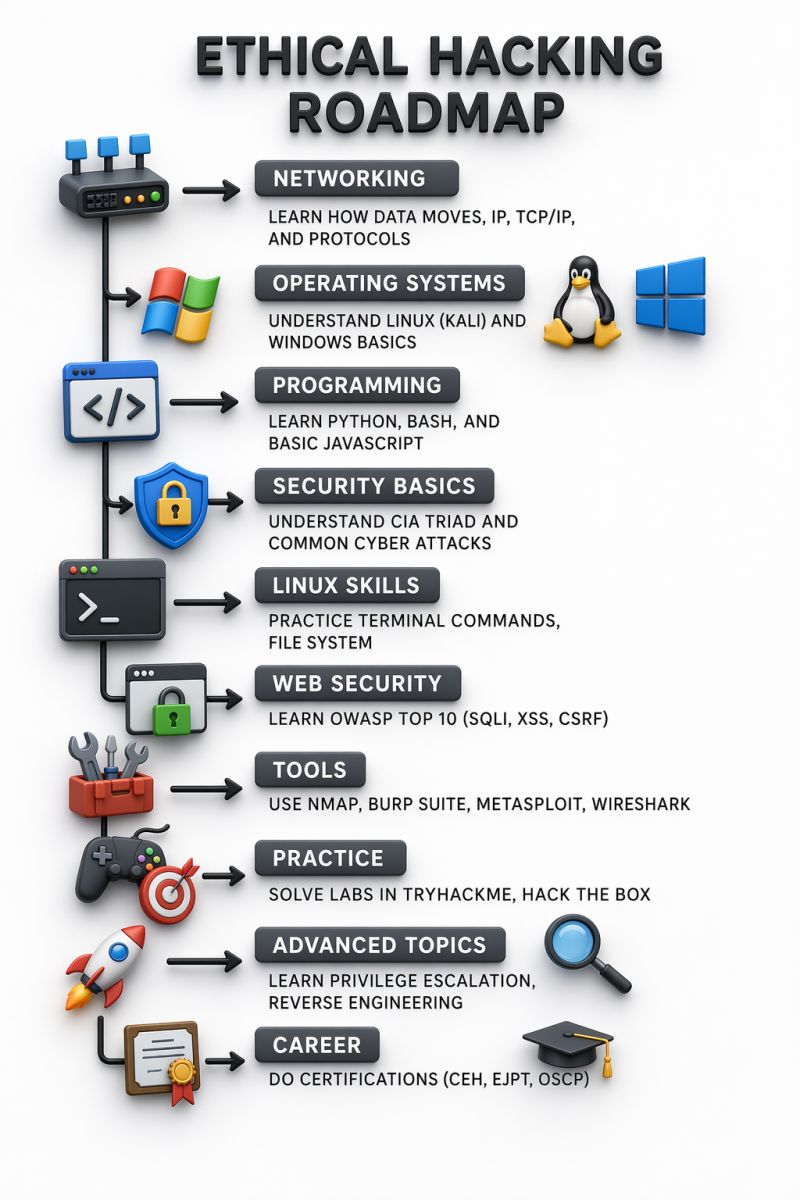
Ethical Hacking Roadmap 🔥 Telegram: t.me/hackinarticles #CyberSecurity #InfoSec #PenetrationTesting #EthicalHacking #BugBounty #ThreatIntelligence #RedTeam #BlueTeam #CloudSecurity #DataSecurity #CyberSecurityAwareness #AI
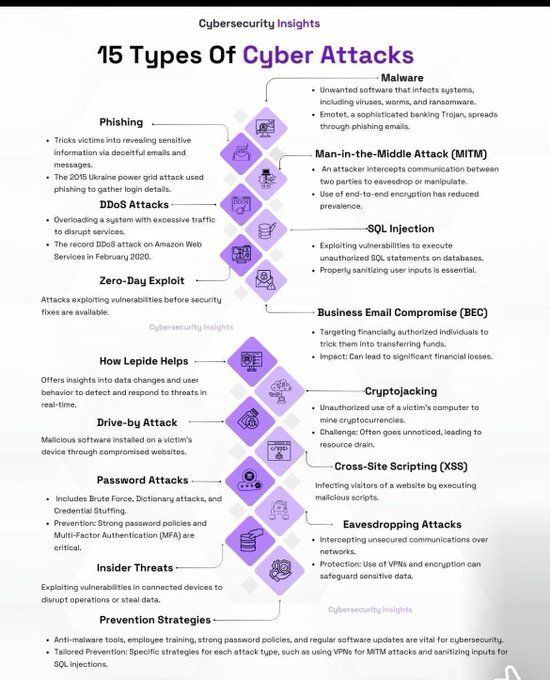
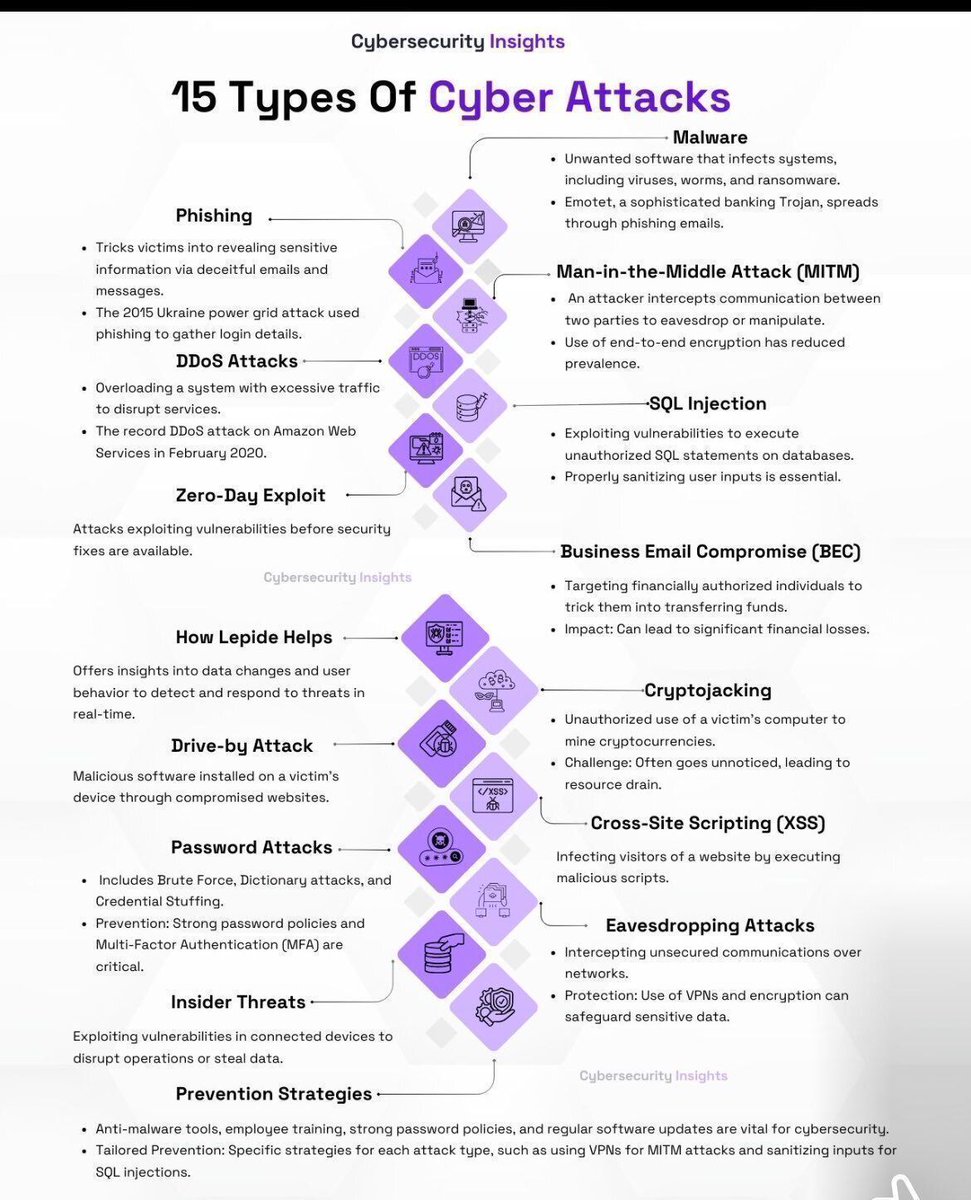
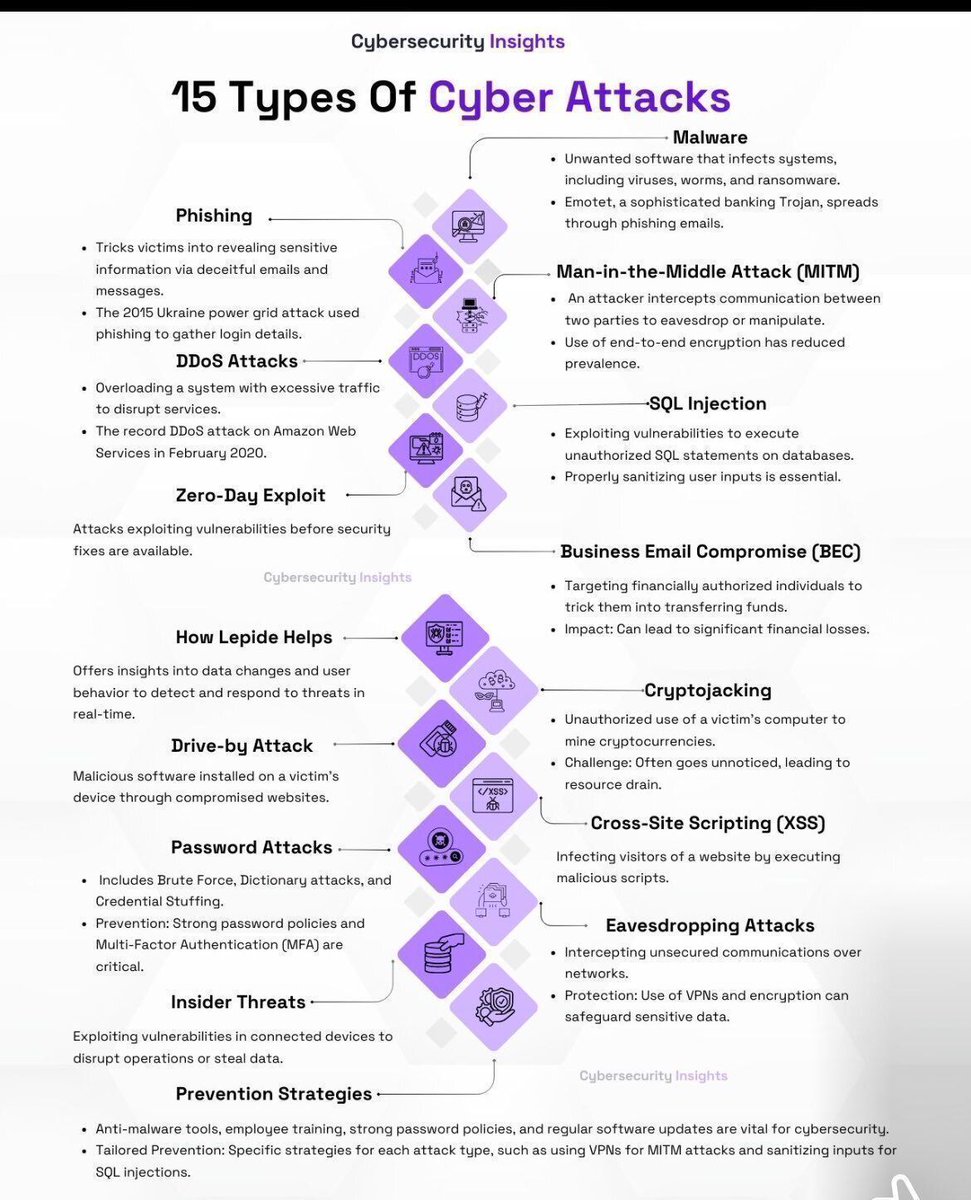
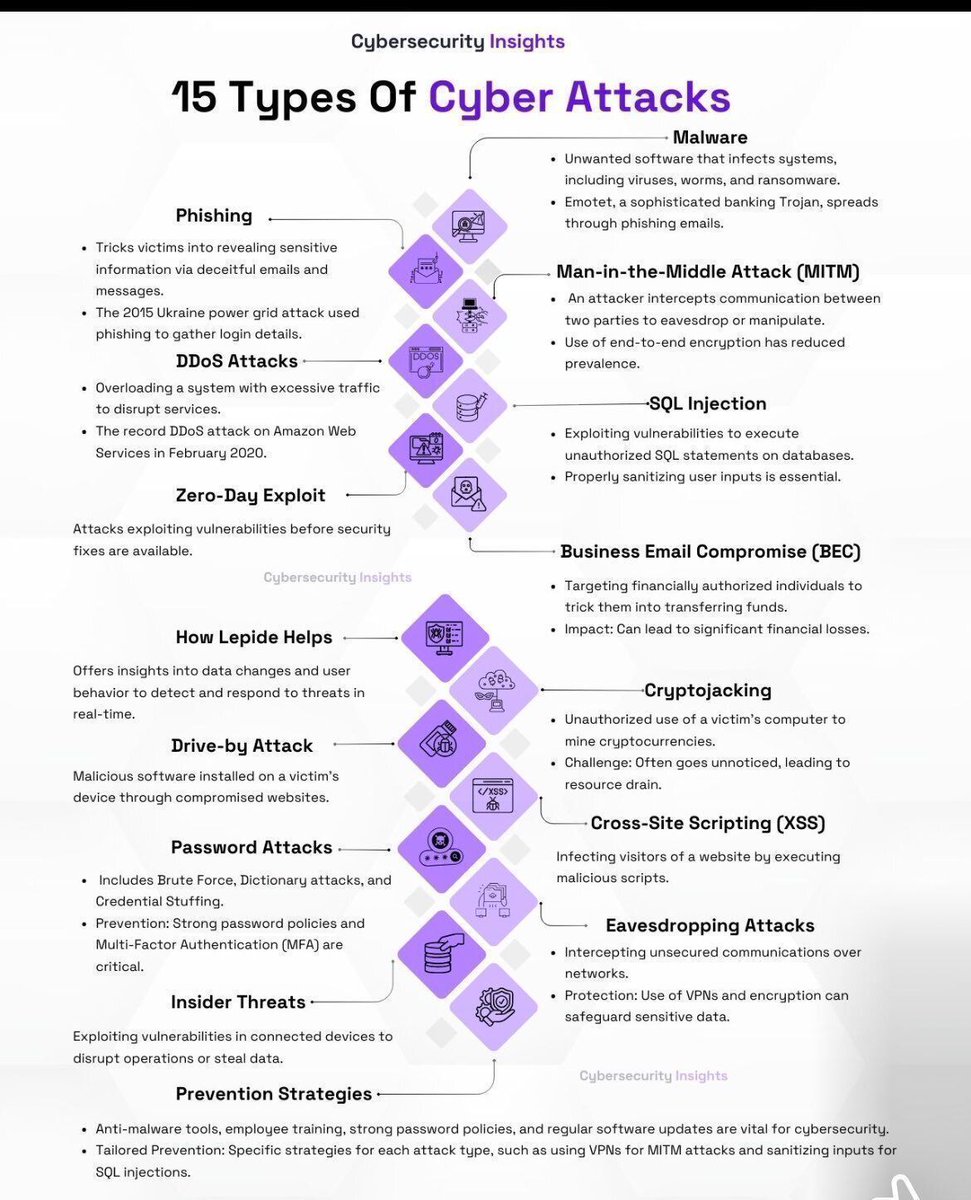
15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk
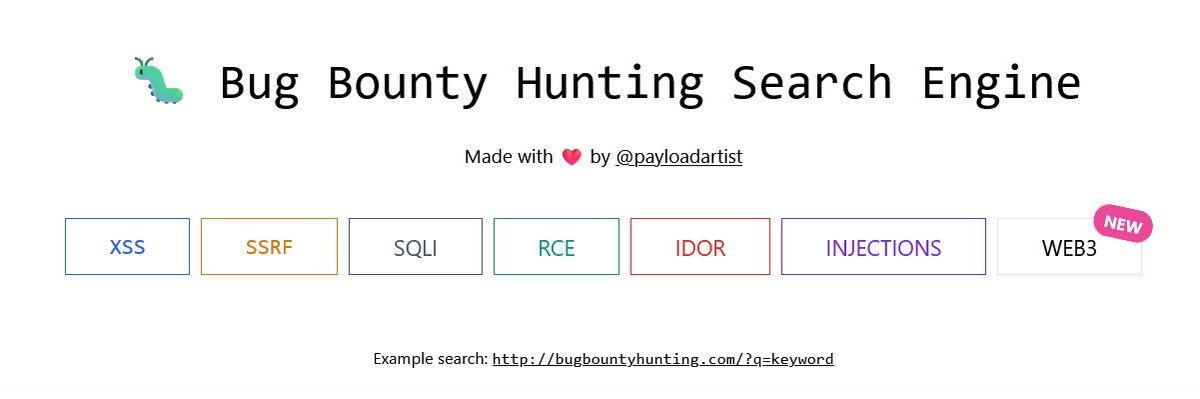
Hunters 🚨 One resource you should definitely bookmark: bugbountyhunting.com Writeups. Resources. Real learning. No fluff. #BugBountyHunter #CyberSecurity #InfoSec #EthicalHacking
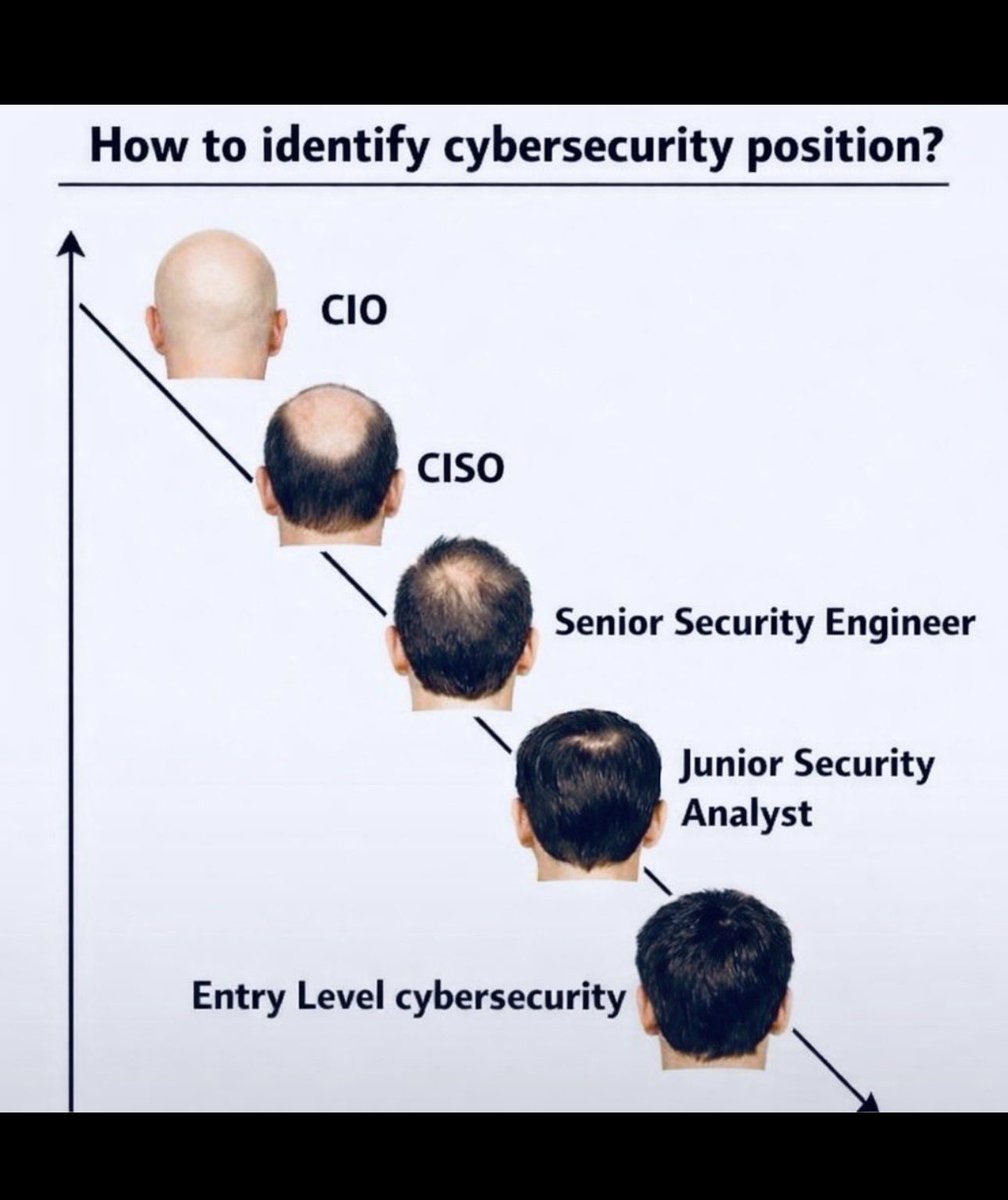
Pic of the Day #infosec #cybersecurity #cybersecuritytips #pentesting #cybersecurityawareness #informationsecurity

ایک غلطی اور واٹس ایپ ختم! ہیکرز کا خوفناک طریقہ سامنے آ گیا #CyberSecurity #PakistanNews #OnlineSafety #HackingAlert #ScamAlert #TechNews #DigitalSecurity #BreakingNews #InternetSafety #TrendingNow #NewsUpdate
WPS Is Still a Risk ⚠️📶 Testing wireless security on networks with WPS enabled using mobile tools. Many routers still expose weak configurations — making proper setup critical for your safety. Share and Comment "WPS" 📶👇 #wifi #cybersecurity #wps #infosec #networksecurity
Wi-Fi Attacks from a Smartwatch? ⌚📡 Technology is evolving… and so are security risks. Would your Wi-Fi be ready? Comment WATCH ⌚👇 #wifi #cybersecurity #infosec #networksecurity #ethicalhacking #technology
🗺️Active Directory Pentesting Mind Map: V1: raw.githubusercontent.com/esidate/pentes… V2: raw.githubusercontent.com/esidate/pentes… 🔖#infosec #cybersecurity #hacking #pentesting #security

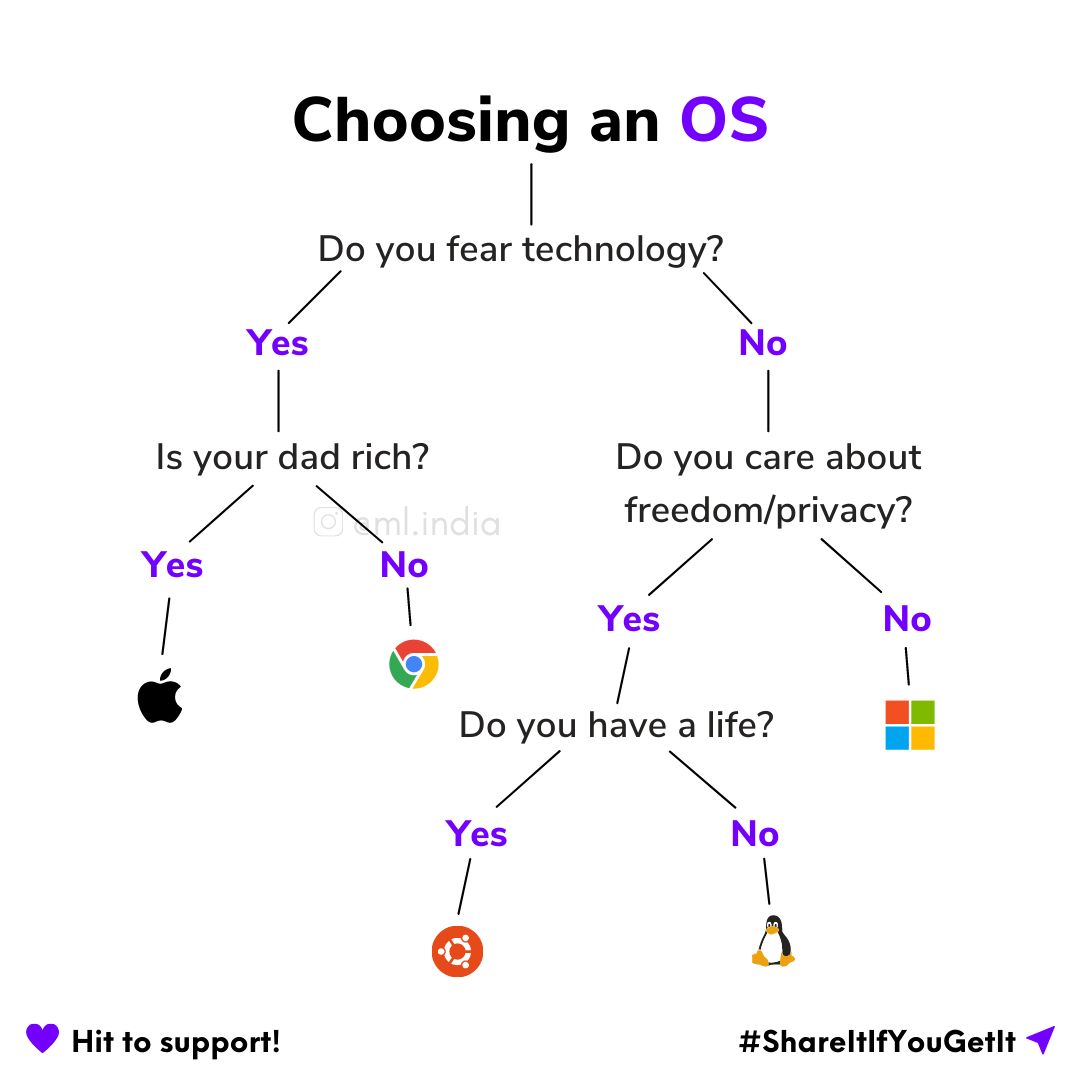
Pic of the Day #infosec #cybersecurity #cybersecuritytips #pentesting #cybersecurityawareness #informationsecurity
Pic of the Day #infosec #cybersecurity #cybersecuritytips #pentesting #cybersecurityawareness #informationsecurity
15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk
Ethical Hacking Roadmap 🔥 Telegram: t.me/hackinarticles #CyberSecurity #InfoSec #PenetrationTesting #EthicalHacking #BugBounty #ThreatIntelligence #RedTeam #BlueTeam #CloudSecurity #DataSecurity #CyberSecurityAwareness #AI
15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk
🚨 200+ Cybersecurity eBooks (Red Team / Pentest / Exploit Dev) Not beginner fluff — real material: • AV/EDR bypass • Buffer overflow • AD attacks • OSINT & recon • Bug bounty • SOC & threat hunting Download 👇 drive.google.com/drive/folders/… #CyberSecurity #EthicalHacking



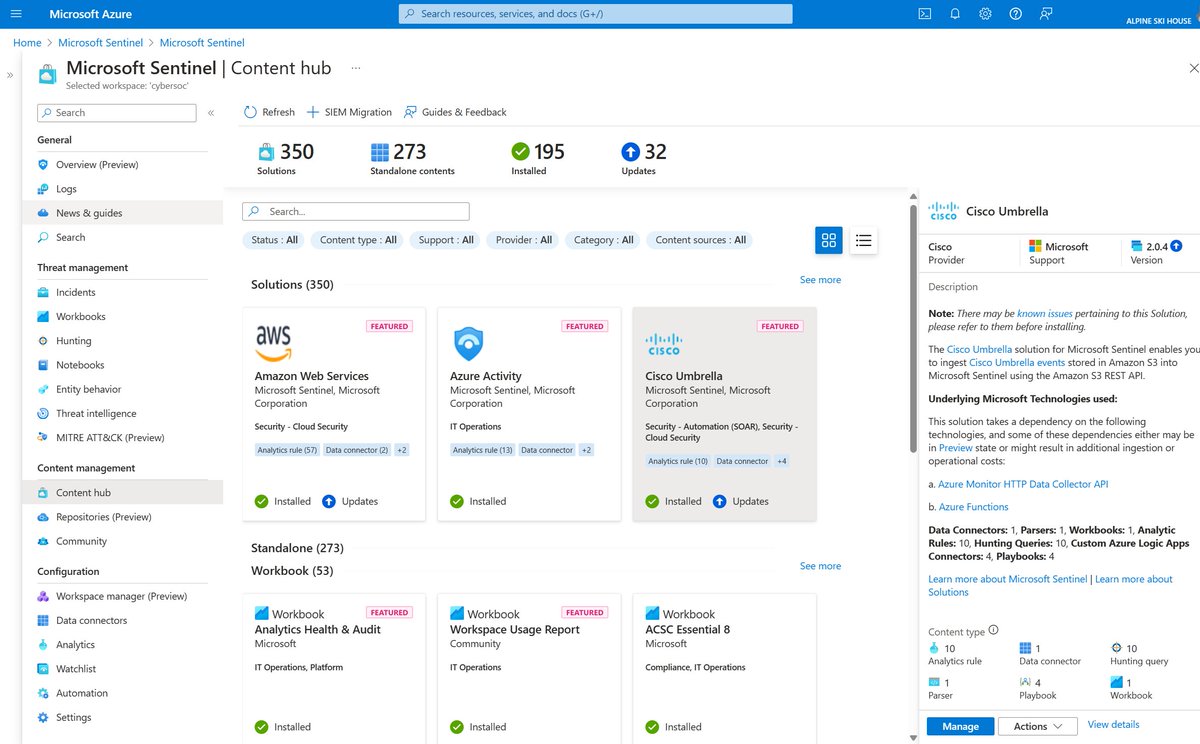
🔐 Control access smarter with Microsoft Sentinel! 👥 Resource-based RBAC for fine-grained permissions 📊 Limit data visibility by team needs ☁️ Secure logs via Azure Monitor Learn how 👉 msft.it/6019Q2pKX #Azure #RBAC #CyberSecurity

📢 Stay informed on the latest vulnerabilities with @CISAgov's Vulnerability Bulletin & gain valuable insights into emerging threats. 💡Check out the latest updates: cisa.gov/news-events/bu… #Cybersecurity #InfoSec #VulnerabilityManagement

🛡️ Secure smarter with Microsoft Sentinel! ✨ Cloud-native SIEM & SOAR ✨ AI-powered threat detection ✨ Automated response playbooks Start protecting now 👉 msft.it/6014Q2TJi #Azure #CyberSecurity #SIEM
AD Hash Types & Hashcat Modes 🔥 Telegram: t.me/hackinarticles #CyberSecurity #InfoSec #PenetrationTesting #EthicalHacking #BugBounty #ThreatIntelligence #RedTeam #BlueTeam #CloudSecurity #DataSecurity #CyberSecurityAwareness #AI

🐲Security analysis and reverse engineering of IoT devices and debugging with Ghidra 🔹Part 1: artresilia.com/iot-series-i-a… 🔹Part 2: artresilia.com/iot-series-ii-… 🔹Part 3: artresilia.com/iot-series-iii… 🔹Part 4: artresilia.com/iot-series-iv-… 🔖#infosec #cybersecurity #hacking #pentesting

🌐Database Search Engine 🗄️16,443,023,451 rows over 1,343 databases 🔗osint.lolarchiver.com/database_lookup 🔖#infosec #cybersecurity #hacking #pentesting #security #OSINT

🔓Best Password Cracking Tools 🔹Medusa 🔹Aircrack-ng 🔹Wfuzz 🔹OphCrack 🔹LophtCrack 🔹Hashcat 🔹Cain & Abel 🔹Rainbow Crack 🔹Brutus 🔹THC Hydra 🔹John the Ripper 🔖#infosec #cybersecurity #hacking #pentesting #security

They are secretly spying on users and profiling them. Learn more: cnews.link/malicious-tikt… #Chrome #privacy #cybersecurity
Something went wrong.
Something went wrong.
United States Trends
- 1. Draft Day N/A
- 2. Good Thursday N/A
- 3. Vrabel N/A
- 4. #PhinsUp N/A
- 5. Happy Friday Eve N/A
- 6. Caleb Downs N/A
- 7. AIIocation N/A
- 8. Schedule III N/A
- 9. #VenezuelaVuelaLibre N/A
- 10. Counseling N/A
- 11. James Pearce N/A
- 12. #WorldBookDay N/A
- 13. Halo N/A
- 14. #ThursdayThoughts N/A
- 15. #thursdayvibes N/A
- 16. molly ringworm N/A
- 17. Thirsty Thursday N/A
- 18. Reza Pahlavi N/A
- 19. Paramount Skydance N/A
- 20. Prince Louis N/A